Weblink Smartphone Compatibility List
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Product ID Product Type Product Description Notes Price (USD) Weight (KG) SKU 10534 Mobile-Phone Apple Iphone 4S 8GB White 226.8
Rm A1,10/F, Shun Luen Factory Building, 86 Tokwawan Road, Hong Kong TEL: +852 2325 1867 FAX: +852 23251689 Website: http://www.ac-electronic.com/ For products not in our pricelist, please contact our sales. 29/8/2015 Product Price Weight Product Type Product Description Notes SKU ID (USD) (KG) 10534 mobile-phone Apple iPhone 4S 8GB White 226.8 0.5 40599 10491 mobile-phone Apple iPhone 5s 16GB Black Slate 486.4 0.5 40557 10497 mobile-phone Apple iPhone 5s 16GB Gold 495.6 0.5 40563 10494 mobile-phone Apple iPhone 5s 16GB White Silver 487.7 0.5 40560 10498 mobile-phone Apple iPhone 5s 32GB Gold 536.3 0.5 40564 11941 mobile-phone Apple iPhone 6 128GB Gold 784.1 0.5 41970 11939 mobile-phone Apple iPhone 6 16GB Gold 622.8 0.5 41968 11936 mobile-phone Apple iPhone 6 16GB Silver 633.3 0.5 41965 11942 mobile-phone Apple iPhone 6 16GB Space Grey 618.9 0.5 41971 11940 mobile-phone Apple iPhone 6 64GB Gold 705.4 0.5 41969 11937 mobile-phone Apple iPhone 6 64GB Silver 706.7 0.5 41966 11943 mobile-phone Apple iPhone 6 64GB Space Grey 708 0.5 41972 11963 mobile-phone Apple iPhone 6 Plus 128GB Silver 917.9 1 41991 11955 mobile-phone Apple iPhone 6 Plus 16GB Gold 755.3 1 41983 11961 mobile-phone Apple iPhone 6 Plus 16GB Silver 731.6 1 41989 11958 mobile-phone Apple iPhone 6 Plus 16GB Space Grey 735.6 1 41986 11956 mobile-phone Apple iPhone 6 Plus 64GB Gold 843.1 1 41984 11962 mobile-phone Apple iPhone 6 Plus 64GB Silver 841.8 1 41990 11959 mobile-phone Apple iPhone 6 Plus 64GB Space Grey 840.5 1 41987 12733 mobile-phone ASUS ZenFone 2 ZE550ML Dual SIM -
Google ARCORE
Google ARCORE Nisfu Asrul Sani @ Lab Langit 9 - PENS 20 - 22 November 2017 environtment Setting up your development environment Install the Android SDK version 7.0 (API Level 24) or higher. To install the Android SDK, install Android Studio. To update the Android SDK, use the Android SDK Manager tool in Android Studio. Install Unity 2017.2 Beta 11 or higher, with the Android Build Support component. For more info, see Downloading and Installing Unity. You will need to get the ARCore SDK for Unity. You can either: Download the SDK Preview for Unity and extract it. -or- Clone the repository with the following command: git clone https://github.com/google-ar/arcore-unity-sdk.git Prepare your device You must use a supported, physical device. ARCore does not support virtual devices such as the Android Emulator. To prepare your device: Enable developer options Enable USB debugging Install the ARCore Service on the device: Download the ARCore Service Connect your Android device to the development machine with a USB cable Install the service by running the following adb command: adb install -r -d arcore-preview.apk https://play.google.com/store/apps/details?id=com.un Additional ity3d.genericremote Supported Devices ARCore is designed to work on a wide variety of qualified Android phones running N and later. During the SDK preview, ARCore supports the following devices: Google Pixel, Pixel XL, Pixel 2, Pixel 2 XL Samsung Galaxy S8 (SM-G950U, SM-G950N, SM- G950F, SM-G950FD, SM-G950W, SM-G950U1) Initially, ARCore will only work with Samsung’s S8 and S8+ and Google’s Pixel phone, but by the end of the year, Google promised to have support for 100 million Android phones, including devices from LG, Huawei and Asus, among others. -
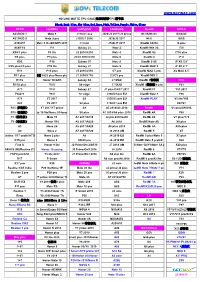
NO LINE MATTE TPU CASE/无痕细磨砂TPU型号表 Black,Dark Blue,Sky Blue,Red,Rose,Pink,Yellow,Purple,White,Cl
WWW.BOYIMAX.COM NO LINE MATTE TPU CASE/无痕细磨砂TPU型号表 Black,Dark blue,Sky blue,Red,Rose,Pink,Yellow,Purple,White,Clear OPPO HUAWEI SAMSUNG SAMSUNG XiaoMi APPLE A33/NEO 7 Mate 9 J110/J1 ace J320/J3 2017/J3 prime Mi 5X/Mi A1 i5/5S/SE A37/NEO 9 Mate 9 pro J120/J1 2016 J520/J5 2017 Mi 6 i6/6S A39/A57 Mate 9 lite/6X/GR5 2017 J1 mini J720/J7 2017 XiaoMi 6X/A2 i6 plus A59/F1S P9 Galaxy J2 Note 3 XiaoMi MIX 2S i7/8 R9/F1 plus P9 lite J2 2016/J210 Note 4 XiaoMi S2 i7/i8 plus R9 plus P9 plus J3/J3 2016/J310 Note 5 XiaoMi 8 iP X R9S P10 Galaxy J5 Note 8 XiaoMi 8 SE iP XS 5.8' R9S plus/F3 plus P10 lite Galaxy J7 Note 9 XiaoMi MAX 3 iP XR 6.1' R11 P10 plus J5 2016/J510 C7 pro XiaoMi MAX 3 pro XS MAX 6.5' R11 plus 麦芒 5/G9 plus/Nova plus J7 2016/J710 C9/C9 pro XiaoMi MIX 3 R11S Honor 5X/GR5 Galaxy S6 J7 MAX XiaoMi 8青春版 ViVo R11S plus Y3 II S6 edge J7 DUO XiaoMi 8探索版/8 pro Y53 A71 Y5 II Galaxy S7 J7 plus/C8/C7 2017 XiaoMi F1 Y53 2017 F5/A73 Y6 II S7 edge J330/J3 pro EU XiaoMi Note 3 Y55 A79 Y3 2017 S8 J530/J5 pro EU XiaoMi PLAY V5 lite/Y66 A83 Y5 2017 S8 plus J730/J7 pro EU V5/Y67 R15 (梦境版) Y7 2017/Y7 prime S9 A5 2018/A8 2018 RedMi V5 plus/X9/X9S R15 (普通版) Mate 10 lite/Nova 2i/Honor 9i S9 plus A7 2018/A8 plus 2018 RedMi 4A Y69 F7(海外版) Mate 10 A7 2017/A710 J2 pro 2018/J250 RedMi 4X V7 plus/Y79 F3(印度版) Honor V10 A3 2017/A320 A6 2018 RedMi Note 4X X9 plus A3 Nova 2S A5 2017/A520 A6 plus 2018 RedMi 5A X9S plus A9 Nova 2 A7 2017/A720 J3 2018 AM RedMi 5 X7 Realme 1/F7 youth/A73S Nova 2 plus A8 J4 2018 EU RedMi 5 plus/Note 5 X7 plus R15 pro Honor 9 A9/A9 pro J6 -

Samsung Galaxy J5 J530F(2017) Duos 16GB Gold
Samsung Galaxy J5 J530F(2017) Duos 16GB Gold Samsung Galaxy J5 (2017) SM-J530F. Bildschirmdiagonale: 13,2 cm (5.2 Zoll), Bildschirmauflösung: 1280 x 720 Pixel, Display-Typ: SAMOLED. Prozessor-Taktfrequenz: 1,6 GHz. RAM-Kapazität: 2 GB, Interne Speicherkapazität: 16 GB. Auflösung Rückkamera: 13 MP, Rückkameratyp: Einzelne Kamera. Sim Card Steckplätze: Dual SIM, 3G, 4G. Vorinstalliertes Betriebssystem: Android. Batteriekapazität: 3000 mAh. Produktfarbe: Gold. Gewicht: 160 g Artikel 374869 Herstellernummer SM-J530FZDDDBT EAN 8806088894775 Zusammenfassung 13.208 cm (5.2 ") 720 x 1280 Super AMOLED, GSM/UMTS/LTE, 1.6 GHz Octa-Core, RAM 2GB, 13.0 MP/13.0 MP, MicroSD, Wi-Fi, Bluetooth, NFC, Android Samsung Galaxy J5 (2017) SM-J530F, 13,2 cm (5.2 Zoll), 2 GB, 16 GB, 13 MP, Android, Gold Samsung Galaxy J5 (2017) SM-J530F. Bildschirmdiagonale: 13,2 cm (5.2 Zoll), Bildschirmauflösung: 1280 x 720 Pixel, Display-Typ: SAMOLED. Prozessor-Taktfrequenz: 1,6 GHz. RAM-Kapazität: 2 GB, Interne Speicherkapazität: 16 GB. Auflösung Rückkamera: 13 MP, Rückkameratyp: Einzelne Kamera. Sim Card Steckplätze: Dual SIM, 3G, 4G. Vorinstalliertes Betriebssystem: Android. Batteriekapazität: 3000 mAh. Produktfarbe: Gold. Gewicht: 160 g Beschreibung Natürliche Eleganz Stil trifft auf Funktionalität. Wir legen großen Wert auf Details, daher haben wir mit dem Galaxy J5 (2017) DUOS ein Smartphone geschaffen, das über ein Metallgehäuse verfügt, eine nicht hervorstehende Kamera und ein 13,18 cm / 5,2" HD Super AMOLED- Display hat. Teilen Sie Ihr Leben aus Ihrer Perspektive Die 13 MP-Hauptkamera mit f1.7-Blende schießt mit einem hohen Detailgrad, auch bei schlechten Lichtverhältnissen, hochauflösende Bilder. Für eine bequeme, einhändige Bedienung lässt sich die Kamera-Schaltfläche auf dem Display verschieben, sodass Sie jederzeit ein Foto schießen können - egal, ob Sie die richtige Pose oder den perfekten Hintergrund suchen. -

Manual De Usuario
SM-A300FU Manual de usuario Spanish. 12/2014. Rev.1.0 www.samsung.com Contenido Lea la siguiente información Conectividad red antes de comenzar 35 Datos móviles 35 Wi-Fi 36 Módem USB y Zona Wi-Fi Para comenzar 7 Contenido de la caja 8 Diseño del dispositivo Movimientos y funciones de 10 Uso de la tarjeta SIM o USIM y la batería accesibilidad 15 Usar la tarjeta de memoria 38 Movimientos y gestos 17 Encender y apagar el dispositivo 17 Bloquear y desbloquear la pantalla Personalizar 41 Administrar las pantallas de inicio y Nociones básicas aplicaciones 18 Usar la pantalla táctil 43 Configurar fondos de pantalla y melodías 21 Diseño de la pantalla Inicio 44 Cambiar la función de bloqueo de pantalla 25 Panel de notificaciones y panel de ajustes rápidos 45 Modo Privado 28 Abrir aplicaciones 46 Modo Sencillo 28 Instalar o desinstalar aplicaciones 47 Transferir datos de un dispositivo anterior 30 Introducir texto 48 Configurar cuentas 32 Captura de pantalla 32 Mis Archivos 33 Función de ahorro de energía Teléfono 34 Ver información de ayuda 49 Llamar 50 Recibir llamadas 51 Opciones durante las llamadas 2 Contenido Contactos 72 Internet 73 Música 53 Añadir contactos 75 Vídeo 53 Importar y exportar contactos 76 Reloj 54 Buscar contactos 78 Calculadora 78 Notas 79 Grabadora Mensajes y correo electrónico 80 Dropbox 55 Mensajes 81 Flipboard 56 Correo electrónico 81 Radio 83 Google apps Cámara 58 Disparo básico Conectarse con otros 60 Modos de disparo dispositivos 63 Ajustes de la cámara 85 Bluetooth 87 Wi-Fi Direct 89 NFC Galería 91 S Beam 65 Ver -

RADA Sense Mobile Application End-User Licence Agreement
RADA Sense Mobile Application End-User Licence Agreement PLEASE READ THESE LICENCE TERMS CAREFULLY BY CONTINUING TO USE THIS APP YOU AGREE TO THESE TERMS WHICH WILL BIND YOU. IF YOU DO NOT AGREE TO THESE TERMS, PLEASE IMMEDIATELY DISCONTINUE USING THIS APP. WHO WE ARE AND WHAT THIS AGREEMENT DOES We Kohler Mira Limited of Cromwell Road, Cheltenham, GL52 5EP license you to use: • Rada Sense mobile application software, the data supplied with the software, (App) and any updates or supplements to it. • The service you connect to via the App and the content we provide to you through it (Service). as permitted in these terms. YOUR PRIVACY Under data protection legislation, we are required to provide you with certain information about who we are, how we process your personal data and for what purposes and your rights in relation to your personal data and how to exercise them. This information is provided in https://www.radacontrols.com/en/privacy/ and it is important that you read that information. Please be aware that internet transmissions are never completely private or secure and that any message or information you send using the App or any Service may be read or intercepted by others, even if there is a special notice that a particular transmission is encrypted. APPLE APP STORE’S TERMS ALSO APPLY The ways in which you can use the App and Documentation may also be controlled by the Apple App Store’s rules and policies https://www.apple.com/uk/legal/internet-services/itunes/uk/terms.html and Apple App Store’s rules and policies will apply instead of these terms where there are differences between the two. -

Prohibited Agreements with Huawei, ZTE Corp, Hytera, Hangzhou Hikvision, Dahua and Their Subsidiaries and Affiliates
Prohibited Agreements with Huawei, ZTE Corp, Hytera, Hangzhou Hikvision, Dahua and their Subsidiaries and Affiliates. Code of Federal Regulations (CFR), 2 CFR 200.216, prohibits agreements for certain telecommunications and video surveillance services or equipment from the following companies as a substantial or essential component of any system or as critical technology as part of any system. • Huawei Technologies Company; • ZTE Corporation; • Hytera Communications Corporation; • Hangzhou Hikvision Digital Technology Company; • Dahua Technology company; or • their subsidiaries or affiliates, Entering into agreements with these companies, their subsidiaries or affiliates (listed below) for telecommunications equipment and/or services is prohibited, as doing so could place the university at risk of losing federal grants and contracts. Identified subsidiaries/affiliates of Huawei Technologies Company Source: Business databases, Huawei Investment & Holding Co., Ltd., 2017 Annual Report • Amartus, SDN Software Technology and Team • Beijing Huawei Digital Technologies, Co. Ltd. • Caliopa NV • Centre for Integrated Photonics Ltd. • Chinasoft International Technology Services Ltd. • FutureWei Technologies, Inc. • HexaTier Ltd. • HiSilicon Optoelectronics Co., Ltd. • Huawei Device Co., Ltd. • Huawei Device (Dongguan) Co., Ltd. • Huawei Device (Hong Kong) Co., Ltd. • Huawei Enterprise USA, Inc. • Huawei Global Finance (UK) Ltd. • Huawei International Co. Ltd. • Huawei Machine Co., Ltd. • Huawei Marine • Huawei North America • Huawei Software Technologies, Co., Ltd. • Huawei Symantec Technologies Co., Ltd. • Huawei Tech Investment Co., Ltd. • Huawei Technical Service Co. Ltd. • Huawei Technologies Cooperative U.A. • Huawei Technologies Germany GmbH • Huawei Technologies Japan K.K. • Huawei Technologies South Africa Pty Ltd. • Huawei Technologies (Thailand) Co. • iSoftStone Technology Service Co., Ltd. • JV “Broadband Solutions” LLC • M4S N.V. • Proven Honor Capital Limited • PT Huawei Tech Investment • Shanghai Huawei Technologies Co., Ltd. -

Hersteller Gerät JT Slimcase Neoprene JT
Bitte suchen Sie nach Ihrem Gerät. Durch Anklicken der Artikelnummer gelangen Sie sofort zu dem Artikel oder Sie geben in der Suche "JT Berlin ARTIKELNUMMER" ein. Sollte Ihr Gerät nicht in dieser Liste enthalten sein, so finden Sie am Ende dieser Liste die Maßangaben unserer Taschen. Hersteller Gerät JT SlimCase JT SlimCase JT SlimCase JT SlimCase JT SlimCase JT SlimCase JT Softcase JT SoftCase Neoprene Leather Leather Wallet stone Premium Premium Neoprene Leather black cognac black cognac Acer Liquid E3 10001 10145 10013 10017 10136 10031 Acer Liquid E600 10014 10018 10136 10031 Acer Liquid E700 10014 10018 10136 10031 Acer Liquid Jade Plus 10003 10007 10141 10013 10017 10136 10031 Acer Liquid Jade S 10003 10007 10141 10013 10017 10136 10031 Acer Liquid Jade Z Plus 10003 10007 10141 10146 10013 10017 10136 10031 Acer Liquid M320 10002 10145 10012 10016 10136 10031 Acer Liquid S1 10032 Acer Liquid S1 Duo 10032 Acer Liquid Z220 10136 Acer Liquid Z320 10002 10145 10012 10016 10136 10031 Acer Liquid Z330 10002 10145 10012 10016 10136 10031 Acer Liquid Z410 10002 10145 10012 10016 10136 10031 Acer Liquid Z5 10003 10146 10013 10017 10136 10031 Acer Liquid Z500 10003 10007 10141 10146 10013 10017 10136 10031 Acer Liquid Z520 Hersteller Gerät JT SlimCase JT SlimCase JT SlimCase JT SlimCase JT SlimCase JT SlimCase JT Softcase JT SoftCase Neoprene Leather Leather Wallet stone Premium Premium Neoprene Leather black cognac black cognac Acer Liquid Z530 10003 10007 10141 10146 10013 10017 10136 10031 Acer Liquid Z530S 10003 10007 10141 10146 10013 -

TCL 科技集团股份有限公司 TCL Technology Group Corporation
TCL Technology Group Corporation Annual Report 2019 TCL 科技集团股份有限公司 TCL Technology Group Corporation ANNUAL REPORT 2019 31 March 2020 1 TCL Technology Group Corporation Annual Report 2019 Table of Contents Part I Important Notes, Table of Contents and Definitions .................................................. 8 Part II Corporate Information and Key Financial Information ........................................... 11 Part III Business Summary .........................................................................................................17 Part IV Directors’ Report .............................................................................................................22 Part V Significant Events ............................................................................................................51 Part VI Share Changes and Shareholder Information .........................................................84 Part VII Directors, Supervisors, Senior Management and Staff .......................................93 Part VIII Corporate Governance ..............................................................................................113 Part IX Corporate Bonds .......................................................................................................... 129 Part X Financial Report............................................................................................................. 138 2 TCL Technology Group Corporation Annual Report 2019 Achieve Global Leadership by Innovation and Efficiency Chairman’s -
Inside Android's Safetynet Attestation: Attack and Defense ●
Inside Android’s SafetyNet Attestation Collin Mulliner & John Kozyrakis About Dr.-Ing. Collin Mulliner John Kozyrakis [email protected] [email protected] @collinrm @ikoz Independent Security Researcher Applied Research Lead, Mobile, Synopsys SIG R&D Mobile Security since 1999 6y+ Security Consultant @ Cigital Worked on: J2ME, PalmOS, Symbian, Windows Mobile app protection design & testing for several Mobile, iOS and Android Security. Co-authored large US & UK orgs ‘The Android Hacker’s Handbook’, built an Mobile static & dynamic analysis tools Android-based device. ● Mobile App Security ● SafetyNet & Attestation Agenda ● Developer's Perspective ● Bypassing SafetyNet ● Conclusions & Future Rooting & root detection Mobile App Security ● App is the gateway to the service ○ More so if mobile first or mobile only (and no public APIs) ● Data displayed & managed by app ○ User is allowed to see content in the app but isn’t allowed to copy it Mobile App Security protects: Service, Revenue, Brand, User / Customer Rooting ● Why attack a mobile app? ○ Analyse internals, use enrolled identity, disable security controls, use low-level APIs etc ● Having the ability to escalate the privileges of a process to “root” ○ Regain full control over device ○ Just one step towards attacking apps ● Access any resource ○ Take screenshot, debug any app, instrument process ● Read / Write any file ○ Read private app data ● Modify OS and software framework ○ API returns different result Highly dependent on Android version due to SELinux (longer discussion…) Attack patterns -

Step 1(To Be Performed on Your Google Pixel 2 XL)
For a connection between your mobile phone and your Mercedes-Benz hands-free system to be successful, Bluetooth® must be turned on in your mobile phone. Please make sure to also read the operating and pairing instructions of the mobile phone. Please follow the steps below to connect your mobile phone Google Pixel 2 XL with the mobile phone application of your Mercedes-Benz hands-free system using Bluetooth®. Step 1(to be performed on your Google Pixel 2 XL) Step 2 To get to the telephone screen of your Mercedes-Benz hands-free system press the Phone icon on the homescreen. Step 3 Select the Phone icon in the lower right corner. Step 4 Select the “Connect a New Device” application. Page 1 of 3 Step 5 Select the “Start Search Function” Step 6 The system will now search for any Bluetooth compatible phones. This may take some time depending on how many devices are found by the system. Step 7 Once the system completes searching select your mobile phone (example "My phone") from the list. Step 8 The pairing process will generate a 6-digit passcode and display it on the screen. Verify that the same 6 digits are shown on the display of your phone. Step 9 (to be performed on your Google Pixel 2 XL) There will be a pop-up "Bluetooth Request: 'MB Bluetooth' would like to pair with your phone. Confirm that the code '### ###' is shown on 'MB Bluetooth'. " Select "Pair" on your phone if the codes match. Page 2 of 3 Step 10 After the passcode is verified on both the mobile and the COMAND, the phone will begin to be authorized. -

TIMWE – Born Global Firm Case Study
CATÓLICA-LISBON, SCHOOL OF BUSINESS & ECONOMICS TIMWE – Born Global Firm Case Study Frederico José Castro Reis Marques December 2012 A Dissertation submitted in partial fulfillment of the requirements for the degree of MSc in Business Administration, at CLSBE – Católica-Lisbon, School of Business & Economics. ABSTRACT Title: TIMWE – Born Global Firm Author: Frederico José Castro Reis Marques TIMWE is the Portuguese based company chosen to illustrate and serve as background to support the creation of a teaching case in Strategy, exploring the internationalization of a real company and the challenges undertaken by the process of being a born global firm, followed by a Teaching Note that can be used as a tool to help solving the case. TIMWE is a Portuguese owned company, founded in 2002, that offers mobile monetization solutions and services (entertainment, marketing and money) to its global clients (brands, end-consumers, media groups, mobile carriers and governments), by leveraging its in- house developed intellectual proprietary technology, wide network of connections, mobile expertise and local presence. The main focus of the business strategy always has been B2O (business-to-operators), and since the beginning of its foundation the company aimed to build a global reach. In 2011, it had 26 offices, employing more than 300 people, operating in 75 countries across the 5 continents, as well as partnerships with over 280 mobile carriers spread all over the world giving access to 3 billion mobile subscribers. The case was prepared with the intent of providing useful insights about an IT services Portuguese company that managed to internationalize and operate in several countries, on top of giving a generic overview of the industry where it acts and is doing business.