Should I Renew My Mcafee Subscription
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Mcafee Epolicy Orchestrator DATA SHEET
DATA SHEET McAfee ePolicy Orchestrator Centrally get, visualize, share, and act on security insights Security management requires cumbersome juggling between tools and data. This puts the adversary at an advantage by offering more time to exploit the gap not seen between the tools and do damage. In addition, the cybersecurity workforce is limited and needs to be empowered to manage cybersecurity complexity. The McAfee® ePolicy Orchestrator® (McAfee ePO™) management platform removes the time-consuming and potential human error effort and inspires those responsible to manage security quicker and with higher efficacy. Fundamental Security Proven Advanced Security Management Start with the fundamentals. Core to any security More than 30,000 businesses and organizations trust architecture is the ability to monitor and control the the McAfee ePO console to manage security, streamline health of endpoints and systems. Industry standards and automate compliance processes, and increase such as Center for Internet Security (CIS) Controls and overall visibility across endpoint, network, and security National Institute of Standards Technology (NIST) SP operations. Big companies rely on the McAfee ePO 800 153 security and privacy controls call this out as console’s highly scalable architecture, allowing large a must. The McAfee ePO console allows you to gain enterprises to manage hundreds and thousands of critical visibility and set and automatically enforce nodes from a single console. The McAfee ePO console policies to ensure a healthy security posture across provides an enterprise security administrator with the your enterprise. Policy management and enforcement opportunity to simplify policy maintenance, pull in third- across security products for your entire enterprise party threat intelligence leveraging Data Exchange Layer is accomplished from a single console, removing the (DXL), and integrate policies bi-directionally with an array complexity of managing multiple products. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -
Debloating Software Through Piece-Wise Compilation and Loading
Debloating Software through Piece-Wise Compilation and Loading Anh Quach and Aravind Prakash, Binghamton University; Lok Yan, Air Force Research Laboratory https://www.usenix.org/conference/usenixsecurity18/presentation/quach This paper is included in the Proceedings of the 27th USENIX Security Symposium. August 15–17, 2018 • Baltimore, MD, USA ISBN 978-1-939133-04-5 Open access to the Proceedings of the 27th USENIX Security Symposium is sponsored by USENIX. Debloating Software through Piece-Wise Compilation and Loading Anh Quach Aravind Prakash Binghamton University Binghamton University [email protected] [email protected] Lok Yan Air Force Research Laboratory [email protected] Abstract This extraneous code may contain its own bugs and vulnerabilities and therefore broadens the overall attack Programs are bloated. Our study shows that only 5% of surface. Additionally, these features add unnecessary libc is used on average across the Ubuntu Desktop envi- burden on modern defenses (e.g., CFI) that do not dis- ronment (2016 programs); the heaviest user, vlc media tinguish between used and unused features in software. player, only needed 18%. Accumulation of unnecessary code in a binary – either In this paper: (1) We present a debloating framework by design (e.g., shared libraries) or due to software devel- built on a compiler toolchain that can successfully de- opment inefficiencies – amounts to code bloating. As a bloat programs (shared/static libraries and executables). typical example, shared libraries are designed to contain Our solution can successfully compile and load most li- the union of all functionality required by its users. braries on Ubuntu Desktop 16.04. -

Q3 Consumer Endpoint Protection Jul-Sep 2020
HOME ANTI- MALWARE PROTECTION JUL - SEP 2020 selabs.uk [email protected] @SELabsUK www.facebook.com/selabsuk blog.selabs.uk SE Labs tested a variety of anti-malware (aka ‘anti-virus’; aka ‘endpoint security’) products from a range of well-known vendors in an effort to judge which were the most effective. Each product was exposed to the same threats, which were a mixture of targeted attacks using well-established techniques and public email and web-based threats that were found to be live on the internet at the time of the test. The results indicate how effectively the products were at detecting and/or protecting against those threats in real time. 2 Home Anti-Malware Protection July - September 2020 MANAGEMENT Chief Executive Officer Simon Edwards CONTENTS Chief Operations Officer Marc Briggs Chief Human Resources Officer Magdalena Jurenko Chief Technical Officer Stefan Dumitrascu Introduction 04 TEstING TEAM Executive Summary 05 Nikki Albesa Zaynab Bawa 1. Total Accuracy Ratings 06 Thomas Bean Solandra Brewster Home Anti-Malware Protection Awards 07 Liam Fisher Gia Gorbold Joseph Pike 2. Threat Responses 08 Dave Togneri Jake Warren 3. Protection Ratings 10 Stephen Withey 4. Protection Scores 12 IT SUPPORT Danny King-Smith 5. Protection Details 13 Chris Short 6. Legitimate Software Ratings 14 PUBLICatION Sara Claridge 6.1 Interaction Ratings 15 Colin Mackleworth 6.2 Prevalence Ratings 16 Website selabs.uk Twitter @SELabsUK 6.3 Accuracy Ratings 16 Email [email protected] Facebook www.facebook.com/selabsuk 6.4 Distribution of Impact Categories 17 Blog blog.selabs.uk Phone +44 (0)203 875 5000 7. -
Consumer Security Products Performance Benchmarks (Edition 2) Antivirus & Internet Security Windows 10
Consumer Security Products Performance Benchmarks (Edition 2) Antivirus & Internet Security Windows 10 January 2020 Document: Consumer Security Products Performance Benchmarks (Edition 2) Authors: J. Han, D. Wren Company: PassMark Software Date: 13 January 2020 Edition: 2 File: Consumer_Security_Products_Performance_Benchmarks_2020_Ed_2.docx Consumer Security Performance Benchmarks 2019 PassMark Software Table of Contents TABLE OF CONTENTS ......................................................................................................................................... 2 REVISION HISTORY ............................................................................................................................................ 3 REFERENCES ...................................................................................................................................................... 3 EXECUTIVE SUMMARY ...................................................................................................................................... 4 OVERALL SCORE ................................................................................................................................................ 5 PRODUCTS AND VERSIONS ............................................................................................................................... 6 PERFORMANCE METRICS SUMMARY ................................................................................................................ 7 TEST RESULTS ................................................................................................................................................ -

Ten Strategies of a World-Class Cybersecurity Operations Center Conveys MITRE’S Expertise on Accumulated Expertise on Enterprise-Grade Computer Network Defense
Bleed rule--remove from file Bleed rule--remove from file MITRE’s accumulated Ten Strategies of a World-Class Cybersecurity Operations Center conveys MITRE’s expertise on accumulated expertise on enterprise-grade computer network defense. It covers ten key qualities enterprise- grade of leading Cybersecurity Operations Centers (CSOCs), ranging from their structure and organization, computer MITRE network to processes that best enable effective and efficient operations, to approaches that extract maximum defense Ten Strategies of a World-Class value from CSOC technology investments. This book offers perspective and context for key decision Cybersecurity Operations Center points in structuring a CSOC and shows how to: • Find the right size and structure for the CSOC team Cybersecurity Operations Center a World-Class of Strategies Ten The MITRE Corporation is • Achieve effective placement within a larger organization that a not-for-profit organization enables CSOC operations that operates federally funded • Attract, retain, and grow the right staff and skills research and development • Prepare the CSOC team, technologies, and processes for agile, centers (FFRDCs). FFRDCs threat-based response are unique organizations that • Architect for large-scale data collection and analysis with a assist the U.S. government with limited budget scientific research and analysis, • Prioritize sensor placement and data feed choices across development and acquisition, enteprise systems, enclaves, networks, and perimeters and systems engineering and integration. We’re proud to have If you manage, work in, or are standing up a CSOC, this book is for you. served the public interest for It is also available on MITRE’s website, www.mitre.org. more than 50 years. -

Release Notes
ESAP 2.6.2 Release Notes SDK Version: Mac and Windows 3.6.9026.2 (V2 Unified + V3) Noteworthy changes: Starting ESAP 2.6.1, each release contains additional files in preparation of new features that will be enabled in the next major release of SA and IC. ESAP 2.6.2 and Junos Pulse Secure Access/Access Control Service Compatibility Chart: This ESAP package can be installed on the following Junos Pulse Secure Access/Access Control Service software versions. o SA 8.0Rx o SA 7.4Rx o SA 7.3Rx o SA 7.2Rx o SA 7.1Rx o SA 7.0Rx o SA 6.5Rx o UAC 5.0Rx o UAC 4.4Rx o UAC 4.3Rx o UAC 4.2Rx o UAC 4.1Rx o UAC 4.0Rx o UAC 3.1Rx Note: The ESAP package may install and function without any errors on older releases however as the install has not been tested, we recommend that it be used only on the above versions of software releases. Support has been added for the following products in ESAP2.6.2 Windows OS Antivirus Products [Comodo Group] COMODO Antivirus (7.x) [McAfee, Inc.] McAfee Endpoint Security Threat Prevention (10.x) [Trend Micro, Inc.] Trend Micro Worry Free Business Security Agent (19.x) Antispyware Products [Comodo Group] COMODO Antivirus (7.x) [McAfee, Inc.] McAfee Endpoint Security Threat Prevention (10.x) [Trend Micro, Inc.] Trend Micro Worry Free Business Security Agent (19.x) Firewall Products [Comodo Group] COMODO Firewall (7.x) [McAfee, Inc.] McAfee Endpoint Security Firewall (10.x) [Trend Micro, Inc.] Trend Micro Worry Free Business Security Agent (19.x) Mac OS Antivirus Products [F-Secure Corp.] F-Secure Anti-Virus for Mac (0.x) Support has been removed for the following products in ESAP2.6.2 Mac OS Antivirus Products [SPAMfighter] VIRUSfighter (7.x) Issues Fixed in ESAP2.6.2 OPSWAT issues fixed: 1. -

EXABEAM SECURITY MANAGEMENT PLATFORM INTEGRATIONS Inbound Data Sources for Log Ingestion and Service Integrations for Incident Response
EXABEAM SECURITY MANAGEMENT PLATFORM INTEGRATIONS Inbound Data Sources for Log Ingestion and Service Integrations for Incident Response The more data sources you have in your security incident and event management (SIEM), the better equipped you are to detect attacks. And the more security orchestration and automation response (SOAR) connections you have between your SIEM and your IT and security systems the quicker LIMITLESS SCALE WITH FLAT, PREDICTABLE PRICING you can respond. Every log and every security event matters. Not retaining your log data can create security blinds spots that prevent Exabeam Security Management Platform (SMP) has compliance or leave your organization vulnerable to attack. approximately 350 integrations with IT and security products Exabeam is designed to scale without penalizing you for the to help your analysts work smarter - providing inbound amount of data you ingest. Our flat pricing model is based integrations with data sources from vendors to easily on the number of users and devices in your environment, allow you to ingest as much data as possible; and SOAR not data volume. integrations with 3rd party vendors to help you automate and orchestrate your security response. CENTRALIZED SECURITY AUTOMATION AND ORCHESTRATION WITH 3RD PARTY INTEGRATIONS EXTENSIVE DATA SOURCES Exabeam Incident Responder integrates with approximately Exabeam ingests data from approximately 300 different 70 third party IT and security products. These integrations IT and security products to provide security analysts with help your analysts to gather evidence and attach them as the full scope of events. Exabeam Data Lake, Exabeam artifacts to incidents or quarantine affected users and assets Advanced Analytics and Exabeam Entity Analytics ingest logs until incidents are mitigated. -

What Are Kernel-Mode Rootkits?
www.it-ebooks.info Hacking Exposed™ Malware & Rootkits Reviews “Accessible but not dumbed-down, this latest addition to the Hacking Exposed series is a stellar example of why this series remains one of the best-selling security franchises out there. System administrators and Average Joe computer users alike need to come to grips with the sophistication and stealth of modern malware, and this book calmly and clearly explains the threat.” —Brian Krebs, Reporter for The Washington Post and author of the Security Fix Blog “A harrowing guide to where the bad guys hide, and how you can find them.” —Dan Kaminsky, Director of Penetration Testing, IOActive, Inc. “The authors tackle malware, a deep and diverse issue in computer security, with common terms and relevant examples. Malware is a cold deadly tool in hacking; the authors address it openly, showing its capabilities with direct technical insight. The result is a good read that moves quickly, filling in the gaps even for the knowledgeable reader.” —Christopher Jordan, VP, Threat Intelligence, McAfee; Principal Investigator to DHS Botnet Research “Remember the end-of-semester review sessions where the instructor would go over everything from the whole term in just enough detail so you would understand all the key points, but also leave you with enough references to dig deeper where you wanted? Hacking Exposed Malware & Rootkits resembles this! A top-notch reference for novices and security professionals alike, this book provides just enough detail to explain the topics being presented, but not too much to dissuade those new to security.” —LTC Ron Dodge, U.S. -

Mcafee Virusscan Enterprise Protect Your Desktops and File Servers from Malicious Threats
DATA SHEET McAfee VirusScan Enterprise Protect your desktops and file servers from malicious threats Keeping networks free from a wide range of threats—viruses, worms, rootkits, and Trojans— Key Advantages is more challenging than ever. Whether your organization is a global enterprise with full-time security staff or a small or medium-size business, McAfee® VirusScan® Enterprise software Unbeatable malware detection and removal ensures that your endpoint servers, desktops, and laptops remain free from malware. Protect your files from viruses, worms, rootkits, Trojans, and other threats. McAfee VirusScan Enterprise software combines techniques. With port blocking, file-name blocking, antivirus, antispyware, firewall, and intrusion prevention folder/directory lockdown, file share lockdown, and Proactive protection from zero- technologies to proactively detect and remove malware. infection trace and block, you can stop many new and day attacks Proactive protection against new It reduces the cost of managing outbreak responses, unknown malware files cold. and unknown buffer-overflow stops zero-day threats, and mitigates the window of Proactive Protection from Attacks exploits that target vulnerabilities in vulnerability—the time between the discovery of a Microsoft applications vulnerability and when fixes are deployed. Plus, with McAfee VirusScan Enterprise software is the industry’s first anti-malware software to offer patented intrusion Leverage McAfee GTI McAfee VirusScan Enterprise software, you have The worldwide presence of McAfee prevention with application-specific buffer-overflow the flexibility to detect and block malware based on Labs enables McAfee VirusScan your business needs: on access, on demand, or on a technology. Now, you can protect your users Enterprise software to leverage schedule. -

Mcafee Epolicy Orchestrator Inspiring and Empowering the Security Professional
DATA SHEET McAfee ePolicy Orchestrator Inspiring and empowering the security professional Security management requires cumbersome juggling between tools and data, often with Key Advantages limited visibility into external threats. This puts the adversary at an advantage by having ■ Industry-acclaimed centralized more time to exploit the gaps not seen between the tools so they can do more damage. management with unique, The cybersecurity workforce is limited and needs to be empowered to simply orchestrate integrated single pane of glass for complex cybersecurity environments. They need to be less reactive and become more great simplicity—available from the cloud or on premises proactive to get ahead of adversaries. ■ Proactive actionable intelligence to get ahead of the adversary Your organization needs to respond quickly to threats on any type of device to minimize ■ Automated workflows to the damage and when upper management demands evidence of security effectiveness. streamline administrative duties The McAfee® ePolicy Orchestrator® (McAfee ePO™) management platform—available and achieve higher efficiency ■ Open and comprehensive platform on premises and from the cloud (with two models to choose from: SaaS or IaaS)—helps integrates McAfee and more than eliminate the time-consuming effort and potential for human error. It also helps those 150 third-party solutions for faster and more accurate responses responsible for managing security respond proactively, faster, and with higher efficacy. ■ Common security management for ® Unique to the McAfee ePO console is McAfee MVISION Insights, the first technology the largest share of devices on the to proactively prioritize threats and campaigns before they hit you, predict if your market ■ Leverages and enhances native countermeasures can withhold the threat, and prescribe what you need to do to counter controls built into operating the threat concurrently. -
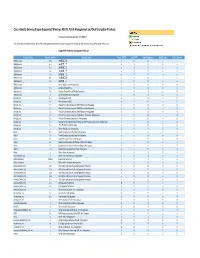
Cisco Identity Services Engine Supported Windows AV/AS/PM/DE
Cisco Identity Services Engine Supported Windows AS/AV, Patch Management and Disk Encryption Products Compliance Module Version 3.6.10363.2 This document provides Windows AS/AV, Patch Management and Disk Encryption support information on the the Cisco AnyConnect Agent Version 4.2. Supported Windows Antispyware Products Vendor_Name Product_Version Product_Name Check_FSRTP Set_FSRTP VirDef_Signature VirDef_Time VirDef_Version 360Safe.com 10.x 360安全卫士 vX X v v 360Safe.com 4.x 360安全卫士 vX X v v 360Safe.com 5.x 360安全卫士 vX X v v 360Safe.com 6.x 360安全卫士 vX X v v 360Safe.com 7.x 360安全卫士 vX X v v 360Safe.com 8.x 360安全卫士 vX X v v 360Safe.com 9.x 360安全卫士 vX X v v 360Safe.com x Other 360Safe.com Antispyware Z X X Z X Agnitum Ltd. 7.x Outpost Firewall Pro vX X X O Agnitum Ltd. 6.x Outpost Firewall Pro 2008 [AntiSpyware] v X X v O Agnitum Ltd. x Other Agnitum Ltd. Antispyware Z X X Z X AhnLab, Inc. 2.x AhnLab SpyZero 2.0 vv O v O AhnLab, Inc. 3.x AhnLab SpyZero 2007 X X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2007 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2008 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2009 Platinum AntiSpyware v v O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 7.0 Platinum Enterprise AntiSpyware v X O v O AhnLab, Inc. 8.x AhnLab V3 Internet Security 8.0 AntiSpyware v v O v O AhnLab, Inc.