A Cipher Based on the Random Sequence of Digits in Irrational Numbers
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6 -
Stream Ciphers) Ppfdrof
CS-630: Cyyyber and Network Security Lecture # 2: Introduction to Cryptography and Symmetric Ciphers (Stream Ciphers) PPfDrof. Dr. SSfiufian HHdameed Department of Computer Science FAST-NUCES FAST-NUCES Cryptog rap hy FAST-NUCES Examples FAST-NUCES Cryptosystem FAST-NUCES Attacks against Cryptosystems 1.))p Cipher text-only: Attacker ppgypossesses a string y of the cipher text 2. ) Known plaintext: Attacker possesses a string x of the plaintext and the corresponding cipher text y. The problem now is to find out the key which produces y from x 3.) Chosen plaintext: Attacker has access to the encryption machinery. Hence he can chose a plaintext string x and construct the corre spondi ng ci phe r te xt st ri ng y. 4.))p Chosen cipher text: Attacker has access to the decryption machinery. Hence, he can chose a cipher text string y and construct the corresponding plaintext string x. FAST-NUCES Security of Keys FAST-NUCES Cryptography is everywhere Secure communication: y web traffic: HTTPS y wireless traffic: 802.11i WPA2 (and WEP), GSM, Bluetooth EtiEncrypting files on dis k: y EFS (Encrypting File System) y TrueCrypt (open-source disk encryption software) Content protection y DVD --- Content Scramble System (CSS) is a Digital Rights Managg()ement (DRM) and encryp ypytion system em pyployed on almost all commercially produced DVD-Video y Easy to break y Blu-Ray --- Advance Access Content System (AACS) User authentication … and much much more FAST-NUCES Things to remember Cryptography is: y A tremendous tool y The basis for many security mechanisms -

A Hybrid Cryptosystem Based on Vigenère Cipher and Columnar Transposition Cipher
International Journal of Advanced Technology & Engineering Research (IJATER) www.ijater.com A HYBRID CRYPTOSYSTEM BASED ON VIGENÈRE CIPHER AND COLUMNAR TRANSPOSITION CIPHER Quist-Aphetsi Kester, MIEEE, Lecturer Faculty of Informatics, Ghana Technology University College, PMB 100 Accra North, Ghana Phone Contact +233 209822141 Email: [email protected] / [email protected] graphy that use the same cryptographic keys for both en- Abstract cryption of plaintext and decryption of cipher text. The keys may be identical or there may be a simple transformation to Privacy is one of the key issues addressed by information go between the two keys. The keys, in practice, represent a Security. Through cryptographic encryption methods, one shared secret between two or more parties that can be used can prevent a third party from understanding transmitted raw to maintain a private information link [5]. This requirement data over unsecured channel during signal transmission. The that both parties have access to the secret key is one of the cryptographic methods for enhancing the security of digital main drawbacks of symmetric key encryption, in compari- contents have gained high significance in the current era. son to public-key encryption. Typical examples symmetric Breach of security and misuse of confidential information algorithms are Advanced Encryption Standard (AES), Blow- that has been intercepted by unauthorized parties are key fish, Tripple Data Encryption Standard (3DES) and Serpent problems that information security tries to solve. [6]. This paper sets out to contribute to the general body of Asymmetric or Public key encryption on the other hand is an knowledge in the area of classical cryptography by develop- encryption method where a message encrypted with a reci- ing a new hybrid way of encryption of plaintext. -

Grade 6 Math Circles Cryptography Solutions Atbash Cipher Caesar Cipher
Faculty of Mathematics Centre for Education in Waterloo, Ontario N2L 3G1 Mathematics and Computing Grade 6 Math Circles November 5/6 2019 Cryptography Solutions Hello World Khoor Zruog Hello Zruog Khoor Khoor Zruog World 1. Person A encrypts plaintext 2. Person B receives ciphertext 3. Person B decrypts ciphertext back into ciphertext into plaintext Atbash Cipher Examples 1. Encrypt \Math Circles" using the Atbash cipher. Nzgs Xrixovh 2. Decrypt \ORLM PRMT" using the Atbash cipher. LION KING Caesar Cipher Examples: Encrypt or decrypt the following messages using the shift number given in parentheses: a) Welcome to Math Circles! (5) Bjqhtrj yt Rfym Hnwhqjx! plaintext A B C D E F G H I J K L M N O P Q R S T U V W X Y Z ciphertext F G H I J K L M N O P Q R S T U V W X Y Z A B C D E 1 b) Ljw hxd anjm cqrb? (9) Can you read this? plaintext A B C D E F G H I J K L M N O P Q R S T U V W X Y Z ciphertext J K L M N O P Q R S T U V W X Y Z A B C D E F G H I c) What if I did a Caesar Shift of 26 units on \Welcome to Math Circles!"? A Caesar shift of 26 would be shifting by the length of the alphabet. For example I would be shifting A 26 letters to the right. -

Breaking Transposition Cipher with Genetic Algorithm
Breaking Transposition Cipher with Genetic Algorithm C.Obi Reddy, National University of Singapore(NUS), ECE Department, [email protected] Abstract: In recent years a number of example total number of letters is 20 optimisation algorithms have emerged which is regular case with the key order of which have proven to be effective in 5. If the plain text is irregular then solving a variety of NP-complete padding of X is done at the tail of the text problems. In this paper an example the to make it regular. kind in cryptanalysis, breaking of Encryption of plain text is done as follows transposition cipher using a heuristic genetic algorithm is presented. Regular: Plain 1 2 3 4 5 Introduction: Text In the Brute Force attack the attacker Key 1 4 2 5 3 tries every possible (k! Keys) key on a T H I S I piece of cipher text until an intelligible S A S I M translation into plaintext is obtained. P L E M E Many types of classical ciphers exist, S S A G E although most fall into one of two broad categories: substitution ciphers and Cipher Text: TSPS ISEA IMEE HALS SIMG transposition ciphers. In the former one, every plaintext character is substituted by Irregular: a cipher character, using a substitution Plain 1 2 3 4 5 alphabet, and in the latter one, plaintext Text characters are permuted using a Key 1 4 2 5 3 predetermined permutation. T H I S I S A S I M Transposition cipher works by breaking P L E M E the plain text in to fixed number of blocks S S A G E and then shuffling the characters in each block according to the agreed key K. -
General Solution for the Adfgvx Cipher System
10 Feb 61 FILE OR From File of Special Consultant (Friedman) SERIAL neral Solution for the ADFGVX Cipher System NUMBER Register No. 129 AND Serial No. 1010 SUBJECT NAME AND EXTENSION OF PERSON REQUESTING FILE ORGANIZATION, B TO Mr. William Friedman LI 6-8520 10 2nd. Str., SE, Wash., D. C. DATE RET'ND. INITIAL HERE RETURN To Mrs. Christian, AG-24, HSA, Ft. Geo. G. Meade Mdo WHEN TRANSFERRING FILE TO ANOTHER PERSON, COMPLET'""1ELF·ADDRESSED TRANSFER COUPON BELOW, DETACH, STITCH TO BLANK INSTRUCTIONS LETTER·SIZE PAPER AND PLACE IN OUT·GOING MAIL SERVIC -· 2ND TRANSFER COUPON Declassified and approved for release by NSA on 05-06-2014 pursuant to E.O. 1352a Co1alidential Register No. 1 2 9 WAR DEPARTMENT OFFICE THE cmEI' SIGNAL OFVICD 1·',' or W .lSBINGTQll I GENERAL SOLUTION FOR THB I ADFGVX CIPHER SYSTEM I. *!~ ,. : i~ ' ·!, ------------~--==....;..'"-=='.,,.;'*: 30 April 1959 ftl• 4oc,_at 18 :re~4 •a<mrIDnUAL•·typ ot JMI> ~tive 52()0.l 4&~ 8 J~.1957, u4 117 "thant1 qr: the Jtirectar, laticllal a.nmv·: AceDt:J' • . ' ... ' 4JJ!fl/~ .; ~':j_ S. W1J.lt.r4 . ! ColCMl, .AOC • ! AclJutut GeMnl. --·-··-··--- --· Classification chanr,ed to R68!1'1G6'Pli8 By Authority ot · HAP.CL:J G4 HAY"-:S, Col<! , Siena! Corps Actin~ Chief, Arm.y Sepurity A~cncy B y :·iA:.JCN G. CA "'PR:::tL1 1st Lt,., Si~ 1 April 1946• . NO ACCOUNTltll t!MCESSARJ Rt:GlSTRAnON CAJJCELED, b7 . Authority Hqs. ASA ltr dated 27 Feb 46 2d Ind 11 l~r 46, signed: - HAROLD G .. HAYES, Col.Ji Sir.mtl Corps Aetin.1; Ch!Pf t Ar?!W S~1:1:ri~y Afen·:y ~::t::ii. -
Lecture 2: Classical Cryptography
Lecture 2: Classical Cryptography Data and Information Management: ELEN 3015 School of Electrical and Information Engineering, University of the Witwatersrand Introduction Monoalphabetic Cipher - Frequency analysis Classical Ciphers Other Substitution Ciphers Transposition ciphers Stream vs Block Enciphering 1. Homework hqfubswlrq lv d phdqv ri dwwdlqlqj vhfxuh frpsxwdwlrq ryhu lqvhfxuh fkdqqhov eb xvlqj hqfubswlrq zh glvjxlvh wkh phvvdjh vr wkdw hyhq li wkh wudqvplvvlrq lv glyhuwhg wkh phvvdjh zloo qrw eh uhyhdohg 1. Monoalphabetic Cipher - Frequency analysis Do a frequency analysis Letter distribution of English language is fixed (for a large body of text) Tables of letter distribution For instance, most commonly used letter is \e" 1. Monoalphabetic Cipher - Frequency analysis 1. Monoalphabetic Cipher - Answer ENCRYPTION IS A MEANS OF ATTAINING SECURE COMMUNICATION OVER INSECURE CHANNELS BY USING ENCRYPTION WE DISGUISE THE MESSAGE SO THAT EVEN IF THE TRANSMISSION IS DIVERTED THE MESSAGE WILL NOT BE REVEALED 2. Classical Ciphers How do we increase security of the monoalphabetic cipher? 3. Polyalphabetic ciphers Use more than one alphabetic substitution to flatten the frequency distribution Combine substitutions that are high with those that are low Eg use: • P1(a) = (a*3)mod26 • P2(a) = ((5*a)+13)mod26 3. Polyalphabetic ciphers Cipher I: ABCDEFG ::: STUVWXYZ a d g j m p s ::: c f i l o r u x Cipher II: ABCDEFG ::: STUVWXYZ n s x c h m r ::: z e j o t y d i 3. Polyalphabetic ciphers - Frequency distribution 3. Vigenere tables a b c d e f ::: t u v w x y z π A a b c d e f ::: t u v w x y z 0 B b c d e f g ::: u v w x y z a 1 C c d e f g h ::: v w x y z a b 2 . -

Transposition Cipher in Cryptography, a Transposition Cipher Is a Method of Encryption by Which the Positions Held by Units of P
Transposition cipher In cryptography, a transposition cipher is a method of encryption by which the positions held by units of plaintext (which are commonly characters or groups of characters) are shifted according to a regular system, so that the ciphertext constitutes a permutation of the plaintext. That is, the order of the units is changed. Mathematically a bijective function is used on the characters' positions to encrypt and an inverse function to decrypt. Following are some implementations. Contents • 1 Rail Fence cipher • 2 Route cipher • 3 Columnar transposition • 4 Double transposition • 5 Myszkowski transposition • 6 Disrupted transposition • 7 Grilles • 8 Detection and cryptanalysis • 9 Combinations • 10 Fractionation Rail Fence cipher The Rail Fence cipher is a form of transposition cipher that gets its name from the way in which it is encoded. In the rail fence cipher, the plaintext is written downwards on successive "rails" of an imaginary fence, then moving up when we get to the bottom. The message is then read off in rows. For example, using three "rails" and a message of 'WE ARE DISCOVERED. FLEE AT ONCE', the cipherer writes out: W . E . C . R . L . T . E . E . R . D . S . O . E . E . F . E . A . O . C . A . I . V . D . E . N . Then reads off: WECRL TEERD SOEEF EAOCA IVDEN (The cipherer has broken this ciphertext up into blocks of five to help avoid errors.) Route cipher In a route cipher, the plaintext is first written out in a grid of given dimensions, then read off in a pattern given in the key. -
An Introduction to Cryptography, Second Edition Richard A
DISCRETE MATHEMATICS AND ITS APPLICATIONS Series Editor KENNETH H. ROSEN An INTRODUCTION to CRYPTOGRAPHY Second Edition © 2007 by Taylor & Francis Group, LLC DISCRETE MATHEMATICS and ITS APPLICATIONS Series Editor Kenneth H. Rosen, Ph.D. Juergen Bierbrauer, Introduction to Coding Theory Kun-Mao Chao and Bang Ye Wu, Spanning Trees and Optimization Problems Charalambos A. Charalambides, Enumerative Combinatorics Henri Cohen, Gerhard Frey, et al., Handbook of Elliptic and Hyperelliptic Curve Cryptography Charles J. Colbourn and Jeffrey H. Dinitz, The CRC Handbook of Combinatorial Designs Steven Furino, Ying Miao, and Jianxing Yin, Frames and Resolvable Designs: Uses, Constructions, and Existence Randy Goldberg and Lance Riek, A Practical Handbook of Speech Coders Jacob E. Goodman and Joseph O’Rourke, Handbook of Discrete and Computational Geometry, Second Edition Jonathan L. Gross and Jay Yellen, Graph Theory and Its Applications, Second Edition Jonathan L. Gross and Jay Yellen, Handbook of Graph Theory Darrel R. Hankerson, Greg A. Harris, and Peter D. Johnson, Introduction to Information Theory and Data Compression, Second Edition Daryl D. Harms, Miroslav Kraetzl, Charles J. Colbourn, and John S. Devitt, Network Reliability: Experiments with a Symbolic Algebra Environment Leslie Hogben, Handbook of Linear Algebra Derek F. Holt with Bettina Eick and Eamonn A. O’Brien, Handbook of Computational Group Theory David M. Jackson and Terry I. Visentin, An Atlas of Smaller Maps in Orientable and Nonorientable Surfaces Richard E. Klima, Neil P. Sigmon, and Ernest L. Stitzinger, Applications of Abstract Algebra with Maple™ and MATLAB®, Second Edition Patrick Knupp and Kambiz Salari, Verification of Computer Codes in Computational Science and Engineering William Kocay and Donald L. -
History of Cryptography an EASY to UNDERSTAND HISTORY of CRYPTOGRAPHY Contents
History of Cryptography AN EASY TO UNDERSTAND HISTORY OF CRYPTOGRAPHY Contents 1. Introduction 3 2. Classical Encryptions (Ancient Times) 4 3. Classical Encryptions (Middle Ages) 6 The Cipher of Mary Queen of Scots 6 Vigenère Ciphers 6 Uesugi Cipher 7 4. Modern Ciphers: Ciphers during World War I and the Emergence of Encryption Machines 8 German Communication Cables Disconnected by the United Kingdom 8 Zimmermann Telegram 8 ADFGVX Cipher 8 The Birth of Enigma 9 5. Modern Ciphers: Encryptions in the Computer and Internet Era 10 DES Cipher 10 Public-Key Cryptosystem 10 RSA Cipher 11 Decrypting the DES Cipher 12 Responsive Action of Cipher Enhancements for SSL 12 6. The Future of Encryption 13 7. Conclusion: Enhancing the Effectiveness of Encryptions used for SSL 14 References 14 © 2013 Thawte, Inc. All rights reserved. Thawte, the thawte logo, and other trademarks, service marks, and designs are registered or unregistered trademarks of Thawte, 2 Inc. and its subsidiaries and affi liates in the United States and in foreign countries. All other trademarks are property of their respective owners. 1. Introduction ncryption and related technologies are widely and frequently Eused as a means of ensuring that information is secure, and their importance has been growing with the increasingly wide- spread utilization of the Internet. The use of encryption can be traced to as far back as about 3000 B.C., during the Babylonian Era. Encryption technologies evolved as they were used in military and political settings, but as a result of the recent widespread use of the Internet and the dramatic increase in the amount of information people come into contact in their daily lives, the settings in which encryption technologies are applied and implemented have increased, and they are now used all around us in our daily lives. -
Ecommunicator - Summer 2019
eCommunicator - Summer 2019 Journal of 32 Signal Regiment eCommunicator Volume 19, Number 1 http://www.torontosignals.ca/ In this issue of the eCommunicator Change of RCCS Beret Pg 17 Commanding Officer’s Parade Pg 16 New Unit Crest Pg 19 Junior Ranks Formal Pg 13 Table of Content About the eCommunicator 3 CO’s Message This is a limited domestic publication produced with 4 RSM’s Message the permission of the Commanding Officer for the purpose of recording the activities within the 5 Honouraries Message Regiment and the Regimental family. It is intended 7 Padre to provide a wide variety of material relating to military communications and military affairs, both Features at home and abroad. 8 Awards and Promotions The views and opinions expressed in this periodical 10 DWD — Warrant Officer Lee Whalen, CD are those of the contributors and not those of the 12 Associates Dinner Department of National Defence, its Units or 13 Junior Ranks Formal Officers, including the Commanding Officer of 32 15 CAF National Women’s Volleyball Championship Signal Regiment. 16 CO’s Parade The editor and publisher are responsible for the 17 Change of Beret Parade production of the eCommunicator but not for the 18 Garrison Ball accuracy, timeliness or description of written and 19 New Unit Crest graphical material published therein. 19 Royal Canadian Logistics Service Branch and RCEME Corps The editor reserves the right to modify or re-format 20 Technology Topic: Software-Defined Radio (SDR) material received, within reason, in order to make 22 709 Signals Army Cadet Corps best use of available space, appearance and layout. -
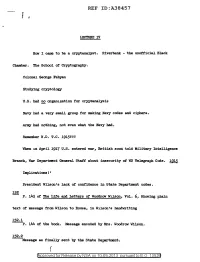
Lecture Iv; How I Came to Be a Cryptanalyst
REF ID:A38457 j I.l!X:TURE IV How I came to be a crypta.nal.yst. Riverbank - the unofficial Black Chamber. The School of Cryptography. Colonel George Fabyan Studying cryptology U.S. had !!2 organization for cryptanalysis Navy had a very small group for ma.king Navy codes and ciphers. Arm:/ had nothing, not even what the Navy had. Remember W.D. T.C. 1915!?? When in April. 1917 U.S. entered war, British soon told Military IntelJ.igence Branch, War Department General Staff about insecurity of WD Telegraph Code. ~ Implications! ' President Wil.son's lack of confidence in State Department codes. 152 P. 143 of The Life and Letters of Woodrow WJ.l.son, Vol. 6 1 Showing plain text of message from Wilson to House, in Wilson's handwriting 152.l P. 144 of the book. Message encoded by Mrs. Woodrow Wilson. 152.2 Message as f'inal..ly sent by the State Department. ( @'pp roved for Release by NSA on 10-09-2013 pursuantto E .0. 1352a REF ID:A38457 ill P. 316 of Woodrow Wilson's "Lif'e e.nd Letters", Vol 51 showing shorthand notes ma.de by Wil.son tor a tel.egram to Col.onel. Bouse. 153.l P. 317 of above showing President Wilson's transcription of the above message into code, done on his own typewriter. 153 2 Transcription into plain l.a.nguage on receipt. 212 Title :page of Manual for the Solution of Military Ciphers by Parker Hitt, 1916 (Things we studied.) J.69 Parker Hitt. Title page at An Advanced Problem in Cry;ptogra;phy and its Solution by Mauborgn.e.