Reference Manual CLI Command Line Interface EAGLE One Rel. 5.3.0, 09-2013
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Administering Unidata on UNIX Platforms
C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta UniData Administering UniData on UNIX Platforms UDT-720-ADMU-1 C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Notices Edition Publication date: July, 2008 Book number: UDT-720-ADMU-1 Product version: UniData 7.2 Copyright © Rocket Software, Inc. 1988-2010. All Rights Reserved. Trademarks The following trademarks appear in this publication: Trademark Trademark Owner Rocket Software™ Rocket Software, Inc. Dynamic Connect® Rocket Software, Inc. RedBack® Rocket Software, Inc. SystemBuilder™ Rocket Software, Inc. UniData® Rocket Software, Inc. UniVerse™ Rocket Software, Inc. U2™ Rocket Software, Inc. U2.NET™ Rocket Software, Inc. U2 Web Development Environment™ Rocket Software, Inc. wIntegrate® Rocket Software, Inc. Microsoft® .NET Microsoft Corporation Microsoft® Office Excel®, Outlook®, Word Microsoft Corporation Windows® Microsoft Corporation Windows® 7 Microsoft Corporation Windows Vista® Microsoft Corporation Java™ and all Java-based trademarks and logos Sun Microsystems, Inc. UNIX® X/Open Company Limited ii SB/XA Getting Started The above trademarks are property of the specified companies in the United States, other countries, or both. All other products or services mentioned in this document may be covered by the trademarks, service marks, or product names as designated by the companies who own or market them. License agreement This software and the associated documentation are proprietary and confidential to Rocket Software, Inc., are furnished under license, and may be used and copied only in accordance with the terms of such license and with the inclusion of the copyright notice. -
Process and Memory Management Commands
Process and Memory Management Commands This chapter describes the Cisco IOS XR software commands used to manage processes and memory. For more information about using the process and memory management commands to perform troubleshooting tasks, see Cisco ASR 9000 Series Aggregation Services Router Getting Started Guide. • clear context, on page 2 • dumpcore, on page 3 • exception coresize, on page 6 • exception filepath, on page 8 • exception pakmem, on page 12 • exception sparse, on page 14 • exception sprsize, on page 16 • follow, on page 18 • monitor threads, on page 25 • process, on page 29 • process core, on page 32 • process mandatory, on page 34 • show context, on page 36 • show dll, on page 39 • show exception, on page 42 • show memory, on page 44 • show memory compare, on page 47 • show memory heap, on page 50 • show processes, on page 54 Process and Memory Management Commands 1 Process and Memory Management Commands clear context clear context To clear core dump context information, use the clear context command in the appropriate mode. clear context location {node-id | all} Syntax Description location{node-id | all} (Optional) Clears core dump context information for a specified node. The node-id argument is expressed in the rack/slot/module notation. Use the all keyword to indicate all nodes. Command Default No default behavior or values Command Modes Administration EXEC EXEC mode Command History Release Modification Release 3.7.2 This command was introduced. Release 3.9.0 No modification. Usage Guidelines To use this command, you must be in a user group associated with a task group that includes appropriate task IDs. -

Technical Report (Open)SSH Secure Use Recommendations
DAT-NT-007-EN/ANSSI/SDE PREMIERMINISTRE Secrétariat général Paris, August 17, 2015 de la défense et de la sécurité nationale No DAT-NT-007-EN/ANSSI/SDE/NP Agence nationale de la sécurité Number of pages des systèmes d’information (including this page): 21 Technical report (Open)SSH secure use recommendations Targeted audience Developers Administrators X IT security managers X IT managers Users Document Information Disclaimer This document, written by the ANSSI, presents the “(Open)SSH secure use recom- mendations”. It is freely available at www.ssi.gouv.fr/nt-ssh. It is an original creation from the ANSSI and it is placed under the “Open Licence” published by the Etalab mission (www.etalab.gouv.fr). Consequently, its diffusion is unlimited and unrestricted. This document is a courtesy translation of the initial French document “Recommanda- tions pour un usage sécurisé d’(Open)SSH”, available at www.ssi.gouv.fr/nt-ssh. In case of conflicts between these two documents, the latter is considered as the only reference. These recommendations are provided as is and are related to threats known at the publication time. Considering the information systems diversity, the ANSSI cannot guarantee direct application of these recommendations on targeted information systems. Applying the following recommendations shall be, at first, validated by IT administrators and/or IT security managers. Document contributors Contributors Written by Approved by Date Cisco1, DAT DAT SDE August 17, 2015 Document changelog Version Date Changelog based on 1.3 – french August 17, 2015 Translation Contact information Contact Address Email Phone 51 bd de La Bureau Communication Tour-Maubourg [email protected] 01 71 75 84 04 de l’ANSSI 75700 Paris Cedex 07 SP 1. -
Process Management
Princeton University Computer Science 217: Introduction to Programming Systems Process Management 1 Goals of this Lecture Help you learn about: • Creating new processes • Waiting for processes to terminate • Executing new programs • Shell structure Why? • Creating new processes and executing new programs are fundamental tasks of many utilities and end-user applications • Assignment 7… 2 System-Level Functions As noted in the Exceptions and Processes lecture… Linux system-level functions for process management Function Description exit() Terminate the process fork() Create a child process wait() Wait for child process termination execvp() Execute a program in current process getpid() Return the process id of the current process 3 Agenda Creating new processes Waiting for processes to terminate Executing new programs Shell structure 4 Why Create New Processes? Why create a new process? • Scenario 1: Program wants to run an additional instance of itself • E.g., web server receives request; creates additional instance of itself to handle the request; original instance continues listening for requests • Scenario 2: Program wants to run a different program • E.g., shell receives a command; creates an additional instance of itself; additional instance overwrites itself with requested program to handle command; original instance continues listening for commands How to create a new process? • A “parent” process forks a “child” process • (Optionally) child process overwrites itself with a new program, after performing appropriate setup 5 fork System-Level -
Openssh Client Cryptographic Module Versions 1.0, 1.1 and 1.2
OpenSSH Client Cryptographic Module versions 1.0, 1.1 and 1.2 FIPS 140-2 Non-Proprietary Security Policy Version 3.0 Last update: 2021-01-13 Prepared by: atsec information security corporation 9130 Jollyville Road, Suite 260 Austin, TX 78759 www.atsec.com © 2021 Canonical Ltd. / atsec information security This document can be reproduced and distributed only whole and intact, including this copyright notice. OpenSSH Client Cryptographic Module FIPS 140-2 Non-Proprietary Security Policy Table of Contents 1. Cryptographic Module Specification ....................................................................................................... 5 1.1. Module Overview .................................................................................................................................... 5 1.2. Modes of Operation ................................................................................................................................ 9 2. Cryptographic Module Ports and Interfaces ......................................................................................... 10 3. Roles, Services and Authentication ...................................................................................................... 11 3.1. Roles ...................................................................................................................................................... 11 3.2. Services ................................................................................................................................................. -
EZ-SCREEN LP Instruction Manual
EZ-SCREEN® LP Low-Profile Safety Light Screen Instruction Manual Original Instructions 140044 Rev. G 27 April 2018 © Banner Engineering Corp. All rights reserved 140044 EZ-SCREEN® LP Low-Profile Safety Light Screen Contents 1 About This Document .............................................................................................................................................5 1.1 Important . Read This Before Proceeding! .....................................................................................................................5 1.2 Use of Warnings and Cautions ...........................................................................................................................................5 1.3 EU Declaration of Conformity (DoC) ..................................................................................................................................5 1.4 Banner Engineering Corp Limited Warranty ......................................................................................................................6 1.5 Contact Us ......................................................................................................................................................................... 6 2 Introduction ............................................................................................................................................................ 8 2.1 Features .............................................................................................................................................................................8 -

Openssh-Ldap-Pubkey Documentation Release 0.3.0
openssh-ldap-pubkey Documentation Release 0.3.0 Kouhei Maeda May 18, 2020 Contents 1 openssh-ldap-pubkey 3 1.1 Status...................................................3 1.2 Requirements...............................................3 1.3 See also..................................................3 2 How to setup LDAP server for openssh-lpk5 2.1 Precondition...............................................5 2.2 Requirements...............................................5 2.3 Install...................................................5 3 How to setup OpenSSH server9 3.1 Precondition...............................................9 3.2 Requirements...............................................9 3.3 Install with nslcd (recommend).....................................9 3.4 Install without nslcd........................................... 11 4 History 13 4.1 0.3.0 (2020-05-18)............................................ 13 4.2 0.2.0 (2018-09-30)............................................ 13 4.3 0.1.3 (2018-08-18)............................................ 13 4.4 0.1.2 (2017-11-25)............................................ 13 4.5 0.1.1 (2015-10-16)............................................ 14 4.6 0.1.0 (2015-10-16)............................................ 14 5 Contributors 15 6 Indices and tables 17 i ii openssh-ldap-pubkey Documentation, Release 0.3.0 Contents: Contents 1 openssh-ldap-pubkey Documentation, Release 0.3.0 2 Contents CHAPTER 1 openssh-ldap-pubkey 1.1 Status 1.2 Requirements 1.2.1 LDAP server • Add openssh-lpk schema. • Add an objectClass ldapPublicKey to user entry. • Add one or more sshPublicKey attribute to user entry. 1.2.2 OpenSSH server • OpenSSH over 6.2. • Installing this utility. • Setup AuthorozedKeysCommand and AuthorizedKeysCommandUser in sshd_config. 1.3 See also • OpenSSH 6.2 release 3 openssh-ldap-pubkey Documentation, Release 0.3.0 • openssh-lpk 4 Chapter 1. openssh-ldap-pubkey CHAPTER 2 How to setup LDAP server for openssh-lpk 2.1 Precondition This article restricts OpenLDAP with slapd_config on Debian systems only. -

Banner 8 Student System
BANNER STUDENT Viewing Student Information Department: Student Information Management Email:[email protected] Phone: 646-7383 Last Update: March 1, 2010 Banner Student Confidential Business Information This documentation is proprietary information of New Mexico State University (NMSU) and is not to be copied, reproduced, lent or disposed of, nor used for any purpose other than that for which it is specifically provided without the written permission of NMSU. Prepared For: Release 8.x Prepared By: New Mexico State University P.O. Box 30001 Las Cruces, New Mexico 88003 United States of America Issued: October 2012 In preparing and providing this publication, NMSU is not rendering legal, accounting, or other similar professional services. NMSU makes no claims that an institution’s use of this publication or the software for which it is provided will insure compliance with applicable federal or state laws, rules, or regulations. Each organization should seek legal, accounting and other similar professional services from competent providers of the organization’s own choosing. © 2010 Regents of New Mexico State University. SunGard or its subsidiaries in the U.S. and other countries is the owner of numerous marks, including “SunGard,” the SunGard logo, “Banner,” “PowerCAMPUS,” “Advance,” “Luminis”, "fsaATLAS," "DegreeWorks," "SEVIS Connection," "SmartCall," “UDC,” and “Unified Digital Campus.” Other names and marks used in this material are owned by third parties. Use of this material is solely for the support of SunGard HE Banner products and NMSU. © SunGard 2006. All rights reserved. The unauthorized possession, use, reproduction, distribution, display or disclosure of this material or the information contained herein is prohibited. -

POSIX Freeware
2115 POSIX Freeware Michael D. Hensley Allegro Consultants, Inc. 2101 Woodside Road Redwood City, CA 94062 (415) 369-2303 voice (415) 369-2304 fax [email protected] http://www.allegro.com Before you can really begin to explore and use the POSIX freeware, it would help to familiarize yourself with POSIX. What Is POSIX? To keep things simple, POSIX is a set of standards based on UNIX. There are three major areas covered by the standards: an end-user shell, a set of utilities, and a collection of programming functions. This paper will get you started with the shell and utilities. When I talk about "POSIX", I'll generally be referring only to the shell and utilities. What Is A POSIX File? The POSIX standards require a "hierarchical file system", like the on UNIX and MSDOS/WINDOWS PC's. HP added a hierarchical file system (usually referred to as the HFS) to MPE with version 4.5. If you have never used UNIX or a PC (or even if you have), you can learn more about the HFS by logging on to your MPE system and typing :XEQ POSIXCBT.LSN.SYS This runs an on-line tutorial about the HFS. POSIX also requires that filenames be case-sensitive (i.e. "FOOBAR" and "FooBar" are two different files). These two things (the HFS and the case-sensitive filenames) create much of the confusion about "POSIX files", but here's the secret: There really isn't any such thing as a "POSIX file" or a "non- POSIX file"! A file is a file is a file. -

Banner Running Jobs (Reports) in Banner
Banner Running Jobs (Reports) in Banner A Banner “job” is a report or process. Processes make global modifications to the database, but typically produce little valuable printed results. Examples include fee assessment, GPA calculation, letter extraction, and posting to the ledger. Reports are run primarily for the printed results. Examples include transcripts, bills, letters and budget reports. Since the client (PC) is actually running the “Job Submission” form (GJAPCTL), and the report is actually running on the Unix (Sun) computer, jobs will not prompt for parameters at runtime. All parameters must be specified in the parameter block of GJAPCTL. After submitting the job, you will immediately go back to Banner (while the job is running on the Sun computer). Output from the report or process will remain on the Sun computer. After the job is done running, you may connect to the Sun computer to spool the file. Running (Submitting) a Job To run a job (report or process), enter the job name using “Direct Access”, or select the Process Submission Control Form (GJAPCTL) from Direct Access or a menu: In the “Process” field, enter the name of the report or process you wish to run. You may issue aListFieldValuesfunction or click on the Processbutton to list all jobs that you have permission to run. If you have saved a parameter set for this report that you wish to use again, use NextField to move to the “Parameter Set” field and enter the parameter set name (or use ListFieldValuesto list sets you have already stored). Issue the NextBlock function to move to the "Printer Control” block. -
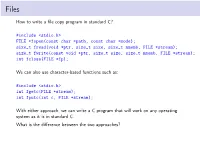
How to Write a File Copy Program in Standard C? #Include <Stdio.H>
Files How to write a file copy program in standard C? #include <stdio.h> FILE *fopen(const char *path, const char *mode); size_t fread(void *ptr, size_t size, size_t nmemb, FILE *stream); size_t fwrite(const void *ptr, size_t size, size_t nmemb, FILE *stream); int fclose(FILE *fp); We can also use character-based functions such as: #include <stdio.h> int fgetc(FILE *stream); int fputc(int c, FILE *stream); With either approach, we can write a C program that will work on any operating system as it is in standard C. What is the difference between the two approaches? /* lab/stdc-mycp.c */ /* appropriate header files */ #define BUF_SIZE 65536 int main(int argc, char *argv[]) { FILE *src, *dst; size_t in, out; char buf[BUF_SIZE]; int bufsize; if (argc != 4) { fprintf(stderr, "Usage: %s <buffer size> <src> <dest>\n", argv[0]); exit(1); } bufsize = atoi(argv[1]); if (bufsize > BUF_SIZE) { fprintf(stderr,"Error: %s: max. buffer size is %d\n",argv[0], BUF_SIZE); exit(1); } src = fopen(argv[2], "r"); if (NULL == src) exit(2); dst = fopen(argv[3], "w"); if (dst < 0) exit(3); while (1) { in = fread(buf, 1, bufsize, src); if (0 == in) break; out = fwrite(buf, 1, in, dst); if (0 == out) break; } fclose(src); fclose(dst); exit(0); } POSIX/Unix File Interface The system call interface for files in POSIX systems like Linux and MacOSX. A file is a named, ordered stream of bytes. I open(..) Open a file for reading or writing. Also allows a file to be locked providing exclusive access. I close(..) I read(..) The read operation is normally blocking. -

Banner General Upgrade Guide 8.11
Banner General Upgrade Guide Release 8.11 March 2019 Banner®, Colleague®, Luminis® and Datatel® are trademarks of Ellucian or its affiliates and are registered in the U.S. and other countries. Ellucian™, PowerCampus™, Advance™, Degree Works™, fsaATLAS™, Course Signals™, SmartCall™, Recruiter™, and ILP™ are trademarks of Ellucian Company L.P. or its affiliates. Other names may be trademarks of their respective owners. ©2019 Ellucian Company L.P. and its affiliates. The unauthorized possession, use, reproduction, distribution, display or disclosure of this material or the information contained herein is prohibited. Contains confidential and proprietary information of Ellucian and its subsidiaries. Use of these materials is limited to Ellucian licensees, and is subject to the terms and conditions of one or more written license agreements between Ellucian and the licensee in question. In preparing and providing this publication, Ellucian is not rendering legal, accounting, or other similar professional services. Ellucian makes no claims that an institution's use of this publication or the software for which it is provided will guarantee compliance with applicable federal or state laws, rules, or regulations. Each organization should seek legal, accounting and other similar professional services from competent providers of the organization's own choosing. Prepared by: Ellucian 2003 Edmund Halley Dr Reston, VA 20191 United States of America Revision History Publication Date Summary March 2019 New version that supports General 8.11 software.