Qualys Cloud Agent for Linux Installation Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Configuring UNIX-Specific Settings: Creating Symbolic Links : Snap
Configuring UNIX-specific settings: Creating symbolic links Snap Creator Framework NetApp September 23, 2021 This PDF was generated from https://docs.netapp.com/us-en/snap-creator- framework/installation/task_creating_symbolic_links_for_domino_plug_in_on_linux_and_solaris_hosts.ht ml on September 23, 2021. Always check docs.netapp.com for the latest. Table of Contents Configuring UNIX-specific settings: Creating symbolic links . 1 Creating symbolic links for the Domino plug-in on Linux and Solaris hosts. 1 Creating symbolic links for the Domino plug-in on AIX hosts. 2 Configuring UNIX-specific settings: Creating symbolic links If you are going to install the Snap Creator Agent on a UNIX operating system (AIX, Linux, and Solaris), for the IBM Domino plug-in to work properly, three symbolic links (symlinks) must be created to link to Domino’s shared object files. Installation procedures vary slightly depending on the operating system. Refer to the appropriate procedure for your operating system. Domino does not support the HP-UX operating system. Creating symbolic links for the Domino plug-in on Linux and Solaris hosts You need to perform this procedure if you want to create symbolic links for the Domino plug-in on Linux and Solaris hosts. You should not copy and paste commands directly from this document; errors (such as incorrectly transferred characters caused by line breaks and hard returns) might result. Copy and paste the commands into a text editor, verify the commands, and then enter them in the CLI console. The paths provided in the following steps refer to the 32-bit systems; 64-bit systems must create simlinks to /usr/lib64 instead of /usr/lib. -

Lab Exercise – Ipv4
Lab Exercise – IPv4 Objective To learn about the details of IP (Internet Protocol). IP is the network layer protocol used throughout the Internet. We will examine IP version 4, since it is ubiquitously deployed, while the IP version 6 is partly deployed. The trace is here: https://kevincurran.org/com320/labs/wireshark/trace-ipv4.pcap The text file is here: https://kevincurran.org/com320/labs/wireshark/trace-ipv4.txt Requirements Wireshark: This lab uses the Wireshark software tool to capture and examine a packet trace. A packet trace is a record of traffic at a location on the network, as if a snapshot was taken of all the bits that passed across a particular wire. The packet trace records a timestamp for each packet, along with the bits that make up the packet, from the lower-layer headers to the higher-layer contents. Wireshark runs on most operating systems, including Windows, Mac and Linux. It provides a graphical UI that shows the sequence of packets and the meaning of the bits when interpreted as protocol headers and data. It col- or-codes packets by their type, and has various ways to filter and analyze packets to let you investigate the behavior of network protocols. Wireshark is widely used to troubleshoot networks. You can down- load it from www.wireshark.org if it is not already installed on your computer. We highly recommend that you watch the short, 5 minute video “Introduction to Wireshark” that is on the site. wget / curl: This lab uses wget (Linux and Windows) and curl (Mac) to fetch web resources. -

Installation Guide LS Nav 2018 (11.0) Contents
LS Nav 2018 (11.0) Installation Guide © 2018 LS Retail ehf. All rights reserved. All trademarks belong to their respective holders. ii Installation Guide LS Nav 2018 (11.0) Contents Contents Installation Guide LS Nav 1 Files in This Version 1 LS Nav Setup File 1 Demonstration Database Backup 1 Documentation 1 Objects 2 Objects \ Uninstall 2 Objects \ Upgrade 2 Objects \ Auto Test 2 Online Help 2 Setup \ LS Nav Rapid Installer 2 Setup \ LS Nav Rapid Start 2 Setup \ LS Nav Toolbox 2 Setup \ LS Printing Station 2 Setup 2 Installation 2 Prerequisites 2 Microsoft Dynamics NAV Application Objects Added or Modified by LS Nav 3 Installing LS Nav in a New Database 4 Installing LS Nav in an Existing Database 4 Uninstall 5 Uninstall the LS Nav xx.x Client Components 5 Uninstall the LS Nav xx.x Service Components 5 Uninstall LS Nav from a Microsoft Dynamics NAV Database 5 Database Compilation 6 System Requirements 6 Security Hardening Guide for LS Nav 7 Clear Data Tables That Are Not Included in the Customer’s License 7 Online Help Installation 7 Installation Guide LS Nav 2018 (11.0) iii Contents Local Setup 8 Remote Setup 8 Older Documents 9 Toolbox Installation 10 See Also 10 Installing the Toolbox 10 Client Components Installer 11 Service Components Installer 12 Install Options (Silent Install) 13 Installing Into a Database (Control Add-Ins Table) 14 Web POS Installation 16 See Also (topics in LS Nav Online Help) 17 Installing Microsoft Dynamics NAV for Web POS 17 Importing Control Add-in for Web POS 17 Web POS in Full-Screen Mode 18 LS Nav Auto Tests 18 Prerequisites 18 Installation 19 Objects needed 19 Running 19 1. -

Getty Scholars' Workspace™ INSTALLATION INSTRUCTIONS
Getty Scholars’ Workspace™ INSTALLATION INSTRUCTIONS This document outlines methods to run the application locally on your personal computer or to do a full installation on a web server. Test Drive with Docker Getty Scholars' Workspace is a multi-tenant web application, so it is intended to be run on a web server. However, if you'd like to run it on your personal computer just to give it a test drive, you can use Docker to create a virtual server environment and run the Workspace locally. Follow the steps below to give it a spin. Scroll further for real deployment instructions. 1. Install Docker on your machine. Follow instructions on the Docker website: https://www.docker.com/ 2. If you are using Docker Machine (Mac or Windows), be sure to start it by using the Docker Quickstart Terminal. Docker is configured to use the default machine with IP 192.168.99.100. 3. At the command line, pull the Getty Scholars' Workspace image. $ docker pull thegetty/scholarsworkspace 4. Run the container. $ docker run -d -p 8080:80 --name=wkspc thegetty/scholarsworkspace supervisord -n 5. Point your browser to `<ip address>:8080/GettyScholarsWorkspace`. Use the IP address noted in Step 2. 6. The Drupal administrator login is `scholar` and the password is `workspace`. Be sure to change these in the Drupal admin interface. 7. To shut it down, stop the container: $ docker stop wkspc Web Server Installation These installation instructions assume you are installing Getty Scholars' Workspace on a server (virtual or physical) with a clean new instance of Ubuntu 14.04 as the operating system. -
K30503041: Creating a Virtual Server with ARP And/Or ICMP Disabled at Creation
K30503041: Creating a virtual server with ARP and/or ICMP disabled at creation Non-Diagnostic Original Publication Date: Apr 16, 2020 Update Date: Apr 16, 2020 Topic You should consider using this procedure under the following condition: You want to create a new virtual server with the Address Resolution Protocol (ARP) and/or the Internet Control Message Protocol (ICMP) disabled at creation. Description In some network environments, you may want to create virtual servers that have ARP and/or ICMP disabled. When creating a new virtual server (one that does not use an IP address of an existing virtual server), you can enable or disable the virtual server. However, you cannot set the IP address of the virtual server with ARP and/or ICMP to 'disabled' when creating the virtual server. You can only enable or disable ARP or ICMP by modifying the virtual address that is automatically created when you create the virtual server. In this scenario, you create the virtual address with ARP and ICMP enabled at the time of creation. You can work around this scenario by creating the virtual address for the virtual server in advance with ARP and/or ICMP disabled. After creating the virtual address, you can then create the virtual server that references the same IP address of the virtual address as the destination IP address of the virtual server. Prerequisites You must meet the following prerequisite to use this procedure: Administrative access to the BIG-IP Configuration utility or the TMOS Shell (tmsh). Note: You cannot create a virtual address using the Configuration utility. -

Openssh-Ldap-Pubkey Documentation Release 0.3.0
openssh-ldap-pubkey Documentation Release 0.3.0 Kouhei Maeda May 18, 2020 Contents 1 openssh-ldap-pubkey 3 1.1 Status...................................................3 1.2 Requirements...............................................3 1.3 See also..................................................3 2 How to setup LDAP server for openssh-lpk5 2.1 Precondition...............................................5 2.2 Requirements...............................................5 2.3 Install...................................................5 3 How to setup OpenSSH server9 3.1 Precondition...............................................9 3.2 Requirements...............................................9 3.3 Install with nslcd (recommend).....................................9 3.4 Install without nslcd........................................... 11 4 History 13 4.1 0.3.0 (2020-05-18)............................................ 13 4.2 0.2.0 (2018-09-30)............................................ 13 4.3 0.1.3 (2018-08-18)............................................ 13 4.4 0.1.2 (2017-11-25)............................................ 13 4.5 0.1.1 (2015-10-16)............................................ 14 4.6 0.1.0 (2015-10-16)............................................ 14 5 Contributors 15 6 Indices and tables 17 i ii openssh-ldap-pubkey Documentation, Release 0.3.0 Contents: Contents 1 openssh-ldap-pubkey Documentation, Release 0.3.0 2 Contents CHAPTER 1 openssh-ldap-pubkey 1.1 Status 1.2 Requirements 1.2.1 LDAP server • Add openssh-lpk schema. • Add an objectClass ldapPublicKey to user entry. • Add one or more sshPublicKey attribute to user entry. 1.2.2 OpenSSH server • OpenSSH over 6.2. • Installing this utility. • Setup AuthorozedKeysCommand and AuthorizedKeysCommandUser in sshd_config. 1.3 See also • OpenSSH 6.2 release 3 openssh-ldap-pubkey Documentation, Release 0.3.0 • openssh-lpk 4 Chapter 1. openssh-ldap-pubkey CHAPTER 2 How to setup LDAP server for openssh-lpk 2.1 Precondition This article restricts OpenLDAP with slapd_config on Debian systems only. -
Curl User Survey 2019 Analysis
curl user survey 2019 analysis “there are so many useful features” summary and analysis by Daniel Stenberg version 1 - June 4, 2019 Table of Contents About curl.............................................................................................................................................3 Survey Background..........................................................................................................................3 Number of responses............................................................................................................................4 Returning respondents?........................................................................................................................5 Users living where?..............................................................................................................................6 What kind of users?..............................................................................................................................7 What protocols......................................................................................................................................8 Multiple platforms..............................................................................................................................10 What platforms...................................................................................................................................11 Which Windows versions...................................................................................................................13 -
Pingdirectory Administration Guide Version
Release 7.3.0.3 Server Administration Guide PingDirectory | Contents | ii Contents PingDirectory™ Product Documentation................................................ 20 Overview of the Server............................................................................. 20 Server Features.................................................................................................................................20 Administration Framework.................................................................................................................21 Server Tools Location....................................................................................................................... 22 Preparing Your Environment....................................................................22 Before You Begin.............................................................................................................................. 22 System requirements..............................................................................................................22 Installing Java......................................................................................................................... 23 Preparing the Operating System (Linux).......................................................................................... 24 Configuring the File Descriptor Limits.................................................................................... 24 File System Tuning.................................................................................................................25 -

After Upgrade and Reboot with Install Configuration Set to Yes, the BIG-IP
K33233632: After upgrade and reboot with Install Configuration set to Yes, the BIG-IP appears to have hung or lost all configuration and mcpd, gtmd, named and others are in a restart loop Support Solution Original Publication Date: Jan 28, 2020 Update Date: Mar 25, 2021 Details Description After you upgrade the BIG-IP system to BIG-IP 14.1.2 and later, certain daemons (e.g. mcpd, gtmd, and named) may be in a restart loop and the BIG-IP appears to have hung or lost all configuration. Additionally, the device may exhibit the following symptoms: You observe error messages similar to the following in /var/log/ltm (below is an example of an mcpd restart loop): err mcpd[8710]: 01070734:3: Configuration error: MCPProcessor::initializeDB: can't chmod for directory (/config/filestore/files_d/<directory_names>) err (Permission denied). err mcpd[8710]: 01070596:3: An unexpected failure has occurred, can't chmod for directory (/config /filestore/files_d/<directory_names>) err (Permission denied). - sys/validation/FileObject.cpp, line 612, exiting... You observe error messages similar to the following in /var/log/ltm: 01420006:3: Loading configuration process failed. You observe error messages similar to the following in /var/log/auditd/audit.log (below is an example for an mcpd restart loop): Note: The message contains denied and unlabeled_t shown in bold below. type=AVC msg=audit(day_time): avc: denied { setattr } for pid=13624 comm="mcpd" name=" external_monitor_d" dev="dm-11" ino=307 scontext=system_u:system_r:mcpd_t:s0 tcontext=system_u:object_r:unlabeled_t:s0 tclass=dir The Configuration utility displays the following: The configuration has not yet loaded. -
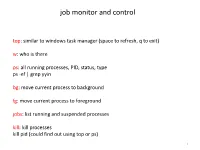
Install and Run External Command Line Softwares
job monitor and control top: similar to windows task manager (space to refresh, q to exit) w: who is there ps: all running processes, PID, status, type ps -ef | grep yyin bg: move current process to background fg: move current process to foreground jobs: list running and suspended processes kill: kill processes kill pid (could find out using top or ps) 1 sort, cut, uniq, join, paste, sed, grep, awk, wc, diff, comm, cat All types of bioinformatics sequence analyses are essentially text processing. Unix Shell has the above commands that are very useful for processing texts and also allows the output from one command to be passed to another command as input using pipe (“|”). less cosmicRaw.txt | cut -f2,3,4,5,8,13 | awk '$5==22' | cut -f1 | sort -u | wc This makes the processing of files using Shell very convenient and very powerful: you do not need to write output to intermediate files or load all data into the memory. For example, combining different Unix commands for text processing is like passing an item through a manufacturing pipeline when you only care about the final product 2 Hands on example 1: cosmic mutation data - Go to UCSC genome browser website: http://genome.ucsc.edu/ - On the left, find the Downloads link - Click on Human - Click on Annotation database - Ctrl+f and then search “cosmic” - On “cosmic.txt.gz” right-click -> copy link address - Go to the terminal and wget the above link (middle click or Shift+Insert to paste what you copied) - Similarly, download the “cosmicRaw.txt.gz” file - Under your home, create a folder -

DPDK-Based Userspace TCP/IP Stack Testing SHU MA EBS – KUAFU ALIBABA CLOUD Agenda
x DPDK-based userspace TCP/IP stack testing SHU MA EBS – KUAFU ALIBABA CLOUD Agenda 1 Background 2 Current status 3 Our practice 4 Q&A Background Luna • high performance network framework • DPDK • Luna Stack (userspace lightweight TCP/IP stack) Product • ESSD (cloud disk) • hundreds of production clusters • tens of thousands of machines Latency • 1/3 kernel • nearly as fast as RDMA https://www.aliyun.com/product/disk Background Challenges in developing Luna Stack • Bug is time-series-related • hard to reproduce • hard to troubleshoot Test Framework • Large number of corner cases 1. bug reproduction • hard to fix 2. trouble shooting • easy to break other cases 3. regression 4. correctness • Convince upper-layer developers • correctness • robustness Current status Linux kernel, FreeBSD • Internal • Low unit test coverage • External (LTP) • 20+ scripts for TCP/IP Testing approaches • Unit test(white box) • need to know code detail, hard to write • Function test(black box) • hard to create scenarios with strict time-series • packetdrill(grey box) • Google, open source • USENIX ATC 2013 • 3 new TCP features, 10 kernel bugs bug fix for Linux kernel Packetdrill: script 4 statements 0 socket(..., SOCK_STREAM, IPPROTO_TCP) = 3 +0 bind(3, ..., ...) = 0 • packets +0 listen(3, 1) = 0 • tcpdump-like syntax • inbound, outbound +0 < S 0:0(0) win 32792 <mss 1460, nop, wscale 7, nop, nop, TS val 0 ecr 0> • system calls +0 > S. 0:0(0) ack 1 <mss 1460, nop, nop, TS val 0 ecr 0, nop, wscale 7> • strace-like syntax +0 `netstat -anp | grep 8080 | grep SYN_RCVD` // examine TCP state • shell commands +.1 < . -

Install Guide - UNIX Oracle CSE
Information Engineering Technology Install Guide - UNIX Oracle CSE Release 8.7.3 © Information Engineering Technology Ltd 2020 www.iet.uk Table Of Contents Introduction ............................................................................................................................................................................... 3 Architecture .................................................................................................................................................................................... 3 Communications ............................................................................................................................................................................. 3 About The Installation Guides .................................................................................................................................................... 4 Software for Download .............................................................................................................................................................. 4 Server Install – UNIX / Oracle CSE ............................................................................................................................................... 5 Pre-Requisites ................................................................................................................................................................................. 5 Who Should Perform this Installation? ..........................................................................................................................................