Navy Rank Abbreviations
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Railway Employee Records for Colorado Volume Iii
RAILWAY EMPLOYEE RECORDS FOR COLORADO VOLUME III By Gerald E. Sherard (2005) When Denver’s Union Station opened in 1881, it saw 88 trains a day during its gold-rush peak. When passenger trains were a popular way to travel, Union Station regularly saw sixty to eighty daily arrivals and departures and as many as a million passengers a year. Many freight trains also passed through the area. In the early 1900s, there were 2.25 million railroad workers in America. After World War II the popularity and frequency of train travel began to wane. The first railroad line to be completed in Colorado was in 1871 and was the Denver and Rio Grande Railroad line between Denver and Colorado Springs. A question we often hear is: “My father used to work for the railroad. How can I get information on Him?” Most railroad historical societies have no records on employees. Most employment records are owned today by the surviving railroad companies and the Railroad Retirement Board. For example, most such records for the Union Pacific Railroad are in storage in Hutchinson, Kansas salt mines, off limits to all but the lawyers. The Union Pacific currently declines to help with former employee genealogy requests. However, if you are looking for railroad employee records for early Colorado railroads, you may have some success. The Colorado Railroad Museum Library currently has 11,368 employee personnel records. These Colorado employee records are primarily for the following railroads which are not longer operating. Atchison, Topeka & Santa Fe Railroad (AT&SF) Atchison, Topeka and Santa Fe Railroad employee records of employment are recorded in a bound ledger book (record number 736) and box numbers 766 and 1287 for the years 1883 through 1939 for the joint line from Denver to Pueblo. -
Ships Unless They Carried He Spoke of "Supporting" MEBA in the American Ing Speed
'i \'' iiV • • . YoK XIX No. 1 SEAFARERS LOG J • OFFICIAL ORGAN OF THE SEAFARERS INTERNATIONAL UNION • ATLANTIC AND GULF DISTRICT • AFL-CIO • .. ."M SIU PREPARED IN ? • ft -Story On Page 3 k f Arf cfm/vc fAAAf Hospitalized New Orleans Seafarers, like men in other ports, got Christ- Vffff fSf fffua Vffccr* mas boost in form of $25 bonus from SIU Welfare Plan. Welfare repre sentative Vic Miorana (seated, left) delivers cash to (1 to r) Martin Kelly, Seno Desoso, Charles Dor- rough, Clovis Coates, Michael Muzio, Demetrio Zerrido. Seated is Mike Liuzza, a visitor. •.•4: : hife. Sea Transportation Service. (Story on Page 2.) rA January 4, 1957 Page Two SEAF ASERS IPG .Shown here at Jacksonville, Fla., where she was crewed by Seafarers, Carib Queen is kicking off first true US "roll on- roll off service." Converted LSD, which normally will carry loaded truck trailers to Caribbean ports, will see first service under MSTS charter, transporting Army supplies to Germany. Carib Queen Begins K-' MSTS Trial Voyage In the latest issue of the "Pilot" Curran resumes Erratic could be another name for NMU President JACKSONVILLE—-With appropriate fanfare and dedica Joseph Curran. his onslaught against the SIU lor acting against his unique notions of trade union behavior. In the tion ceremonies the SlU-manned Carib Queen has embarked His inability to control explosive emotional out bursts, resulting from real or fancied grievances, course of that attack, he tipped his mitt as to his on her maiden voyage as the first true full-sized trailership. real concern by sneering "egg crate ship" at plans After touching at San Juan and-t- ~~ only serves to add to a record of inconsistency and to build a low-cost passenger liner for. -

CAPP 52-21 April 2011
AEROSPACE LEADERSHIP FITNESS CHARACTER CIVIL AIR PATROL CADETS AT SCHOOL Program Overview for Educators CAPP 52-21 April 2011 Civil Air Patrol provides middle and high schools with CIVIL AIR PATROL a character education curriculum through its Cadet is a non-profit corporation that Program. was chartered by the U.S. Congress in 1946 and is the This guide is intended for professional educators who all-volunteer auxiliary of the are interested in making the Cadet Program part of U.S. Air Force. Its 61,000 their school community. It outlines the program’s goals members support its aerospace and benefits, describes the curriculum, and explains education, cadet program, and how the program is managed. emergency services missions. p NICOLE MALACHOWSKI p ERIC BOE Former Air Force Thunderbird Pilot Astronaut “My experiences as a CAP cadet were “I made my first solo flight at a CAP fundamental to my success.” encampment.” Change 1, June 2014: Updated contact information on page 9. INTRODUCTION Through partnerships with middle and high schools, Civil Air Patrol’s Cadet Program is fulfilling its mission of develop- ing tomorrow’s aerospace leaders. CAP offers schools an exciting form of character education that uses the students’ enthusiasm for aviation, space, and technology as a motivator. An Air Force-affiliated program, high schools find Civil Air Patrol a low-cost alternative to Junior ROTC. Middle schools p Serving in a find that the challenge of cadet life provides the structure early adolescents need. A color guard middle school CAP squadron can be a great complement to a high school JROTC program. -
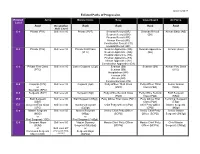
Enlisted Paths of Progression Chart
Updated 2/24/17 Enlisted Paths of Progression Enlisted Army Marine Corps Navy Coast Guard Air Force Level Rank Occupation Rank Rank Rank Rank Skill Level E-1 Private (PV1) Skill level 10 Private (PVT) Seaman Recruit (SR) Seaman Recruit Airman Basic (AB) Seaman Recruit (SR) (SR) Fireman Recruit (FR) Airman Recruit (AR) Construction Recruit (CR) Hospital Recruit (HR) E-2 Private (PV2) Skill level 10 Private First Class Seaman Apprentice (SA) Seaman Apprentice Airman (Amn) (PFC) Seaman Apprentice (SA) (SA) Hospital Apprentice (HA) Fireman Apprentice (FA) Airman Apprentice (AA) Construction Apprentice (CA) E-3 Private First Class Skill level 10 Lance Corporal (LCpl) Seaman (SN) Seaman (SN) Airman First Class (PFC) Seaman (SN) (A1C) Hospitalman (HN) Fireman (FN) Airman (AN) Constructionman (CN) E-4 Corporal (CPL) Skill level 10 Corporal (Cpl) Petty Officer Third Class Petty Officer Third Senior Airman or (PO3) Class (PO3) (SRA) Specialist (SPC) E-5 Sergeant (SGT) Skill level 20 Sergeant (Sgt) Petty Office Second Class Petty Office Second Staff Sergeant (PO2) Class (PO2) (SSgt) E-6 Staff Sergeant Skill level 30 Staff Sergeant (SSgt) Petty Officer First Class (PO1) Petty Officer First Technical Sergeant (SSG) Class (PO1) (TSgt) E-7 Sergeant First Class Skill level 40 Gunnery Sergeant Chief Petty Officer (CPO) Chief Petty Officer Master Sergeant (SFC) (GySgt) (CPO) (MSgt) E-8 Master Sergeant Skill level 50 Master Sergeant Senior Chief Petty Officer Senior Chief Petty Senior Master (MSG) (MSgt) (SCPO) Officer (SCPO) Sergeant (SMSgt) or or First Sergeant (1SG) First Sergeant (1stSgt) E-9 Sergeant Major Skill level 50 Master Gunnery Master Chief Petty Officer Master Chief Petty Chief Master (SGM) Sergeant (MGySgt) (MCPO) Officer (MCPO) Sergeant (CMSgt) or Skill level 60* or Command Sergeant (*For some fields, Sergeant Major Major (CSM) not all.) (SgtMaj) . -
Joining Handbook
Royal Canadian Sea Cadet Corps Centurion Joining Handbook VER: SEPTEMBER 2016 www.centurionseacadets.org Table of Contents What is the Sea Cadet Program? .................................................................................................................. 4 Parents’ and/or Guardians’ Page .................................................................................................................. 5 Why choose Sea Cadets? .......................................................................................................................... 5 How much does the program cost? .......................................................................................................... 5 The Navy League of Canada ...................................................................................................................... 5 Kanata Branch ....................................................................................................................................... 5 General Overview ......................................................................................................................................... 6 Training ..................................................................................................................................................... 6 Regular Parade Nights ........................................................................................................................... 6 Mandatory and Supplementary Training ............................................................................................. -
New Cadet Handbook
NEW CADET HANDBOOK WELCOME ABOARD 1 Welcome Aboard!!!! You are joining one of the finest youth organizations in the Nation, The United States Naval Sea Cadet Corps (NSCC). The NSCC or just Sea Cadets is actually two programs The Naval Sea Cadet Corps (NSCC) is for American youth ages 13-17 that have a desire to learn about the Navy, Marine Corps, Coast Guard and Merchant Marine. Sea Cadets are authorized by the Secretary of the Navy to wear Navy uniforms appropriately marked with the Sea Cadet Corps insignia. The objectives of the Sea Cadet program are to introduce youth to naval life, to develop in them a sense of pride, patriotism, courage, and self- reliance, and to maintain an environment free of drugs and gangs. The Navy League Cadet Corps (NLCC) is for boys and girls, at least 10 but not yet 14 years old, who are interested in the sea and ships, and our nation’s seagoing services. The Navy League program is designed to introduce young people to maritime and military life, and to prepare them for later entrance into the Naval Sea Cadet Corps. This Handbook will help guide you into the unit. Again WELCOME ABOARD!!!! 2 Your Unit Your unit of the Sea Cadets is called the AMERICAN VETERANS DIVISION. Sea Cadet units are divided into three types: • DIVISIONS – NSCC Divisions train primarily in the field of seamanship. • SQUADRONS – NSCC Squadrons train primarily in the field of Aviation. • BATTALIONS – NSCC Battalions train primarily in the field of Naval Construction. While a unit may train primarily in one field of the Navy, its cadets do receive cross training in other fields. -

DECK STUDY RECOMMENDATIONS Revision #4, December 15, 2010
M.E.T. Marine Education Textbooks 124 North Van Avenue Houma, Louisiana 70363-5895 Phone: (985) 879-3866 Fax: (985) 879-3911 DSR Website: www.marineeducationtextbooks.com Email: [email protected] DECK STUDY RECOMMENDATIONS Revision #4, December 15, 2010. Edited by: Richard A. Block, B.A., M.S. Ed., Master, N.C., 500/1600 tons. [Comment: All previous deck study recommendations are cancelled.] TABLE OF CONTENTS their experience to improve the quality of this information by reporting any discrepancies. Our Study Material Recommendations.............................1 We understand that many of our recommendations involve The New Terminology ....................................................1 considerable expense. We encourage you to ask your public Select the Credential You Want.......................................2 library to acquire the basic books required by all persons in Types of Officer Endorsements .......................................4 the commercial marine industry. Learn how to use all the The Difference Between Exam “Topics” & “Modules”....4 reference books that are used on your vessel. Share your Applying for a Credential or an Endorsement...................5 information with other mariners, but beware of outdated Is This Your First Coast Guard Credential? ….................6 information while preparing for an exam! Obsolete material Coast Guard Credentialing Regulations ...........................6 can mislead you in a number of ways. How Do I find the Study Material I Need?.......................7 List of Exam Topics (Figure 1)........................................8 Individual Chapters Fill Knowledge Gaps Special Order of Individual “Deck” Chapters.................12 Marine Education Textbooks (MET) has been in Special Order of Individual “Engine” Chapters..............14 business for over 40 years catering to the needs of “limited Special Order of “Other” Chapters.................................14 tonnage” merchant mariners. -

The Return of Coppersmith's Attack:Practical Factorization of Widely Used RSA Moduli
Session H1: Crypto Attacks CCS’17, October 30-November 3, 2017, Dallas, TX, USA The Return of Coppersmith’s Aack: Practical Factorization of Widely Used RSA Moduli Matus Nemec Marek Sys∗ Petr Svenda Masaryk University, Masaryk University Masaryk University Ca’ Foscari University of Venice [email protected] [email protected] [email protected] Dusan Klinec Vashek Matyas EnigmaBridge, Masaryk University Masaryk University [email protected] [email protected] ABSTRACT 1 INTRODUCTION We report on our discovery of an algorithmic aw in the construc- RSA [69] is a widespread algorithm for asymmetric cryptography tion of primes for RSA key generation in a widely-used library used for digital signatures and message encryption. RSA security of a major manufacturer of cryptographic hardware. e primes is based on the integer factorization problem, which is believed generated by the library suer from a signicant loss of entropy. to be computationally infeasible or at least extremely dicult for We propose a practical factorization method for various key lengths suciently large security parameters – the size of the private primes including 1024 and 2048 bits. Our method requires no additional and the resulting public modulus N . As of 2017, the most common information except for the value of the public modulus and does length of the modulus N is 2048 bits, with shorter key lengths not depend on a weak or a faulty random number generator. We such as 1024 bits still used in practice (although not recommend devised an extension of Coppersmith’s factorization aack utilizing anymore) and longer lengths like 4096 bits becoming increasingly an alternative form of the primes in question. -

Neptune's Might: Amphibious Forces in Normandy
Neptune’s Might: Amphibious Forces in Normandy A Coast Guard LCVP landing craft crew prepares to take soldiers to Omaha Beach, June 6, 1944 Photo 26-G-2349. U.S. Coast Guard Photo, Courtesy Naval History and Heritage Command By Michael Kern Program Assistant, National History Day 1 “The point was that we on the scene knew for sure that we could substitute machines for lives and that if we could plague and smother the enemy with an unbearable weight of machinery in the months to follow, hundreds of thousands of our young men whose expectancy of survival would otherwise have been small could someday walk again through their own front doors.” - Ernie Pyle, Brave Men 2 What is National History Day? National History Day is a non-profit organization which promotes history education for secondary and elementary education students. The program has grown into a national program since its humble beginnings in Cleveland, Ohio in 1974. Today over half a million students participate in National History Day each year, encouraged by thousands of dedicated teachers. Students select a historical topic related to a theme chosen each year. They conduct primary and secondary research on their chosen topic through libraries, archives, museums, historic sites, and interviews. Students analyze and interpret their sources before presenting their work in original papers, exhibits, documentaries, websites, or performances. Students enter their projects in contests held each spring at the local, state, and national level where they are evaluated by professional historians and educators. The program culminates in the Kenneth E. Behring National Contest, held on the campus of the University of Maryland at College Park each June. -

The Industrial Role of Scrap Copper at Jamestown Carter C
THE JOURNAL OF THE JAMESTOWN Carter C. Hudgins REDISCOVERY CENTER “Old World Industries and New World Hope: The VOL. 2 JAN. 2004 Industrial Role of Scrap Copper at Jamestown” Available from https://www.historicjamestowne.org Old World Industries and New World Hope: The Industrial Role of Scrap Copper at Jamestown Carter C. Hudgins 1. Introduction Jamestown scholars have long believed that during the first ten years of the Virginia Colony (1607-1617), settlers attempted to elude starvation by trading European copper with local Powhatans in exchange for foodstuffs. Contem- porary reports, such as those written by John Smith, docu- Figure 1. A sample of scrap waste selected from copper found at ment this bartering, and recent archaeological discoveries Jamestown. of over 7,000 pieces of scrap sheet copper within James Fort seem to substantiate the existence of this commerce (Figure 2. Jamestown’s Scrap Copper 1). Although much of this waste metal was undoubtedly Examinations of the scrap copper found in Jamestown associated with the exchange of goods between the English Rediscovery’s five largest Fort-Period features—Pit 1, Pit 3, and Powhatans, this study suggests that significant amounts Structure 165, SE Bulwark Trench, and Feature JR 731— of Jamestown’s scrap copper were also related to contempo- reveal that a significant percentage of the copper bears manu- rary English copper industries and an anticipation of met- facturing evidence that can be credited to coppersmithing allurgical resources in the New World. industries in England. Several examples of copper that pos- th During the late 16 century, the Society of Mines Royal sess the markings of English industry are shown in Figures and the Society of Minerals and Battery Works were formed 2, 3 and 4, and relate to the making of copper wire, buckles to mine English metals, produce copper-alloy products, and and kettles respectively. -
The Legacy of Commodore David Porter, USN: Midshipman David Glasgow Farragut Part One of a Three-Part Series
The Legacy of Commodore David Porter, USN: Midshipman David Glasgow Farragut Part One of a three-part series Vice Admiral Jim Sagerholm, USN (Ret.), September 15, 2020 blueandgrayeducation.org David Glasgow Farragut | National Portrait Gallery In any discussion of naval leadership in the Civil War, two names dominate: David Glasgow Farragut and David Dixon Porter. Both were sons of David Porter, one of the U.S. Navy heroes in the War of 1812, Farragut having been adopted by Porter in 1808. Farragut’s father, George Farragut, a seasoned mariner from Spain, together with his Irish wife, Elizabeth, operated a ferry on the Holston River in eastern Tennessee. David Farragut was their second child, born in 1801. Two more children later, George moved the family to New Orleans where the Creole culture much better suited his Mediterranean temperament. Through the influence of his friend, Congressman William Claiborne, George Farragut was appointed a sailing master in the U.S. Navy, with orders to the naval station in New Orleans, effective March 2, 1807. George Farragut | National Museum of American David Porter | U.S. Naval Academy Museum History The elder Farragut traveled to New Orleans by horseback, but his wife and four children had to go by flatboat with the family belongings, a long and tortuous trip lasting several months. A year later, Mrs. Farragut died from yellow fever, leaving George with five young children to care for. The newly arrived station commanding officer, Commander David Porter, out of sympathy for Farragut, offered to adopt one of the children. The elder Farragut looked to the children to decide which would leave, and seven-year-old David, impressed by Porter’s uniform, volunteered to go. -

Collective Bargaining Agreement
COLLECTIVE BARGAINING AGREEMENT between the STATE OF ALASKA and the INLANDBOATMEN’S UNION of the PACIFIC ALASKA REGION 2014 – 2017 Table of Contents RULE 1 - SCOPE ............................................................................................................................................................. 1 1.04 - Labor Management Committee Purpose .................................................................................................................... 1 RULE 2 - RECOGNITION ......................................................................................................................................... 2 RULE 3 - HIRING .......................................................................................................................................................... 2 RULE 4 - DEFINITIONS ............................................................................................................................................ 2 4.01 - Employees ................................................................................................................................................................ 2 4.02 - Regularly Assigned Positions .................................................................................................................................... 3 4.03 - Vessels ..................................................................................................................................................................... 3 RULE 5 - UNION MEMBERSHIP .........................................................................................................................