Linux on the IBM Iseries Server an Implementation Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Troubleshooting Passwords
Troubleshooting Passwords The following procedures may be used to troubleshoot password problems: • Performing Password Recovery with an Existing Administrator, page 1 • Performing Password Recovery with No Existing Administrator, page 1 • Performing Password Recovery for the Linux Grapevine User Account, page 2 Performing Password Recovery with an Existing Administrator To perform password recovery for a user (administrator, installer or observer) where there exists at least one controller administrator (ROLE_ADMIN) user account, take the following steps: 1 Contact the existing administrator to set up a temporary password for the user that requires password recovery. Note The administrator can set up a temporary password by deleting the user's account and then recreating it with the lost password. The user can then log back into the controller to regain access and change the password once again to whatever he or she desires. 2 The user then needs to log into the controller with the temporary password and change the password. Note Passwords are changed in the controller GUI using the Change Password window. For information about changing passwords, see Chapter 4, Managing Users and Roles in the Cisco Application Policy Infrastructure Controller Enterprise Module Configuration Guide. Performing Password Recovery with No Existing Administrator The following procedure describes how to perform password recovery where there exists only one controller administrator (ROLE_ADMIN) user account and this account cannot be successfully logged into. Cisco Application Policy Infrastructure Controller Enterprise Module Troubleshooting Guide, Release 1.3.x 1 Troubleshooting Passwords Performing Password Recovery for the Linux Grapevine User Account Note We recommend that you create at least two administrator accounts for your deployment. -

Version 7.8-Systemd
Linux From Scratch Version 7.8-systemd Created by Gerard Beekmans Edited by Douglas R. Reno Linux From Scratch: Version 7.8-systemd by Created by Gerard Beekmans and Edited by Douglas R. Reno Copyright © 1999-2015 Gerard Beekmans Copyright © 1999-2015, Gerard Beekmans All rights reserved. This book is licensed under a Creative Commons License. Computer instructions may be extracted from the book under the MIT License. Linux® is a registered trademark of Linus Torvalds. Linux From Scratch - Version 7.8-systemd Table of Contents Preface .......................................................................................................................................................................... vii i. Foreword ............................................................................................................................................................. vii ii. Audience ............................................................................................................................................................ vii iii. LFS Target Architectures ................................................................................................................................ viii iv. LFS and Standards ............................................................................................................................................ ix v. Rationale for Packages in the Book .................................................................................................................... x vi. Prerequisites -

Linux for Zseries: Device Drivers and Installation Commands (March 4, 2002) Summary of Changes
Linux for zSeries Device Drivers and Installation Commands (March 4, 2002) Linux Kernel 2.4 LNUX-1103-07 Linux for zSeries Device Drivers and Installation Commands (March 4, 2002) Linux Kernel 2.4 LNUX-1103-07 Note Before using this document, be sure to read the information in “Notices” on page 207. Eighth Edition – (March 2002) This edition applies to the Linux for zSeries kernel 2.4 patch (made in September 2001) and to all subsequent releases and modifications until otherwise indicated in new editions. © Copyright International Business Machines Corporation 2000, 2002. All rights reserved. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Summary of changes .........v Chapter 5. Linux for zSeries Console || Edition 8 changes.............v device drivers............27 Edition 7 changes.............v Console features .............28 Edition 6 changes ............vi Console kernel parameter syntax .......28 Edition 5 changes ............vi Console kernel examples ..........28 Edition 4 changes ............vi Usingtheconsole............28 Edition 3 changes ............vii Console – Use of VInput ..........30 Edition 2 changes ............vii Console limitations ............31 About this book ...........ix Chapter 6. Channel attached tape How this book is organized .........ix device driver ............33 Who should read this book .........ix Tapedriverfeatures...........33 Assumptions..............ix Tape character device front-end........34 Tape block -

Xen and the Linux Console Or: Why Xencons={Tty,Ttys,Xvc} Will Go Away
Xen and the linux console or: why xencons={tty,ttyS,xvc} will go away. by Gerd Hoffmann <[email protected]> So, what is the Linux console? Well, there isn't a simple answer to that question. Which is the reason for this paper in the first place. For most users it probably is the screen they are sitting in front of. Which is correct, but it also isn't the full story. Especially there are a bunch of CONFIG_*_CONSOLE kernel options referring to two different (but related) subsystems of the kernel. Introducing virtual terminals (CONFIG_VT) Well, every linux user knows them: Virtual terminals. Using Alt-Fx you can switch between different terminals. Each terminal has its own device, namely /dev/tty<nr>. Most Linux distributions have a getty ready for text login on /dev/tty{1-6} and the X-Server for the graphical login on /dev/tty7. /dev/tty0 is a special case: It referes to the terminal which is visible at the moment. The VT subsystem doesn't draw the characters itself though, it has hardware specific drivers for that. The most frequently used ones are: CONFIG_VGA_CONSOLE VGA text console driver, this one will drive your VGA card if you boot the machine in VGA text mode. CONFIG_FRAMEBUFFER_CONSOLE Provides text screens on top of a graphical display. The graphical display in turn is driven by yet another driver. On x86 this very often is vesafb. Other platforms have generic drivers too. There are also a bunch of drivers for specific hardware, such as rivafb for nvidia cards. -
MC-1200 Series Linux Software User's Manual
MC-1200 Series Linux Software User’s Manual Version 1.0, November 2020 www.moxa.com/product © 2020 Moxa Inc. All rights reserved. MC-1200 Series Linux Software User’s Manual The software described in this manual is furnished under a license agreement and may be used only in accordance with the terms of that agreement. Copyright Notice © 2020 Moxa Inc. All rights reserved. Trademarks The MOXA logo is a registered trademark of Moxa Inc. All other trademarks or registered marks in this manual belong to their respective manufacturers. Disclaimer Information in this document is subject to change without notice and does not represent a commitment on the part of Moxa. Moxa provides this document as is, without warranty of any kind, either expressed or implied, including, but not limited to, its particular purpose. Moxa reserves the right to make improvements and/or changes to this manual, or to the products and/or the programs described in this manual, at any time. Information provided in this manual is intended to be accurate and reliable. However, Moxa assumes no responsibility for its use, or for any infringements on the rights of third parties that may result from its use. This product might include unintentional technical or typographical errors. Changes are periodically made to the information herein to correct such errors, and these changes are incorporated into new editions of the publication. Technical Support Contact Information www.moxa.com/support Moxa Americas Moxa China (Shanghai office) Toll-free: 1-888-669-2872 Toll-free: 800-820-5036 Tel: +1-714-528-6777 Tel: +86-21-5258-9955 Fax: +1-714-528-6778 Fax: +86-21-5258-5505 Moxa Europe Moxa Asia-Pacific Tel: +49-89-3 70 03 99-0 Tel: +886-2-8919-1230 Fax: +49-89-3 70 03 99-99 Fax: +886-2-8919-1231 Moxa India Tel: +91-80-4172-9088 Fax: +91-80-4132-1045 Table of Contents 1. -

Debian GNU/Linux Installation Guide
Debian GNU/Linux Installation Guide July 31, 2021 Debian GNU/Linux Installation Guide Copyright © 2004 – 2021 the Debian Installer team This manual is free software; you may redistribute it and/or modify it under the terms of the GNU General Public License. Please refer to the license in Appendix F. Build version of this manual: 20210730. i Contents 1 Welcome to Debian 1 1.1 What is Debian? . 1 1.2 What is GNU/Linux? . 1 1.3 What is Debian GNU/Linux? . 2 1.4 What is the Debian Installer? . 3 1.5 Getting Debian . 3 1.6 Getting the Newest Version of This Document . 3 1.7 Organization of This Document . 3 1.8 About Copyrights and Software Licenses . 4 2 System Requirements 5 2.1 Supported Hardware . 5 2.1.1 Supported Architectures . 5 2.1.2 Three different ARM ports . 6 2.1.3 Variations in ARM CPU designs and support complexity . 6 2.1.4 Platforms supported by Debian/armhf . 6 2.1.5 Platforms no longer supported by Debian/armhf . 8 2.1.6 Multiple Processors . 8 2.1.7 Graphics Hardware Support . 8 2.1.8 Network Connectivity Hardware . 8 2.1.9 Peripherals and Other Hardware . 8 2.2 Devices Requiring Firmware . 8 2.3 Purchasing Hardware Specifically for GNU/Linux . 9 2.3.1 Avoid Proprietary or Closed Hardware . 9 2.4 Installation Media . 9 2.4.1 CD-ROM/DVD-ROM/BD-ROM . 9 2.4.2 Network . 10 2.4.3 Hard Disk . 10 2.4.4 Un*x or GNU system . -

Debian GNU/Linux Installation Guide
Debian GNU/Linux Installation Guide July 31, 2021 Debian GNU/Linux Installation Guide Copyright © 2004 – 2021 the Debian Installer team This manual is free software; you may redistribute it and/or modify it under the terms of the GNU General Public License. Please refer to the license in Appendix F. Build version of this manual: 20210730. i Contents 1 Welcome to Debian 1 1.1 What is Debian? . 1 1.2 What is GNU/Linux? . 1 1.3 What is Debian GNU/Linux? . 2 1.4 What is the Debian Installer? . 3 1.5 Getting Debian . 3 1.6 Getting the Newest Version of This Document . 3 1.7 Organization of This Document . 3 1.8 About Copyrights and Software Licenses . 4 2 System Requirements 5 2.1 Supported Hardware . 5 2.1.1 Supported Architectures . 5 2.1.2 CPU, Main Boards, and Video Support . 6 2.1.2.1 CPU . 6 2.1.2.2 I/O Bus . 6 2.1.3 Laptops . 6 2.1.4 Multiple Processors . 6 2.1.5 Graphics Hardware Support . 6 2.1.6 Network Connectivity Hardware . 7 2.1.6.1 Wireless Network Cards . 7 2.1.7 Braille Displays . 7 2.1.8 Hardware Speech Synthesis . 7 2.1.9 Peripherals and Other Hardware . 7 2.2 Devices Requiring Firmware . 7 2.3 Purchasing Hardware Specifically for GNU/Linux . 8 2.3.1 Avoid Proprietary or Closed Hardware . 8 2.4 Installation Media . 8 2.4.1 CD-ROM/DVD-ROM/BD-ROM . 9 2.4.2 USB Memory Stick . -

REALIZATION of LINUX PLATFORM in DISTRIBUTED CONTROL SYSTEM by EPICS at BEPCII Zhuo Zhao, C.H.Wang, Ge Lei, J.J.Zhao, K.J.Yue, Jia Liu, IHEP, Beijing, China
Proceedings of ICALEPCS2003, Gyeongju, Korea REALIZATION OF LINUX PLATFORM IN DISTRIBUTED CONTROL SYSTEM BY EPICS AT BEPCII Zhuo Zhao, C.H.Wang, Ge Lei, J.J.Zhao, K.J.Yue, Jia Liu, IHEP, Beijing, China Abstract also has friendly operating interface and it supports IHEP will begin the BEPCII project that has been software transplanting. funded by the Chinese Government in order to further At present, Red Hat Linux has developed release 9. So I upgrade the BEPC (Beijing Electron Positron Collider) select the latest release-Red Hat Linux 9 as the operating which has operated since 1989 [1]. As a part of this system that is installed on PC [4]. updating project, control system is decided to use EPICS The installing of ftp server and downloading of [2]. EPICS IOCs can run on many kinds of operating systems [3], for example VxWorks, Unix, Linux, VxWorks kernel Windows, RTEMS and so on. Based on the idea of After the Red Hat Linux 9 has been installed on one creating EPICS OPI on Linux and downloading real-time PC, ftp server should be also installed and started. The ftp database to VME IOC target board, this article is mainly server that I select is vsftpd whose “.rpm” instalation file about how to setup EPICS base and EPICS extension on is included in the Red Hat Linux 9’s installation Linux operating system and furthermore how to finish CDROM. communication between server and Linux control The VxWorks boot file should be in the special platform. In order to come into being a friendly directory in order to download VxWorks kernel. -
Wireless Communication
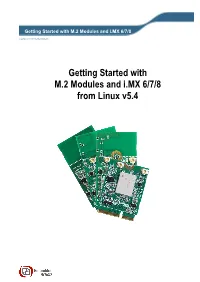
Getting Started with M.2 Modules and i.MX 6/7/8 Copyright 2020 © Embedded Artists AB Getting Started with M.2 Modules and i.MX 6/7/8 from Linux v5.4 Getting Started with M.2 Modules and i.MX 6/7/8 from Linux v5.4 Page 2 Embedded Artists AB Jörgen Ankersgatan 12 SE-211 45 Malmö Sweden http://www.EmbeddedArtists.com Copyright 2020 © Embedded Artists AB. All rights reserved. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language or computer language, in any form or by any means, electronic, mechanical, magnetic, optical, chemical, manual or otherwise, without the prior written permission of Embedded Artists AB. Disclaimer Embedded Artists AB makes no representation or warranties with respect to the contents hereof and specifically disclaim any implied warranties or merchantability or fitness for any particular purpose. Information in this publication is subject to change without notice and does not represent a commitment on the part of Embedded Artists AB. Feedback We appreciate any feedback you may have for improvements on this document. Send your comments by using the contact form: www.embeddedartists.com/contact. Trademarks All brand and product names mentioned herein are trademarks, services marks, registered trademarks, or registered service marks of their respective owners and should be treated as such. Copyright 2020 © Embedded Artists AB Rev A Getting Started with M.2 Modules and i.MX 6/7/8 from Linux v5.4 Page 3 Table of Contents 1 Document Revision History ................................. 5 2 Introduction .......................................................... -
Xen and the Linux Console
Xen and the linux console why xencons={tty,ttyS,xvc} will go away. Gerd Hoffmann <[email protected]> What is the Linux console? ● Answering this question is the point of this talk ... ● For most users it probably is the screen they are sitting in front of. ● The linux kernel has two different (but related) subsystems. ● Both have a bunch of CONFIG_*_CONSOLE config options Virtual Terminals (CONFIG_VT) ● Using Alt-Fx users can switch between different terminals on the same physical screen. ● Each terminal has its own device: /dev/tty<nr>. ● Most Linux distros have getty's running on /dev/tty{1-6}, the X-Server uses /dev/tty7. ● /dev/tty0: The terminal which is visible at the moment. ● The VT subsystem needs a hardware specific drivers for actual output. VT drivers (incomplete) ● CONFIG_VGA_CONSOLE – Drives VGA card in text mode. ● CONFIG_FRAMEBUFFER_CONSOLE – Provides text screens on top of a graphical display. – The graphical display is handled by some fb driver: vesafb (generic), matroxfb, pvfb (xen), ... ● CONFIG_DUMMY_CONSOLE – Used when no other driver is present. – Solves initialization order issues and usually runs for a short time at boot only. Introducing /dev/console ● /dev/console is the linux console device. ● The kernel messages (printk) will go to the console device. ● The kernel boots /sbin/init with /dev/console as terminal. ● Often linked to /dev/tty0. – One reason for the confusion ... – That is only one option though. – Especially there is no strong connection between virtual terminals and /de v/console. About Console drivers ● There are two kinds of console drivers: – Some can just print messages. – The others are associated with a full-featured terminal. -

I.MX Linux® User's Guide NXP Semiconductors
NXP Semiconductors Document identifier: IMXLUG User Guide Rev. LF5.10.52_2.1.0, 30 September 2021 i.MX Linux® User's Guide NXP Semiconductors Contents Chapter 1 Overview............................................................................................... 6 1.1 Audience....................................................................................................................................6 1.2 Conventions...............................................................................................................................6 1.3 Supported hardware SoCs and boards..................................................................................... 6 1.4 References................................................................................................................................ 7 Chapter 2 Introduction........................................................................................... 9 Chapter 3 Basic Terminal Setup.......................................................................... 10 Chapter 4 Booting Linux OS................................................................................ 11 4.1 Software overview................................................................................................................... 11 4.1.1 Bootloader.................................................................................................................................12 4.1.2 Linux kernel image and device tree......................................................................................... -

What's New in RHEL 6 for Linux on System Z?
Hans-Joachim Picht, Linux on System z Initiatives & Linux Champion EMEA <[email protected]> Brad Hinson, Worldwide Lead, Linux on System z <[email protected]> What's New in RHEL 6 for Linux on System z? Linux on System z Live Virtual Class - http://www.vm.ibm.com/education/lvc/ December 15. 2010 © 2010 IBM Corporation Linux on System z Update: Current & Future Linux on System z Technology Structure of Linux on System z Many Linux software packages did not require any code change to run on Linux on System z 0.28 % platform specific code in GCC 4.1 Backend Linux Applications Linux Kernel GNU Runtime Environment Backend Architecture Network Protocols Filesystems GNU ComplierSuite Independent Code Memory Process Generic Drivers Management Management 0.55 % of platform Platform Dependent HW Dependent Drivers specific code Code in Glibc 2.5 System z Instruction Set and I/O Hardware 2 1.81 % platform specific code in Linux Kernel 2.6.25 © 2010 IBM Corporation Linux on System z Update: Current & Future Linux on System z Technology IBM Linux on System z Development IBM Linux on System z Development contributes in the following areas: Kernel, s390-tools, Open Source Tools (e.g. eclipse, ooprofile), GCC, GLIBC, Binutils Upstream Kernel Developer Works Website Community Customer ....the code you use is the result of the efforts of an anonymous army of blue 3 penguins involved in developing, testing, documenting, .... © 2010 IBM Corporation Linux on System z Update: Current & Future Linux on System z Technology Linux on System z Development Focus Integration