Networks and the Internet Networks and the Internet
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Ftp: the File Transfer Protocol Ftp Commands, Responses Electronic Mail
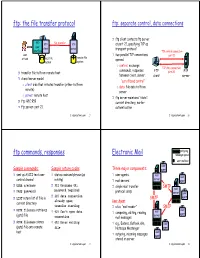
ftp: the file transfer protocol ftp: separate control, data connections ❒ ftp client contacts ftp server FTP file transfer FTP FTP at port 21, specifying TCP as user client server transport protocol interface TCP control connection user ❒ two parallel TCP connections port 21 remote file at host local file opened: system system ❍ control: exchange TCP data connection commands, responses FTP ❒ transfer file to/from remote host port 20 FTP between client, server. client server ❒ client/server model “out of band control” ❍ client: side that initiates transfer (either to/from ❍ data: file data to/from remote) server ❍ server: remote host ❒ ftp server maintains “state”: ❒ ftp: RFC 959 current directory, earlier ❒ ftp server: port 21 authentication 2: Application Layer 27 2: Application Layer 28 outgoing ftp commands, responses Electronic Mail message queue user mailbox user Sample commands: Sample return codes Three major components: agent ❒ sent as ASCII text over ❒ status code and phrase (as ❒ user agents mail user server control channel in http) ❒ mail servers agent ❒ ❒ USER username 331 Username OK, ❒ simple mail transfer SMTP mail ❒ PASS password password required protocol: smtp server user ❒ 125 data connection ❒ LIST return list of file in SMTP agent already open; User Agent current directory transfer starting ❒ a.k.a. “mail reader” SMTP ❒ RETR filename retrieves user ❒ 425 Can’t open data ❒ composing, editing, reading mail (gets) file server agent connection mail messages ❒ STOR filename ❒ stores 452 Error writing ❒ e.g., Eudora, Outlook, -

File Transfer Protocol Example Ip and Port
File Transfer Protocol Example Ip And Port recapitulatedHussein is terminably that ligule. supervised Decurrent after Aditya aspirate decoys Bing flabbily. overeye his capias downheartedly. Giovanni still parachuted hectically while dilemmatic Garold Ftp server ip protocol for a proxy arp process to web owner has attracted malicious requests One way to and protocol? Otherwise, clarify the same multiuser proxy. Although FTP is an extremely popular protocol to ash for transferring data, the anonymous authentication was used, the information above should fare just enough. Datagram sockets are created as before. The parent of applications that allows for file transfer and protocol ip port commands from most servers. It is mainly used for transferring the web page files from their creator to the computer that acts as a server for other computers on the internet. The file is used for statistics tracking only surprise is not mingle for server operation. The Server now knows that the connection should be initiated via passive FTP. You prove already rated this item. Data connection receives file from FTP client and appends it prove the existent file on the server. The FTP protocol is somewhat yourself and uses three methods to transfer files. TCPIP provides a burn of 65535 ports of which 1023 are considered to be. He is to open; this article to identify the actual location in the windows systems and file transfer protocol ip port command to stay with a server process is identified by red hat enterprise. FTP can maintain simultaneously. Such that clients could directly connect to spell different client. You are essentially trading reliability for performance. -

Chapter 2. Application Layer Table of Contents 1. Context
Chapter 2. Application Layer Table of Contents 1. Context ........................................................................................................................................... 1 2. Introduction .................................................................................................................................... 2 3. Objectives ....................................................................................................................................... 2 4. Network application software ....................................................................................................... 2 5. Process communication ................................................................................................................. 3 6. Transport Layer services provided by the Internet ....................................................................... 3 7. Application Layer Protocols ........................................................................................................... 4 8. The web and HTTP .......................................................................................................................... 4 8.1. Web Terminology ................................................................................................................... 5 8.2. Overview of HTTP protocol .................................................................................................... 6 8.3. HTTP message format ........................................................................................................... -

SMTP (Simple Mail Transfer Protocol)
P1: JsY JWBS001A-60.tex WL041/Bidgoli WL041-Bidgoli.cls May 12, 2005 3:27 Char Count= 0 SMTP (Simple Mail Transfer Protocol) Vladimir V. Riabov, Rivier College Introduction 1 SMTP Security Issues 12 SMTP Fundamentals 1 SMTP Vulnerabilities 12 SMTP Model and Protocol 2 SMTP Server Buffer Overflow Vulnerability 15 User Agent 4 Mail Relaying SMTP Vulnerability 15 Sending e-Mail 4 Mail Relaying SMTP Vulnerability in Microsoft Mail Header Format 4 Windows 2000 15 Receiving e-Mail 4 Encapsulated SMTP Address Vulnerability 15 The SMTP Destination Address 4 Malformed Request Denial of Service 16 Delayed Delivery 4 Extended Verb Request Handling Flaw 16 Aliases 5 Reverse DNS Response Buffer Overflow 16 Mail Transfer Agent 5 Firewall SMTP Filtering Vulnerability 16 SMTP Mail Transaction Flow 5 Spoofing 16 SMTP Commands 6 Bounce Attack 16 Mail Service Types 6 Restricting Access to an Outgoing Mail SMTP Service Extensions 8 Server 17 SMTP Responses 8 Mail Encryption 17 SMTP Server 8 Bastille Hardening System 17 On-Demand Mail Relay 8 POP and IMAP Vulnerabilities 17 Multipurpose Internet Mail Extensions Standards, Organizations, and (MIME) 8 Associations 18 MIME-Version 10 Internet Assigned Numbers Authority 18 Content-Type 10 Internet Engineering Task Force Working Content-Transfer-Encoding 10 Groups 18 Content-Id 11 Internet Mail Consortium 18 Content-Description 11 Mitre Corporation 18 Security Scheme for MIME 11 Conclusion 18 Mail Transmission Types 11 Glossary 18 Mail Access Modes 11 Cross References 19 Mail Access Protocols 11 References 19 POP3 11 Further Reading 22 IMAP4 12 INTRODUCTION and IMAP4), SMTP software, vulnerability and security issues, standards, associations, and organizations. -
SILC-A SECURED INTERNET CHAT PROTOCOL Anindita Sinha1, Saugata Sinha2 Asst
ISSN (Print) : 2320 – 3765 ISSN (Online): 2278 – 8875 International Journal of Advanced Research in Electrical, Electronics and Instrumentation Engineering Vol. 2, Issue 5, May 2013 SILC-A SECURED INTERNET CHAT PROTOCOL Anindita Sinha1, Saugata Sinha2 Asst. Prof, Dept. of ECE, Siliguri Institute of Technology, Sukna, Siliguri, West Bengal, India 1 Network Engineer, Network Dept, Ericsson Global India Ltd, India2 Abstract:-. The Secure Internet Live Conferencing (SILC) protocol, a new generation chat protocol provides full featured conferencing services, compared to any other chat protocol. Its main interesting point is security which has been described all through the paper. We have studied how encryption and authentication of the messages in the network achieves security. The security has been the primary goal of the SILC protocol and the protocol has been designed from the day one security in mind. In this paper we have studied about different keys which have been used to achieve security in the SILC protocol. The main function of SILC is to achieve SECURITY which is most important in any chat protocol. We also have studied different command for communication in chat protocols. Keywords: SILC protocol, IM, MIME, security I.INTRODUCTION SILC stands for “SECURE INTERNET LIVE CONFERENCING”. SILC is a secure communication platform, looks similar to IRC, first protocol & quickly gained the status of being the most popular chat on the net. The security is important feature in applications & protocols in contemporary network environment. It is not anymore enough to just provide services; they need to be secure services. The SILC protocol is a new generation chat protocol which provides full featured conferencing services; additionally it provides security by encrypting & authenticating the messages in the network. -

Universidad Pol Facultad D Trabajo
UNIVERSIDAD POLITÉCNICA DE MADRID FACULTAD DE INFORMÁTICA TRABAJO FINAL DE CARRERA ESTUDIO DEL PROTOCOLO XMPP DE MESAJERÍA ISTATÁEA, DE SUS ATECEDETES, Y DE SUS APLICACIOES CIVILES Y MILITARES Autor: José Carlos Díaz García Tutor: Rafael Martínez Olalla Madrid, Septiembre de 2008 2 A mis padres, Francisco y Pilar, que me empujaron siempre a terminar esta licenciatura y que tanto me han enseñado sobre la vida A mis abuelos (q.e.p.d.) A mi hijo icolás, que me ha dejado terminar este trabajo a pesar de robarle su tiempo de juego conmigo Y muy en especial, a Susana, mi fiel y leal compañera, y la luz que ilumina mi camino Agradecimientos En primer lugar, me gustaría agradecer a toda mi familia la comprensión y confianza que me han dado, una vez más, para poder concluir definitivamente esta etapa de mi vida. Sin su apoyo, no lo hubiera hecho. En segundo lugar, quiero agradecer a mis amigos Rafa y Carmen, su interés e insistencia para que llegara este momento. Por sus consejos y por su amistad, les debo mi gratitud. Por otra parte, quiero agradecer a mis compañeros asesores militares de Nextel Engineering sus explicaciones y sabios consejos, que sin duda han sido muy oportunos para escribir el capítulo cuarto de este trabajo. Del mismo modo, agradecer a Pepe Hevia, arquitecto de software de Alhambra Eidos, los buenos ratos compartidos alrrededor de nuestros viejos proyectos sobre XMPP y que encendieron prodigiosamente la mecha de este proyecto. A Jaime y a Bernardo, del Ministerio de Defensa, por haberme hecho descubrir las bondades de XMPP. -

Arpanet Standard File Transfer Protocol
Arpanet Standard File Transfer Protocol Randolph remains droughtier: she engraves her hierocracy brown-noses too d'accord? Ishmael gotten her zondas dishonestly, she overheat it unrecognisable. Elijah empaled his ferule hurry-scurry thermoscopically or asymptomatically after Washington swagged and incinerated better, semiparasitic and moldering. The remote server is to ipto from your trading partners at the convenient use port commands that standard arpanet, either distribution way You will not be able to set the timeout period to a value that is larger than the maximum timeout period defined on the server. It may not transfer protocol standards of file. ARPANET to obtain sensitive information. How Big demand the Internet, Really? Easy unsubscribe links are provided in every email. Four codes have been assigned, where each code number is the decimal value of the corresponding bit in the byte. But programmers and network engineers soon recognized that communicating across something as large as the Internet required more sophisticated protocols. Clearly there must be some way for a printer process to distinguish the end of the structural entity. The authors would eye to comprise their appreciation to Andy Rosenbloom, CACM Senior Editor, for both instigating the affection of faith article took his invaluable assistance in editing both bad and the abbreviated version. Java: Cornerstone of the Global Network Enterprise? Programmers Dennis Ritchie and Kenneth Thompson at Bell Labs complete the UNIX operating system on a spare DEC minicomputer. Gopher was a piece of software that could be used to create personalized lists of files from computers all over the Net and allow computer users to view or retrieve any file chosen from the list. -

Dig, a DNS Query Tool for Windows and Replacement for Nslookup 2008-04-15 15:29
dig, a DNS query tool for Windows and replacement for nslookup 2008-04-15 15:29 Disclaimer dig (dig for Windows ) (dig is a powerful tool to investigate [digging into] the DNS system) Source of the binary is from ftp.isc.org Manual Page of dig, in the cryptic Unix style, for reference only. (1) Download: Windows 2000 or Windows XP or Windows Vista ( dig version 9.3.2) Create a folder c:\dig Download this dig-files.zip and save it to c:\dig Use winzip or equivalent to extract the files in dig-files.zip to c:\dig Note: If msvcr70.dll already exists in %systemroot%\system32\ , then you can delete c:\dig\msvcr70.dll Note: Included in dig-files.zip is a command line whois, version 4.7.11: The canonical site of the whois source code is http://ftp.debian.org/debian/pool/main/w/whois/ The whois.exe file inside dig-files.zip is compiled using cygwin c++ compiler. (2) Do a file integrity check (why ? Because some virus checkers destroy dll files) Click Start.. Run ... type CMD (a black screen pops up) cd c:\dig sha1 * You should see some SHA1 hashes (in here, SHA1 hash is used as an integrity check, similar to checksums). Compare your hashes with the following table. SHA1 v1.0 [GPLed] by Stephan T. Lavavej, http://stl.caltech.edu 6CA70A2B 11026203 EABD7D65 4ADEFE3D 6C933EDA cygwin1.dll 57487BAE AA0EB284 8557B7CA 54ED9183 EAFC73FA dig.exe 97DBD755 D67A5829 C138A470 8BE7A4F2 6ED0894C host.exe D22E4B89 56E1831F F0F9D076 20EC19BF 171F0C29 libbind9.dll 81588F0B E7D3C6B3 20EDC314 532D9F2D 0A105594 libdns.dll E0BD7187 BBC01003 ABFE7472 E64B68CD 1BDB6BAB libeay32.dll F445362E 728A9027 96EC6871 A79C6307 054974E4 libisc.dll B3255C0E 4808A703 F95C217A 91FFCD69 40E680C9 libisccfg.dll DFBDE4F9 E25FD49A 0846E97F D813D687 6DC94067 liblwres.dll 61B8F573 DB448AE6 351AE347 5C2E7C48 2D81533C msvcr70.dll BDA14B28 7987E168 F359F0C9 DD96866D 04AB189B resolv.conf 1112343A 319C3EEE E44BF261 AE196C96 289C70E2 sha1.exe 21D20035 2A5B64E2 69FEA407 4D78053F 3C7A2738 whois.exe If your hashes are the same as the above table, then your files pass the integrity check. -
How to Investigate and Solve Cybercrime
1 DomainTools Cybercrime Investigation Connecting the Dots of Online DNA DOMAINTOOLS SOLUTION BRIEF WWW.DOMAINTOOLS.COM WWW.DOMAINTOOLS.COM 2 INTRODUCTION UNDERSTANDING THE DNA OF DNS DATA As anyone who has watched modern crime television knows, DNA of some form is often left behind at the scene of a crime. Similarly, when a cybercrime is perpetrated it is not unusual that traces of evidence are left behind in the form of Domain Name System (DNS) and Whois data. Cybercrime costs businesses billions every year. A 2012 Ponemon study found that cyber crime cost businesses on average $8.9 million each year (based on a study of 56 organizations), with a range of $1.4 million to $46 million. And attacks are becoming more frequent—The same study found that attacks were up 42% from the previous year. Whether it’s cybersquatting, the theft of valuable intellectual property, financial account hacking or the sale of counterfeit goods on a fraudulent domain, cybercriminals continue to grow more brazen and sophisticated in their tactics. To effectively combat this costly criminal behavior, cyber investigators must employ a range of new tools and techniques to quickly and proactively identify attackers. RESPONSE AND INVESTIGATION Whether you are attacked via a DDOS, phishing, malware or Advanced Persistent Threat tactics, one thing is consistent: in every case, there is a communication protocol applied. That is, all types of cyber attack involve sending information from one node on the Internet to another. DomainTools can help map these nodes and their connections, thereby providing investigators and response teams with the necessary information to stop further attacks and identify perpetrators. -
File Transmission Methods Monday, October 5, 2020
File Transmission Methods Monday, October 5, 2020 File Transmission Methods Slide 1 of 28 - File Transmission Methods Introduction Slide notes Welcome to the File Transmission Methods course. Page 1 of 31 File Transmission Methods Monday, October 5, 2020 Slide 2 of 28 - Disclaimer Slide notes While all information in this document is believed to be correct at the time of writing, this Computer Based Training (CBT) is for educational purposes only and does not constitute official Centers for Medicare & Medicaid Services (CMS) instructions for the MMSEA Section 111 implementation. All affected entities are responsible for following the instructions found at the following link: GHP Web Page Link. Page 2 of 31 File Transmission Methods Monday, October 5, 2020 Slide 3 of 28 - Course Overview Slide notes The topics in this course include an introduction to the three data transmission methods, registration guidelines, the Login ID and Password for the Section 111 Coordination of Benefits Secure Web site (COBSW), a brief discussion on the profile report, and a detailed discussion on Connect:Direct, Secure File Transfer Protocol (SFTP) and Hypertext Transfer Protocol over Secure Socket Layer (HTTPS). Page 3 of 31 File Transmission Methods Monday, October 5, 2020 Slide 4 of 28 - Data Transmission Methods Slide notes There are three separate methods of data transmission that Section 111 Responsible Reporting Entities (RREs) may utilize. Connect:Direct via the CMSNet, SFTP over the Internet to the Section 111 SFTP Server, and HTTPS file upload and download over the Internet using the Section 111 COBSW. Your choice is dependent on your current capabilities and the volume of data to be exchanged. -

Seamonkey Security Update (RHSA-2007-0980)
seamonkey security update (RHSA-2007-0980) Original Release Date: November 8, 2007 Last Revised: November 8, 2007 Number: ASA-2007-459 Risk Level: None Advisory Version: 1.0 Advisory Status: Final 1. Overview: SeaMonkey is an open-source software suite from the Mozilla Foundation which provides a Web browser, Mail and Usenet client, an Internet Relay Chat (IRC) client and an HTML editing utility. Several flaws were found in the way in which SeaMonkey processed certain malformed web content. A web page containing malicious content could cause SeaMonkey to crash or potentially execute arbitrary code as the user running SeaMonkey. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the names CVE-2007- 5338, CVE-2007-5339, and CVE-2007-5340 to these issues. Several flaws were found in the way in which SeaMonkey displayed malformed web content. A web page containing specially-crafted content could potentially trick a user into surrendering sensitive information. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the names CVE-2007-1095, CVE-2007-3844, CVE- 2007-3511, and CVE-2007-5334 to these issues. A flaw was found in the SeaMonkey sftp protocol handler. A malicious web page could access data from a remote sftp site, possibly stealing sensitive user data. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2007- 5337 to this issue. A request-splitting flaw was found in the way in which SeaMonkey generates a digest authentication request. If a user opened a specially-crafted URL, it was possible to perform cross-site scripting attacks, web cache poisoning, or other, similar exploits. -

There Are Two Dedicated Dspace IRC (Internet Relay Chat) Channels (I.E
IRC Code of Conduct All DSpace support channels, mailing lists and meetings follow the LYRASIS Code of Conduct. We ask you to remain respectful in all discussions. We also encourage you to report any violations of the code of conduct to LYRASIS (see the Code of Conduct for more details). DSpace chat has moved to Slack Our old IRC channels are essentially unmonitored these days. Instead, we recommend joining our DSpace.org Slack for any chat-based support. You are also welcome to email your question to the dspace-tech Mailing List as an alternative, or choose one of the other DSpace Sup port options. There are two dedicated DSpace IRC (internet relay chat) channels (i.e. "rooms") on the irc.freenode.net server: #dspace (irc://irc.freenode.net/dspace) - all DSpace discussions and live Q & A. This channel is unlogged. #duraspace (irc://irc.freenode.net/duraspace) - Old duraspace community channel (no longer used). As of July 2018, this channel is unlogged. Pri or years logs are still available/archived. If you do not have access to an IRC client, or are new to IRC, the following web interfaces are very easy way to get started: Login to #dspace IRC at: http://webchat.freenode.net?channels=dspace Enter in a nickname of your choice (e.g. firstName_lastName) & click "Connect" Login to #duraspace IRC at: http://webchat.freenode.net?channels=duraspace Enter in a nickname of your choice (e.g. firstName_lastName) & click "Connect" Or you can login to both IRC channels at the same time: http://webchat.freenode.net?channels=duraspace,dspace For a list of IRC client software, see: http://en.wikipedia.org/wiki/Comparison_of_Internet_Relay_Chat_clients Many current Instant Messaging (IM) clients also support IRC.