What Is the Shell? • the Login Shell
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

UKUI: a Lightweight Desktop Environment Based on Pluggable
2016 International Conference on Artificial Intelligence and Computer Science (AICS 2016) ISBN: 978-1-60595-411-0 UKUI: A Lightweight Desktop Environment Based on Pluggable Framework for Linux Distribution Jie YU1, Lu SI1,*, Jun MA1, Lei LUO1, Xiao-dong LIU1, Ya-ting KUANG2, Huan PENG2, Rui LI1, Jin-zhu KONG2 and Qing-bo WU1 1College of Computer, National University of Defense Technology, Changsha, China 2Tianjin KYLIN Information Technology Co., Ltd, Tianjin, China *[email protected] *Corresponding author Keywords: Desktop environment, Ubuntu, User interface. Abstract. Ubuntu is an operating system with Linux kernel based on Debian and distributed as free and open-source software. It uses Unity as its default desktop environment, which results in more difficulties of usage for Microsoft Windows users. In this paper, we present a lightweight desktop environment named UKUI based on UbuntuKylin, the official Chinese version of Ubuntu, for Linux distribution. It is designed as a pluggable framework and provides better user experience during human-computer interaction. In order to evaluate the performance of UKUI, a set of testing bench suits were performed on a personal computer. Overall, the results showed that UKUI has better performance compared with Unity. Introduction Linux is a freely available operating system (OS) originated by Linux Torvalds and further developed by thousands of others. Typically, Linux is packaged in a form known as a Linux distribution for both desktop and server use. Some of the most popular mainstream Linux distributions are Red Hat [1], Ubuntu [2], Arch [3], openSUSY [4], Gentoo [5], etc. There are several desktop environments available for nowadays modern Linux distributions, such as XFCE [6], GNOME [7], KDE [8] and LXDE [9]. -

Shell Script & Advance Features of Shell Programming
Kirti Kaushik et al, International Journal of Computer Science and Mobile Computing, Vol.4 Issue.4, April- 2015, pg. 458-462 Available Online at www.ijcsmc.com International Journal of Computer Science and Mobile Computing A Monthly Journal of Computer Science and Information Technology ISSN 2320–088X IJCSMC, Vol. 4, Issue. 4, April 2015, pg.458 – 462 RESEARCH ARTICLE Shell Script & Advance Features of Shell Programming Kirti Kaushik* Roll No.15903, CS, Department of Computer science, Dronacharya College of Engineering, Gurgaon-123506, India Email: [email protected] Jyoti Yadav Roll No. 15040, CS, Department of Applied Computer science, Dronacharya College of Engineering, Gurgaon-123506, India Email: [email protected] Kriti Bhatia Roll No. 15048, CS, Department of Applied Computer science, Dronacharya College of Engineering, Gurgaon-123506, India Email: [email protected] Abstract-- In this research paper, the idea of shell scripting and writing computer programs is examined and different parts of shell programming are likewise contemplated. A shell script is a PC system intended to be controlled by the UNIX shell which is a charge line translator. The different tongues of shell scripts are thought to be scripting dialects. Regular operations performed by shell scripts incorporate document control, program execution, and printing content. A shell script can give an advantageous variety ofa framework order where unique environment settings, charge alternatives, or post-transforming apply naturally, yet in a manner that permits the new script to still go about as a completely typical UNIX summon. The real ideas like Programming in the Borne and C-shell, in which it would be clarified that how shell programming could be possible in Borne and C-shell. -
Openvms Security
OpenVMS Security Presented by Paul Williams PARSEC Group 999 18th Street, Suite 1725 Denver, CO 80202 www.parsec.com | 888-4-PARSEC To Download this Presentation, please visit: http://www.parsec.com/public/openvmssecurity.pdf To E-mail Paul [email protected] www.parsec.com | 888-4-PARSEC Outline • OpenVMS Security Design • Physical Security • Object Security • UIC/ACL Security • User Access • Break-in Detection • Network and Internet Considerations • Encrypted Network Communication • Kerberos • Secure Socket Layer (SSL) Goals • Discuss the important points and consideration of OpenVMS Security • Concentrate on the mechanics and mechanisms of OpenVMS features. • Show how OpenVMS is one of the most secure operating systems on the market. OpenVMS Security Design • Security was designed into OpenVMS since V1.0 • Many different levels of security in OpenVMS Physical Security Object Security User Management Network Security • Has never had a virus Physical Security • System • System Console • Storage devices and media System Disk Data and Database Volumes Backups • Network devices and media Physical Security: System • Increase system reliability through restricted access Prevent intentional tampering and outage Prevent outage due to accidents • Prevent Front Panel Access Halts Reset/initializations Power switch/source Power on action settings (VAX) switch Physical Security: Console • Can be a big security hole for OpenVMS Anyone with physical access to the console can break into OpenVMS buy getting into the SYSBOOT utility. Then OpenVMS can be broken into: Buy redirecting startup Buy changing system parameters Physical Security: Getting to SYSBOOT on the Integrity Console Example • On the Integrity shutdown to the EFI Boot Manager and select the EFI Shell and create a alias. -

Mac OS X: an Introduction for Support Providers
Mac OS X: An Introduction for Support Providers Course Information Purpose of Course Mac OS X is the next-generation Macintosh operating system, utilizing a highly robust UNIX core with a brand new simplified user experience. It is the first successful attempt to provide a fully-functional graphical user experience in such an implementation without requiring the user to know or understand UNIX. This course is designed to provide a theoretical foundation for support providers seeking to provide user support for Mac OS X. It assumes the student has performed this role for Mac OS 9, and seeks to ground the student in Mac OS X using Mac OS 9 terms and concepts. Author: Robert Dorsett, manager, AppleCare Product Training & Readiness. Module Length: 2 hours Audience: Phone support, Apple Solutions Experts, Service Providers. Prerequisites: Experience supporting Mac OS 9 Course map: Operating Systems 101 Mac OS 9 and Cooperative Multitasking Mac OS X: Pre-emptive Multitasking and Protected Memory. Mac OS X: Symmetric Multiprocessing Components of Mac OS X The Layered Approach Darwin Core Services Graphics Services Application Environments Aqua Useful Mac OS X Jargon Bundles Frameworks Umbrella Frameworks Mac OS X Installation Initialization Options Installation Options Version 1.0 Copyright © 2001 by Apple Computer, Inc. All Rights Reserved. 1 Startup Keys Mac OS X Setup Assistant Mac OS 9 and Classic Standard Directory Names Quick Answers: Where do my __________ go? More Directory Names A Word on Paths Security UNIX and security Multiple user implementation Root Old Stuff in New Terms INITs in Mac OS X Fonts FKEYs Printing from Mac OS X Disk First Aid and Drive Setup Startup Items Mac OS 9 Control Panels and Functionality mapped to Mac OS X New Stuff to Check Out Review Questions Review Answers Further Reading Change history: 3/19/01: Removed comment about UFS volumes not being selectable by Startup Disk. -
SUSE® Linux Enterprise Desktop 12 and the Workstation Extension: What's New ?
SUSE® Linux Enterprise Desktop 12 and the Workstation Extension: What's New ? Frédéric Crozat <[email protected]> Enterprise Desktop Release Manager Scott Reeves <[email protected]> Enterprise Desktop Development Manager Agenda • Design Criteria • Desktop Environment in SUSE Linux Enterprise 12 • GNOME Shell • Desktop Features and Applications 2 Design Criteria SUSE Linux Enterprise Desktop Interoperability Ease of Use Security Ease of Management Lower Costs 4 SUSE Linux Enterprise Desktop 12 • Focus on technical workstation ‒ Developers and System administrators • One tool for the job • Main desktop applications will be shipped: ‒ Mail client, Office Suite, Graphical Editors, ... • SUSE Linux Enterprise Workstation Extension ‒ Extend SUSE Linux Enterprise Server with packages only available on SUSE Linux Enterprise Desktop. (x86-64 only) 5 Desktop in SUSE Linux Enterprise 12 As Part of the Common Code Base SUSE Linux Enterprise 12 Desktop Environment • SUSE Linux Enterprise 12 contains one primary desktop environment • Additional light-weight environment for special use-cases: ‒ Integrated Systems • Desktop environment is shared between the server and desktop products 7 SUSE Linux Enterprise 12 Desktop Environment • GNOME 3 is the main desktop environment ‒ SLE Classic mode by default ‒ GNOME 3 Classic Mode and GNOME 3 Shell Mode also available • SUSE Linux Enterprise 12 ships also lightweight IceWM ‒ Targeted at Integrated Systems • QT fully supported: ‒ QT5 supported for entire SLE12 lifecycle ‒ QT4 supported, will be removed in future -

Program That Runs Other Programs Unix/Linux Process Hierarchy Shell
shell: program that runs other programs Building a Shell 1 5 Unix/Linux Process Hierarchy shell program that runs other programs on behalf of the user sh Original Unix shell (Stephen Bourne, AT&T Bell Labs, 1977) [0] bash “Bourne-Again” Shell, widely used default on most Unix/Linux/Mac OS X systems others.. init [1] while (true) { Print command prompt. Daemon Login shell Read command line from user. e.g. httpd Parse command line. If command is built-in, do it. Child Child Child Else fork process to execute command. in child: Execute requested command with execv. (never returns) Grandchild Grandchild in parent: Wait for child to complete. } 6 7 1 terminal ≠ shell Background vs. Foreground User interface to shell and other programs. Users generally run one command at a time Graphical (GUI) vs. command-line (CLI) Type command, read output, type another command Command-line terminal (emulator): Input (keyboard) Some programs run “for a long time” Output (screen) $ emacs fizz. txt # shell stuck until ema cs exi ts. A “background” job is a process we don't want to wait for $ emacs boom. txt & # em acs ru ns in backg round [1] 9073 # wh ile sh ell i s... $ gdb ./ umbre lla # im mediat ely r eady f or nex t com mand don't do this with emacs un l es s u si n g X wi nd o ws vers i o n 8 9 Managing Background Jobs Signals Signal: small message notifying a process of event in system Shell waits for and reaps foreground jobs. -
Reactos0.3.3 System Requirements
R e a Overview c t Since the past decade, developers from around the world are working hard to make ReactOS O a reality. Intended to be fully compatible with Windows applications and hardware drivers, ReactOS will finally provide an alternative to people wishing to embrace open source but S remain hindered by the lack of Linux versions for their everyday software or incompatible hardware. ReactOS is an open implementation of the Windows platform, built from the 0 . ground up with an NT-compatible kernel, Win32 subsystem and shell. It ships with its own 3 . version of the familiar Explorer shell, ensuring newcomers will have a familiar and seamless 3 experience. Not only that, ReactOS aims to avoid many common security pitfalls caused by poor planning or implementation in Windows, better protecting users from malicious viruses and attacks. 0.3.3 ReactOS 0.3.3 features a completed kernel rewrite, which vastly increases stability and functionality. It is far superior to the previous release when it comes to hardware compatibility and easily surpasses it in software compatibility. Many applications that failed to work in 0.3.1 have returned and look better than ever. 0.3.3 signifies the most improvements visible to end users in a long time, with additions to the control panel and improved GUI rendering without glitches. Gamers can also rejoice as Unreal Tournament '99 once more works on 0.3.3, demonstrating the potential ReactOS holds as a gaming platform. ReactOS has also reached the point where it can run a virtualised version of itself in QEMU, a further step forward in making ReactOS truly self-hosting. -
Simple Shell Scripting for Scientists
Simple Shell Scripting for Scientists Day Three Julian King Bruce Beckles University of Cambridge Computing Service 1 Introduction • Who: ! Julian King, Unix Support, UCS ! Bruce Beckles, e-Science Specialist, UCS • What: ! Simple Shell Scripting for Scientists course, Day Three ! Part of the Scientific Computing series of courses • Contact (questions, etc): ! [email protected] • Health & Safety, etc: ! Fire exits • Please switch off mobile phones! [email protected] Simple Shell Scripting for Scientists: Day Three 2 As this course is part of the Scientific Computing series of courses run by the Computing Service, all the examples that we use will be more relevant to scientific computing than to system administration, etc. This does not mean that people who wish to learn shell scripting for system administration and other such tasks will get nothing from this course, as the techniques and underlying knowledge taught are applicable to shell scripts written for almost any purpose. However, such individuals should be aware that this course was not designed with them in mind. 2 What we don’t cover • Different types of shell: ! We are using the Bourne-Again SHell (bash). • Differences between versions of bash • Very advanced shell scripting – try one of these courses instead: ! “Python: Introduction for Absolute Beginners” ! “Python: Introduction for Programmers” [email protected] Simple Shell Scripting for Scientists: Day Three 3 bash is probably the most common shell on modern Unix/Linux systems – in fact, on most modern Linux distributions it will be the default shell (the shell users get if they don’t specify a different one). -

Introduction to Unix Shell (Part I)
Introduction to Unix shell (part I) Evgeny Stambulchik Faculty of Physics, Weizmann Institute of Science, Rehovot 7610001, Israel Joint ICTP-IAEA School on Atomic Processes in Plasmas February 27 – March 3, 2017 Trieste, Italy Contrary to popular belief, Unix is user friendly. It just happens to be very selective about who it decides to make friends with. Unknown Initially used at Bell Labs, but soon licensed to academy (notably, U. of California, Berkeley) and commercial vendors (IBM, Sun, etc). There are two major products that came out of Berkeley: LSD and Unix. We don’t believe this to be a coincidence. Jeremy S. Anderson, Unix systems administrator Historical overview (kind of) Unix is a family of multiuser, multitasking operating systems stemming from the original Unix developed in the 1970’s at Bell Labs by Ken Thompson, Dennis Ritchie1, and others. Some consider Unix to be the second most important invention to come out of AT&T Bell Labs after the transistor. Dennis Ritchie 1Also famous for creating the C programming language. Historical overview (kind of) Unix is a family of multiuser, multitasking operating systems stemming from the original Unix developed in the 1970’s at Bell Labs by Ken Thompson, Dennis Ritchie1, and others. Some consider Unix to be the second most important invention to come out of AT&T Bell Labs after the transistor. Dennis Ritchie Initially used at Bell Labs, but soon licensed to academy (notably, U. of California, Berkeley) and commercial vendors (IBM, Sun, etc). There are two major products that came out of Berkeley: LSD and Unix. -

Natural Shell: an Assistant for End-User Scripting
International Journal of People-Oriented Programming Volume 5 • Issue 1 • January-June 2016 Natural Shell: An Assistant for End-User Scripting Xiao Liu, College of Information Sciences and Technology, Pennsylvania State University, University Park, PA, USA Yufei Jiang, College of Information Sciences and Technology, Pennsylvania State University, University Park, PA, USA Lawrence Wu, College of Information Sciences and Technology, Pennsylvania State University, University Park, PA, USA Dinghao Wu, College of Information Sciences and Technology, Pennsylvania State University, University Park, PA, USA ABSTRACT Scripting is a widely-used way to automate the execution of tasks. Despite the popularity of scripting, it remains difficult to use for both beginners and experts: because of the cryptic commands for the first group, and incompatible syntaxes across different systems, for the latter group. The authors introduce Natural Shell, an assistant for enabling end-users to generate commands and scripts for various purposes. Natural Shell automatically synthesizes scripts for different shell systems based on natural language descriptions. By interacting with Natural Shell, new users can learn the basics of scripting languages without the obstacles from the incomprehensible syntaxes. On the other hand, the authors’ tool frees more advanced users from manuals when they switch shell systems. The authors have developed a prototype system and demonstrate its effectiveness with a benchmark of 50 examples of popular shell commands collected from online forums. In addition, the authors analyzed the usage of Natural Shell in a lab study that involves 10 participants with different scripting skill levels. Natural Shell effectively assists the users to generate commands in assigned syntaxes and greatly streamlines their learning and using experience. -

Project #1: Command-Line User Interface Shell and Utilities Principles of Operating Systems (LAB) COP 4610/CGS 5764 (Fall 2014)
Project #1: Command-Line User Interface Shell and Utilities Principles of Operating Systems (LAB) COP 4610/CGS 5764 (Fall 2014) Due Date and Time: Refer to the lab calendar at: http://www.cs.fsu.edu/~cop4610t/calendar.html. 1 Overview For this project you will implement a command-line (text-based) user interface shell. The purpose of this shell is to provide a means for users to interact with an operating system (OS). Your shell is to provide a subset of the UNIX utilities as well as some non-UNIX ones. The behavior of the UNIX utilities (denoted in this document by the UNIX tag next to their name) should adhere to the Single UNIX Specification (SUS) standards published by The Open Group. The additional non-UNIX utilities and features (identified by the NON-UNIX tag next to their name) are detailed in this document and during the lab lecture(s). 2 Objectives The objective of this project is to develop an initial understanding of the components of an OS and approaches to implement them. Upon successful completion of this project, the student should possess the following understanding and skills. • Understand one commonly used process model to execute program instructions. • Understand the effect of practical factors on implementing OS utilities. • Commonly used means to communicate with both the OS and the user. • Reasonable ability to implement OS functionality using C. • Low-level programming development and debugging skills. 3 Required Operation The following details the required behavior of the implemented shell. 3.1 Prompt NON-UNIX The shell should output a prompt when it can accept new commands. -
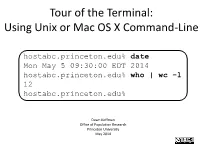
Tour of the Terminal: Using Unix Or Mac OS X Command-Line
Tour of the Terminal: Using Unix or Mac OS X Command-Line hostabc.princeton.edu% date Mon May 5 09:30:00 EDT 2014 hostabc.princeton.edu% who | wc –l 12 hostabc.princeton.edu% Dawn Koffman Office of Population Research Princeton University May 2014 Tour of the Terminal: Using Unix or Mac OS X Command Line • Introduction • Files • Directories • Commands • Shell Programs • Stream Editor: sed 2 Introduction • Operating Systems • Command-Line Interface • Shell • Unix Philosophy • Command Execution Cycle • Command History 3 Command-Line Interface user operating system computer (human ) (software) (hardware) command- programs kernel line (text (manages interface editors, computing compilers, resources: commands - memory for working - hard-drive cpu with file - time) memory system, point-and- hard-drive many other click (gui) utilites) interface 4 Comparison command-line interface point-and-click interface - may have steeper learning curve, - may be more intuitive, BUT provides constructs that can BUT can also be much more make many tasks very easy human-manual-labor intensive - scales up very well when - often does not scale up well when have lots of: have lots of: data data programs programs tasks to accomplish tasks to accomplish 5 Shell Command-line interface provided by Unix and Mac OS X is called a shell a shell: - prompts user for commands - interprets user commands - passes them onto the rest of the operating system which is hidden from the user How do you access a shell ? - if you have an account on a machine running Unix or Linux , just log in. A default shell will be running. - if you are using a Mac, run the Terminal app.