The Problem of Spyware
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cisco Identity Services Engine Supported Windows AV/AS/PM/DE
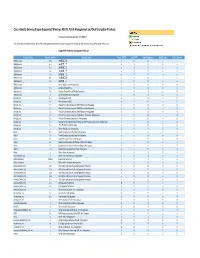
Cisco Identity Services Engine Supported Windows AS/AV, Patch Management and Disk Encryption Products Compliance Module Version 3.6.10363.2 This document provides Windows AS/AV, Patch Management and Disk Encryption support information on the the Cisco AnyConnect Agent Version 4.2. Supported Windows Antispyware Products Vendor_Name Product_Version Product_Name Check_FSRTP Set_FSRTP VirDef_Signature VirDef_Time VirDef_Version 360Safe.com 10.x 360安全卫士 vX X v v 360Safe.com 4.x 360安全卫士 vX X v v 360Safe.com 5.x 360安全卫士 vX X v v 360Safe.com 6.x 360安全卫士 vX X v v 360Safe.com 7.x 360安全卫士 vX X v v 360Safe.com 8.x 360安全卫士 vX X v v 360Safe.com 9.x 360安全卫士 vX X v v 360Safe.com x Other 360Safe.com Antispyware Z X X Z X Agnitum Ltd. 7.x Outpost Firewall Pro vX X X O Agnitum Ltd. 6.x Outpost Firewall Pro 2008 [AntiSpyware] v X X v O Agnitum Ltd. x Other Agnitum Ltd. Antispyware Z X X Z X AhnLab, Inc. 2.x AhnLab SpyZero 2.0 vv O v O AhnLab, Inc. 3.x AhnLab SpyZero 2007 X X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2007 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2008 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2009 Platinum AntiSpyware v v O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 7.0 Platinum Enterprise AntiSpyware v X O v O AhnLab, Inc. 8.x AhnLab V3 Internet Security 8.0 AntiSpyware v v O v O AhnLab, Inc. -

Vipre Antivirus Premium User Guide
Use of this software is subject to the End User License Agreement found in the product directory (C:\Program Files\Sunbelt Software\VIPRE\eula.rtf). By installing the software, you agree to accept the terms of the License Agreement. VIPRE® Antivirus Premium v.4.0. Copyright (c) 2010 Sunbelt Software, Inc. All rights reserved. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies. Information in this document is subject to change without notice. No part of this publication may be reproduced, photocopied, stored in a retrieval system, transmitted, or translated into any language without the prior written permission of Sunbelt Software, Inc. VIPRE® Antivirus Premium User Guide 2 http://www.sunbeltsoftware.com/support Copyright© 2010 Sunbelt Software, Inc. [email protected] All rights reserved. Toll-free Technical Support: 877-673-1153 Table of Contents Chapter 1: Introduction .............................................................................................................................1 System Requirements ............................................................................................................................................ 2 Threats to your Computer...................................................................................................................................... 3 Key Features......................................................................................................................................................... -
CONTENTS in THIS ISSUE Fighting Malware and Spam
JULY 2008 Fighting malware and spam CONTENTS IN THIS ISSUE 2 COMMENT MEMORY GAME A commitment to quality and reliability Eric Filiol describes a set of computer memory weaknesses that could enable the theft of sensitive data via malware attacks. 3 NEWS page 6 IT heavyweights combine forces to fi ght cyber crime SNAKES AND LADDERS Liar, liar The object-oriented programming language Python can be used for many kinds of software Fast fl ux trojan author in court development – potentially including malware development. Aleksander Czarnowski believes in 3 VIRUS PREVALENCE TABLE being prepared and provides a brief overview of how to reverse engineer a Python module. page 10 4 VIRUS ANALYSIS THE WAITING GAME The road less truvelled: W32/Truvel This month John Hawes got his hands on a beta version of FEATURES the long-awaited VIPRE from 6 New memory persistence threats anti-spyware expert Sunbelt Software and found it to be 10 Reversing Python modules well worth the wait. 13 Advertising database poisoning page 16 16 PRODUCT REVIEW Sunbelt Software VIPRE Antivirus + Antispyware This month: anti-spam news and events, and 20 END NOTES & NEWS Paul Baccas questions whether spear phishing is on the rise. ISSN 1749-7027 COMMENT ‘The purpose of the VB100 is Tests that pit products against the WildList have never claimed to prove that a given product can detect all to provide a regular measure of known malware (which would be impossible to prove) the competence, reliability and and they do not attempt to rank products against one another on the basis of detecting more or fewer of the credibility of software vendors in samples listed. -

Dealing with Adware and Spyware
SECURITY Dealing With Adware And Spyware Lisa Phifer You'll need a hybrid of host- ment just by reducing spyware remediation cost. Webroot estimates that help de.sk calls, resurrect- and network-based ing compromised workstations and the resulting approaches, as well as the down time run about $250 per user, per year (a security professional's calculation is shown in Figure 1). Potential return on investment does not end greatest asset: Constant there. Spyware not only slows desktops; it saps vigilance. worker productivity and hogs bandwidth. Accord- ing to SurfControl, ISPs find that peer-to-peer f early viruses like BubbleBoy and LoveBug spyware programs (e.g., Grokster, KaZaA, make you pine for simpler times, then you are Limewire) generate up to 70 percent of network probably waging war against this millenni- traffic. Spyware that exposes private data may um's far more tenacious foe: The stubborn result in embarrassing public disclosure, costly Icrop of spyware that now infests three out of four customer notificafion and compliance violations PCs. From pesky adware like BonziBuddy to that bring hefty fines. Spyware is also a popular malicious malware like Trojan-Down loader-Zlob, vector for executing electronic crimes like identi- spyware is literally choking corporate desktops ty theft and on-line fraud. In one well-publicized and networks. Responsible for one out of four case, 22 Israelis were anested for using spyware help desk calls and half of the PC crashes report- to commit corporate espionage. Wbite data theft ed to Microsoft, spyware is draining IT resources costs are notoriously difficult to quantify, the and business productivity. -
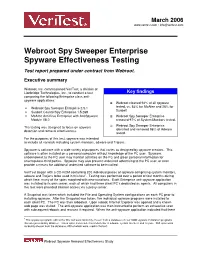
Webroot Spy Sweeper Enterprise Spyware Effectiveness Testing Test Report Prepared Under Contract from Webroot
March 2006 www.veritest.com • [email protected] Webroot Spy Sweeper Enterprise Spyware Effectiveness Testing Test report prepared under contract from Webroot. Executive summary Webroot, Inc. commissioned VeriTest, a division of Lionbridge Technologies, Inc., to conduct a test Key findings comparing the following Enterprise class anti- spyware applications: Webroot cleaned 94% of all spyware • Webroot Spy Sweeper Enterprise 2.5.1 tested, vs. 53% for McAfee and 26% for Sunbelt • Sunbelt CounterSpy Enterprise 1.5.268 • McAfee AntiVirus Enterprise with AntiSpyware Webroot Spy Sweeper Enterprise Module V8.0 removed 97% of System Monitors tested. Webroot Spy Sweeper Enterprise The testing was designed to focus on spyware identified and removed 96% of Adware detection and removal effectiveness. tested. For the purposes of this test, spyware was intended to include all varietals including system monitors, adware and Trojans. Spyware is software with a wide variety of purposes that varies as designed by spyware creators. This software is often installed on a personal computer without knowledge of the PC user. Spyware, unbeknownst to the PC user may monitor activities on the PC and glean personal information for unscrupulous third parties. Spyware may also present undesired advertising to the PC user, or even provide a means for additional undesired software to be installed. VeriTest began with a CD-ROM containing 200 individual pieces of spyware comprising system monitors, adware and Trojans to be used in this test1. Testing was performed over a period of four months during which time, many of the spies morphed with new variations. Each Enterprise anti-spyware application was installed to its own server, each of which had three client PC’s dedicated as agents. -
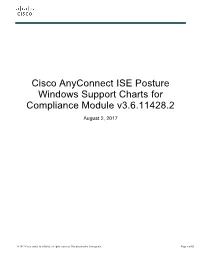
Cisco Anyconnect ISE Posture Windows Support Charts for Compliance Module V3.6.11428.2
Cisco AnyConnect ISE Posture Windows Support Charts for Compliance Module v3.6.11428.2 August 2, 2017 © 2017 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 65 Contents Anti-Virus .................................................................................................................................................................................... 3 Anti-Spyware ............................................................................................................................................................................ 43 Patch Management................................................................................................................................................................... 59 Disk Encryption ........................................................................................................................................................................ 61 ©2017 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 2 of 65 This document lists the Windows OS anti-virus, anti-spyware, patch management, and disk encryption products that are supported by the ISE Posture Agent. The Windows compliance modules are version 3.6.11428.2. Anti-Virus Definition State Product Name Product Version Live Update Min. Compliance Module Version Check 360Safe.com 360 Antivirus 1.x yes yes 3.4.16.1 360 Antivirus 3.x yes - 3.5.5767.2 360 Total Security 4.x yes - 3.6.9335.2 360 Total Security 5.x yes - 3.6.9872.2 360 Total Security 6.x yes - 3.6.9908.2 360 Total Security 7.x yes - 3.6.10231.2 360 Total Security 8.x yes - 3.6.10547.2 360天擎 6.x - - 3.6.11017.2 360杀毒 1.x yes - 3.4.13.1 360杀毒 2.x yes - 3.4.25.1 360杀毒 3.x - - 3.5.2101.2 360杀毒 4.x - - 3.5.6528.2 360杀毒 5.x yes - 3.6.8769.2 Other 360Safe.com Antivirus x - - 3.5.2101.2 AEC, spol. s r.o. Other AEC, spol. s r.o. Antivirus x - - 3.5.2101.2 TrustPort Antivirus 2.x - yes 3.4.8.1 Agnitum Ltd. -

Sentriant® AG200
Extreme Networks Data Sheet Sentriant® AG200 While efforts to improve network security have been focused on locking down the network perimeter and securing critical internal network assets, the security of endpoint devices, which make up the majority of devices on the network, have gone largely untouched. Security attacks, however, are increasingly originating from endpoint devices such as LAN workstations, remote access laptops and home computers to compromise networks. The reason Network Access Control (NAC)—protects the network by verifying is simple: endpoint devices typically bypass that endpoint devices are free from threats and in standard perimeter security measures and compliance with IT security policies. connect directly into the network. Extreme Networks® Sentriant AG200 verifies Advanced Endpoint Integrity Testing that endpoint devices accessing the network, • Flexible access policies such as laptops and desktops, are free from • Comprehensive test suite security threats and in compliance with the organization’s security standards. It systematically • Pre-connect testing tests endpoint devices for compliance with • Wide range of endpoint support organizational security policies, quarantining non-compliant machines before they can damage Flexible Deployment Options the network. • Multiple enforcement methods Sentriant AG200 dramatically reduces the cost • Single-server or multi-server deployment and effort of securing internal network access. It • Simple, easy installation and rollout tests devices used by remote employees -

Products Supported by ESAP 1.4.8
Products supported by ESAP 1.4.8 FIREWALL PRODUCTS: Product Name AOL Firewall (1.x) AOL Privacy Wall (2.x) AVG 8.0 [Firewall] (8.x) AVG Firewall (7.x) AhnLab Security Pack (2.x) AhnLab V3 Internet Security 2007 (7.x) AhnLab V3 Internet Security 2007 Platinum (7.x) AhnLab V3 Internet Security 2008 Platinum (7.x) AhnLab V3 Internet Security 7.0 Platinum Enterprise (7.x) Aliant Busines Security Suite Desktop Firewall (7.x) Aliant Business Security Suite Desktop Firewall (6.x) Aliant Security Services Personal Firewall (7.x) Aluria Security Center Firewall (1.x) Armor2net Personal Firewall (3.x) Avira Premium Security Suite (7.x) Avira Premium Security Suite (9.x) BellSouth Internet Security Firewall (5.x) BitDefender 8 Professional Plus (8.x) BitDefender 9 Internet Security (9.x) BitDefender 9 Professional Plus (9.x) BitDefender Antivirus Plus v10 (10.x) BitDefender Client Professional Plus (8.x) BitDefender Internet Security 2008 (11.x) BitDefender Internet Security 2009 (12.x) BitDefender Internet Security v10 (10.x) BitDefender Professional Edition (7.x) BitDefender Total Security 2008 (11.x) BitDefender Total Security 2009 (12.x) BlackICE (3.x) BlackICE (4.x) BlackICE (5.x) BlackICE (6.x) BlackICE (7.x) BullGuard 7.0 Firewall (7.x) BullGuard 8.0 Firewall (8.x) BullGuard Gamers Edition (8.x) CA Personal Firewall (10.x) CA Personal Firewall (11.x) CA Personal Firewall (9.x) COMODO Firewall Pro (2.x) COMODO Firewall Pro (3.x) COMODO Internet Security (3.x) Cisco Security Agent (5.x) Cisco Security Agent (6.x) CyberArmor Personal Firewall -
Windows XP Hacks & Mods for Dummies
01_748978 ffirs.qxd 8/31/05 12:06 AM Page iii Windows® XP Hacks & Mods FOR DUMmIES‰ by Woody Leonhard 01_748978 ffirs.qxd 8/31/05 12:06 AM Page ii 01_748978 ffirs.qxd 8/31/05 12:06 AM Page i Windows® XP Hacks & Mods FOR DUMmIES‰ 01_748978 ffirs.qxd 8/31/05 12:06 AM Page ii 01_748978 ffirs.qxd 8/31/05 12:06 AM Page iii Windows® XP Hacks & Mods FOR DUMmIES‰ by Woody Leonhard 01_748978 ffirs.qxd 8/31/05 12:06 AM Page iv Windows® XP Hacks & Mods For Dummies® Published by Wiley Publishing, Inc. 111 River Street Hoboken, NJ 07030-5774 www.wiley.com Copyright © 2005 by Wiley Publishing, Inc., Indianapolis, Indiana Published by Wiley Publishing, Inc., Indianapolis, Indiana Published simultaneously in Canada No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permit- ted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permission should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4355, or online at http://www.wiley.com/go/permissions. Trademarks: Wiley, the Wiley Publishing logo, For Dummies, the Dummies Man logo, A Reference for the Rest of Us!, The Dummies Way, Dummies Daily, The Fun and Easy Way, Dummies.com, and related trade dress are trademarks or registered trademarks of John Wiley & Sons, Inc.