Juniper Networks Inc(Jnpr)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
2012 Annual Report
2012 Annual Report Notice of 2013 Annual Meeting of Stockholders and Proxy Statement Report on Form 10-K Dear Juniper Stockholder, From a financial perspective, Juniper began to return to improving performance in the second half of 2012. While we were not satisfied with our results, we believe we can and will perform better. There were a number of challenges in 2012, including continued macro-economic uncertainty, a decline in the total addressable market for routing and tightening customer demand in major geographies and sectors including Europe and the US Federal Government. While navigating these challenges, we took decisive actions to address performance factors in our control, including restructuring the organization and driving initiatives that have raised our level of execution. These initiatives have contributed to three key areas that together put us in a stronger position for renewed growth and market share gains. Juniper strengthened our product portfolio in 2012. We sharpened our focus as a pure play in high performance networking in three product families: Routing, Switching and Security. We added new product offerings in each of these families in 2012 and we enhanced many of the core products in those families with new capabilities. Early this year we articulated a clear strategy for Juniper in the area of Software Defined Networks. Due to this hard work, we now have the broadest, deepest and highest-performance product lineup in our history, with an ambitious innovation roadmap that is addressing the transformative roles that mobility and cloud computing are playing in the new network. In routing, we remain a strong leader in the edge with our MX line which enables Service Providers to deliver and expand services and maximize revenues faster than other market solutions. -
PCI DSS Virtualization Guidelines
Standard: PCI Data Security Standard (PCI DSS) Version: 2.0 Date: June 2011 Author: Virtualization Special Interest Group PCI Security Standards Council Information Supplement: PCI DSS Virtualization Guidelines Information Supplement • PCI DSS Virtualization Guidelines • June 2011 Table of Contents 1 Introduction ....................................................................................................................... 3 1.1 Audience ................................................................................................................ 3 1.2 Intended Use .......................................................................................................... 4 2 Virtualization Overview .................................................................................................... 5 2.1 Virtualization Concepts and Classes ..................................................................... 5 2.2 Virtual System Components and Scoping Guidance ............................................. 7 3 Risks for Virtualized Environments .............................................................................. 10 3.1 Vulnerabilities in the Physical Environment Apply in a Virtual Environment ....... 10 3.2 Hypervisor Creates New Attack Surface ............................................................. 10 3.3 Increased Complexity of Virtualized Systems and Networks .............................. 11 3.4 More Than One Function per Physical System ................................................... 11 3.5 Mixing VMs of -
Vgw Virtual Gateway Virtual Gateway Virtual
vGW Virtual Gateway Administration Guide Release 4.5 Service Pack 1 Copyright © 2011, Juniper Networks, Inc Juniper Networks, Inc. 1194 North Mathilda Avenue Sunnyvale, California 94089 USA 408-745-2000 www.juniper.net Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered trademarks of Juniper Networks, Inc. in the United States and other countries. The Juniper Networks Logo, the Junos logo, and JunosE are trademarks of Juniper Networks, Inc. All other trademarks, service marks, registered trademarks, or registered service marks are the property of their respective owners. Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify, transfer, or otherwise revise this publication without notice. Products made or sold by Juniper Networks or components thereof might be covered by one or more of the following patents that are owned by or licensed to Juniper Networks: U.S. Patent Nos. 5,473,599, 5,905,725, 5,909,440, 6,192,051, 6,333,650, 6,359,479, 6,406,312, 6,429,706, 6,459,579, 6,493,347, 6,538,518, 6,538,899, 6,552,918, 6,567,902, 6,578,186, and 6,590,785. SOFTWARE LICENSE The terms and conditions for using this software are described in the software license contained in the acknowledgment to your purchase order or, to the extent applicable, to any reseller agreement or end-user purchase agreement executed between you and Juniper Networks. By using this software, you indicate that you understand and agree to be bound by those terms and conditions. -

Secure Data Center Networking with Open Vswitch
Secure Data Center Networking with Open vSwitch Pa Pa Hlaing University of Computer Studies, Yangon [email protected] Abstract agility and isolation of VMs. Most physical switches deployed in conventional DCNs are not designed for either supporting such unique VM Data centers have become the next- requirements or flexible enough to augment new generation computing platforms for enterprises functionalities [7]. At the same time, VM and Internet users. This is primarily due to the networking has inherently unique characteristics, economic and technical advantages of resource such as the awareness of the migration of VMs sharing in data centers. By sharing computing and their multicast membership. Therefore, much and storage resources through services such as research has begun exploring the opportunity to cloud computing or software-as-a-service (SaaS), introduce a new, flexible and programmable users can amortize the cost of hardware and networking layer based on the knowledge of software. Because of the virtualization of VMs. resources, a new virtualized network access layer Modern data center networks consist of both has been introduced to interconnect VMs within physical networks connected by switches and the data centers. In data center, hosts have been virtual networks formed by VMs running inside recently employed virtual switch to interconnect physical hosts. Inside one computer, many VMs virtual machines (VMs) within data center can exist (as many as 120 VMs per host), each of networks. Virtual Switch is essential to control which has at least one virtual network interface and manage VM within the hosts. Open vSwitch, card (VNIC). The VNICs communicate with a network switch specifically built for Xen external networks through the host’s physical virtualization environment is presented. -

S32 - a Primer on Virtualization Tom Ray
S32 - A Primer on Virtualization Tom Ray A Primer on Virtualization Ignoring the man behind the curtain? Agenda • Top 3 things you need to know about Virtualization when you Audit it, & your IT & IT security groups. – What IS virtualization? – What are the issues? – What is a reasonable, “AUDIT-READY” secure Reference Architecture? • Discuss how to Audit a virtualized IT 2 1 What is Virtualization? 3 Some Observations • It is NOT new (but some developments are) • It is an “already expected ” cost containment technology in many IT departments • Before you can answer “what is” you need to identify which kind you are interested in • It is jargon and acronym-rich, & it’s vendor balkanized • It is (still) immature and so nothing does it full justice – no one approach, no set of standards, or vendor, or architecture, or set of components, or framework, or technology, or technique, or regulations, etc. • It will radically impact how you “do” IT & environments 4 2 What are the Issues? 5 In Summary 1. Disconnect between Logical and Physical is exploited for the technology’s benefit; not the humans’ 2. Dynamism 3. Blur & Ease of Sprawl – Increased Complexity & Interdependencies – Overlap of various roles’ capabilities 4. Resource equation is still a zero-sum game (at best) – Same staff (IT & Business) – Same Procedures? , … same Tools? 5. The technology’s Immaturity 6. Our IT Operations Immaturity 7. The CIO’s Drivers (expectations, motivations & intentions) 6 3 What is a reasonable, “AUDIT‐READY” secure Reference Architecture? 7 2 Security Reference Architectures Durable Non Compliance People / Organizations X Processes / Tasks / RnR Metrics? Threat Technologies / Constructs X Mitigation Build Specs / Contracts / Metrics? Documentation Technical-Trust Enablement 1. -
Juniper Networks Inc
JUNIPER NETWORKS INC FORM 10-K (Annual Report) Filed 02/26/13 for the Period Ending 12/31/12 Address 1194 NORTH MATHILDA AVE SUNNYVALE, CA 94089 Telephone 4087452000 CIK 0001043604 Symbol JNPR SIC Code 3576 - Computer Communications Equipment Industry Communications Equipment Sector Technology Fiscal Year 12/31 http://www.edgar-online.com © Copyright 2013, EDGAR Online, Inc. All Rights Reserved. Distribution and use of this document restricted under EDGAR Online, Inc. Terms of Use. Table of Contents UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 Form 10-K (Mark One) ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the fiscal year ended December 31, 2012 OR TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the transition period from__________ to____________ Commission file number 001-34501 JUNIPER NETWORKS, INC. (Exact name of registrant as specified in its charter) Delaware 77-0422528 (State or other jurisdiction of incorporation or organization) (IRS Employer Identification No.) 1194 North Mathilda Avenue Sunnyvale, California 94089 (408) 745-2000 (Address of principal executive offices)(Zip Code) ( Registrant's telephone number, including area code) Securities registered pursuant to Section 12(b) of the Act: Title of Each Class Name of Each Exchange on Which Registered Common Stock, par value $0.00001 per share New York Stock Exchange Securities registered pursuant to Section 12(g) of the Act: None Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. -
Juniper Networks Inc
JUNIPER NETWORKS INC FORM 10-K (Annual Report) Filed 02/26/14 for the Period Ending 12/31/13 Address 1194 NORTH MATHILDA AVE SUNNYVALE, CA 94089 Telephone 4087452000 CIK 0001043604 Symbol JNPR SIC Code 3576 - Computer Communications Equipment Industry Communications Equipment Sector Technology Fiscal Year 12/31 http://www.edgar-online.com © Copyright 2014, EDGAR Online, Inc. All Rights Reserved. Distribution and use of this document restricted under EDGAR Online, Inc. Terms of Use. UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 FORM 10-K (Mark One) ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the fiscal year ended December 31, 2013 or TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the transition period from__________ to____________ Commission file number 001-34501 JUNIPER NETWORKS, INC. (Exact name of registrant as specified in its charter) Delaware 77-0422528 (State or other jurisdiction of incorporation or organization) (I.R.S. Employer Identification No.) 1194 North Mathilda Avenue Sunnyvale, California 94089 (Address of principal executive offices) (Zip code) (408) 745-2000 (Registrant's telephone number, including area code) Securities registered pursuant to Section 12(b) of the Act: Title of Each Class Name of Each Exchange on Which Registered Common Stock, par value $0.00001 per share New York Stock Exchange Securities registered pursuant to Section 12(g) of the Act: None Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. -
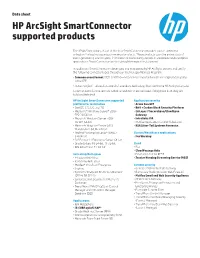
HP Arcsight Smartconnector Supported Products Data Sheet
Data sheet HP ArcSight SmartConnector supported products The HP ArcSight library of out-of-the-box SmartConnectors provides source-optimized collection for leading security commercial products. These products span the entire stack of event-generating source types, from network and security devices to databases and enterprise applications. SmartConnectors are the default listing in this document. In addition to SmartConnectors developed and maintained by HP ArcSight, we test and certify the following connector types through our Technology Alliances Program: • Common event format (CEF) Certified—helps ensure event information is captured properly in the CEF • Action Certified—allows for control of a vendor’s technology from within the HP ArcSight Console Common event format are in bold below and Action are Italicized. If they have both they are bold and Italicized. HP ArcSight SmartConnector supported Application security platform for installation • Arxan GuardIT • CentOS-6.5, 6.6, and 7.0 • Bit9 + Carbon Black Security Platform • Microsoft® Windows Server® 2008 • CA Layer 7 SecureSpan/CloudSpan SP2 32/64-bit Gateway • Microsoft Windows Server 2008 • Intralinks VIA R2 SP1 64-bit • McAfee Application Control (Solidcore) • Microsoft Windows Server 2012 • RSA Silver Tail Systems Forensics Standard 64-bit, R2 64-bit • Red Hat® Enterprise Linux® (RHEL) Clinical/Healthcare applications 6.4 64-bit • FairWarning • SUSE Linux 11 Enterprise Server 64-bit • Oracle Solaris 10 64-bit, 11 32-bit Cloud • IBM AIX version 7.1 64-bit • Box • CloudPassage -
In Re: Juniper Networks, Inc. Securities Litigation 06-CV-04327
Case 5:06-cv-04327-JW Document 83 Filed 06/07/2007 Page 1 of 3 1 NINA F. LOCKER, State Bar No. 123838 Email: [email protected] 2 STEVEN GUGGENHEIM, State Bar No. 201386 Email: [email protected] 3 JONI OSTLER, State Bar No. 230009 Email: [email protected] 4 WILSON SONSINI GOODRICH & ROSATI Professional Corporation 5 650 Page Mill Road Palo Alto, CA 94304-1050 6 Telephone: (650) 493-9300 Facsimile: (650) 565-5100 7 8 Attorneys for Defendants Juniper Networks, Inc., Scott Kriens, Pradeep Sindhu, Marcel Gani, Robert 9 M. Calderoni, Kenneth Goldman, William R. Hearst III, Stratton Sclavos, Vinod Khosla, 10 Kenneth Levy and William R. Stensrud 11 UNITED STATES DISTRICT COURT 12 NORTHERN DISTRICT OF CALIFORNIA 13 SAN JOSE DIVISION 14 In re JUNIPER NETWORKS, INC. ) No. C06-04327-JW SECURITIES LITIGATION ) 15 DECLARATION OF JONI OSTLER IN SUPPORT OF DEFENDANTS' MOTION 16 This Document Relates To: ) TO DISMISS AMENDED CONSOLIDATED CLASS ACTION 17 ALL ACTIONS. ) COMPLAINT 18 Date: September 10, 2007 Time: 9 :00 a.m. 19 Courtroom: 8 1 Before: Hon. James Ware 20 21 22 23 24 25 26 27 28 OSTLER DECL. ISO DEFENDANTS' MOTION TO Dismiss Case 5:06-cv-04327-JW Document 83 Filed 06/07/2007 Page 2 of 3 1 I, Joni Ostler, declare as follows: 2 1. I am an attorney associated with the law firm of Wilson Sonsini Goodrich & 3 Rosati, a Professional Corporation, counsel of record for Defendants Juniper Networks, Inc. 4 ("Juniper ), Scott G. Kriens, Pradeep Sindhu, Marcel Gani, Robert M. Calderoni, Kenneth 5 Goldman, William R. -
NSA-GCHQ Juniper
TOP SECRET STRAP1 ASSESSMENT OF INTELLIGENCE OPPORTUNITY - JUNIPER 03 February 2011 Executive Summary Background • Juniper Networks, Inc. headquartered in Sunnyvale, California, USA is a high-performance Internet Protocol network products company. Juniper's main products include T-series, M- series, E-series, MX-series, and J-series families of routers, EX-series Ethernet switches, and NetScreen and SRX-series security products. • While Juniper is not necessarily the market share leader in any one space, they are a strong competitor and technology leader across several important markets from a SIGINT perspective. Juniper is at the core of the Internet in many countries by virtue of providing the highest density routers for many years. • Juniper’s leadership in core IP routing and the Enterprise Network Firewall and SSL VPN markets means that the SIGINT community should keep up with Juniper technology to be positioned to maintain CNE access over time. Currently exploit capability • Juniper NetScreen Firewalls models NS5gt, N25, NS50, NS500, NS204, NS208, NS5200, NS5000, SSG5, SSG20, SSG140, ISG 1000, ISG 2000. Some reverse engineering may be required depending on firmware revisions. • Juniper Routers: M320 is currently being worked on and we would expect to have full support by the end of the 2010. Recommendations and Expected Outcomes • Discover Juniper equipment on networks in hard target countries to assess potential Juniper exploitation opportunities with existing capabilities. • Assess potential additional targetable networks if additional equipment models could be exploited (e.g. if we could exploit MX-series routers, then networks X, Y, & Z could be exploited). • Assess an effort to exploit the JUNOS operating system. -

Executive Biographies
Executive Biographies Kevin Johnson, Chief Executive Officer Kevin Johnson joined Juniper Networks in September of 2008 as Chief Executive Officer and a member of the board. Mr. Johnson has been appointed by the President of the United States of America to serve on the National Security Telecommunications Advisory Committee (NSTAC). Prior to joining Juniper, Mr. Johnson spent 16 years at Microsoft, most recently as President of the Platforms and Services Division, an organization of more than 14,000 employees with responsibility for product development, marketing and strategy for the Windows and Online Services businesses. Under his leadership, the division achieved record-breaking results with more than $20 billion in revenue in fiscal year 2008. In addition, Mr. Johnson focused on building Microsoft's position as an industry leader in online advertising and evolving its "software + services" strategy. He worked globally with small- to medium-sized businesses as well as large consumer, service provider and enterprise customers. Prior to that role, Mr. Johnson served as Group Vice President of Microsoft's worldwide sales, marketing and services organizations and also oversaw corporate operations and IT functions that supported the work of Microsoft employees around the world. He started his career as a software developer and worked in IBM's systems integration and consulting business. He earned a bachelor's degree in business administration from New Mexico State University. He served as a founding member of the board of directors of NPower, a nonprofit organization that helps other nonprofits use technology to expand the reach and impact of their work, and as a member of the Western Region Board of Advisors of Catalyst, a nonprofit organization dedicated to women's career advancement. -

View Annual Report
UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 Form 10-K (Mark One) ¥ ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the fiscal year ended December 31, 2008 OR n TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the transition period from to Commission file number 0-26339 JUNIPER NETWORKS, INC. (Exact name of registrant as specified in its charter) Delaware 77-0422528 (State or other jurisdiction of (IRS Employer incorporation or organization) Identification No.) 1194 North Mathilda Avenue (408) 745-2000 Sunnyvale, California 94089 (Registrant’s telephone (Address of principal executive number, including area code) offices, including zip code) Securities registered pursuant to Section 12(b) of the Act: Title of Each Class Name of Each Exchange on Which Registered Common Stock, par value $0.00001 per share The NASDAQ Global Select Market Securities registered pursuant to Section 12(g) of the Act: None Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. Yes n No ¥ Indicate by check mark if the registrant is not required to file reports pursuant to Section 13 or Section 15(d) of the Act. Yes n No ¥ Indicate by check mark whether the Registrant (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities Exchange Act of 1934 during the preceding 12 months (or for such shorter period that the registrant was required to file such reports), and (2) has been subject to such filings requirements for the past 90 days.