Release V0.4 Jan Luebbe, Enrico Joerns, Juergen Borleis
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Greetings from Slackbuilds.Org
Greetings from SlackBuilds.org David Spencer pkgsrcCon 2017 About SBo 11 years old conventional ports-inspired setup ● from source ftw ● shell script + metadata ~6500 packages disjoint from core Slackware (~1400 packages) lightweight project one new server, one old server About SBo ~250 maintainers active in last year ~12500 commits in last year no bugtracker no CI ● Infrastructure is a productivity killer ● Aggressively reductionist on dep management ● Vanilla from upstream, patch only when needed ● Don’t split packages ● git git baby About SBo submissions are open ambition to submit ‘something’ is a thing maintainers drop in and drop out review must be sympathetic volunteers are a pipeline not a funnel don’t crush people’s dreams maintainer is expert on the software reviewer (admin) is expert on good packaging no room for style variations About SBo Education needs to be a thing No time in review feedback hurts, doesn’t scale Currently done on mailing list & forum ● CI as education Listening systemd refugees rolling release ● stable versus current out of date / security / unmaintained upstream disappearing SBo maintainers disappearing sources and projects ● repology ● keeps mailing list active Happy community Users helping each other Tools Satellite projects Package all the obscure things ● if it exists it will attract users Unopened letter to the world Need to educate upstreams proper releases with proper tarballs don’t move or delete old tarballs learn to write a decent Makefile no, I don’t want your stinking CFLAGS don’t use -Werror -
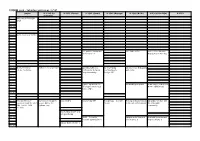
FOSDEM 2018 Schedule
FOSDEM 2018 - Saturday 2018-02-03 (1/15) Janson K.1.105 (La H.2215 (Ferrer) H.1301 (Cornil) H.1302 (Depage) H.1308 (Rolin) H.1309 (Van Rijn) H.2111 Fontaine)… 09:30 Welcome to FOSDEM 2018 09:45 10:00 Consensus as a Service 10:15 10:30 The path to Data-plane The State of Go video - It's a lot more micro-services than just a HTML5 tag 10:45 11:00 Next Generation Python 3: 10 years later OpenDaylight as a De-mystifying Advanced Go debugging Internet Initiative Platform for Network contributing to with Delve Programmability PostgreSQL 11:15 11:30 Ligato: a platform for Networking deepdive Rendering of subtitles in development of cloud- HTML5 with imscJS native VNFs 11:45 12:00 Unix Architecture Surviving in an Open Easy GnuPG Networking-VPP PostgreSQL -- A Crash Testing and Automation An update on VLC and Evolution from the 1970 Source Niche: the Course in the Era of Containers the VideoLAN PDP-7 to the 2018 Pythran case community FreeBSD 12:15 BulletinBoard DHT and wireguard-p2p 12:30 ONAP – A road to Upspin and a future of Kodi v18 features and network automation ↴ the Internet ↴ improvements ↴ Nakadi Event Broker ↴ 12:45 FOSDEM 2018 - Saturday 2018-02-03 (2/15) H.2213 H.2214 H.3227 H.3228 AW1.120 AW1.121 AW1.125 AW1.126 09:30 09:45 10:00 10:15 10:30 A real life story about Cypher: An evolving Status of the Apache CANCELLED Simulating Arrival & Informal Everything is a device! product testing with query language for ODF Toolkit (incubating) Multilevel Caches in Discussions robotframework property graphs Cachegrind 10:45 Working in the ODF -

Beta Release
CLIP OS 5: Beta release Timothée Ravier, Thibaut Sautereau Agence nationale de la sécurité des systèmes d’information (ANSSI) 10 & 11 December 2019, Paris Open Source Summit About the ANSSI ◮ Agence nationale de la sécurité des systèmes d’information ◮ French authority in the area of cyberdefence, network and information security ◮ Provides its expertise and technical assistance to government departments and businesses and plays an enhanced role in supporting operators of vital importance. ANSSI CLIP OS 5: Beta release 2/37 CLIP OS? ◮ Linux distribution developed by the ANSSI ◮ Initially only available internally ◮ Now open source, mostly under the LGPL v2.1+ ◮ Code and issue tracker hosted on GitHub12: ◮ Version 4: available as reference and for upstream patch contribution ◮ Version 5: currently developed version, beta released in December 2019 1https://github.com/CLIPOS 2https://github.com/CLIPOS-Archive ANSSI CLIP OS 5: Beta release 3/37 CLIP OS? Not yet another Linux distribution ◮ Not a generic/multi-purpose distribution Targets three main use cases ◮ Mobile office workstation ◮ Remote administration workstation ◮ IPsec gateway ANSSI CLIP OS 5: Beta release 4/37 Hardened OS ◮ Based on Gentoo Hardened ◮ Hardened Linux kernel and confined services ◮ No interactive root account available: ⇒ "Unprivileged" admin, audit and update roles ◮ Automatic updates using A/B partition model (similar to Android 7+) ◮ Multilevel security: ◮ Provide two isolated user environments ◮ Controlled interactions between isolated environments ANSSI CLIP OS -
Scientific Linux Status Update
Scientific Linux Status Update Speaker: Pat Riehecky Authors: Glenn Cooper, Rennie Scott, Bonnie King, Pat Riehecky HEPiX May 2018 14 May 2018 Major Updates • Connie Sieh has retired We wish her well! • Red Hat bought CoreOS • Scientific Linux Official Docker containers 7.5 released 6.9 released • CVE-2018-1000156 patch: Malicious patch files cause ed to execute arbitrary commands 05/14/2018 HEPiX 2018 Official Docker Containers Scientific Linux now has official Docker containers. docker run -it sl:6 /bin/bash docker run -it sl:7 /bin/bash docker run -it sl:latest /bin/bash They are updated monthly with latest security errata. See the official readme for more information. As a reminder, containers will let you run things long past their end of life date. 05/14/2018 HEPiX 2018 SL5 – It is removed from your site right? SL5 went end of life March 31 2017 The SL distribution servers show over 2700 individual IP addresses still requesting nightly updates in April 2018. 05/14/2018 HEPiX 2018 SL6 – Production Phase 3 SL6 end of life November 30 2020 RHEL 6.10 BETA – April 27 2018 Current status is Production Phase 3 During the Production 3 Phase, Critical Impact Security Advisories and selected Urgent Priority Bug Fix Advisories may be released as they become available. Other errata advisories may be delivered as appropriate. 05/14/2018 HEPiX 2018 SL7 – Production Phase 2 SL7 end of life June 30 2024 SL 7.5 – May 10 2018 Current status is Production Phase 2 During the Production 2 Phase, Critical impact Security Advisories and selected Urgent Priority Bug Fix Advisories may be released as they become available. -

26. Februar 2018 Sponsoren
26. Februar 2018 Sponsoren Premiumsponsoren Weitere Sponsoren Was bieten die Chemnitzer Linux-Tage? Die Chemnitzer Linux-Tage sind die größte Veranstaltung zum Thema Linux und Open Source in Deutschland. Mit unserem Engagement stehen wir für Open Source, freie Information und sichere Kommunikation für jedermann. Sie finden: • ein reichhaltiges Vortragsprogramm (S. 4) und Lightning Talks (S. 26) für Projektvorstellungen, • Workshops (S. 26) und Praxis Dr. Tux (S. 44), • Linux-Live: vielfältige Demonstrationen und Firmenpräsentationen (S. 31), • Zertifizierungsprüfungen (S. 45), • CLT-Junior – Technik, die Spaß macht (S. 29), • Service (S. 46): Information, Kinderparadies, Fanartikel- und Buchverkauf, Imbiss, • flächendeckend WLAN (S. 47), PGP-Keysigning-Party und vieles mehr. Ablauf: Sonnabend 8:30 Einlassbeginn 9:00-18:00 Vorträge (S. 4) und Workshops (S. 26) 10:00-17:00 CLT-Junior (S. 26) und Elektronikbasteln für Kinder (S. 23) 12:30 Grußwort des Prorektors (V7) 15:00 Business-Forum (S. 25) 16:00 PGP-Party (S. 45) 18:00 Linux-Nacht (S. 46) Sonntag 9:00 Einlassbeginn 10:00-18:00 Vorträge (S. 4) und Workshops (S. 26) 10:00-17:00 CLT-Junior (S. 26) und Elektronikbasteln für Kinder (S. 23) 10:30 / 12:30 LPI-Prüfungen (S. 45) 15:30 Thomas-Krenn-Award (S. 46) und Lightning Talks (S. 26) 18:00 Ende der Chemnitzer Linux-Tage 2018 Inhaltsverzeichnis Programmierung . 21 Datenbanken . 22 Sponsoren . .2 Kernel . 23 Was bieten die Chemnitzer Linux-Tage?3 Management . 24 Vorträge . .4 Specials . 25 Einsteigerforum . .4 Workshops . 26 Jeder fängt mal an . .5 CLT-Junior . 29 Crypto und Sicherheit . .7 Linux-Live . 31 Virtualisierung . 10 Projekte . -

Omzetten Van Een Windows C++ MFC Telefonie Servertoepassing Naar Linux
Academiejaar 2013–2014 Faculteit Ingenieurswetenschappen en Architectuur Valentin Vaerwyckweg 1 – 9000 Gent Omzetten van een Windows C++ MFC telefonie servertoepassing naar Linux Masterproef voorgedragen tot het behalen van het diploma van Master in de industriële wetenschappen: informatica Tibault DAMMAN Promotoren: Ann VAN OVERBERGE Ing. Filip HOSTE (MyForce) Powered by TCPDF (www.tcpdf.org) Voorwoord Vooreerst mijn dank aan iedereen bij MyForce voor een bijzonder aangename stage, ik weet niet wat ik zonder de voortdurende aanmoediging (\en, compileert het al?") gedaan zou hebben. In het bijzonder wil ik Filip Hoste en Bert Reyntjes bedanken voor hun hulp en uitleg bij de code. Daarnaast wil ik ook mijn promotor Ann Van Overberge bedanken voor het nalezen van deze scriptie en geven van bruikbare feedback. Ook aan Rudy Stoop, tweede lezer en docent C++, een woord van dank. Ten slotte dank ik ook Hannes, Arne en Bas voor hun tips en het verdragen van mijn onge- twijfeld eindeloos geklaag. Tibault Damman De Pinte, 28 augustus 2014 Omzetten van een Windows C++ MFC telefonie servertoepassing naar Linux door Tibault DAMMAN Masterproef voorgedragen tot het behalen van het diploma van Master in de industri¨ele wetenschappen: informatica Academiejaar 2013{2014 Interne promotor: Ann VAN OVERBERGE Externe promotor: Ing. Filip HOSTE (MyForce) Faculteit Ingenieurswetenschappen en Architectuur Universiteit Gent Abstract MyForce is een bedrijf dat zich specialiseert in het ontwikkelen van oplossingen voor bedrijven waar automatisatie van telefonie centraal staat, zoals bij callcenters en bureaus voor markt- onderzoek. HardwareClient is het component dat instaat voor de communicatie tussen het publieke telefonienetwerk (via ISDN en VoIP) en het interne bedrijfsnetwerk. -

Release 1.5.1 Jan Luebbe, Enrico Joerns, Juergen Borleis
RAUC Documentation Release 1.5.1 Jan Luebbe, Enrico Joerns, Juergen Borleis Jan 22, 2021 Contents 1 Updating your Embedded Device3 2 RAUC Basics 5 3 Using RAUC 9 4 Examples 19 5 Scenarios 25 6 Integration 29 7 Advanced Topics 51 8 Design Checklist 67 9 Frequently Asked Questions 71 10 Reference 73 11 Terminology 89 12 Contributing 91 13 Changes in RAUC 93 14 The Need for Updating 109 15 What is RAUC? 111 16 And What Not? 113 17 Key Features of RAUC 115 Index 117 i ii RAUC Documentation, Release 1.5.1 Contents: Contents 1 RAUC Documentation, Release 1.5.1 2 Contents CHAPTER 1 Updating your Embedded Device This chapter does not explicitly tell you anything about RAUC itself, but it provides an initial overview of basic requirements and design consideration that have to be taken into account when designing an update architecture for your embedded device. Thus, if you know about updating and are interested in RAUC itself, only, simply skip this chapter. Nevertheless, this chapter could also provide some useful hints that can already be useful when designing the device you intend to update later on. In this you initial phase you can prevent yourself from making wrong decisions. 1.1 Redundancy and Atomicity There are two key requirements for allowing you to robustly update your system. The first one is redundancy: You must not update the system you are currently running on. Otherwise a failure during updating will brick the only system you can run your update from. The second one is atomicity: Writing your update to the currently inactive device is a critical operation. -

RAUC Documentation Release 1.5.1.131-1564
RAUC Documentation Release 1.5.1.131-1564 Jan Luebbe, Enrico Joerns, Juergen Borleis Sep 30, 2021 Contents 1 Updating your Embedded Device3 2 RAUC Basics 5 3 Using RAUC 9 4 Examples 21 5 Scenarios 27 6 Integration 31 7 Advanced Topics 53 8 Design Checklist 69 9 Frequently Asked Questions 73 10 Reference 75 11 Terminology 91 12 Contributing 93 13 Changes in RAUC 97 14 The Need for Updating 113 15 What is RAUC? 115 16 And What Not? 117 17 Key Features of RAUC 119 Index 121 i ii RAUC Documentation, Release 1.5.1.131-1564 Contents: Contents 1 RAUC Documentation, Release 1.5.1.131-1564 2 Contents CHAPTER 1 Updating your Embedded Device This chapter does not explicitly tell you anything about RAUC itself, but it provides an initial overview of basic requirements and design consideration that have to be taken into account when designing an update architecture for your embedded device. Thus, if you know about updating and are interested in RAUC itself, only, simply skip this chapter. Nevertheless, this chapter could also provide some useful hints that can already be useful when designing the device you intend to update later on. In this you initial phase you can prevent yourself from making wrong decisions. 1.1 Redundancy and Atomicity There are two key requirements for allowing you to robustly update your system. The first one is redundancy: You must not update the system you are currently running on. Otherwise a failure during updating will brick the only system you can run your update from. -
Graph-Radial.Pdf
beep yap yade xorp xen wpa wlcs wcc vzctl vg vast v86d ust udt ucx tup ttyd tpb tgt tboot tang t50 sxiv sptag spice shim sbd rr rio rear rauc rarpd qsstv qrq qps qperf atop acpi 0ad apr zyn zpaq yash xqf wrk wit pcb pam p4est oscar orpie ondir ola oflib o2 ntp nsd ns3 ns2 npd6 nnn nng nield kitty kcov kbtin k3b jove ircii ipip ipe iotjs ion iitii iftop anet alevt agda afuse afnix adcli acct gpart matplotlib numexpr zhcon vrrpd fxload dov4l yavta yacpi wvdial wsjtx wmifs weston vtgrab vmpk vmem vkeybd urfkill ulogd2 uftrace udevil tvtime tucnak topline tiptop tcplay tayga sysstat sysprof svxlink libgisi libemf libdfp libcxl libbpf libacpi latrace kpatch khmer elastix dvblast crystal cpustat chrony casync boxfort bowtie bilibop axmail awesfx armnn aqemu acpitail webdis vnstat vnlog vlock vibe.d vbrfix vblade validns urweb unscd ncrack mystiq mtools mruby mpqc3 mothur mm3d mkcue miredo midish meliae mclibs maude lwipv6 ltunify lsyncd libvhdi libsfml libscca librepo librelp libregf libfwnt libfvde libevtx libcreg libbfio libalog kwave knockd kismet jmtpfs jattach ivtools isc-kea anfo baresip badger pigpio babeld asylum 3depict parole-dev esekeyd twclock thermald thc-ipv6 tftp-hpa te923con tarantool systemc syslinux sysconfig suricata supermin subread spacefm quotatool qjoypad qcontrol qastools pystemd pps-tools powertop pommed ifhp ffmpegfs faultstat f2fs-tools eventstat ethstatus espeakup embree elogind ebtables earlyoom digitools dbus-cpp darktable cubemap crystalhd criterion cputool circlator cen64-qt can-utils bolt-lmm bluedevil blktrace -
Using Open Source Software to Build an Industrial Grade Embedded
Open Source Summit Japan 2019 Using Open Source Software to Build an Industrial-grade Embedded Linux Platform from Scratch SZ Lin (林上智) Embedded Linux Development Center, Software R&D Engineer 07/19, 2019 About Me SZ LIN (林上智) Software Engineer at Moxa Cybersecurity Fundamentals Specialist ISA/ IEC 62443 Debian Developer Blog - https://szlin.me 2 Industrial Embedded Linux Platforms Application Smart Smart Smart Smart Smart Smart Rail Grid Oil Field Transportation Factory Marine Edge Connectivity Industrial Computing Network Infrastructure Industrial Serial I/O Video Embedded Computers Industrial Wireless Industrial Connectivity Connectivity Connectivity Ethernet LAN Routers Device 3 Before Using Open Source Software Something You Should Know 4 Copyright Patent Copyright is a legal right, that grants A patent gives its owner the right to the creator of an original work exclude others from making, using, exclusive rights to determine whether, selling, and importing an invention and under what conditions, this for a limited period of time, usually original work may be used by others twenty years. src: https://en.wikipedia.org/wiki/Copyright src: https://en.wikipedia.org/wiki/Patent 5 Copyright Patent Identify key recommended processes It is a shared defensive patent pool for effective open source management with the mission to protect Linux [2]. [1]. 6 Processes, Tooling and Support OpenChain SPDX [3] FOSSology [4] Trust between entities in the supply chain Trust for software packages Free scanning technology The OpenChain Project builds Software Package Data Exchange FOSSology is a open source trust in open source by making (SPDX) is a file format used to license compliance software open source license document information on the system and toolkit compliance simpler and more software licenses under which a consistent given piece of computer software is distributed.