Some Results on Derandomization
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Complexity Zoo
The Complexity Zoo Scott Aaronson www.ScottAaronson.com LATEX Translation by Chris Bourke [email protected] 417 classes and counting 1 Contents 1 About This Document 3 2 Introductory Essay 4 2.1 Recommended Further Reading ......................... 4 2.2 Other Theory Compendia ............................ 5 2.3 Errors? ....................................... 5 3 Pronunciation Guide 6 4 Complexity Classes 10 5 Special Zoo Exhibit: Classes of Quantum States and Probability Distribu- tions 110 6 Acknowledgements 116 7 Bibliography 117 2 1 About This Document What is this? Well its a PDF version of the website www.ComplexityZoo.com typeset in LATEX using the complexity package. Well, what’s that? The original Complexity Zoo is a website created by Scott Aaronson which contains a (more or less) comprehensive list of Complexity Classes studied in the area of theoretical computer science known as Computa- tional Complexity. I took on the (mostly painless, thank god for regular expressions) task of translating the Zoo’s HTML code to LATEX for two reasons. First, as a regular Zoo patron, I thought, “what better way to honor such an endeavor than to spruce up the cages a bit and typeset them all in beautiful LATEX.” Second, I thought it would be a perfect project to develop complexity, a LATEX pack- age I’ve created that defines commands to typeset (almost) all of the complexity classes you’ll find here (along with some handy options that allow you to conveniently change the fonts with a single option parameters). To get the package, visit my own home page at http://www.cse.unl.edu/~cbourke/. -

The Polynomial Hierarchy
ij 'I '""T', :J[_ ';(" THE POLYNOMIAL HIERARCHY Although the complexity classes we shall study now are in one sense byproducts of our definition of NP, they have a remarkable life of their own. 17.1 OPTIMIZATION PROBLEMS Optimization problems have not been classified in a satisfactory way within the theory of P and NP; it is these problems that motivate the immediate extensions of this theory beyond NP. Let us take the traveling salesman problem as our working example. In the problem TSP we are given the distance matrix of a set of cities; we want to find the shortest tour of the cities. We have studied the complexity of the TSP within the framework of P and NP only indirectly: We defined the decision version TSP (D), and proved it NP-complete (corollary to Theorem 9.7). For the purpose of understanding better the complexity of the traveling salesman problem, we now introduce two more variants. EXACT TSP: Given a distance matrix and an integer B, is the length of the shortest tour equal to B? Also, TSP COST: Given a distance matrix, compute the length of the shortest tour. The four variants can be ordered in "increasing complexity" as follows: TSP (D); EXACTTSP; TSP COST; TSP. Each problem in this progression can be reduced to the next. For the last three problems this is trivial; for the first two one has to notice that the reduction in 411 j ;1 17.1 Optimization Problems 413 I 412 Chapter 17: THE POLYNOMIALHIERARCHY the corollary to Theorem 9.7 proving that TSP (D) is NP-complete can be used with DP. -

Collapsing Exact Arithmetic Hierarchies
Electronic Colloquium on Computational Complexity, Report No. 131 (2013) Collapsing Exact Arithmetic Hierarchies Nikhil Balaji and Samir Datta Chennai Mathematical Institute fnikhil,[email protected] Abstract. We provide a uniform framework for proving the collapse of the hierarchy, NC1(C) for an exact arith- metic class C of polynomial degree. These hierarchies collapses all the way down to the third level of the AC0- 0 hierarchy, AC3(C). Our main collapsing exhibits are the classes 1 1 C 2 fC=NC ; C=L; C=SAC ; C=Pg: 1 1 NC (C=L) and NC (C=P) are already known to collapse [1,18,19]. We reiterate that our contribution is a framework that works for all these hierarchies. Our proof generalizes a proof 0 1 from [8] where it is used to prove the collapse of the AC (C=NC ) hierarchy. It is essentially based on a polynomial degree characterization of each of the base classes. 1 Introduction Collapsing hierarchies has been an important activity for structural complexity theorists through the years [12,21,14,23,18,17,4,11]. We provide a uniform framework for proving the collapse of the NC1 hierarchy over an exact arithmetic class. Using 0 our method, such a hierarchy collapses all the way down to the AC3 closure of the class. 1 1 1 Our main collapsing exhibits are the NC hierarchies over the classes C=NC , C=L, C=SAC , C=P. Two of these 1 1 hierarchies, viz. NC (C=L); NC (C=P), are already known to collapse ([1,19,18]) while a weaker collapse is known 0 1 for a third one viz. -

On the Power of Parity Polynomial Time Jin-Yi Cai1 Lane A
On the Power of Parity Polynomial Time Jin-yi Cai1 Lane A. Hemachandra2 December. 1987 CUCS-274-87 I Department of Computer Science. Yale University, New Haven. CT 06520 1Department of Computer Science. Columbia University. New York. NY 10027 On the Power of Parity Polynomial Time Jin-yi Gaia Lane A. Hemachandrat Department of Computer Science Department of Computer Science Yale University Columbia University New Haven, CT 06520 New York, NY 10027 December, 1987 Abstract This paper proves that the complexity class Ef)P, parity polynomial time [PZ83], contains the class of languages accepted by NP machines with few ac cepting paths. Indeed, Ef)P contains a. broad class of languages accepted by path-restricted nondeterministic machines. In particular, Ef)P contains the polynomial accepting path versions of NP, of the counting hierarchy, and of ModmNP for m > 1. We further prove that the class of nondeterministic path-restricted languages is closed under bounded truth-table reductions. 1 Introduction and Overview One of the goals of computational complexity theory is to classify the inclusions and separations of complexity classes. Though nontrivial separation of complexity classes is often a challenging problem (e.g. P i: NP?), the inclusion structure of complexity classes is progressively becoming clearer [Sim77,Lau83,Zac86,Sch87]. This paper proves that Ef)P contains a broad range of complexity classes. 1.1 Parity Polynomial Time The class Ef)P, parity polynomial time, was defined and studied by Papadimitriou and . Zachos as a "moderate version" of Valiant's counting class #P . • Research supported by NSF grant CCR-8709818. t Research supported in part by a Hewlett-Packard Corporation equipment grant. -

Ex. 8 Complexity 1. by Savich Theorem NL ⊆ DSPACE (Log2n)
Ex. 8 Complexity 1. By Savich theorem NL ⊆ DSP ACE(log2n) ⊆ DSP ASE(n). we saw in one of the previous ex. that DSP ACE(n2f(n)) 6= DSP ACE(f(n)) we also saw NL ½ P SP ASE so we conclude NL ½ DSP ACE(n) ½ DSP ACE(n3) ½ P SP ACE but DSP ACE(n) 6= DSP ACE(n3) as needed. 2. (a) We emulate the running of the s ¡ t ¡ conn algorithm in parallel for two paths (that is, we maintain two pointers, both starts at s and guess separately the next step for each of them). We raise a flag as soon as the two pointers di®er. We stop updating each of the two pointers as soon as it gets to t. If both got to t and the flag is raised, we return true. (b) As A 2 NL by Immerman-Szelepsc¶enyi Theorem (NL = vo ¡ NL) we know that A 2 NL. As C = A \ s ¡ t ¡ conn and s ¡ t ¡ conn 2 NL we get that A 2 NL. 3. If L 2 NICE, then taking \quit" as reject we get an NP machine (when x2 = L we always reject) for L, and by taking \quit" as accept we get coNP machine for L (if x 2 L we always reject), and so NICE ⊆ NP \ coNP . For the other direction, if L is in NP \coNP , then there is one NP machine M1(x; y) solving L, and another NP machine M2(x; z) solving coL. We can therefore de¯ne a new machine that guesses the guess y for M1, and the guess z for M2. -
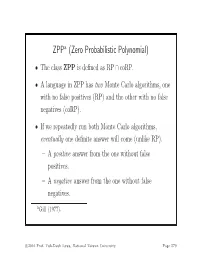
ZPP (Zero Probabilistic Polynomial)
ZPPa (Zero Probabilistic Polynomial) • The class ZPP is defined as RP ∩ coRP. • A language in ZPP has two Monte Carlo algorithms, one with no false positives (RP) and the other with no false negatives (coRP). • If we repeatedly run both Monte Carlo algorithms, eventually one definite answer will come (unlike RP). – A positive answer from the one without false positives. – A negative answer from the one without false negatives. aGill (1977). c 2016 Prof. Yuh-Dauh Lyuu, National Taiwan University Page 579 The ZPP Algorithm (Las Vegas) 1: {Suppose L ∈ ZPP.} 2: {N1 has no false positives, and N2 has no false negatives.} 3: while true do 4: if N1(x)=“yes”then 5: return “yes”; 6: end if 7: if N2(x) = “no” then 8: return “no”; 9: end if 10: end while c 2016 Prof. Yuh-Dauh Lyuu, National Taiwan University Page 580 ZPP (concluded) • The expected running time for the correct answer to emerge is polynomial. – The probability that a run of the 2 algorithms does not generate a definite answer is 0.5 (why?). – Let p(n) be the running time of each run of the while-loop. – The expected running time for a definite answer is ∞ 0.5iip(n)=2p(n). i=1 • Essentially, ZPP is the class of problems that can be solved, without errors, in expected polynomial time. c 2016 Prof. Yuh-Dauh Lyuu, National Taiwan University Page 581 Large Deviations • Suppose you have a biased coin. • One side has probability 0.5+ to appear and the other 0.5 − ,forsome0<<0.5. -

The Weakness of CTC Qubits and the Power of Approximate Counting
The weakness of CTC qubits and the power of approximate counting Ryan O'Donnell∗ A. C. Cem Sayy April 7, 2015 Abstract We present results in structural complexity theory concerned with the following interre- lated topics: computation with postselection/restarting, closed timelike curves (CTCs), and approximate counting. The first result is a new characterization of the lesser known complexity class BPPpath in terms of more familiar concepts. Precisely, BPPpath is the class of problems that can be efficiently solved with a nonadaptive oracle for the Approximate Counting problem. Similarly, PP equals the class of problems that can be solved efficiently with nonadaptive queries for the related Approximate Difference problem. Another result is concerned with the compu- tational power conferred by CTCs; or equivalently, the computational complexity of finding stationary distributions for quantum channels. Using the above-mentioned characterization of PP, we show that any poly(n)-time quantum computation using a CTC of O(log n) qubits may as well just use a CTC of 1 classical bit. This result essentially amounts to showing that one can find a stationary distribution for a poly(n)-dimensional quantum channel in PP. ∗Department of Computer Science, Carnegie Mellon University. Work performed while the author was at the Bo˘gazi¸ciUniversity Computer Engineering Department, supported by Marie Curie International Incoming Fellowship project number 626373. yBo˘gazi¸ciUniversity Computer Engineering Department. 1 Introduction It is well known that studying \non-realistic" augmentations of computational models can shed a great deal of light on the power of more standard models. The study of nondeterminism and the study of relativization (i.e., oracle computation) are famous examples of this phenomenon. -

IBM Research Report Derandomizing Arthur-Merlin Games And
H-0292 (H1010-004) October 5, 2010 Computer Science IBM Research Report Derandomizing Arthur-Merlin Games and Approximate Counting Implies Exponential-Size Lower Bounds Dan Gutfreund, Akinori Kawachi IBM Research Division Haifa Research Laboratory Mt. Carmel 31905 Haifa, Israel Research Division Almaden - Austin - Beijing - Cambridge - Haifa - India - T. J. Watson - Tokyo - Zurich LIMITED DISTRIBUTION NOTICE: This report has been submitted for publication outside of IBM and will probably be copyrighted if accepted for publication. It has been issued as a Research Report for early dissemination of its contents. In view of the transfer of copyright to the outside publisher, its distribution outside of IBM prior to publication should be limited to peer communications and specific requests. After outside publication, requests should be filled only by reprints or legally obtained copies of the article (e.g. , payment of royalties). Copies may be requested from IBM T. J. Watson Research Center , P. O. Box 218, Yorktown Heights, NY 10598 USA (email: [email protected]). Some reports are available on the internet at http://domino.watson.ibm.com/library/CyberDig.nsf/home . Derandomization Implies Exponential-Size Lower Bounds 1 DERANDOMIZING ARTHUR-MERLIN GAMES AND APPROXIMATE COUNTING IMPLIES EXPONENTIAL-SIZE LOWER BOUNDS Dan Gutfreund and Akinori Kawachi Abstract. We show that if Arthur-Merlin protocols can be deran- domized, then there is a Boolean function computable in deterministic exponential-time with access to an NP oracle, that cannot be computed by Boolean circuits of exponential size. More formally, if prAM ⊆ PNP then there is a Boolean function in ENP that requires circuits of size 2Ω(n). -

Inaugural - Dissertation
INAUGURAL - DISSERTATION zur Erlangung der Doktorwurde¨ der Naturwissenschaftlich-Mathematischen Gesamtfakultat¨ der Ruprecht - Karls - Universitat¨ Heidelberg vorgelegt von Timur Bakibayev aus Karagandinskaya Tag der mundlichen¨ Prufung:¨ 10.03.2010 Weak Completeness Notions For Exponential Time Gutachter: Prof. Dr. Klaus Ambos-Spies Prof. Dr. Serikzhan Badaev Abstract The standard way for proving a problem to be intractable is to show that the problem is hard or complete for one of the standard complexity classes containing intractable problems. Lutz (1995) proposed a generalization of this approach by introducing more general weak hardness notions which still imply intractability. While a set A is hard for a class C if all problems in C can be reduced to A (by a polynomial-time bounded many-one reduction) and complete if it is hard and a member of C, Lutz proposed to call a set A weakly hard if a nonnegligible part of C can be reduced to A and to call A weakly complete if in addition A 2 C. For the exponential-time classes E = DTIME(2lin) and EXP = DTIME(2poly), Lutz formalized these ideas by introducing resource bounded (Lebesgue) measures on these classes and by saying that a subclass of E is negligible if it has measure 0 in E (and similarly for EXP). A variant of these concepts, based on resource bounded Baire category in place of measure, was introduced by Ambos-Spies (1996) where now a class is declared to be negligible if it is meager in the corresponding resource bounded sense. In our thesis we introduce and investigate new, more general, weak hardness notions for E and EXP and compare them with the above concepts from the litera- ture. -

A Note on NP ∩ Conp/Poly Copyright C 2000, Vinodchandran N
BRICS Basic Research in Computer Science BRICS RS-00-19 V. N. Variyam: A Note on A Note on NP \ coNP=poly NP \ coNP = Vinodchandran N. Variyam poly BRICS Report Series RS-00-19 ISSN 0909-0878 August 2000 Copyright c 2000, Vinodchandran N. Variyam. BRICS, Department of Computer Science University of Aarhus. All rights reserved. Reproduction of all or part of this work is permitted for educational or research use on condition that this copyright notice is included in any copy. See back inner page for a list of recent BRICS Report Series publications. Copies may be obtained by contacting: BRICS Department of Computer Science University of Aarhus Ny Munkegade, building 540 DK–8000 Aarhus C Denmark Telephone: +45 8942 3360 Telefax: +45 8942 3255 Internet: [email protected] BRICS publications are in general accessible through the World Wide Web and anonymous FTP through these URLs: http://www.brics.dk ftp://ftp.brics.dk This document in subdirectory RS/00/19/ A Note on NP ∩ coNP/poly N. V. Vinodchandran BRICS, Department of Computer Science, University of Aarhus, Denmark. [email protected] August, 2000 Abstract In this note we show that AMexp 6⊆ NP ∩ coNP=poly, where AMexp denotes the exponential version of the class AM.Themain part of the proof is a collapse of EXP to AM under the assumption that EXP ⊆ NP ∩ coNP=poly 1 Introduction The issue of how powerful circuit based computation is, in comparison with Turing machine based computation has considerable importance in complex- ity theory. There are a large number of important open problems in this area. -

The Computational Complexity Column by V
The Computational Complexity Column by V. Arvind Institute of Mathematical Sciences, CIT Campus, Taramani Chennai 600113, India [email protected] http://www.imsc.res.in/~arvind The mid-1960’s to the early 1980’s marked the early epoch in the field of com- putational complexity. Several ideas and research directions which shaped the field at that time originated in recursive function theory. Some of these made a lasting impact and still have interesting open questions. The notion of lowness for complexity classes is a prominent example. Uwe Schöning was the first to study lowness for complexity classes and proved some striking results. The present article by Johannes Köbler and Jacobo Torán, written on the occasion of Uwe Schöning’s soon-to-come 60th birthday, is a nice introductory survey on this intriguing topic. It explains how lowness gives a unifying perspective on many complexity results, especially about problems that are of intermediate complexity. The survey also points to the several questions that still remain open. Lowness results: the next generation Johannes Köbler Humboldt Universität zu Berlin [email protected] Jacobo Torán Universität Ulm [email protected] Abstract Our colleague and friend Uwe Schöning, who has helped to shape the area of Complexity Theory in many decisive ways is turning 60 this year. As a little birthday present we survey in this column some of the newer results related with the concept of lowness, an idea that Uwe translated from the area of Recursion Theory in the early eighties. Originally this concept was applied to the complexity classes in the polynomial time hierarchy. -

Complete Problems of Propositional Logic for the Exponential Hierarchy
Complete Problems of Propositional Logic for the Exponential Hierarchy Martin Lück Institut für Theoretische Informatik Leibniz Universität Hannover, DE [email protected] Abstract. Large complexity classes, like the exponential time hierarchy, received little attention in terms of finding complete problems. In this work a generalization of propositional logic is investigated which fills this gap with the introduction of Boolean higher-order quantifiers or equivalently Boolean Skolem functions. This builds on the important results of Wrathall and Stockmeyer regarding complete problems, namely QBF and QBF푘, for the polynomial hierarchy. Furthermore it generalizes the Dependency QBF problem introduced by Peterson, Reif and Azhar which is complete for NEXP, the first level of the exponential hierarchy. Also it turns out that the hardness results do not collapse at the consideration of conjunctive and disjunctive normal forms, in contrast to plain QBF. 1 Introduction The class of problems decidable in polynomial space, PSPACE, can equivalently be defined as the class AP, i.e., via alternating machines with polynomial P P runtime and no bound on the alternation number. The classes 훴푘 and 훱푘 of the polynomial hierarchy are then exactly the restrictions of AP to levels of bounded alternation [5]. The problem of quantified Boolean formulas, often called QBF resp. QBF푘, is complete for these classes. The subscript 푘 denotes the number of allowed quantifier alternations of a qbf in prenex normal form, whereas QBF imposes no bound on quantifier alternations. For this correspondence Stockmeyer called QBF the 휔-jump of the bounded QBF푘 variants, and similar the class PSPACE the 휔-jump of the polynomial hierarchy [15], in reference to the arithmetical hierarchy.