Softether VPN Project
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Flexgw Ipsec VPN Image User Guide
FlexGW IPsec VPN Image User Guide Zhuyun Information Technology Co.,Ltd. www.cloudcare.cn Zhuyun Information Technology Co.,Ltd. Contents .......................................................................................................... .................................................................................................................. 1 Introduction 4 1.1 Software Compon.e..n..t.s................................................................................................................... 4 1.2 Login Description ................................................................................................................... 4 1.3 Function Description ....................................................................................................5 1.4 Typical Scenarios Des..c..r..i.p..t..i.o..n......................................................................................................5 1.5 Program Description .................................................................................6 1.6 Software Operation Command Summary ............................... 7 ............................................................................................................... 2 IPSec Site-to-Site VPN User Guide (VPC network scenario) 8 2.1 Start IPSec VPN.s..e..r..v..i.c..e.................................................................................................................8 2.2 Add new tunnel ................................................................................................................. -
![Arxiv:1907.07120V1 [Cs.CY] 16 Jul 2019 1 Introduction That China Hindered Access to I2P by Poisoning DNS Resolu- Tions of the I2P Homepage and Three Reseed Servers](https://docslib.b-cdn.net/cover/9451/arxiv-1907-07120v1-cs-cy-16-jul-2019-1-introduction-that-china-hindered-access-to-i2p-by-poisoning-dns-resolu-tions-of-the-i2p-homepage-and-three-reseed-servers-59451.webp)
Arxiv:1907.07120V1 [Cs.CY] 16 Jul 2019 1 Introduction That China Hindered Access to I2P by Poisoning DNS Resolu- Tions of the I2P Homepage and Three Reseed Servers
Measuring I2P Censorship at a Global Scale Nguyen Phong Hoang Sadie Doreen Michalis Polychronakis Stony Brook University The Invisible Internet Project Stony Brook University Abstract required flexibility for conducting fine-grained measurements on demand. We demonstrate these benefits by conducting an The prevalence of Internet censorship has prompted the in-depth investigation of the extent to which the I2P (invis- creation of several measurement platforms for monitoring ible Internet project) anonymity network is blocked across filtering activities. An important challenge faced by these different countries. platforms revolves around the trade-off between depth of mea- Due to the prevalence of Internet censorship and online surement and breadth of coverage. In this paper, we present surveillance in recent years [7, 34, 62], many pro-privacy and an opportunistic censorship measurement infrastructure built censorship circumvention tools, such as proxy servers, virtual on top of a network of distributed VPN servers run by vol- private networks (VPN), and anonymity networks have been unteers, which we used to measure the extent to which the developed. Among these tools, Tor [23] (based on onion rout- I2P anonymity network is blocked around the world. This ing [39,71]) and I2P [85] (based on garlic routing [24,25,33]) infrastructure provides us with not only numerous and ge- are widely used by privacy-conscious and censored users, as ographically diverse vantage points, but also the ability to they provide a higher level of privacy and anonymity [42]. conduct in-depth measurements across all levels of the net- In response, censors often hinder access to these services work stack. -

Implementation Single Account Pdc Vpn Based on Ldap
IMPLEMENTATION SINGLE ACCOUNT PDC VPN BASED ON LDAP Gregorius Hendita Artha Kusuma Teknik Informatika, Fakultas Teknik Universitas Pancasila [email protected] Abstrak Data is an important for the company. Centralized data storage to facilitate users for accessing data in the company. Data will be stored centrally with PDC (Primary Domain Controller). Build communicate between head office and branch office requires high cost for each connection is not enough to ensure safety and security of data. Exchange data between head office and branch office should be kept confidential. VPN (Virtual Private Network) makes communication more efficient, not only the cost affordable that connection, security and safety will be the primary facility of VPN (Virtual Private Network). Service were established in the system will be integrated using LDAP (Lightweight Directory Access Protocol) to create a single account in each services such as PDC (Primary Domain Controller) and VPN (Virtual Private Network). The purposes of this final project to design and implementation a system centralized data storage and build communicate between head office and branch office are integrated with LDAP (Lighweight Active Directory Protocol). Hopefully this system can give more advantage to each network users. Keyword: PDC, VPN, LDAP, Single Account. I. Introduction previous workstations. To support the performance of the employees of the company of course has a Centralized data storage makes it easy for users variety of network services are formed in it such as to access data. many companies need a ftp, mail server, file sharing etc. These services of centralized storage system, because the data is course have their respective accounts. -
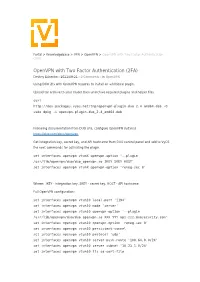
Openvpn with Two-Factor Authentication (2FA)
Portal > Knowledgebase > VPN > OpenVPN > OpenVPN with Two Factor Authentication (2FA) OpenVPN with Two Factor Authentication (2FA) Dmitriy Eshenko - 2021-09-21 - 0 Comments - in OpenVPN Using DUO 2fa with OpenVPN requires to install an additional plugin. Upload tar archive to your router then unarchive required plugins and helper files curl http://dev.packages.vyos.net/tmp/openvpn-plugin-duo_2.4_amd64.deb -O sudo dpkg -i openvpn-plugin-duo_2.4_amd64.deb Following documentation from DUO site, configure OpenVPN instance https://duo.com/docs/openvpn Get integration key, secret key, and API hostname from DUO control panel and add to VyOS the next commands for activating the plugin. set interfaces openvpn vtunX openvpn-option '--plugin /usr/lib/openvpn/duo/duo_openvpn.so IKEY SKEY HOST' set interfaces openvpn vtunX openvpn-option 'reneg-sec 0' Where: IKEY - integration key, SKEY - secret key, HOST - API hostname Full OpenVPN configuration: set interfaces openvpn vtun10 local-port '1194' set interfaces openvpn vtun10 mode 'server' set interfaces openvpn vtun10 openvpn-option '--plugin /usr/lib/openvpn/duo/duo_openvpn.so XXX YYY api-zzz.duosecurity.com' set interfaces openvpn vtun10 openvpn-option 'reneg-sec 0' set interfaces openvpn vtun10 persistent-tunnel set interfaces openvpn vtun10 protocol 'udp' set interfaces openvpn vtun10 server push-route '100.64.0.0/24' set interfaces openvpn vtun10 server subnet '10.23.1.0/24' set interfaces openvpn vtun10 tls ca-cert-file '/config/auth/ovpn/ca.crt' set interfaces openvpn vtun10 tls cert-file '/config/auth/ovpn/central.crt' set interfaces openvpn vtun10 tls crl-file '/config/auth/ovpn/crl.pem' set interfaces openvpn vtun10 tls dh-file '/config/auth/ovpn/dh.pem' set interfaces openvpn vtun10 tls key-file '/config/auth/ovpn/central.key' How to generate cryptographic materials described by the following link https://support.vyos.io/en/kb/articles/using-easy-rsa-to-generate-x-509-certificates-and-keys -2. -

Poster: Introducing Massbrowser: a Censorship Circumvention System Run by the Masses
Poster: Introducing MassBrowser: A Censorship Circumvention System Run by the Masses Milad Nasr∗, Anonymous∗, and Amir Houmansadr University of Massachusetts Amherst fmilad,[email protected] ∗Equal contribution Abstract—We will present a new censorship circumvention sys- side the censorship regions, which relay the Internet traffic tem, currently being developed in our group. The new system of the censored users. This includes systems like Tor, VPNs, is called MassBrowser, and combines several techniques from Psiphon, etc. Unfortunately, such circumvention systems are state-of-the-art censorship studies to design a hard-to-block, easily blocked by the censors by enumerating their limited practical censorship circumvention system. MassBrowser is a set of proxy server IP addresses [14]. (2) Costly to operate: one-hop proxy system where the proxies are volunteer Internet To resist proxy blocking by the censors, recent circumven- users in the free world. The power of MassBrowser comes from tion systems have started to deploy the proxies on shared-IP the large number of volunteer proxies who frequently change platforms such as CDNs, App Engines, and Cloud Storage, their IP addresses as the volunteer users move to different a technique broadly referred to as domain fronting [3]. networks. To get a large number of volunteer proxies, we This mechanism, however, is prohibitively expensive [11] provide the volunteers the control over how their computers to operate for large scales of users. (3) Poor QoS: Proxy- are used by the censored users. Particularly, the volunteer based circumvention systems like Tor and it’s variants suffer users can decide what websites they will proxy for censored from low quality of service (e.g., high latencies and low users, and how much bandwidth they will allocate. -

N2N: a Layer Two Peer-To-Peer VPN
N2N: A Layer Two Peer-to-Peer VPN Luca Deri1, Richard Andrews2 ntop.org, Pisa, Italy1 Symstream Technologies, Melbourne, Australia2 {deri, andrews}@ntop.org Abstract. The Internet was originally designed as a flat data network delivering a multitude of protocols and services between equal peers. Currently, after an explosive growth fostered by enormous and heterogeneous economic interests, it has become a constrained network severely enforcing client-server communication where addressing plans, packet routing, security policies and users’ reachability are almost entirely managed and limited by access providers. From the user’s perspective, the Internet is not an open transport system, but rather a telephony-like communication medium for content consumption. This paper describes the design and implementation of a new type of peer-to- peer virtual private network that can allow users to overcome some of these limitations. N2N users can create and manage their own secure and geographically distributed overlay network without the need for central administration, typical of most virtual private network systems. Keywords: Virtual private network, peer-to-peer, network overlay. 1. Motivation and Scope of Work Irony pervades many pages of history, and computing history is no exception. Once personal computing had won the market battle against mainframe-based computing, the commercial evolution of the Internet in the nineties stepped the computing world back to a substantially rigid client-server scheme. While it is true that the today’s Internet serves as a good transport system for supplying a plethora of data interchange services, virtually all of them are delivered by a client-server model, whether they are centralised or distributed, pay-per-use or virtually free [1]. -

Brocade Vyatta Network OS ALG Configuration Guide, 5.2R1
CONFIGURATION GUIDE Brocade Vyatta Network OS ALG Configuration Guide, 5.2R1 Supporting Brocade 5600 vRouter, VNF Platform, and Distributed Services Platform 53-1004711-01 24 October 2016 © 2016, Brocade Communications Systems, Inc. All Rights Reserved. Brocade, the B-wing symbol, and MyBrocade are registered trademarks of Brocade Communications Systems, Inc., in the United States and in other countries. Other brands, product names, or service names mentioned of Brocade Communications Systems, Inc. are listed at www.brocade.com/en/legal/ brocade-Legal-intellectual-property/brocade-legal-trademarks.html. Other marks may belong to third parties. Notice: This document is for informational purposes only and does not set forth any warranty, expressed or implied, concerning any equipment, equipment feature, or service offered or to be offered by Brocade. Brocade reserves the right to make changes to this document at any time, without notice, and assumes no responsibility for its use. This informational document describes features that may not be currently available. Contact a Brocade sales office for information on feature and product availability. Export of technical data contained in this document may require an export license from the United States government. The authors and Brocade Communications Systems, Inc. assume no liability or responsibility to any person or entity with respect to the accuracy of this document or any loss, cost, liability, or damages arising from the information contained herein or the computer programs that accompany it. The product described by this document may contain open source software covered by the GNU General Public License or other open source license agreements. To find out which open source software is included in Brocade products, view the licensing terms applicable to the open source software, and obtain a copy of the programming source code, please visit http://www.brocade.com/support/oscd. -
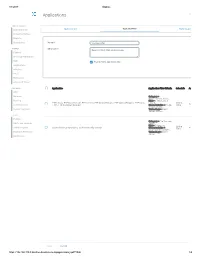
Applications Log Viewer
4/1/2017 Sophos Applications Log Viewer MONITOR & ANALYZE Control Center Application List Application Filter Traffic Shaping Default Current Activities Reports Diagnostics Name * Mike App Filter PROTECT Description Based on Block filter avoidance apps Firewall Intrusion Prevention Web Enable Micro App Discovery Applications Wireless Email Web Server Advanced Threat CONFIGURE Application Application Filter Criteria Schedule Action VPN Network Category = Infrastructure, Netw... Routing Risk = 1-Very Low, 2- FTPS-Data, FTP-DataTransfer, FTP-Control, FTP Delete Request, FTP Upload Request, FTP Base, Low, 4... All the Allow Authentication FTPS, FTP Download Request Characteristics = Prone Time to misuse, Tra... System Services Technology = Client Server, Netwo... SYSTEM Profiles Category = File Transfer, Hosts and Services Confe... Risk = 3-Medium Administration All the TeamViewer Conferencing, TeamViewer FileTransfer Characteristics = Time Allow Excessive Bandwidth,... Backup & Firmware Technology = Client Server Certificates Save Cancel https://192.168.110.3:4444/webconsole/webpages/index.jsp#71826 1/4 4/1/2017 Sophos Application Application Filter Criteria Schedule Action Applications Log Viewer Facebook Applications, Docstoc Website, Facebook Plugin, MySpace Website, MySpace.cn Website, Twitter Website, Facebook Website, Bebo Website, Classmates Website, LinkedIN Compose Webmail, Digg Web Login, Flickr Website, Flickr Web Upload, Friendfeed Web Login, MONITOR & ANALYZE Hootsuite Web Login, Friendster Web Login, Hi5 Website, Facebook Video -

106-Atvar Jattana.Cdr
Research Paper Engineering E-ISSN No : 2454-9916 | Volume : 3 | Issue : 5 | May 2017 VPNBROADBANDLANSHARINGWITHWI-FINANOBASED USBADAPTER Atvar Singh 1 | C.Er. Harisharan Aggarwal 2 1 Department of Electronics and Communication Engg., Guru Gobind Singh College Of Engg. & Technology, Guru kashi University, Talwandi sabo, Bathinda, Punjab, India. 2 HOD, Department of Electronics and Communication Engg., Guru Gobind Singh College Of Engg. & Technology, Guru kashi University, Talwandi sabo, Bathinda, Punjab, India ABSTRACT Virtual Private Network (VPN) is a network technology that creates a secure network connection over a public network such as the Internet or a private network owned by a service provider. Large corporations, educational institutions, and government agencies use VPN (wimax) technology to enable remote users to securely connect to a private network. Many corporations are very seriously concerned about VPN security of networks. In this regards, the VPN (wimax) modem and antenna standard was developed to the standard address the security problems, no doubts virtual private networking is famous for good security for the clients past few years. But VPN Broadband connection is a major problem not make a multiuser clients, because it is a single user. In the thesis work ,VPN (wimax) broadband internet connect through Wi-Fi on android mobile with the help of nano technology based mini adapter clients sharing a broadband LAN also we make with the help of nano adapter make a multiuser KEYWORDS: Wimax antenna, Broadband VPN, Nano mini adapter(IEEE 802.11) I. INTRODUCTION Service (QOS) management over the Internet can cause packet loss and other per- A Virtual private network (VPN) extends a private network across a public net- formance issues. -

Managed Firewalls
DEDICATED HOSTING PRODUCT OVERVIEW MANAGED FIREWALLS Securing your network from malicious activity. Rackspace delivers expertise and service for the world’s leading clouds and technologies. TRUST RACKSPACE And we can help secure your dedicated servers and your cloud, with firewalls from Cisco® and • A leader in the 2017 Gartner Magic Quadrant Juniper Networks — fully supported around the clock by certified Rackspace engineers. Your for Public Cloud Infrastructure Managed Service firewall is dedicated completely to your environment for the highest level of network security Providers, Worldwide and connectivity, and includes access to our Firewall Manager and our One-Hour Hardware • Hosting provider for more than half of the Replacement Guarantee. Fortune 100 • 16+ years of hosting experience WHY RACKSPACE FOR DEDICATED, FULLY MANAGED FIREWALLS? • Customers in 150+ countries You have valuable and confidential information stored on your dedicated and cloud servers. Dedicated firewalls from Cisco and Juniper Networks add an additional layer of security to your servers, helping to stop potentially malicious packets from ever reaching your network. “RACKSPACE’S SECURITY CONTROLS AND REPUTATION AS AN SSAE 16 CERTIFIED KEY BENEFITS PROVIDER HAS BEEN A Highest level of security: Help protect your data and stop potentially malicious packets TREMENDOUS FACTOR IN OUR from entering your network with an IPSec, and Common Criteria EAL4 evaluation status certified firewall. SUCCESS.” DAVID SCHIFFER :: FOUNDER AND PRESIDENT, Expertise: Rackspace security experts fully manage your firewalls 24x7x365. Consult with SAFE BANKING SYSTEMS CISSP-certified security engineers to assess and architect your firewalls to help you meet your security and compliance requirements. Visibility and control: Help protect your infrastructure with deep packet inspection of traffic based on traffic filtering rules you define. -

Threat Modeling and Circumvention of Internet Censorship by David Fifield
Threat modeling and circumvention of Internet censorship By David Fifield A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science in the Graduate Division of the University of California, Berkeley Committee in charge: Professor J.D. Tygar, Chair Professor Deirdre Mulligan Professor Vern Paxson Fall 2017 1 Abstract Threat modeling and circumvention of Internet censorship by David Fifield Doctor of Philosophy in Computer Science University of California, Berkeley Professor J.D. Tygar, Chair Research on Internet censorship is hampered by poor models of censor behavior. Censor models guide the development of circumvention systems, so it is important to get them right. A censor model should be understood not just as a set of capabilities|such as the ability to monitor network traffic—but as a set of priorities constrained by resource limitations. My research addresses the twin themes of modeling and circumvention. With a grounding in empirical research, I build up an abstract model of the circumvention problem and examine how to adapt it to concrete censorship challenges. I describe the results of experiments on censors that probe their strengths and weaknesses; specifically, on the subject of active probing to discover proxy servers, and on delays in their reaction to changes in circumvention. I present two circumvention designs: domain fronting, which derives its resistance to blocking from the censor's reluctance to block other useful services; and Snowflake, based on quickly changing peer-to-peer proxy servers. I hope to change the perception that the circumvention problem is a cat-and-mouse game that affords only incremental and temporary advancements. -

3. Security and Reliability
3. Security and Reliability 3.1. Excellent Security and Reliability, Superior to Hardware You might have a question that whether SoftEther VPN is really secure as same as hardware VPN products or not. Someone might think that software VPNs is inferior to hardware VPNs. Of course, SoftEther VPN is implemented as a software code, not hardware as either specific integrated circuit. But it is absolutely correct that SoftEther VPN has an adequate security fulfillment as same as hardware's one, and moreover it might be superior to hardware VPN. What is Hardware VPN Products? Please see the fact that almost all hardware VPNs on the today's market is not a pure hardware. They are nearly software program, actually. Do you have any experience to open the top cover of any Cisco Router? You can see that inside devices on the Cisco Router is almost same as today's computer. The major differences are only the architecture of CPU. To reduce the manufacturing cost, Cisco and other VPN vendors adopts cheaper CPU than computers, such as MIPS, ARM and PowerPC. Anything more important differences are there between a desktop computer and a hardware VPN router. And you can analyze the inside mechanism of Cisco Router by some information leaked from the Internet or books. Cisco VPN Router and other manufacturer's router are running the software operating system on their device. On the operating system, the routing and VPN session-managing software is also working to process VPN communication. Virtually almost all important processes are implemented as software, not as hardware, on the existing hardware VPN products in the today market.