Guide to Securing Apple OS X 10.10 Systems for IT Professionals: a NIST Security Configuration Checklist
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cocoa Touch & Iphone
Music Appreciation 243: Introduction to Rick Astley Evan Doll [email protected] Alan Cannistraro [email protected] Thursday, April 2, 2009 Thursday, April 2, 2009 Welcome to CS193P: iPhone Application Development Evan Doll [email protected] Alan Cannistraro [email protected] Thursday, April 2, 2009 Staff • Lecturers ■ Evan Doll [email protected] ■ Alan Cannistraro [email protected] • Student TAs ■ Troy Brant [email protected] ■ Paul Salzman [email protected] • “Professor Emeritus” ■ Paul Marcos [email protected] Thursday, April 2, 2009 How many of you... • Are familiar with object-oriented programming? • Have developed software with Mac OS X? • Have developed apps for the iPhone? Thursday, April 2, 2009 Lectures, Sections, Office Hours • Lectures ■ 320-105, Monday & Wednesday 3:15 – 4:30 PM • Optional Section ■ 200-205, Friday 3:15 – 4:05 PM as announced ■ Guest speakers, additional topics ■ First one will be next Friday 4/10 • Office Hours ■ Troy and Paul will be holding office hours ■ Time & location TBD, check website for details Thursday, April 2, 2009 Requirements • Prerequisite: CS 106B/X • Recommended Book: None, we’ll use Apple documentation • You must have access to an Intel-based Macintosh ■ Running Mac OS X 10.5 Leopard ■ iPhone SDK (Not available on cluster computers!) • Owning an iPhone or iPod Touch is not required ■ Assignments may be done with the iPhone Simulator ■ Loaner iPod Touches should be available, more details to come Thursday, April 2, 2009 Enrollment • Response has been phenomenal again -

Apple Bonjour for Windows 7 32 Bit Downloadl
Apple Bonjour For Windows 7 32 Bit Downloadl Apple Bonjour For Windows 7 32 Bit Downloadl 1 / 2 Download bonjour for windows 7 64 bit for free. Development Tools downloads - Bonjour SDK by Apple Inc. and many more programs are available for instant .... Download locations for Bonjour 1.0.6, Downloads: 9828, Size: 2.05 MB. Easily network your PC to an existing network. ... File section. File Type: Win32 EXE MIME Type: ... Company Name: Apple Inc. File Description: Bonjour .... You can download Bonjour for Windows from Apple's Bonjour support pages. Bonjour for Windows is bundled with Bonjour Print Services for .... Download Bonjour for Windows XP (32/64 bit) Free. ... Languages: English (en); Publisher Software: Apple Computer Inc; Gadgets: Desktop PC, Ultrabook, .... Bonjour, free and safe download. Bonjour latest version: A Free Networking Tool From Apple Computers. The Bonjour program was created by Apple as a .... Bonjour Print Services. Free Apple Windows XP/Vista/7/8/10 Version 2.0.2 Full Specs.. Apple's Bonjour is a software program that automatically manages ... With Microsoft Windows, it's optional, as long as your PC has no programs that require it. ... Rolls Out Bonjour Print Services for Windows as Free Download .... If you need help downloading or updating iTunes from the Microsoft Store, contact Microsoft for help. ... Windows 7 and 8 · Windows 10 ... Support; Bonjour; Apple Application Support 32-bit; Apple Application Support 64-bit.. Download Bonjour for Windows. ... Sistema operativo Windows 7 32 bit / Vista 32-bit / XP 32-bit / Windows 8; Licencia: Freeware (Gratis); Creador: Apple ... Bonjour para Windows es una aplicación útil y libre de Apple, con el que se crea ... -

Learn Yosemite OS X from PCM's Apple Experts
Learn Yosemite OS X from PCM’s Apple Experts Yosemite 101: OS X Support Essentials Give PCM the opportunity to train your team to support users of Apple’s Mac OS X Yosemite. Our Apple certified trainers are ready to come to your location and provide PCM’s Apple certified trainers will teach your team Yosemite OS X fundamentals and how to be efficient with you with invaluable Yosemite tools and resources. hands-on instruction. OS X Yosemite Support Essentials is a three-day, Who Should Attend hands-on course that provides an in-depth explo- • Help desk specialists, technical coordinators, ration of troubleshooting on Mac OS X v10.10 Yo- service technicians, and others who support semite. This course is designed to give you a tour Mac users. of the breadth of functionality of Mac OS X v10.10 • Technical support personnel in businesses that Yosemite and the best methods for effectively use Macs. supporting users of Mac OS X v10.10 Yosemite • Technical coordinators or power users who systems. The course is a combination of lectures manage networks of computers running and hands-on case study exercises that provide Mac OS X — such as teachers and technology practical real-world experience. specialists who manage networks or computer labs. At your location For a class at your location, PCM will provide an What You Will Learn Apple Certified Trainer, all the student materials, • The troubleshooting process and how to and an exam voucher for each attendee (up to become more efficient with available tools 6 students included in price). -

Dropdmg 3.6.2 Manual
DropDMG 3.6.2 Manual C-Command Software c-command.com February 16, 2021 Contents 1 Introduction 4 1.1 Feature List..............................................4 2 Installing and Updating 6 2.1 Requirements.............................................6 2.2 Installing DropDMG.........................................7 2.3 Updating From a Previous Version.................................7 2.4 Reinstalling a Fresh Copy......................................8 2.5 Uninstalling DropDMG.......................................9 2.6 Security & Privacy Access......................................9 3 Using DropDMG 13 3.1 Basics................................................. 13 3.2 Making a Bootable Device Image of a Hard Drive......................... 14 3.3 Backing Up Your Files to CD/DVD................................ 16 3.4 Burning Backups of CDs/DVDs................................... 17 3.5 Restoring Files and Disks...................................... 18 3.6 Making Images With Background Pictures............................. 19 3.7 Protecting Your Files With Encryption............................... 20 3.8 Transferring Files Securely...................................... 21 3.9 Sharing Licenses and Layouts.................................... 21 3.10 Splitting a File or Folder Into Pieces................................ 22 3.11 Creating a DropDMG Quick Action................................ 22 4 Menus 23 4.1 The DropDMG Menu........................................ 23 4.1.1 About DropDMG...................................... 23 4.1.2 Software -
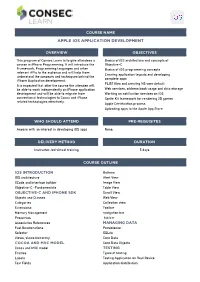
Apple Ios Application Development
COURSE NAME APPLE IOS APPLICATION DEVELOPMENT OVERVIEW OBJECTIVES This program of Consec Learn is to give attendees a Basics of iOS architecture and concepts of course in iPhone Programming. It will introduce the Objective-C Framework, Programming languages and other Basics of iOS programming concepts relevant APIs to the audience and will help them Creating application layouts and developing understand the concepts and techniques behind the complete apps iPhone Application development. PLIST files and creating NS user default It is expected that after the course the attendee will be able to work independently on iPhone application Web services, address book usage and data storage development and will be able to migrate from Working on notification services on iOS conventional technologies to Cocoa and iPhone Sprite Kit framework for rendering 2D games related technologies effectively. Apple Certification process Uploading apps to the Apple App Store WHO SHOULD ATTEND PRE-REQUISITES Anyone with an interest in developing iOS apps None. DELIVERY METHOD DURATION Instructor-led virtual training 5 days COURSE OUTLINE IOS INTRODUCTION Buttons IOS architecture Alert View XCode and interface builder Image View Objective-C -Fundamentals Table View OBJECTIVE-C AND IPHONE SDK Scroll View Objects and Classes Web View Categories Collection view Extensions Toolbar Memory Management navigation bar Properties tab bar Associative References MANAGING DATA Fast Enumerations Persistence Selector SQLite Views, Views hierarchy Core Data COCOA AND MVC MODEL -

Enterprise Best Practices for Ios Devices On
White Paper Enterprise Best Practices for iOS devices and Mac computers on Cisco Wireless LAN Updated: January 2018 © 2018 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 1 of 51 Contents SCOPE .............................................................................................................................................. 4 BACKGROUND .................................................................................................................................. 4 WIRELESS LAN CONSIDERATIONS .................................................................................................... 5 RF Design Guidelines for iOS devices and Mac computers on Cisco WLAN ........................................................ 5 RF Design Recommendations for iOS devices and Mac computers on Cisco WLAN ........................................... 6 Wi-Fi Channel Coverage .................................................................................................................................. 7 ClientLink Beamforming ................................................................................................................................ 10 Wi-Fi Channel Bandwidth ............................................................................................................................. 10 Data Rates .................................................................................................................................................... 12 802.1X/EAP Authentication .......................................................................................................................... -

Best Practices for Integrating OS X with Active Directory
Apple Technical White Paper Best Practices for Integrating OS X with Active Directory OS X Mountain Lion v10.8 Contents Introduction ........................................................................................................................3 How to Integrate OS X with Active Directory .......................................................4 Enterprise Integration Challenges .............................................................................7 Deployment Strategies ..................................................................................................9 Home Directories ..............................................................................................................10 Conclusion ...........................................................................................................................11 Appendix A: More Information ....................................................................................12 Appendix B: Third-Party Add-on Solutions ............................................................13 2 Apple Technical White Paper Best Practices for Integrating OS X with Active Directory Introduction Apple’s support for Active Directory within OS X enables Mac clients and servers to integrate smoothly into existing Active Directory environments, and provides the option of deploying a single, directory services infrastructure that can support both Mac and Windows clients. Apple’s Built-in Solution Large organizations have a need to manage user identities and access across a variety -

Security Analysis and Decryption of Lion Full Disk Encryption
Infiltrate the Vault: Security Analysis and Decryption of Lion Full Disk Encryption Omar Choudary Felix Grobert¨ ∗ Joachim Metz ∗ University of Cambridge [email protected] [email protected] [email protected] Abstract 1 Introduction Since the launch of Mac OS X 10.7, also known as Lion, With the launch of Mac OS X 10.7 (Lion), Apple has Apple includes a volume encryption software named introduced a volume encryption mechanism known as FileVault 2 [8] in their operating system. While the pre- FileVault 2. Apple only disclosed marketing aspects of vious version of FileVault (introduced with Mac OS X the closed-source software, e.g. its use of the AES-XTS 10.3) only encrypted the home folder, FileVault 2 can en- tweakable encryption, but a publicly available security crypt the entire volume containing the operating system evaluation and detailed description was unavailable until (this is commonly referred to as full disk encryption). now. This has two major implications: first, there is now a new functional layer between the encrypted volume and We have performed an extensive analysis of the original file system (typically a version of HFS Plus). FileVault 2 and we have been able to find all the This new functional layer is actually a full volume man- algorithms and parameters needed to successfully read ager which Apple called CoreStorage [10] Although this an encrypted volume. This allows us to perform forensic full volume manager could be used for more than volume investigations on encrypted volumes using our own encryption (e.g. mirroring, snapshots or online storage tools. -
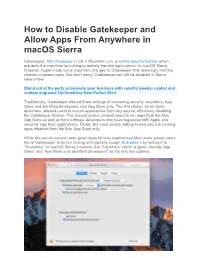
How to Disable Gatekeeper and Allow Apps from Anywhere in Macos Sierra
How to Disable Gatekeeper and Allow Apps From Anywhere in macOS Sierra Gatekeeper, first introduced in OS X Mountain Lion, is a Mac security feature which prevents the user from launching potentially harmful applications. In macOS Sierra, however, Apple made some important changes to Gatekeeper that seemingly limit the choices of power users. But don’t worry, Gatekeeper can still be disabled in Sierra. Here’s how. Stand out at the party or promote your business with colorful powder coated and custom engraved Yeti tumblers from Perfect Etch. Traditionally, Gatekeeper offered three settings of increasing security: anywhere, App Store and identified developers, and App Store only. The first choice, as its name describes, allowed users to launch applications from any source, effectively disabling the Gatekeeper feature. The second choice allowed users to run apps from the Mac App Store as well as from software developers who have registered with Apple and securely sign their applications. Finally, the most secure setting limited users to running apps obtained from the Mac App Store only. While the secure options were good ideas for less experienced Mac users, power users found Gatekeeper to be too limiting and typically sought to disable it by setting it to “Anywhere.” In macOS Sierra, however, the “Anywhere” option is gone, leaving “App Store” and “App Store and identified developers” as the only two options. Disable Gatekeeper in macOS Sierra The Gatekeeper settings can be found in System Preferences > Security & Privacy > General. The Gatekeeper options are located beneath “All apps downloaded from:” with the choice of “Anywhere” missing. Thankfully, the “Anywhere” setting can be restored to Gatekeeper in Sierra with a Terminal command. -

Open Directory Administration for Version 10.5 Leopard Second Edition
Mac OS X Server Open Directory Administration For Version 10.5 Leopard Second Edition Apple Inc. © 2008 Apple Inc. All rights reserved. The owner or authorized user of a valid copy of Mac OS X Server software may reproduce this publication for the purpose of learning to use such software. No part of this publication may be reproduced or transmitted for commercial purposes, such as selling copies of this publication or for providing paid-for support services. Every effort has been made to make sure that the information in this manual is correct. Apple Inc., is not responsible for printing or clerical errors. Apple 1 Infinite Loop Cupertino CA 95014-2084 www.apple.com The Apple logo is a trademark of Apple Inc., registered in the U.S. and other countries. Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, iCal, iChat, Leopard, Mac, Macintosh, QuickTime, Xgrid, and Xserve are trademarks of Apple Inc., registered in the U.S. and other countries. Finder is a trademark of Apple Inc. Adobe and PostScript are trademarks of Adobe Systems Incorporated. UNIX is a registered trademark of The Open Group. Other company and product names mentioned herein are trademarks of their respective companies. Mention of third-party products is for informational purposes only and constitutes neither an endorsement nor a recommendation. Apple assumes no responsibility with regard to the performance or use of these products. -

Speech & Telephony for Web.Qxp
Alfred’s Teach Yourself Computer Audio Speech and Telephony (Free supplemental chapter, only available at www.alfred.com) TODD SOUVIGNIER Copyright © MMIII by Alfred Publishing Co., Inc. All rights reserved. Alfred Publishing Co., Inc. 16320 Roscoe Blvd., Suite 100 P. O. Box 10003 Van Nuys, CA 91410-0003 www.alfred.com SPEECH AND TELEPHONY What you’ll learn to do in this chapter: •Make your computer react to spoken commands •Make your computer talk back to you •Create a voice print “password” •Do computer-to-computer voice conferencing •Use the computer for phone dialing •Make telephone calls over the Internet The various forms of technology covered in Alfred’s been available to Windows users for many years, but, Teach Yourself Computer Audio can easily be used to until recently, users had to obtain them by way of record, process and play back human speech just as purchasing and installing add-in upgrades of separate well as music or any other sound. Speech is a universal software packages. Apple has also led the field in voice human attribute, so it is no surprise that a number of recognition, allowing users to create system passwords different technologies and applications related to it based upon the unique sound of one’s voice. have arisen on the various computer platforms. In addition to technologies that allow the computer to The popular image of futuristic computing was largely talk or listen, transmission technologies convey the derived from films such as 2001: A Space Odyssey and user’s voice to another location. Many businesses the television series Star Trek. -
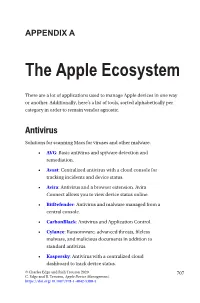
The Apple Ecosystem
APPENDIX A The Apple Ecosystem There are a lot of applications used to manage Apple devices in one way or another. Additionally, here’s a list of tools, sorted alphabetically per category in order to remain vendor agnostic. Antivirus Solutions for scanning Macs for viruses and other malware. • AVG: Basic antivirus and spyware detection and remediation. • Avast: Centralized antivirus with a cloud console for tracking incidents and device status. • Avira: Antivirus and a browser extension. Avira Connect allows you to view device status online. • BitDefender: Antivirus and malware managed from a central console. • CarbonBlack: Antivirus and Application Control. • Cylance: Ransomware, advanced threats, fileless malware, and malicious documents in addition to standard antivirus. • Kaspersky: Antivirus with a centralized cloud dashboard to track device status. © Charles Edge and Rich Trouton 2020 707 C. Edge and R. Trouton, Apple Device Management, https://doi.org/10.1007/978-1-4842-5388-5 APPENDIX A THe AppLe ECOSYSteM • Malware Bytes: Antivirus and malware managed from a central console. • McAfee Endpoint Security: Antivirus and advanced threat management with a centralized server to track devices. • Sophos: Antivirus and malware managed from a central console. • Symantec Mobile Device Management: Antivirus and malware managed from a central console. • Trend Micro Endpoint Security: Application whitelisting, antivirus, and ransomware protection in a centralized console. • Wandera: Malicious hot-spot monitoring, jailbreak detection, web gateway for mobile threat detection that integrates with common MDM solutions. Automation Tools Scripty tools used to automate management on the Mac • AutoCasperNBI: Automates the creation of NetBoot Images (read: NBI’s) for use with Casper Imaging. • AutoDMG: Takes a macOS installer (10.10 or newer) and builds a system image suitable for deployment with Imagr, DeployStudio, LANrev, Jamf Pro, and other asr or Apple Systems Restore-based imaging tools.