Faculty of Engineering, Technology and Management Sciences
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Generalizing Loop-Invariant Code Motion in a Real-World Compiler
Imperial College London Department of Computing Generalizing loop-invariant code motion in a real-world compiler Author: Supervisor: Paul Colea Fabio Luporini Co-supervisor: Prof. Paul H. J. Kelly MEng Computing Individual Project June 2015 Abstract Motivated by the perpetual goal of automatically generating efficient code from high-level programming abstractions, compiler optimization has developed into an area of intense research. Apart from general-purpose transformations which are applicable to all or most programs, many highly domain-specific optimizations have also been developed. In this project, we extend such a domain-specific compiler optimization, initially described and implemented in the context of finite element analysis, to one that is suitable for arbitrary applications. Our optimization is a generalization of loop-invariant code motion, a technique which moves invariant statements out of program loops. The novelty of the transformation is due to its ability to avoid more redundant recomputation than normal code motion, at the cost of additional storage space. This project provides a theoretical description of the above technique which is fit for general programs, together with an implementation in LLVM, one of the most successful open-source compiler frameworks. We introduce a simple heuristic-driven profitability model which manages to successfully safeguard against potential performance regressions, at the cost of missing some speedup opportunities. We evaluate the functional correctness of our implementation using the comprehensive LLVM test suite, passing all of its 497 whole program tests. The results of our performance evaluation using the same set of tests reveal that generalized code motion is applicable to many programs, but that consistent performance gains depend on an accurate cost model. -

Loop Transformations and Parallelization
Loop transformations and parallelization Claude Tadonki LAL/CNRS/IN2P3 University of Paris-Sud [email protected] December 2010 Claude Tadonki Loop transformations and parallelization C. Tadonki – Loop transformations Introduction Most of the time, the most time consuming part of a program is on loops. Thus, loops optimization is critical in high performance computing. Depending on the target architecture, the goal of loops transformations are: improve data reuse and data locality efficient use of memory hierarchy reducing overheads associated with executing loops instructions pipeline maximize parallelism Loop transformations can be performed at different levels by the programmer, the compiler, or specialized tools. At high level, some well known transformations are commonly considered: loop interchange loop (node) splitting loop unswitching loop reversal loop fusion loop inversion loop skewing loop fission loop vectorization loop blocking loop unrolling loop parallelization Claude Tadonki Loop transformations and parallelization C. Tadonki – Loop transformations Dependence analysis Extract and analyze the dependencies of a computation from its polyhedral model is a fundamental step toward loop optimization or scheduling. Definition For a given variable V and given indexes I1, I2, if the computation of X(I1) requires the value of X(I2), then I1 ¡ I2 is called a dependence vector for variable V . Drawing all the dependence vectors within the computation polytope yields the so-called dependencies diagram. Example The dependence vectors are (1; 0); (0; 1); (¡1; 1). Claude Tadonki Loop transformations and parallelization C. Tadonki – Loop transformations Scheduling Definition The computation on the entire domain of a given loop can be performed following any valid schedule.A timing function tV for variable V yields a valid schedule if and only if t(x) > t(x ¡ d); 8d 2 DV ; (1) where DV is the set of all dependence vectors for variable V . -

Foundations of Scientific Research
2012 FOUNDATIONS OF SCIENTIFIC RESEARCH N. M. Glazunov National Aviation University 25.11.2012 CONTENTS Preface………………………………………………….…………………….….…3 Introduction……………………………………………….…..........................……4 1. General notions about scientific research (SR)……………….……….....……..6 1.1. Scientific method……………………………….………..……..……9 1.2. Basic research…………………………………………...……….…10 1.3. Information supply of scientific research……………..….………..12 2. Ontologies and upper ontologies……………………………….…..…….…….16 2.1. Concepts of Foundations of Research Activities 2.2. Ontology components 2.3. Ontology for the visualization of a lecture 3. Ontologies of object domains………………………………..………………..19 3.1. Elements of the ontology of spaces and symmetries 3.1.1. Concepts of electrodynamics and classical gauge theory 4. Examples of Research Activity………………….……………………………….21 4.1. Scientific activity in arithmetics, informatics and discrete mathematics 4.2. Algebra of logic and functions of the algebra of logic 4.3. Function of the algebra of logic 5. Some Notions of the Theory of Finite and Discrete Sets…………………………25 6. Algebraic Operations and Algebraic Structures……………………….………….26 7. Elements of the Theory of Graphs and Nets…………………………… 42 8. Scientific activity on the example “Information and its investigation”……….55 9. Scientific research in Artificial Intelligence……………………………………..59 10. Compilers and compilation…………………….......................................……69 11. Objective, Concepts and History of Computer security…….………………..93 12. Methodological and categorical apparatus of scientific research……………114 13. Methodology and methods of scientific research…………………………….116 13.1. Methods of theoretical level of research 13.1.1. Induction 13.1.2. Deduction 13.2. Methods of empirical level of research 14. Scientific idea and significance of scientific research………………………..119 15. Forms of scientific knowledge organization and principles of SR………….121 1 15.1. Forms of scientific knowledge 15.2. -

Compiler Optimizations
Compiler Optimizations CS 498: Compiler Optimizations Fall 2006 University of Illinois at Urbana-Champaign A note about the name of optimization • It is a misnomer since there is no guarantee of optimality. • We could call the operation code improvement, but this is not quite true either since compiler transformations are not guaranteed to improve the performance of the generated code. Outline Assignment Statement Optimizations Loop Body Optimizations Procedure Optimizations Register allocation Instruction Scheduling Control Flow Optimizations Cache Optimizations Vectorization and Parallelization Advanced Compiler Design Implementation. Steven S. Muchnick, Morgan and Kaufmann Publishers, 1997. Chapters 12 - 19 Historical origins of compiler optimization "It was our belief that if FORTRAN, during its first months, were to translate any reasonable "scientific" source program into an object program only half as fast as its hand coded counterpart, then acceptance of our system would be in serious danger. This belief caused us to regard the design of the translator as the real challenge, not the simple task of designing the language."... "To this day I believe that our emphasis on object program efficiency rather than on language design was basically correct. I believe that has we failed to produce efficient programs, the widespread use of language like FORTRAN would have been seriously delayed. John Backus FORTRAN I, II, and III Annals of the History of Computing Vol. 1, No 1, July 1979 Compilers are complex systems “Like most of the early hardware and software systems, Fortran was late in delivery, and didn’t really work when it was delivered. At first people thought it would never be done. -

Compiler Construction
Compiler construction PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 10 Dec 2011 02:23:02 UTC Contents Articles Introduction 1 Compiler construction 1 Compiler 2 Interpreter 10 History of compiler writing 14 Lexical analysis 22 Lexical analysis 22 Regular expression 26 Regular expression examples 37 Finite-state machine 41 Preprocessor 51 Syntactic analysis 54 Parsing 54 Lookahead 58 Symbol table 61 Abstract syntax 63 Abstract syntax tree 64 Context-free grammar 65 Terminal and nonterminal symbols 77 Left recursion 79 Backus–Naur Form 83 Extended Backus–Naur Form 86 TBNF 91 Top-down parsing 91 Recursive descent parser 93 Tail recursive parser 98 Parsing expression grammar 100 LL parser 106 LR parser 114 Parsing table 123 Simple LR parser 125 Canonical LR parser 127 GLR parser 129 LALR parser 130 Recursive ascent parser 133 Parser combinator 140 Bottom-up parsing 143 Chomsky normal form 148 CYK algorithm 150 Simple precedence grammar 153 Simple precedence parser 154 Operator-precedence grammar 156 Operator-precedence parser 159 Shunting-yard algorithm 163 Chart parser 173 Earley parser 174 The lexer hack 178 Scannerless parsing 180 Semantic analysis 182 Attribute grammar 182 L-attributed grammar 184 LR-attributed grammar 185 S-attributed grammar 185 ECLR-attributed grammar 186 Intermediate language 186 Control flow graph 188 Basic block 190 Call graph 192 Data-flow analysis 195 Use-define chain 201 Live variable analysis 204 Reaching definition 206 Three address -

Study Topics Test 3
Printed by David Whalley Apr 22, 20 9:44 studytopics_test3.txt Page 1/2 Apr 22, 20 9:44 studytopics_test3.txt Page 2/2 Topics to Study for Exam 3 register allocation array padding scalar replacement Chapter 6 loop interchange prefetching intermediate code representations control flow optimizations static versus dynamic type checking branch chaining equivalence of type expressions reversing branches coercions, overloading, and polymorphism code positioning translation of boolean expressions loop inversion backpatching and translation of flow−of−control constructs useless jump elimination translation of record declarations unreachable code elimination translation of switch statements data flow optimizations translation of array references common subexpression elimination partial redundancy elimination dead assignment elimination Chapter 5 evaluation order determination recurrence elimination syntax directed definitions machine specific optimizations synthesized and inherited attributes instruction scheduling dependency graphs filling delay slots L−attributed definitions exploiting instruction−level parallelism translation schemes peephole optimization syntax−directed construction of syntax trees and DAGs constructing a control flow graph syntax−directed translation with YACC optimizations before and after code generation instruction selection optimization Chapter 7 Chapter 10 activation records call graphs instruction pipelining typical actions during calls and returns data dependences storage allocation strategies true dependences static, -

Translation Validation of Optimizing Compilers
Translation Validation of Optimizing Compilers by Yi Fang A dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy Department of Computer Science Courant Institute of Mathematical Sciences New York University December, 2005 Advisor: Amir Pnueli Abstract There is a growing awareness, both in industry and academia, of the crucial role of formally verifying the translation from high-level source-code into low- level object code that is typically performed by an optimizing compiler. Formally verifying an optimizing compiler, as one would verify any other large program, is not feasible due to its size, ongoing evolution and modification, and possibly, proprietary considerations. Translation validation is a novel approach that offers an alternative to the verification of translator in general and compilers in partic- ular: Rather than verifying the compiler itself, one constructs a validation tool which, after every run of the compiler, formally confirms that the target code pro- duced in the run is a correct translation of the source program. This thesis work takes an important step towards ensuring an extremely high level of confidence in compilers targeted at EPIC architectures. The dissertation focuses on the translation validation of structure-preserving optimizations, i.e., transformations that do not modify programs’ structure in a major way, which include most of the global optimizations performed by compil- ers. The first part of the dissertation develops the theory of a correct translation, which provides a precise definition of the notion of a target program being a cor- rect translation of a source program, and the method that formally establishes the correctness of structure preserving transformations based on computational induc- tion. -

Denotational Translation Validation
Denotational Translation Validation The Harvard community has made this article openly available. Please share how this access benefits you. Your story matters Citation Govereau, Paul. 2012. Denotational Translation Validation. Doctoral dissertation, Harvard University. Citable link http://nrs.harvard.edu/urn-3:HUL.InstRepos:10121982 Terms of Use This article was downloaded from Harvard University’s DASH repository, and is made available under the terms and conditions applicable to Other Posted Material, as set forth at http:// nrs.harvard.edu/urn-3:HUL.InstRepos:dash.current.terms-of- use#LAA c 2012 - Paul Govereau All rights reserved. Thesis advisor Author Greg Morrisett Paul Govereau Denotational Translation Validation Abstract In this dissertation we present a simple and scalable system for validating the correctness of low-level program transformations. Proving that program transfor- mations are correct is crucial to the development of security critical software tools. We achieve a simple and scalable design by compiling sequential low-level programs to synchronous data-flow programs. Theses data-flow programs are a denotation of the original programs, representing all of the relevant aspects of the program se- mantics. We then check that the two denotations are equivalent, which implies that the program transformation is semantics preserving. Our denotations are computed by means of symbolic analysis. In order to achieve our design, we have extended symbolic analysis to arbitrary control-flow graphs. To this end, we have designed an intermediate language called Synchronous Value Graphs (SVG), which is capable of representing our denotations for arbitrary control-flow graphs, we have built an algorithm for computing SVG from normal assembly language, and we have given a formal model of SVG which allows us to simplify and compare denotations. -

The Need for Large Register Files in Integer Codes
1 The Need for Large Register Files in Integer Codes Matthew Postiff, David Greene, and Trevor Mudge {postiffm,greened,tnm}@eecs.umich.edu EECS Department, University of Michigan 1301 Beal Ave., Ann Arbor, MI 48109-2122 Abstract Register allocation is an important optimization for high performance microprocessors but there is no consensus in the architecture or compiler communities as to the best num- ber of registers to provide in an instruction set architecture. This paper discusses reasons why this situation has occurred and shows from a compiler perspective that, compared to the conventional 32-register file, 64 or more registers enables performance improvements from 5% to 20%. This is demonstrated with existing advanced compiler optimizations on the SPECint95 and SPEC2000 benchmarks. This work also documents that the optimiza- tions eliminate cache hit operations, converting common-case cache hits to faster register accesses. Finally, this work provides additional measurements for the proper number of registers in a high-performance instruction set and shows that most programs can easily use 100 to 200 registers when multiple active functions are considered for simultaneous allocation to the register file. 1. Introduction Large register files have many advantages. If used effectively they can: 1) reduce memory traffic by removing load and store operations; 2) improve performance by decreasing path length; and 3) decrease power consumption by eliminating operations to the memory hierarchy. Their merit derives from the fact that they require few address bits and act as a very high-speed cache. On the other hand, large, multi-ported register files can become the critical path that sets the cycle time of the processor. -
Loop Optimizations
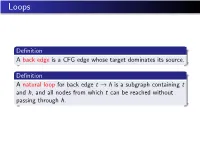
Loops Definition A back edge is a CFG edge whose target dominates its source. Definition A natural loop for back edge t ! h is a subgraph containing t and h, and all nodes from which t can be reached without passing through h. Example Loops Definition The loop for a header h is the union of all natural loops for back edges whose target is h. Property Two loops with different headers h1 6= h2 are either disjoint (loop(h1) \ loop(h2) = fg), or nested within each other (loop(h1) ⊂ loop(h2)). Loops Definition A subgraph of a graph is strongly connected if there is a path in the subgraph from every node to every other node. Property Every loop is a strongly connected subgraph. (Why?) Definition A CFG is reducible if every strongly connected subgraph contains a unique node (the header) that dominates all nodes in the subgraph. Example Is f2; 3g a strongly connected subgraph? Is f2; 3g a loop? Example Is f2; 3g a strongly connected subgraph? Is f2; 3g a loop? Definition A CFG is reducible if every strongly connected subgraph contains a unique node (the header) that dominates all nodes in the subgraph. Loop-invariant computations Definition A definition c = a op b is loop-invariant if a and b 1 are constant, 2 have all their reaching definitions outside the loop, OR 3 have only one reaching definition (why?) which is loop-invariant. Loop-invariant code motion read i; x = 1; y = 2; t = 2; while(i<10) { t = y - x; i = i + t; } print t; Loop-invariant code motion read i; x = 1; y = 2; t = 2; t = y - x; while(i<10) { i = i + t; } print t; Loop-invariant code motion It is safe to move a computation ` : c = a op b to just before the header of the loop if 1 it is loop-invariant, 2 it has no side-effects, 3 c is not live immediately before the loop header, 4 ` is the only definition of c in the loop, and 5 ` dominates all exits from the loop at which c is live. -

CS6013 - Modern Compilers: Theory and Practise Overview of Different Optimizations
Optimizing compilers CS6013 - Modern Compilers: Theory and Practise Overview of different optimizations V. Krishna Nandivada Copyright c 2020 by Antony L. Hosking. Permission to make digital or hard copies of part or all of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that IIT Madras copies bear this notice and full citation on the first page. To copy otherwise, to republish, to post on servers, or to redistribute to lists, requires prior specific permission and/or fee. Request permission to publish from [email protected]. * V.Krishna Nandivada (IIT Madras) CS6013 - Jan 2020 2 / 1 Compiler structure Optimization token stream Potential optimizations: Source-language (AST): Parser constant bounds in syntax tree loops/arrays loop unrolling Goal: produce fast code Semantic analysis (eg, type checking) suppressing run-time What is optimality? checks syntax tree enable later optimisations Problems are often hard Many are intractable or even undecideable Intermediate IR: local and global code generator CSE elimination Many are NP-complete low−level IR live variable analysis Which optimizations should be used? (eg, canonical trees/tuples) code hoisting Many optimizations overlap or interact Optimizer enable later optimisations low−level IR Code-generation (machine (eg, canonical trees/tuples) code): Machine code register allocation generator instruction scheduling machine code peephole optimization * * V.Krishna Nandivada (IIT Madras) CS6013 -

Program Analysis and Compilation Techniques for Speeding up Transactional Database Workloads
Program Analysis and Compilation Techniques for Speeding up Transactional Database Workloads THÈSE NO 8023 (2017) PRÉSENTÉE LE 13 OCTOBRE 2017 À LA FACULTÉ INFORMATIQUE ET COMMUNICATIONS LABORATOIRE DE THÉORIE ET APPLICATIONS D'ANALYSE DE DONNÉES PROGRAMME DOCTORAL EN INFORMATIQUE ET COMMUNICATIONS ÉCOLE POLYTECHNIQUE FÉDÉRALE DE LAUSANNE POUR L'OBTENTION DU GRADE DE DOCTEUR ÈS SCIENCES PAR Mohammad DASHTI RAHMAT ABADI acceptée sur proposition du jury: Prof. E. Bugnion, président du jury Prof. C. Koch, directeur de thèse Dr Ph. A. Bernstein, rapporteur Prof. A. Pavlo, rapporteur Prof. A. Ailamaki, rapporteuse Suisse 2017 I have seen flowers come in stony places And kind things done by men with ugly faces And the gold cup won by the worst horse at the races, So I trust, too. — John Masefield To my beloved wife, Faeze, and to my dear son, Daniel. Acknowledgements I would like to express my special appreciation and thanks to my advisor, Prof. Christoph Koch. He has taught me, both consciously and unconsciously, how good (database) research is done. I would like to thank him for encouraging my research and for allowing me to grow as a research scientist. I appreciate all his contributions of time, ideas, and funding to make my Ph.D. experience productive and stimulating. Christoph taught me how to distinguish between incremental and fundamental advances in science, to think big and to aim for the biggest targets. I am also thankful to him that he almost always pulled an all-nighter with us before a deadline. I would like to thank Dr. Phil Bernstein, my advisor at Microsoft Research, where I interned during summer 2016.