Srvstart.Exe You Will See Output Similar to the Following
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
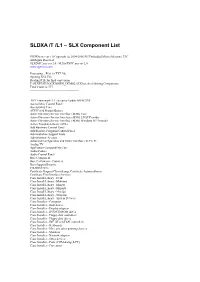
SLDXA /T /L1 – SLX Component List
SLDXA /T /L1 – SLX Component List SLDXA.exe ver 1.0 Copyright (c) 2004-2006 SJJ Embedded Micro Solutions, LLC All Rights Reserved SLXDiffC.exe ver 2.0 / SLXtoTXTC.exe ver 2.0 www.sjjmicro.com Processing... File1 to TXT file. Opening XSL File Reading RTF for final conversion F:\SLXTEST\LOCKDOWN_DEMO2.SLX has the following Components Total Count is: 577 -------------------------------------------------- .NET Framework 1.1 - Security Update KB887998 Accessibility Control Panel Accessibility Core ACPI Fixed Feature Button Active Directory Service Interface (ADSI) Core Active Directory Service Interface (ADSI) LDAP Provider Active Directory Service Interface (ADSI) Windows NT Provider Active Template Library (ATL) Add Hardware Control Panel Add/Remove Programs Control Panel Administration Support Tools Administrator Account Advanced Configuration and Power Interface (ACPI) PC Analog TV Application Compatibility Core Audio Codecs Audio Control Panel Base Component Base Performance Counters Base Support Binaries CD-ROM Drive Certificate Request Client & Certificate Autoenrollment Certificate User Interface Services Class Install Library - Desk Class Install Library - Mdminst Class Install Library - Mmsys Class Install Library - Msports Class Install Library - Netcfgx Class Install Library - Storprop Class Install Library - System Devices Class Installer - Computer Class Installer - Disk drives Class Installer - Display adapters Class Installer - DVD/CD-ROM drives Class Installer - Floppy disk controllers Class Installer - Floppy disk drives -
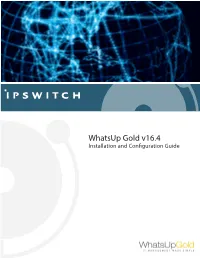
Installing and Configuring Whatsup Gold V16.3
WhatsUp Gold v16.4 Installation and Conguration Guide Contents Installing and Configuring WhatsUp Gold using WhatsUp Setup Installation Overview ........................................................................................................................................................... 1 Overview ...................................................................................................................................................................... 1 Security considerations ......................................................................................................................................... 2 Standard WhatsUp Gold Installation ............................................................................................................................ 2 Distributed Installation ....................................................................................................................................................... 4 Installing WhatsUp Gold - Distributed (Central Site) ............................................................................... 4 Installing WhatsUp Gold - Distributed (Remote Site) .............................................................................. 6 Failover Installation .............................................................................................................................................................. 7 Installing WhatsUp Gold - Failover (Secondary Site) .............................................................................. -
Identity Provisioning to Masaryk University IT Services Based on Microsoft Environment
Masaryk University Faculty of Informatics Identity provisioning to Masaryk University IT services based on Microsoft environment Master’s Thesis Bc. David Štencel Brno, Spring 2019 Masaryk University Faculty of Informatics Identity provisioning to Masaryk University IT services based on Microsoft environment Master’s Thesis Bc. David Štencel Brno, Spring 2019 This is where a copy of the official signed thesis assignment and a copy ofthe Statement of an Author is located in the printed version of the document. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out on my own. All sources, references, and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Bc. David Štencel Advisor: Mgr. Kamil Malinka, Ph.D. i Acknowledgements I would like to thank my advisor Mgr. Kamil Malinka, Ph.D. for his professional guidance and experience. Also, I would like to thank Jan Izydorczyk, Mgr. Slávek Licehammer, and the rest of the Office 365 team at ICS for their collaboration, support, and patience during the creation of this master’s thesis. Finally, I would like to thank my family for all their support during my whole studies. iii Abstract The aim of the thesis is to design and implement an interconnection of university identity management system Perun with services run- ning in Microsoft environment. Resultant PowerShell scripts utilizing OpenSSH and PowerShell remoting allow data transmission from Perun to Windows hosts and launching service provisioning scripts. The thesis covers Active Directory and Office 365 as example target services, and a revised PowerShell web proxy that adjusts additional object settings within university Office 365. -

(RUNTIME) a Salud Total
Windows 7 Developer Guide Published October 2008 For more information, press only: Rapid Response Team Waggener Edstrom Worldwide (503) 443-7070 [email protected] Downloaded from www.WillyDev.NET The information contained in this document represents the current view of Microsoft Corp. on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This guide is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, IN THIS SUMMARY. Complying with all applicable copyright laws is the responsibility of the user. Without limiting the rights under copyright, no part of this document may be reproduced, stored in or introduced into a retrieval system, or transmitted in any form, by any means (electronic, mechanical, photocopying, recording or otherwise), or for any purpose, without the express written permission of Microsoft. Microsoft may have patents, patent applications, trademarks, copyrights or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. Unless otherwise noted, the example companies, organizations, products, domain names, e-mail addresses, logos, people, places and events depicted herein are fictitious, and no association with any real company, organization, product, domain name, e-mail address, logo, person, place or event is intended or should be inferred. -

Installation Instructions for Version 8 (TS M0) of the SAS System For
Installation Instructions for Release 8.1 (TS1M0) of the SAS® System for Microsoft® Windows® Table of Contents Chapter 1, Introduction.......................................................................................................... 1 Terminology and Symbols Used in this Document ................................................................... 1 SASROOT Directory .................................................................................................. 1 Types of Installation Configurations........................................................................... 1 Pre-installation Checklist........................................................................................................... 2 Proper Handling of Your Media................................................................................................ 3 SAS Setup Help for Installing the SAS System......................................................................... 3 Online Help for Using the SAS System..................................................................................... 3 The Help System......................................................................................................... 4 HTML Viewer............................................................................................................. 4 Exiting SAS Setup..................................................................................................................... 4 Additional Documentation ........................................................................................................4 -
An Introduction to Windows Operating System
EINAR KROGH AN INTRODUCTION TO WINDOWS OPERATING SYSTEM Download free eBooks at bookboon.com 2 An Introduction to Windows Operating System 2nd edition © 2017 Einar Krogh & bookboon.com ISBN 978-87-403-1935-4 Peer review by Høgskolelektor Lars Vidar Magnusson, Høgskolen i Østfold Download free eBooks at bookboon.com 3 AN INTRODUCTION TO WINDOWS OPERATING SYSTEM CONTENTS CONTENTS Introduction 9 1 About Windows history 10 1.1 MS-DOS 10 1.2 The first versions of Windows 11 1.3 Windows NT 12 1.4 Windows versions based on Windows NT 13 1.5 Windows Server 15 1.6 Control Questions 17 2 The tasks of an operating system 18 2.1 About the construction of computers 19 2.2 Central tasks for an operating system 20 2.3 Control Questions 22 �e Graduate Programme I joined MITAS because for Engineers and Geoscientists I wanted real responsibili� www.discovermitas.comMaersk.com/Mitas �e Graduate Programme I joined MITAS because for Engineers and Geoscientists I wanted real responsibili� Maersk.com/Mitas Month 16 I wwasas a construction Month 16 supervisorI wwasas in a construction the North Sea supervisor in advising and the North Sea Real work helpinghe foremen advising and IInternationalnternationaal opportunities ��reeree wworkoro placements solves Real work problems helpinghe foremen IInternationalnternationaal opportunities ��reeree wworkoro placements solves problems Download free eBooks at bookboon.com Click on the ad to read more 4 AN INTRODUCTION TO WINDOWS OPERATING SYSTEM CONTENTS 3 Some concepts and terms of the Windows operating system 23 3.1 -
Smartconnector Configuration Guide for Microsoft Windows Event Log – Unified, Selecting Microsoft Windows Event Log – Unified As the Connector to Be Configured
Micro Focus Security ArcSight Connectors SmartConnector for Windows Event Log – Unified: Microsoft Service Control Manager Supplemental Configuration Guide August 30, 2018 Supplemental Configuration Guide SmartConnector for Windows Event Log – Unified: Microsoft Service Control Manager August 30, 2018 Copyright © 2010 – 2018 Micro Focus and its affiliates and licensors. Warranty The only warranties for products and services of Micro Focus and its affiliates and licensors (“Micro Focus”) are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. Micro Focus shall not be liable for technical or editorial errors or omissions contained herein. The information contained herein is subject to change without notice. Restricted Rights Legend Confidential computer software. Except as specifically indicated otherwise, a valid license from Micro Focus is required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor's standard commercial license. Trademark Notices Adobe™ is a trademark of Adobe Systems Incorporated. Microsoft® and Windows® are U.S. registered trademarks of Microsoft Corporation. UNIX® is a registered trademark of The Open Group. Revision History Date Description 05/15/2013 Updated mappings for event 7045. 03/29/2013 First edition of this guide. Configuration Guide -

Running a Script Without User Intervention 7
,ch02.2190 Page 6 Thursday, April 8, 2004 11:55 AM 2 Chapter 2 Running a Script Without User Intervention 2. We have indicated that scripts can be used to save huge amounts of time by carry- ing out mundane maintenance and configuration tasks automatically. However, it should be pointed out that no matter how sophisticated a script may be, it is never anything more than a text file containing words and symbols that can be under- stood by an interpreter. It is completely powerless to carry out any activities on a workstation unless explicitly executed. If you happen to be sitting in front of a workstation, running a script is trivial: it usually involves typing its name at the command prompt. While it might sound rather painless on the face of it, this inter- active method of running a script is completely impractical if you are attempting to look after a large number of workstations. The reason is simple: visiting each workstation in turn is the time-consuming activity. Unless the maintenance or con- figuration you intend to carry out is extremely complicated, it is likely to take very little additional effort to carry out the task manually. Unfortunately, there is no easy way to start a script remotely short of running a Telnet server on every workstation under your control (and there are many good reasons not to do this). Thankfully, however, there are ways of preinstalling scripts so that they run themselves either at predetermined times or in response to a workstation state. The significance of this is that a maintenance script designed to run regularly has to be installed only once and will require no further interven- tion; a configuration script can be preinstalled and primed so that it will start up by itself when required. -

Windows System Error Codes and What They Mean
Windows system error codes and what they mean This information was gathered from: https://msdn.microsoft.com/en-us/library/windows/desktop/ ms681382(v=vs.85).aspx You can find additional error codes and messages in the above website. Code Description: 0 The operation completed successfully. 1 Incorrect function. 2 The system cannot find the file specified. 3 The system cannot find the path specified. 4 The system cannot open the file. 5 Access is denied. 6 The handle is invalid. 7 The storage control blocks were destroyed. 8 Not enough storage is available to process this command. 9 The storage control block address is invalid. 10 The environment is incorrect. 11 An attempt was made to load a program with an incorrect format. 12 The access code is invalid. 13 The data is invalid. 14 Not enough storage is available to complete this operation. 15 The system cannot find the drive specified. 16 The directory cannot be removed. 17 The system cannot move the file to a different disk drive. 18 There are no more files. 19 The media is write protected. 20 The system cannot find the device specified. 21 The device is not ready. 22 The device does not recognize the command. 23 Data error (cyclic redundancy check). 24 The program issued a command but the command length is incorrect. 25 The drive cannot locate a specific area or track on the disk. 26 The specified disk or diskette cannot be accessed. 27 The drive cannot find the sector requested. 28 The printer is out of paper. -

This Article Is the Second Part of a Three Part Series
12/31/2020 Windows Administration: Inside the Windows Vista Kernel: Part 2 | Microsoft Docs 09/08/2016 • 23 minutes to read This article is the second part of a three part series. Click here to read Part One. Click here to read Part Three. Windows Administration Inside the Windows Vista Kernel: Part 2 Mark Russinovich At a Glance: Memory management Startup and shutdown Power management Last month, in the first installment of this three-part series, I looked at Windows Vista kernel enhancements in the areas of processes and I/O. This time I'll cover advances in the way Windows Vista manages memory, as well as major improvements to system startup, shutdown, and power management (Part One). Every release of Windows® improves scalability and performance, and Windows Vista™ is no different. The Windows Vista Memory Manager includes numerous enhancements, like more extensive use of lock-free synchronization techniques, finer-grained locking, tighter data-structure packing, larger paging I/Os, support for modern GPU memory architectures, and more efficient use of the hardware Translation Lookaside Buffer. Plus, Windows Vista memory management now offers dynamic address space allocation for the requirements of different workloads. Four performance-enhancing features that use new technologies make their operating system debut on Windows Vista: SuperFetch, ReadyBoost, ReadyBoot, and ReadyDrive. I'll discuss them in detail later in this article. Dynamic Kernel Address Space https://docs.microsoft.com/en-us/previous-versions/technet-magazine/cc162480(v=msdn.10) 1/15 12/31/2020 Windows Administration: Inside the Windows Vista Kernel: Part 2 | Microsoft Docs Windows and the applications that run on it have bumped their heads on the address space limits of 32-bit processors. -

Windows Services – All Roads Lead to SYSTEM
Windows Services – All roads lead to SYSTEM Kostas Lintovois 30th September 2016 mwrinfosecurity.com | © MWR InfoSecurity 2 Contents 1. Introduction ..................................................................................... 4 1.1 Windows Service Accounts ............................................................................... 5 2. Auditing Windows Services .................................................................... 6 2.1 Insecure File System Permissions ....................................................................... 6 2.2 Insecure Registry Permissions ........................................................................... 8 2.3 Insecure Named Pipes Permissions ................................................................... 10 2.4 Insecure Service Permissions .......................................................................... 12 2.5 Missing DLLs .............................................................................................. 15 2.6 Unquoted Service Binary Paths ........................................................................ 17 3. Service Exploitation ........................................................................... 19 4. Scripted Assessment ........................................................................... 21 5. Summary ........................................................................................ 22 6. References ...................................................................................... 23 mwrinfosecurity.com | © MWR InfoSecurity -
File Management
roma tre university maurizio pizzonia windows 1 © 2011 maurizio pizzonia – operating systems – roma tre university, italy Microsoft Press Server 2008 andWindows Vista 5 Windows® Internals: IncludingWindows M. Russinovich, D.A.Solomon references th ed. 2 © 2011 maurizio pizzonia – operating systems – roma tre university, italy • • • • several “system processes” several support access syscalls never services directly and applications user ismode graphics in kernel word overloaded kernel: – – use “subsystems DLLs” that goes with “environment subsystems” “environment “subsystemsuse thatwith DLLs” goes mode inkernel to runs MS according of it part what a is only architecture overview 3 3 © 2011 maurizio pizzonia – operating systems – roma tre university, italy • • • • needs besides, usesWindows kernel threads for its own that so... tree is only informative, Windows does not rely on if the parent dies the info is not updated in the child processes “usually” form a tree – – the parent is the creator of the process parent information is not reliable windows processes 4 4 © 2011 maurizio pizzonia – operating systems – roma tre university, italy architecture details: user mode 5 © 2011 maurizio pizzonia – operating systems – roma tre university, italy • • • syscalls are never directly performed by by syscalls performed processes are directly never are subsystems really subsystemsare needed? really os/2posix, subystems: windows, – – – – – syscalls are not documented not are syscalls my impression is that subsystems are a “legacy” feature “legacy” a are subsystems isthat impression my process supporting + DLLs are OS from underlying processes user decouple layers decoupling • • • • • relationships with Windows update a“localupdate state” subsystemDLLs maycall supporting Ntdll.dll,just process or interactwith supportingprocess:see “environment subsystem” software ofunix porting “easy” allows e.g.