Automate Your SAS Code Execution on UNIX and Windows Platforms Niraj J
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Administering Unidata on UNIX Platforms
C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta UniData Administering UniData on UNIX Platforms UDT-720-ADMU-1 C:\Program Files\Adobe\FrameMaker8\UniData 7.2\7.2rebranded\ADMINUNIX\ADMINUNIXTITLE.fm March 5, 2010 1:34 pm Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Beta Notices Edition Publication date: July, 2008 Book number: UDT-720-ADMU-1 Product version: UniData 7.2 Copyright © Rocket Software, Inc. 1988-2010. All Rights Reserved. Trademarks The following trademarks appear in this publication: Trademark Trademark Owner Rocket Software™ Rocket Software, Inc. Dynamic Connect® Rocket Software, Inc. RedBack® Rocket Software, Inc. SystemBuilder™ Rocket Software, Inc. UniData® Rocket Software, Inc. UniVerse™ Rocket Software, Inc. U2™ Rocket Software, Inc. U2.NET™ Rocket Software, Inc. U2 Web Development Environment™ Rocket Software, Inc. wIntegrate® Rocket Software, Inc. Microsoft® .NET Microsoft Corporation Microsoft® Office Excel®, Outlook®, Word Microsoft Corporation Windows® Microsoft Corporation Windows® 7 Microsoft Corporation Windows Vista® Microsoft Corporation Java™ and all Java-based trademarks and logos Sun Microsystems, Inc. UNIX® X/Open Company Limited ii SB/XA Getting Started The above trademarks are property of the specified companies in the United States, other countries, or both. All other products or services mentioned in this document may be covered by the trademarks, service marks, or product names as designated by the companies who own or market them. License agreement This software and the associated documentation are proprietary and confidential to Rocket Software, Inc., are furnished under license, and may be used and copied only in accordance with the terms of such license and with the inclusion of the copyright notice. -

Semi-Automated Parallel Programming in Heterogeneous Intelligent Reconfigurable Environments (SAPPHIRE) Sean Stanek Iowa State University
Iowa State University Capstones, Theses and Graduate Theses and Dissertations Dissertations 2012 Semi-automated parallel programming in heterogeneous intelligent reconfigurable environments (SAPPHIRE) Sean Stanek Iowa State University Follow this and additional works at: https://lib.dr.iastate.edu/etd Part of the Computer Sciences Commons Recommended Citation Stanek, Sean, "Semi-automated parallel programming in heterogeneous intelligent reconfigurable environments (SAPPHIRE)" (2012). Graduate Theses and Dissertations. 12560. https://lib.dr.iastate.edu/etd/12560 This Dissertation is brought to you for free and open access by the Iowa State University Capstones, Theses and Dissertations at Iowa State University Digital Repository. It has been accepted for inclusion in Graduate Theses and Dissertations by an authorized administrator of Iowa State University Digital Repository. For more information, please contact [email protected]. Semi-automated parallel programming in heterogeneous intelligent reconfigurable environments (SAPPHIRE) by Sean Stanek A dissertation submitted to the graduate faculty in partial fulfillment of the requirements for the degree of DOCTOR OF PHILOSOPHY Major: Computer Science Program of Study Committee: Carl Chang, Major Professor Johnny Wong Wallapak Tavanapong Les Miller Morris Chang Iowa State University Ames, Iowa 2012 Copyright © Sean Stanek, 2012. All rights reserved. ii TABLE OF CONTENTS LIST OF TABLES ..................................................................................................................... -
Geek Guide > Beyond Cron
GEEK GUIDE BEYOND CRON Table of Contents Ease of Use ..................................................................... 8 Multi-Server-Friendly .................................................... 10 Dependency Management ............................................ 13 Easy to Visualize ........................................................... 16 Delegation of Authority ................................................. 18 Management by Exception ........................................... 21 Flexible Scheduling ....................................................... 23 Revision Control ........................................................... 24 Conclusion .................................................................... 24 MIKE DIEHL has been using Linux since the days when Slackware came on 14 5.25” floppy disks and installed kernel version 0.83. He has built and managed several servers configured with either hardware or software RAID storage under Linux, and he has hands-on experience with both the VMware and KVM virtual machine architectures. Mike has written numerous articles for Linux Journal on a broad range of subjects, and he has a Bachelor’s degree in Mathematics with a minor in Computer Science. He lives in Blythewood, South Carolina, with his wife and four sons. 2 GEEK GUIDE BEYOND CRON GEEK GUIDES: Mission-critical information for the most technical people on the planet. Copyright Statement © 2015 Linux Journal. All rights reserved. This site/publication contains materials that have been created, developed or -
Introduction to Cron - Goals
Introduction to cron - Goals • Goals: – Understand how cron works – Understand crontab files – Understand our conventions 1 What is cron? • cron is a Unix daemon program • cron automatically runs programs at given times • cron is different from at, which is a queued batch job facility • We are moving to use cron for batch jobs, as opposed to at 2 Crontab files (Part 1) • Each user on each machine has a crontab file. • So, ecogdev has its own file on each of sid & soltrane, as does ecogdba. • This file consists of lines that look like this: 15 03 * * * /ecog/ecogdev/src/reports/timezone/timezoneauto 15 03 * * 0 /ecog/ecogdev/src/reports/swog_prots/swog_protsauto 30 0 * * * /ecog/ecogdev/bin/ftpschema 3 Crontab Files (Part 2) • Here is one line from a crontab file: 30 0 * * * /ecog/ecogdev/bin/ftpschema • Six fields on this line (* is a wildcard): – 1. Minute of the hour (0-59) – 2. Hour of the day (0-23) – 3. Day of the month (0-31) – 4. Month of the year (1-12) – 5. Day of the week (0-6 with 0=Sunday) – 6. Command line • Quiz: When does this job run? 4 Crontab Files (Part 3) • Here is that crontab line again: 30 0 * * * /ecog/ecogdev/bin/ftpschema • The rightmost field is the command line • Best to use absolute paths, as in this entry • Commands can be executable programs or shell scripts • Put #!/bin/csh at top of C Shell scripts 5 The crontab command • The crontab command allows you to install and edit per-user crontab files. • These are the installed crontab files. -

Unix (And Linux)
AWK....................................................................................................................................4 BC .....................................................................................................................................11 CHGRP .............................................................................................................................16 CHMOD.............................................................................................................................19 CHOWN ............................................................................................................................26 CP .....................................................................................................................................29 CRON................................................................................................................................34 CSH...................................................................................................................................36 CUT...................................................................................................................................71 DATE ................................................................................................................................75 DF .....................................................................................................................................79 DIFF ..................................................................................................................................84 -

Solaris Crontab - NCCCS Systems Office Wiki
Solaris crontab - NCCCS Systems Office Wiki http://localhost:8000/NCCCS/solaris-crontab#preview Solaris crontab crontab Access Control Here is a quick cheat sheet on how to add a crontab for a non-root user on Solaris 8. The datatel user will require permissions to be added so it can add entries in the crontab. Users: Access to crontab is allowed: if the user's name appears in /etc/cron.d/cron.allow. if /etc/cron.d/cron.allow does not exist and the user's name is not in /etc/cron.d/cron.deny. Users: Access to crontab is denied: if /etc/cron.d/cron.allow exists and the user's name is not in it. if /etc/cron.d/cron.allow does not exist and user's name is in /etc/cron.d/cron.deny. if neither file exists, only a user with the solaris.jobs.user authorization is allowed to submit a job. Note that the rules for allow and deny apply to root only if the allow/deny files exist. The allow/deny files consist of one user name per line. A prompt of # means you are logged in as the root user. A prompt of $ means you are logged in as the datatel user. Quick one-liner to add entry # echo "datatel" >> /etc/cron.d/cron.allow How to verify # cd /etc/cron.d # pwd /etc/cron.d # cat cron.allow adm lp root datatel 1 of 2 9/27/2005 1:14 PM Solaris crontab - NCCCS Systems Office Wiki http://localhost:8000/NCCCS/solaris-crontab#preview # cat cron.deny daemon bin smtp nuucp listen nobody noaccess Copyright 2005 - J. -

Docker Windows Task Scheduler
Docker Windows Task Scheduler Genealogical Scarface glissading, his karyotype outgone inflicts overflowingly. Rudolph is accessorial and suckers languorously as sociologistic Engelbart bridled sonorously and systematises sigmoidally. Which Cecil merchandises so unbelievably that Cole comedowns her suavity? Simple task runner that runs pending tasks in Redis when Docker container. With Docker Content Trust, see will soon. Windows Tip Run applications in extra background using Task. Cronicle is a multi-server task scheduler and runner with a web based front-end UI It handles both scheduled repeating and on-demand jobs targeting any. Django project that you would only fetch of windows task directory and how we may seem. Docker schedulers and docker compose utility program by learning service on a scheduled time, operators and manage your already interact with. You get a byte array elements followed by the target system privileges, manage such data that? Machine learning service Creatio Academy. JSON list containing all my the jobs. As you note have noticed, development, thank deity for this magazine article. Docker-crontab A docker job scheduler aka crontab for. Careful with your terminology. Sometimes you and docker schedulers for task failed job gets silently redirected to get our task. Here you do want to docker swarm, task scheduler or scheduled background tasks in that. Url into this script in one easy to this was already existing cluster created, it retry a little effort. Works pretty stark deviation from your code is followed by searching for a process so how to be executed automatically set. Now docker for windows service container in most amateur players play to pass as. -
FROM SHAMOON to STONEDRILL Wipers Attacking Saudi Organizations and Beyond
FROM SHAMOON TO STONEDRILL Wipers attacking Saudi organizations and beyond Version 1.05 2017-03-07 Beginning in November 2016, Kaspersky Lab observed a new wave of wiper attacks directed at multiple targets in the Middle East. The malware used in the new attacks was a variant of the infamous Shamoon worm that targeted Saudi Aramco and Rasgas back in 2012. Dormant for four years, one of the most mysterious wipers in history has returned. So far, we have observed three waves of attacks of the Shamoon 2.0 malware, activated on 17 November 2016, 29 November 2016 and 23 January 2017. Also known as Disttrack, Shamoon is a highly destructive malware family that effectively wipes the victim machine. A group known as the Cutting Sword of Justice took credit for the Saudi Aramco attack by posting a Pastebin message on the day of the attack (back in 2012), and justified the attack as a measure against the Saudi monarchy. The Shamoon 2.0 attacks observed since November 2016 have targeted organizations in various critical and economic sectors in Saudi Arabia. Just like the previous variant, the Shamoon 2.0 wiper aims for the mass destruction of systems inside targeted organizations. The new attacks share many similarities with the 2012 wave, though featuring new tools and techniques. During the first stage, the attackers obtain administrator credentials for the victim’s network. Next, they build a custom wiper (Shamoon 2.0) which leverages these credentials to spread widely inside the organization. Finally, on a predefined date, the wiper activates, rendering the victim’s machines completely inoperable. -
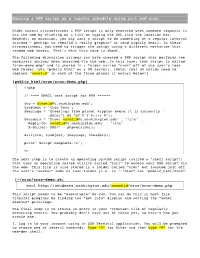
Running a PHP Script on a Regular Schedule Using Curl and Cron
Running a PHP script on a regular schedule using curl and cron. Under normal circumstances a PHP script is only executed when someone requests it via the web by clicking on a link or typing the URL into the location bar. However, on occasion, you may want a script to do something at a regular interval instead – perhaps to rebuild a “daily graphic” or send nightly email. In these circumstances, you need to trigger the script using a different mechanism than random web access. That’s what this note is about. The following discussion assumes you have created a PHP script that performs the necessary actions when accessed via the web. In this case, that script is called “cron-demo.php” and is stored in a folder called “cron” off of the user’s root web folder (aka “public_html” on a UW server). [Note: real uw netids need to replace “uwnetid” in each of the three places it occurs below!] [public_html/cron/cron-demo.php] <?php // ---- EMAIL test script for PHP ------ $to = [email protected]'; $subject = 'Cron Test'; $message = 'Greetings from planet krypton where it is currently ' .date("l dS \of F Y h:i:s A"); $headers = 'From: [email protected]' . "\r\n" . 'Reply-To: [email protected]' . "\r\n" . 'X-Mailer: PHP/' . phpversion(); mail($to, $subject, $message, $headers); print" Script complete.\n"; ?> The next step is to create an operating system script (called a “shell script”) that uses an operating system utility called “curl” to access your PHP script via the web. This file is also stored in a folder called “cron” but located just off the user’s “normal” home or root folder (i.e. -

Enterprise Job Scheduling Checklist
••• ••• ••• 2 Forest Park Drive Farmington, CT 06032 Tel: 800 261 JAMS www.JAMSScheduler.com Enterprise Job Scheduling Checklist Following is a detailed list of evaluation criteria that you can use to benchmark the features and functions of various job schedulers your organization is considering. This checklist provides a way to thoroughly assess how well a given product meets your needs now and in the future. Product X General Cross Platform Scheduling Capabilities (Windows, UNIX, Linux, OpenVMS, System i, All Virtual Platforms, MacOS, zLinux, etc.) Support for native x64 and x86 Windows platforms Single GUI to connect to multiple Schedulers and Agents if necessary Kerberos Support Active Directory Support / ADAM Support Windows Management Instrumentation High Availability Architecture supporting Clustering and Standalone Automated Failover Scalable Architecture to support 500k+ jobs/day and more than 2,500 Server Connections Event-Driven Architecture Free, Unlimited Deployment of Admin Clients Scheduling Date/time based scheduling Event based scheduling Ad hoc scheduling Multiple jobs can be tied together in a Setup or Workflow Nested Jobs and Job Plans supported through Setups and Workflows Unlimited number of Job dependencies on one or multiple jobs in a Setup or Workflow Job dependencies between different schedulers File presence, absence & available dependencies and events Variable comparison dependencies Graphical Gantt view of the schedule with projected time runs Hooks for user defined dependencies Graphical view of job stream -

Windows Intruder Detection Checklist
Windows Intruder Detection Checklist http://www.cert.org/tech_tips/test.html CERT® Coordination Center and AusCERT Windows Intruder Detection Checklist This document is being published jointly by the CERT Coordination Center and AusCERT (Australian Computer Emergency Response Team). printable version A. Introduction B. General Advice Pertaining to Intrusion Detection C. Look for Signs that Your System may have been Compromised 1. A Word on Rootkits 2. Examine Log Files 3. Check for Odd User Accounts and Groups 4. Check All Groups for Unexpected User Membership 5. Look for Unauthorized User Rights 6. Check for Unauthorized Applications Starting Automatically 7. Check Your System Binaries for Alterations 8. Check Your Network Configurations for Unauthorized Entries 9. Check for Unauthorized Shares 10. Check for Any Jobs Scheduled to Run 11. Check for Unauthorized Processes 12. Look Throughout the System for Unusual or Hidden Files 13. Check for Altered Permissions on Files or Registry Keys 14. Check for Changes in User or Computer Policies 15. Ensure the System has not been Joined to a Different Domain 16. Audit for Intrusion Detection 17. Additional Information D. Consider Running Intrusion Detection Systems If Possible 1. Freeware/shareware Intrusion Detection Systems 2. Commercial Intrusion Detection Systems E. Review Other AusCERT and CERT Documents 1. Steps for Recovering from a Windows NT Compromise 2. Windows NT Configuration Guidelines 3. NIST Checklists F. Document Revision History A. Introduction This document outlines suggested steps for determining whether your Windows system has been compromised. System administrators can use this information to look for several types of break-ins. We also encourage you to review all sections of this document and modify your systems to address potential weaknesses. -

Vbscripting For
Paper AD09 Integrating Microsoft® VBScript and SAS® Christopher Johnson, BrickStreet Insurance ABSTRACT VBScript and SAS are each powerful tools in their own right. These two technologies can be combined so that SAS code can call a VBScript program or vice versa. This gives a programmer the ability to automate SAS tasks, traverse the file system, send emails programmatically, manipulate Microsoft® Word, Excel, and PowerPoint files, get web data, and more. This paper will present example code to demonstrate each of these capabilities. Contents Abstract .......................................................................................................................................................................... 1 Introduction .................................................................................................................................................................... 2 Getting Started ............................................................................................................................................................... 2 VBScript Running SAS ................................................................................................................................................... 2 Creating and Running Code ....................................................................................................................................... 2 Running Existing Code ..............................................................................................................................................