Assembly Language
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Theendokernel: Fast, Secure
The Endokernel: Fast, Secure, and Programmable Subprocess Virtualization Bumjin Im Fangfei Yang Chia-Che Tsai Michael LeMay Rice University Rice University Texas A&M University Intel Labs Anjo Vahldiek-Oberwagner Nathan Dautenhahn Intel Labs Rice University Abstract Intra-Process Sandbox Multi-Process Commodity applications contain more and more combina- ld/st tions of interacting components (user, application, library, and Process Process Trusted Unsafe system) and exhibit increasingly diverse tradeoffs between iso- Unsafe ld/st lation, performance, and programmability. We argue that the Unsafe challenge of future runtime isolation is best met by embracing syscall()ld/st the multi-principle nature of applications, rethinking process Trusted Trusted read/ architecture for fast and extensible intra-process isolation. We IPC IPC write present, the Endokernel, a new process model and security Operating System architecture that nests an extensible monitor into the standard process for building efficient least-authority abstractions. The Endokernel introduces a new virtual machine abstraction for Figure 1: Problem: intra-process is bypassable because do- representing subprocess authority, which is enforced by an main is opaque to OS, sandbox limits functionality, and inter- efficient self-isolating monitor that maps the abstraction to process is slow and costly to apply. Red indicates limitations. system level objects (processes, threads, files, and signals). We show how the Endokernel Architecture can be used to develop enforces subprocess access control to memory and CPU specialized separation abstractions using an exokernel-like state [10, 17, 24, 25, 75].Unfortunately, these approaches only organization to provide virtual privilege rings, which we use virtualize minimal parts of the CPU and neglect tying their to reorganize and secure NGINX. -

6.004 Computation Structures Spring 2009
MIT OpenCourseWare http://ocw.mit.edu 6.004 Computation Structures Spring 2009 For information about citing these materials or our Terms of Use, visit: http://ocw.mit.edu/terms. M A S S A C H U S E T T S I N S T I T U T E O F T E C H N O L O G Y DEPARTMENT OF ELECTRICAL ENGINEERING AND COMPUTER SCIENCE 6.004 Computation Structures β Documentation 1. Introduction This handout is a reference guide for the β, the RISC processor design for 6.004. This is intended to be a complete and thorough specification of the programmer-visible state and instruction set. 2. Machine Model The β is a general-purpose 32-bit architecture: all registers are 32 bits wide and when loaded with an address can point to any location in the byte-addressed memory. When read, register 31 is always 0; when written, the new value is discarded. Program Counter Main Memory PC always a multiple of 4 0x00000000: 3 2 1 0 0x00000004: 32 bits … Registers SUB(R3,R4,R5) 232 bytes R0 ST(R5,1000) R1 … … R30 0xFFFFFFF8: R31 always 0 0xFFFFFFFC: 32 bits 32 bits 3. Instruction Encoding Each β instruction is 32 bits long. All integer manipulation is between registers, with up to two source operands (one may be a sign-extended 16-bit literal), and one destination register. Memory is referenced through load and store instructions that perform no other computation. Conditional branch instructions are separated from comparison instructions: branch instructions test the value of a register that can be the result of a previous compare instruction. -

Introduction to Programming in Fortran 77 for Students of Science and Engineering
Introduction to programming in Fortran 77 for students of Science and Engineering Roman GrÄoger University of Pennsylvania, Department of Materials Science and Engineering 3231 Walnut Street, O±ce #215, Philadelphia, PA 19104 Revision 1.2 (September 27, 2004) 1 Introduction Fortran (FORmula TRANslation) is a programming language designed speci¯cally for scientists and engineers. For the past 30 years Fortran has been used for such projects as the design of bridges and aeroplane structures, it is used for factory automation control, for storm drainage design, analysis of scienti¯c data and so on. Throughout the life of this language, groups of users have written libraries of useful standard Fortran programs. These programs can be borrowed and used by other people who wish to take advantage of the expertise and experience of the authors, in a similar way in which a book is borrowed from a library. Fortran belongs to a class of higher-level programming languages in which the programs are not written directly in the machine code but instead in an arti¯cal, human-readable language. This source code consists of algorithms built using a set of standard constructions, each consisting of a series of commands which de¯ne the elementary operations with your data. In other words, any algorithm is a cookbook which speci¯es input ingredients, operations with them and with other data and ¯nally returns one or more results, depending on the function of this algorithm. Any source code has to be compiled in order to obtain an executable code which can be run on your computer. -

A Beginner's Guide to Freebasic
A Beginner’s Guide to FreeBasic Richard D. Clark Ebben Feagan A Clark Productions / HMCsoft Book Copyright (c) Ebben Feagan and Richard Clark. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front-Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled "GNU Free Documentation License". The source code was compiled under version .17b of the FreeBasic compiler and tested under Windows 2000 Professional and Ubuntu Linux 6.06. Later compiler versions may require changes to the source code to compile successfully and results may differ under different operating systems. All source code is released under version 2 of the Gnu Public License (http://www.gnu.org/copyleft/gpl.html). The source code is provided AS IS, WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. Microsoft Windows®, Visual Basic® and QuickBasic® are registered trademarks and are copyright © Microsoft Corporation. Ubuntu is a registered trademark of Canonical Limited. 2 To all the members of the FreeBasic community, especially the developers. 3 Acknowledgments Writing a book is difficult business, especially a book on programming. It is impossible to know how to do everything in a particular language, and everyone learns something from the programming community. I have learned a multitude of things from the FreeBasic community and I want to send my thanks to all of those who have taken the time to post answers and examples to questions. -

Frequently Asked Questions in Mathematics
Frequently Asked Questions in Mathematics The Sci.Math FAQ Team. Editor: Alex L´opez-Ortiz e-mail: [email protected] Contents 1 Introduction 4 1.1 Why a list of Frequently Asked Questions? . 4 1.2 Frequently Asked Questions in Mathematics? . 4 2 Fundamentals 5 2.1 Algebraic structures . 5 2.1.1 Monoids and Groups . 6 2.1.2 Rings . 7 2.1.3 Fields . 7 2.1.4 Ordering . 8 2.2 What are numbers? . 9 2.2.1 Introduction . 9 2.2.2 Construction of the Number System . 9 2.2.3 Construction of N ............................... 10 2.2.4 Construction of Z ................................ 10 2.2.5 Construction of Q ............................... 11 2.2.6 Construction of R ............................... 11 2.2.7 Construction of C ............................... 12 2.2.8 Rounding things up . 12 2.2.9 What’s next? . 12 3 Number Theory 14 3.1 Fermat’s Last Theorem . 14 3.1.1 History of Fermat’s Last Theorem . 14 3.1.2 What is the current status of FLT? . 14 3.1.3 Related Conjectures . 15 3.1.4 Did Fermat prove this theorem? . 16 3.2 Prime Numbers . 17 3.2.1 Largest known Mersenne prime . 17 3.2.2 Largest known prime . 17 3.2.3 Largest known twin primes . 18 3.2.4 Largest Fermat number with known factorization . 18 3.2.5 Algorithms to factor integer numbers . 18 3.2.6 Primality Testing . 19 3.2.7 List of record numbers . 20 3.2.8 What is the current status on Mersenne primes? . -

Memory Layout and Access Chapter Four
Memory Layout and Access Chapter Four Chapter One discussed the basic format for data in memory. Chapter Three covered how a computer system physically organizes that data. This chapter discusses how the 80x86 CPUs access data in memory. 4.0 Chapter Overview This chapter forms an important bridge between sections one and two (Machine Organization and Basic Assembly Language, respectively). From the point of view of machine organization, this chapter discusses memory addressing, memory organization, CPU addressing modes, and data representation in memory. From the assembly language programming point of view, this chapter discusses the 80x86 register sets, the 80x86 mem- ory addressing modes, and composite data types. This is a pivotal chapter. If you do not understand the material in this chapter, you will have difficulty understanding the chap- ters that follow. Therefore, you should study this chapter carefully before proceeding. This chapter begins by discussing the registers on the 80x86 processors. These proces- sors provide a set of general purpose registers, segment registers, and some special pur- pose registers. Certain members of the family provide additional registers, although typical application do not use them. After presenting the registers, this chapter describes memory organization and seg- mentation on the 80x86. Segmentation is a difficult concept to many beginning 80x86 assembly language programmers. Indeed, this text tends to avoid using segmented addressing throughout the introductory chapters. Nevertheless, segmentation is a power- ful concept that you must become comfortable with if you intend to write non-trivial 80x86 programs. 80x86 memory addressing modes are, perhaps, the most important topic in this chap- ter. -

Chapter 7 Expressions and Assignment Statements
Chapter 7 Expressions and Assignment Statements Chapter 7 Topics Introduction Arithmetic Expressions Overloaded Operators Type Conversions Relational and Boolean Expressions Short-Circuit Evaluation Assignment Statements Mixed-Mode Assignment Chapter 7 Expressions and Assignment Statements Introduction Expressions are the fundamental means of specifying computations in a programming language. To understand expression evaluation, need to be familiar with the orders of operator and operand evaluation. Essence of imperative languages is dominant role of assignment statements. Arithmetic Expressions Their evaluation was one of the motivations for the development of the first programming languages. Most of the characteristics of arithmetic expressions in programming languages were inherited from conventions that had evolved in math. Arithmetic expressions consist of operators, operands, parentheses, and function calls. The operators can be unary, or binary. C-based languages include a ternary operator, which has three operands (conditional expression). The purpose of an arithmetic expression is to specify an arithmetic computation. An implementation of such a computation must cause two actions: o Fetching the operands from memory o Executing the arithmetic operations on those operands. Design issues for arithmetic expressions: 1. What are the operator precedence rules? 2. What are the operator associativity rules? 3. What is the order of operand evaluation? 4. Are there restrictions on operand evaluation side effects? 5. Does the language allow user-defined operator overloading? 6. What mode mixing is allowed in expressions? Operator Evaluation Order 1. Precedence The operator precedence rules for expression evaluation define the order in which “adjacent” operators of different precedence levels are evaluated (“adjacent” means they are separated by at most one operand). -

Thriving in a Crowded and Changing World: C++ 2006–2020
Thriving in a Crowded and Changing World: C++ 2006–2020 BJARNE STROUSTRUP, Morgan Stanley and Columbia University, USA Shepherd: Yannis Smaragdakis, University of Athens, Greece By 2006, C++ had been in widespread industrial use for 20 years. It contained parts that had survived unchanged since introduced into C in the early 1970s as well as features that were novel in the early 2000s. From 2006 to 2020, the C++ developer community grew from about 3 million to about 4.5 million. It was a period where new programming models emerged, hardware architectures evolved, new application domains gained massive importance, and quite a few well-financed and professionally marketed languages fought for dominance. How did C++ ś an older language without serious commercial backing ś manage to thrive in the face of all that? This paper focuses on the major changes to the ISO C++ standard for the 2011, 2014, 2017, and 2020 revisions. The standard library is about 3/4 of the C++20 standard, but this paper’s primary focus is on language features and the programming techniques they support. The paper contains long lists of features documenting the growth of C++. Significant technical points are discussed and illustrated with short code fragments. In addition, it presents some failed proposals and the discussions that led to their failure. It offers a perspective on the bewildering flow of facts and features across the years. The emphasis is on the ideas, people, and processes that shaped the language. Themes include efforts to preserve the essence of C++ through evolutionary changes, to simplify itsuse,to improve support for generic programming, to better support compile-time programming, to extend support for concurrency and parallel programming, and to maintain stable support for decades’ old code. -

Operators and Expressions
UNIT – 3 OPERATORS AND EXPRESSIONS Lesson Structure 3.0 Objectives 3.1 Introduction 3.2 Arithmetic Operators 3.3 Relational Operators 3.4 Logical Operators 3.5 Assignment Operators 3.6 Increment and Decrement Operators 3.7 Conditional Operator 3.8 Bitwise Operators 3.9 Special Operators 3.10 Arithmetic Expressions 3.11 Evaluation of Expressions 3.12 Precedence of Arithmetic Operators 3.13 Type Conversions in Expressions 3.14 Operator Precedence and Associability 3.15 Mathematical Functions 3.16 Summary 3.17 Questions 3.18 Suggested Readings 3.0 Objectives After going through this unit you will be able to: Define and use different types of operators in Java programming Understand how to evaluate expressions? Understand the operator precedence and type conversion And write mathematical functions. 3.1 Introduction Java supports a rich set of operators. We have already used several of them, such as =, +, –, and *. An operator is a symbol that tells the computer to perform certain mathematical or logical manipulations. Operators are used in programs to manipulate data and variables. They usually form a part of mathematical or logical expressions. Java operators can be classified into a number of related categories as below: 1. Arithmetic operators 2. Relational operators 1 3. Logical operators 4. Assignment operators 5. Increment and decrement operators 6. Conditional operators 7. Bitwise operators 8. Special operators 3.2 Arithmetic Operators Arithmetic operators are used to construct mathematical expressions as in algebra. Java provides all the basic arithmetic operators. They are listed in Tabled 3.1. The operators +, –, *, and / all works the same way as they do in other languages. -

AN125: Integrating Raisonance 8051 Tools Into The
AN125 INTEGRATING RAISONANCE 8051 TOOLS INTO THE SILICON LABS IDE 1. Introduction 4. Configure the Tool Chain This application note describes how to integrate the Integration Dialog Raisonance 8051 Tools into the Silicon Laboratories Under the 'Project' menu, select 'Tool Chain Integration’ IDE (Integrated Development Environment). Integration to bring up the dialog box shown below. Raisonance provides an efficient development environment with (Ride 7) is the default. To use Raisonance (Ride 6), you compose, edit, build, download and debug operations can select it from the 'Preset Name' drop down box integrated in the same program. under 'Tools Definition Presets'. Next, define the Raisonance assembler, compiler, and linker as shown in 2. Key Points the following sections. The Intel OMF-51 absolute object file generated by the Raisonance 8051 tools enables source-level debug from the Silicon Labs IDE. Once Raisonance Tools are integrated into the IDE they are called by simply pressing the ‘Assemble/ Compile Current File’ button or the ‘Build/Make Project’ button. See the “..\Silabs\MCU\Examples” directory for examples that can be used with the Raisonance tools. Information in this application note applies to Version 4.00 and later of the Silicon Labs IDE and Ride7 and later of the Raisonance 8051 tools. 4.1. Assembler Definition 1. Under the ‘Assembler’ tab, if the assembler 3. Create a Project in the Silicon executable is not already defined, click the browse Labs IDE button next to the ‘Executable:’ text box, and locate the assembler executable. The default location for A project is necessary in order to link assembly files the Raisonance assembler is: created by the compiler and build an absolute ‘OMF-51’ C:\Program Files\Raisonance\Ride7\bin\ma51.exe output file. -
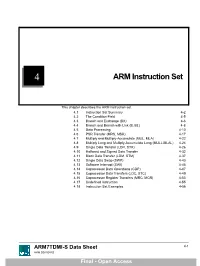
ARM Instruction Set
4 ARM Instruction Set This chapter describes the ARM instruction set. 4.1 Instruction Set Summary 4-2 4.2 The Condition Field 4-5 4.3 Branch and Exchange (BX) 4-6 4.4 Branch and Branch with Link (B, BL) 4-8 4.5 Data Processing 4-10 4.6 PSR Transfer (MRS, MSR) 4-17 4.7 Multiply and Multiply-Accumulate (MUL, MLA) 4-22 4.8 Multiply Long and Multiply-Accumulate Long (MULL,MLAL) 4-24 4.9 Single Data Transfer (LDR, STR) 4-26 4.10 Halfword and Signed Data Transfer 4-32 4.11 Block Data Transfer (LDM, STM) 4-37 4.12 Single Data Swap (SWP) 4-43 4.13 Software Interrupt (SWI) 4-45 4.14 Coprocessor Data Operations (CDP) 4-47 4.15 Coprocessor Data Transfers (LDC, STC) 4-49 4.16 Coprocessor Register Transfers (MRC, MCR) 4-53 4.17 Undefined Instruction 4-55 4.18 Instruction Set Examples 4-56 ARM7TDMI-S Data Sheet 4-1 ARM DDI 0084D Final - Open Access ARM Instruction Set 4.1 Instruction Set Summary 4.1.1 Format summary The ARM instruction set formats are shown below. 3 3 2 2 2 2 2 2 2 2 2 2 1 1 1 1 1 1 1 1 1 1 9876543210 1 0 9 8 7 6 5 4 3 2 1 0 9 8 7 6 5 4 3 2 1 0 Cond 0 0 I Opcode S Rn Rd Operand 2 Data Processing / PSR Transfer Cond 0 0 0 0 0 0 A S Rd Rn Rs 1 0 0 1 Rm Multiply Cond 0 0 0 0 1 U A S RdHi RdLo Rn 1 0 0 1 Rm Multiply Long Cond 0 0 0 1 0 B 0 0 Rn Rd 0 0 0 0 1 0 0 1 Rm Single Data Swap Cond 0 0 0 1 0 0 1 0 1 1 1 1 1 1 1 1 1 1 1 1 0 0 0 1 Rn Branch and Exchange Cond 0 0 0 P U 0 W L Rn Rd 0 0 0 0 1 S H 1 Rm Halfword Data Transfer: register offset Cond 0 0 0 P U 1 W L Rn Rd Offset 1 S H 1 Offset Halfword Data Transfer: immediate offset Cond 0 -

Cognitive Programming Language (CPL) Programmer's Guide
Cognitive Programming Language (CPL) Programmer's Guide 105-008-02 Revision C2 – 3/17/2006 *105-008-02* Copyright © 2006, Cognitive. Cognitive™, Cxi™, and Ci™ are trademarks of Cognitive. Microsoft® and Windows™ are trademarks of Microsoft Corporation. Other product and corporate names used in this document may be trademarks or registered trademarks of other companies, and are used only for explanation and to their owner’s benefit, without intent to infringe. All information in this document is subject to change without notice, and does not represent a commitment on the part of Cognitive. No part of this document may be reproduced for any reason or in any form, including electronic storage and retrieval, without the express permission of Cognitive. All program listings in this document are copyrighted and are the property of Cognitive and are provided without warranty. To contact Cognitive: Cognitive Solutions, Inc. 4403 Table Mountain Drive Suite A Golden, CO 80403 E-Mail: [email protected] Telephone: +1.800.525.2785 Fax: +1.303.273.1414 Table of Contents Introduction.............................................................................................. 1 Label Format Organization .................................................................. 2 Command Syntax................................................................................ 2 Important Programming Rules............................................................. 3 Related Publications...........................................................................