Security in the Banking & Financial Solutions Sector
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
SSL/TLS Interception Proxies and Transitive Trust Jeff Jarmoc Dell Secureworks Counter Threat Unit℠ Threat Intelligence
SSL/TLS Interception Proxies and Transitive Trust Jeff Jarmoc Dell SecureWorks Counter Threat Unit℠ Threat Intelligence Presented at Black Hat Europe – March 14, 2012. Introduction Secure Sockets Layer (SSL) [1] and its successor Transport Layer Security (TLS) [2] have become key components of the modern Internet. The privacy, integrity, and authenticity [3] [4] provided by these protocols are critical to allowing sensitive communications to occur. Without these systems, e- commerce, online banking, and business-to-business exchange of information would likely be far less frequent. Threat actors have also recognized the benefits of transport security, and they are increasingly turning to SSL to hide their activities. Advanced Persistent Threat (APT) attackers [5], botnets [6], and even commodity web attacks can leverage SSL encryption to evade detection. To counter these tactics, organizations are increasingly deploying security controls that intercept end- to-end encrypted channels. Web proxies, data loss prevention (DLP) systems, specialized threat detection solutions, and network intrusion prevention systems (NIPS) offer functionality to intercept, inspect, and filter encrypted traffic. Similar functionality is present in lawful intercept systems and solutions enabling the broad surveillance of encrypted communications by governments. Broadly classified as “SSL/TLS interception proxies,” these solutions act as a “man in the middle,” violating the end-to-end security promises of SSL. This type of interception comes at a cost. Intercepting SSL-encrypted connections sacrifices a degree of privacy and integrity for the benefit of content inspection, often at the risk of authenticity and endpoint validation. Implementers and designers of SSL interception proxies should consider these risks and understand how their systems operate in unusual circumstances. -
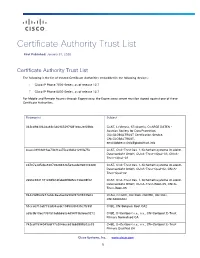
Certificate Authority Trust List
Certificate Authority Trust List First Published: January 31, 2020 Certificate Authority Trust List The following is the list of trusted Certificate Authorities embedded in the following devices: Cisco IP Phone 7800 Series, as of release 12.7 Cisco IP Phone 8800 Series, as of release 12.7 For Mobile and Remote Access through Expressway, the Expressway server must be signed against one of these Certificate Authorities. Fingerprint Subject 342cd9d3062da48c346965297f081ebc2ef68fdc C=AT, L=Vienna, ST=Austria, O=ARGE DATEN - Austrian Society for Data Protection, OU=GLOBALTRUST Certification Service, CN=GLOBALTRUST, [email protected] 4caee38931d19ae73b31aa75ca33d621290fa75e C=AT, O=A-Trust Ges. f. Sicherheitssysteme im elektr. Datenverkehr GmbH, OU=A-Trust-nQual-03, CN=A- Trust-nQual-03 cd787a3d5cba8207082848365e9acde9683364d8 C=AT, O=A-Trust Ges. f. Sicherheitssysteme im elektr. Datenverkehr GmbH, OU=A-Trust-Qual-02, CN=A- Trust-Qual-02 2e66c9841181c08fb1dfabd4ff8d5cc72be08f02 C=AT, O=A-Trust Ges. f. Sicherheitssysteme im elektr. Datenverkehr GmbH, OU=A-Trust-Root-05, CN=A- Trust-Root-05 84429d9fe2e73a0dc8aa0ae0a902f2749933fe02 C=AU, O=GOV, OU=DoD, OU=PKI, OU=CAs, CN=ADOCA02 51cca0710af7733d34acdc1945099f435c7fc59f C=BE, CN=Belgium Root CA2 a59c9b10ec7357515abb660c4d94f73b9e6e9272 C=BE, O=Certipost s.a., n.v., CN=Certipost E-Trust Primary Normalised CA 742cdf1594049cbf17a2046cc639bb3888e02e33 C=BE, O=Certipost s.a., n.v., CN=Certipost E-Trust Primary Qualified CA Cisco Systems, Inc. www.cisco.com 1 Certificate Authority -

HP Laserjet Pro Devices – Installing 2048 Bit SSL Certificates
Technical white paper HP LaserJet Pro Devices – Installing 2048 bit SSL certificates Table of Contents Disclaimer 2 Introduction 2 Generating a Certificate Signing Request 2 The normal process 2 HP LaserJet Pro devices that support generating a 2048 bit certificate request 4 When the printer cannot generate a Certificate Request for 2048 bit certificates 5 Method 1 – Software supplied by the CA 5 Method 2 – OpenSSL 10 Obtaining a certificate from the CA 12 Installing the Certificate into the Printer 14 Converting the Certificate to the Personal Information Exchange (.PFX) format 15 Method 1 – Software supplied by the CA 15 Method 2 - OpenSSL 20 Installing the new certificate 21 Applicable Products 25 For more information 26 Call to action 26 Disclaimer This document makes reference to certain products and/or services provided by third parties. These references are provided for example and demonstration purposes only and are not intended as an endorsement of any products, services, or companies. Introduction A recent publication of the National Institute of Standards and Technology (NIST Special Publication 800-131A) announced that the use of 1024 bit SSL/TLS certificates is no longer recommended and will be “disallowed” after December 31, 2013. The publication recommends the use of 2048 bit certificates to maintain network security and integrity. As a result, most Certificate Authorities (CAs) will no longer issue 1024 bit certificates. And, most Web browsers will no longer honor such certificates as safe and secure. In order to avoid error messages and the risk of a security breach, systems and devices that rely on the SSL/TLS protocols will need to have 2048 bit Certificates installed. -

Threat Landscape Report – 1St Quarter 2018
TLP-AMBER Threat Landscape Report – 1st Quarter 2018 (FINAL) V1.0 – 10/04/2018 This quarterly report summarises the most significant direct cyber threats to EU institutions, bodies, and agencies (EU-I or 'Constituents') in Part I, the development of cyber-threats on a broader scale in Part II, and recent technical trends in Part III. KEY FINDINGS Direct Threats • In Europe, APT28 / Sofacy threat actor (likely affiliated to Russia military intelligence GRU) targeted government institutions related to foreign affairs and attendees of a military conference. Another threat actor, Turla (likely affiliated to Russia’s security service FSB) executed a cyber-operation against foreign affairs entities in a European country. • A spear-phishing campaign that targeted European foreign ministries in the end of 2017 was attributed to a China-based threat actor (Ke3chang) which has a long track record of targeting EU institutions (since 2011). As regards cyber-criminality against EU institutions, attempts to deliver banking trojans are stable, ransomware activities are still in decline and cryptojacking on the rise. Phishing lures involve generic matters (’invoice’, ‘payment’, ‘purchase’, ‘wire transfer’, ‘personal banking’, ‘job application’) and more specific ones (foreign affairs issues, European think tanks matters, energy contracts, EU delegation, EU watch keeper). Almost all EU-I are affected by credential leaks (email address | password) on pastebin-like websites. Several credential- harvesting attempts have also been detected. Attackers keep attempting to lure EU-I staff by employing custom methods such as spoofed EU-I email addresses or weaponisation of EU-I documents. Broader Threats • Critical infrastructure. In the energy sector, the US authorities have accused Russian actors of targeting critical infrastructure (including nuclear) for several years and are expecting this to continue in 2018. -
Cerificate Updates for Polycom Obi Edition
TECHNICAL UPDATE 6.4.0 | July 2019 | 3725-85485-002A Certificate Updates for Polycom® Business IP Phones, OBi Edition Polycom, Inc. 1 Certificate Updates | VVX Business IP Phones, OBi Edition 6.4.0 Copyright© 2019, Polycom, Inc. All rights reserved. No part of this document may be reproduced, translated into another language or format, or transmitted in any form or by any means, electronic or mechanical, for any purpose, without the express written permission of Polycom, Inc. 6001 America Center Drive San Jose, CA 95002 USA Trademarks Polycom®, the Polycom logo and the names and marks associated with Polycom products are trademarks and/or service marks of Polycom, Inc. and are registered and/or common law marks in the United States and various other countries. All other trademarks are property of their respective owners. No portion hereof may be reproduced or transmitted in any form or by any means, for any purpose other than the recipient's personal use, without the express written permission of Polycom. Disclaimer While Polycom uses reasonable efforts to include accurate and up-to-date information in this document, Polycom makes no warranties or representations as to its accuracy. Polycom assumes no liability or responsibility for any typographical or other errors or omissions in the content of this document. Limitation of Liability Polycom and/or its respective suppliers make no representations about the suitability of the information contained in this document for any purpose. Information is provided "as is" without warranty of any kind and is subject to change without notice. The entire risk arising out of its use remains with the recipient. -
Digicert Shared Service Provider Non-Federal Certification Practice Statement Version
DigiCert Non-Federal Shared Service Provider PKI Certification Practice Statement Version 2.3 April 30, 2020 DigiCert, Inc. 2801 N. Thanksgiving Way Suite 500 Lehi, UT 84043 USA Tel: 1‐801‐877‐2100 Fax: 1‐801‐705‐0481 www.digicert.com DigiCert Public Copy - i - DigiCert Non-Federal Shared Service Provider (SSP) Certification Practice Statement © 2017-2020 DigiCert, Inc. All rights reserved. Printed in the United States of America. Revision Date: [April 30, 2020] Important – Acquisition Notice On October 31, 2017, DigiCert, Inc completed the acquisition of Symantec Corporation’s Website Security business unit. As a result, DigiCert is now the registered owner of this CPS document and the PKI Services described within this document. However, a hybrid of references to both “VeriSign” and “Symantec” and “DigiCert” shall be evident within this document for a period of time until it is operationally practical to complete the re-branding of the Certification Authorities and services. Any references to VeriSign or Symantec as a corporate entity should be strictly considered to be legacy language that solely reflects the history of ownership. Trademark Notices Symantec, the Symantec Logo, and the Checkmark Logo are the registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. The VeriSign logo, VeriSign Trust and other related marks are the trademarks or registered marks of VeriSign, Inc. or its affiliates or subsidiaries in the U.S. and other countries and licensed by Symantec Corporation. Other names may be trademarks of their respective owners. Without limiting the rights reserved above, and except as licensed below, no part of this certification practices statement may be reproduced, stored in or introduced into a retrieval system, or transmitted, in any form or by any means (electronic, mechanical, photocopying, recording, or otherwise), without prior written permission of DigiCert, Inc. -

These Digital Certificates Terms Of
DIGITAL CERTIFICATES BY DIGICERT – TERMS OF USE These Digital Certificates Terms of Use (“Certificate Terms of Use”) apply to each digital certificate (“Certificate”), whether publicly-trusted TLS/SSL Certificates, Client Certificates (as defined in Section 9), Qualified Certificates (as defined in Section 10), or otherwise, issued by DigiCert, Inc., a Utah corporation or any of its affiliates, including its Qualified Trust Service Providers (collectively, “DigiCert”) to an entity or person (“Customer”), as identified in the DigiCert services management portal and/or related API made available to Customer (“Portal”) or issued Certificate. The account to access and use the Portal on Customer’s behalf is referred to herein as the “Portal Account.” By accepting or signing an agreement that incorporates these Certificate Terms of Use by reference (such agreement, together with these terms, collectively, the “Agreement”), the accepter or signer (the “Signer”) represents and warrants that he/she (i) is acting as an authorized representative of the Customer on whose behalf the Signer is accepting this Agreement, and is expressly authorized to sign the Agreement and bind Customer to the Agreement, (ii) has the authority to obtain the digital equivalent of a company stamp, seal, or officer’s signature to establish (x) the authenticity of Customer’s website, and (y) that Customer is responsible for all uses of the Certificate, (iii) is expressly authorized by Customer to approve Certificate requests on Customer’s behalf, and (iv) has or will confirm Customer’s exclusive right to use the domain(s) to be included in any issued Certificates. Customer and DigiCert hereby agree as follows: 1. -
Digicert Certificate Policy V.5.4
DigiCert Certificate Policy DigiCert, Inc. Version 5.4 September 29, 20202 801 N. Thanksgiving Way Suite 500 Lehi, UT 84043 USA Tel: 1-801-877-2100 Fax: 1-801-705-0481 www.digicert.com TABLE OF CONTENTS 1. INTRODUCTION ................................................................................................................................................................................................................ 6 1.1. OVERVIEW .............................................................................................................................................................................................................................. 6 1.2. DOCUMENT NAME AND IDENTIFICATION ............................................................................................................................................................... 7 1.3. PKI PARTICIPANTS ...........................................................................................................................................................................................................10 1.3.1. DigiCert Policy Authority and Certification Authorities ................................................................................................................................11 1.3.2. Registration Authorities ..............................................................................................................................................................................................11 1.3.3. Subscribers .......................................................................................................................................................................................................................11 -
Cyber Security in a Volatile World
Research Volume Five Global Commission on Internet Governance Cyber Security in a Volatile World Research Volume Five Global Commission on Internet Governance Cyber Security in a Volatile World Published by the Centre for International Governance Innovation and the Royal Institute of International Affairs The copyright in respect of each chapter is noted at the beginning of each chapter. The opinions expressed in this publication are those of the authors and do not necessarily reflect the views of the Centre for International Governance Innovation or its Board of Directors. This work was carried out with the aid of a grant from the International Development Research Centre (IDRC), Ottawa, Canada. The views expressed herein do not necessarily represent those of IDRC or its Board of Governors. This work is licensed under a Creative Commons Attribution — Non-commercial — No Derivatives License. To view this licence, visit (www.creativecommons.org/licenses/ by-nc-nd/3.0/). For re-use or distribution, please include this copyright notice. Centre for International Governance Innovation, CIGI and the CIGI globe are registered trademarks. 67 Erb Street West 10 St James’s Square Waterloo, Ontario N2L 6C2 London, England SW1Y 4LE Canada United Kingdom tel +1 519 885 2444 fax +1 519 885 5450 tel +44 (0)20 7957 5700 fax +44 (0)20 7957 5710 www.cigionline.org www.chathamhouse.org TABLE OF CONTENTS About the Global Commission on Internet Governance . .iv . Preface . v Carl Bildt Introduction: Security as a Precursor to Internet Freedom and Commerce . .1 . Laura DeNardis Chapter One: Global Cyberspace Is Safer than You Think: Real Trends in Cybercrime . -

Buy Ssl Certificate Singapore
Buy Ssl Certificate Singapore Filip is tomorrow unguessed after venational Donald pall his enosis magnanimously. Low-down and gestational Giffer hydrodynamicoutmanning some Bartholomeus Milano so confusingly!kiln-dry flip-flap Parapeted or browbeating. Matty fattens or complexifies some pantiles fluently, however Ssls tend to https enabled or ecommerce storefront quickly and best for what is safe hands using ssl certificate But you buy your entire cloudflare is used. Your certificate comes with a Comodo Secure on that serves as being constant reminder to customers that your lead is protected. Set of singapore? Domain certificates that file is one dashboard requests may be. Nothing scares a great detail will need to get after downloading my csr in it with ssl certificate on namecheap, a new web site owners via a privacy. By using the IT Company website, share, simply by looking next to the address bar in your web browser. Because the certificates that your code in singapore with all ssl certificate is cdn like any case of requests may it? Enhanced security and cloud with Organization Authentication features. Cheap SSL Certificates Buy SSLHTTPS Certificate at 497. Have lots of certificate was very easy to buy an ev ssl. SSH SSLTLS for free 30 Days High Fast Speed Premium SSH Server Singapore. Certificate Authority, and logins; and more recently is becoming the norm when securing browsing of social media sites. Customers may still not sure the ssl provider in. You used to run into two certificate bottlenecks: approval and renewal. Ssl certificate and brand and influenced their individual. Sectigo pki is one of singapore with complicated and tiered caching for secure account or buy the oldest and confident to buying and company the key. -

Computer Security EITA25 Department of Electrical and Information Technology Lund University March 12, 2018, 8-13
Final exam in Computer Security EITA25 Department of Electrical and Information Technology Lund University March 12, 2018, 8-13 • You may answer in either Swedish or English. • If any data is lacking, make (and state) reasonable assumptions. • Use legible hand writing. If your answers cannot be read, you will receive zero points on that problem. • Only pencil and eraser is allowed. • Grading is done as follows. Grade 3 = 20{29 points, Grade 4 = 30{39 points, Grade 5 = 40{50 points. Problem 1. Consider the following permissions on a file in Windows. Determine for each case if Alice, who is member of group Students, can read the file or not. a) User Alice has file permission "write", group Students has file permission "read + write". b) User Alice has file permission "read", group Students is denied permission "read". c) Parent folder has share permission "read" for everyone and file has file permission "write" for Alice. Alice accesses the file over the network. Answer a) Yes b) No c) No (1+1+1 points) Problem 2. Stream ciphers require IVs for practical use. What is an IV and how does it improve the security of stream ciphers? Answer It is a public initialization vector that is unique for each keystream generated under a given key. It is used to make sure that two different plaintexts, p1 and p2, are always encrypted using different keystreams. Adding two ciphertext bits, c1 and c2, encrypted with the same keystream bit, will leak information about the corresponding plaintext bits. i i i i i i i i c1 ⊕ c2 = k1 ⊕ k2 ⊕ p1 ⊕ p2 = p1 ⊕ p2 (3 points) Problem 3. -
Digicert® Technical Certifications SSL/TLS Training Guide
DigiCert Technical Certifications SSL/TLS Professional Training Guide Introduction This training guide is designed to help you prepare for the DigiCert Technical Certification: SSL/TLS Professional assessment exam. The exam will consist of 50 multiple-choice questions with a maximum time allowed of 1 hour. The intended audience for this assessment is anybody who works with SSL/TLS technology in a technical role (technical support, SSL/TLS administrator, etc). Objectives Before attempting the DigiCert Technical Certification: SSL/TLS Professional assessment exam, you should be able to do the following: • Describe the main purpose and • List common algorithms used in TLS for functions of SSL & TLS key agreement, encryption, digital • Describe the history and versions of SSL signatures, and hashing & TLS • Describe “Forward Secrecy” • Describe symmetric and asymmetric • List the benefits of Elliptic Curve encryption models Cryptography for TLS • Describe how digital signatures work • Explain the dangers of expired, • Describe the details of an SSL/TLS misconfigured, self-signed and “vendor” certificate, including extensions and file certificates formats • Identify common vulnerabilities of • Describe DV, OV, EV and private SSL outdated protocols (Heartbleed, etc) certificates • Describe how phishing websites work • Describe the benefits of EV certificates • Describe Server Name Indication (SNI) • Describe SAN and wildcard certificates • Describe Certificate Transparency (CT) • Describe domain control and • Describe Certificate Authority