An Innovative Custom Cyber Security Solution for Protecting Enterprises and Corporates’ Assets
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

DEFINICIÓN Un Antivirus
ANTIVIRUS DEFINICIÓN Un antivirus es un programa de computadora cuyo propósito es combatir y erradicar los virus informáticos. Para que el antivirus sea productivo y efectivo hay que configurarlo cuidadosamente de tal forma que aprovechemos todas las cualidades que ellos poseen. Hay que saber cuales son sus fortalezas y debilidades y tenerlas en cuenta a la hora de enfrentar a los virus. Un antivirus es una solución para minimizar los riesgos y nunca será una solución definitiva, lo principal es mantenerlo actualizado. Para mantener el sistema estable y seguro el antivirus debe estar siempre actualizado, tomando siempre medidas preventivas y correctivas y estar constantemente leyendo sobre los virus y nuevas tecnologías. ¿CÓMO FUNCIONA? Básicamente, un antivirus compara el código de cada archivo con una base de datos de los códigos (también conocidos como firmas o vacunas) de los virus conocidos, por lo que es importante actualizarla periódicamente a fin de evitar que un virus nuevo no sea detectado. También se les ha agregado funciones avanzadas, como la búsqueda de comportamientos típicos de virus (técnica conocida como Heurística) o la verificación contra virus en redes de computadores. Normalmente un antivirus tiene un componente que se carga en memoria y permanece en ella para verificar todos los archivos abiertos, creados, modificados y ejecutados en tiempo real. Es muy común que tengan componentes que revisen los adjuntos de los correos electrónicos salientes y entrantes, así como los scripts y programas que pueden ejecutarse en un navegador web (ActiveX, Java, JavaScript). ALGUNOS ANTIVIRUS 1 CLAM ANTIVIRUS Comodo AntiVirus FProt Antivirus FSecure AntiVirus ZoneAlarm Antivirus ANTIVIRUS HEURISTICOS Los heurísticos analizan el código de cada archivo con métodos genéricos y detectan virus nuevos que todavía no se han incluido en la base de datos de virus del programa antivirus. -
2016 SIEM Content and Parsing Updates Table of Contents
2016 SIEM Content and Parsing Updates Table of Contents Table of Contents 2 SIEM Data Sources 5 January 21, 2016 5 February 10, 2016 5 February 16, 2016 5 February 26, 2016 5 March 25, 2016 5 June 2, 2016 6 June 8, 2016 6 July 19, 2016 6 August 04, 2016 6 August 11, 2016 6 August 15, 2016 6 September 1, 2016 6 September 2, 2016 7 September 26, 2016 7 October 12, 2016 7 October 13, 2016 7 November 7, 2016 7 November 10, 2016 8 November 11, 2016 8 December 2, 2016 8 SIEM Custom Types 9 October 13, 2016 9 October 25, 2016 9 SIEM Parsing Rules 10 January 8, 2015 10 January 12, 2016 10 January 13, 2016 10 January 21, 2016 10 January 22, 2016 11 January 25, 2016 11 January 29, 2016 11 January 29, 2016 11 February 4, 2016 11 February 8, 2016 12 February 10, 2016 12 February 11, 2016 12 February 16, 2016 12 February 17, 2016 12 February 19, 2016 13 February 23, 2016 13 February 24, 2016 13 February 25, 2016 13 February 26, 2016 13 February 29, 2016 14 March 2, 2016 14 March 3, 2016 14 March 7, 2016 15 March 8, 2016 15 March 9, 2016 15 March 11, 2016 15 March 14, 2016 15 March 16, 2016 15 March 17, 2016 16 March 18, 2016 16 March 21, 2016 16 March 24, 2016 17 March 25, 2016 17 March 29, 2016 17 March 30, 2016 18 March 31, 2016 18 April 01, 2016 18 April 04, 2016 18 April 07, 2016 18 April 08, 2016 18 April 21, 2016 18 2 April 26, 2016 19 May 3, 2016 19 May 5, 2016 19 May 5, 2016 19 May 9, 2016 19 May 11, 2016 19 May 16, 2016 19 May 18, 2016 19 May 23, 2016 19 May 24, 2016 20 May 25, 2016 20 May 26, 2016 21 May 27, 2016 21 June 2, 2016 21 June 06, -

Accomplished and Certified IT Security Professional with Experience Assisting Organizations Successfully Complete Enterprise-Wide Security Projects
ROHIT BANKOTI Accomplished and certified IT security professional with experience assisting organizations successfully complete enterprise-wide security projects. Experience in finance, technology, healthcare, telecom industries and a proven track record of streamlining security processes, design and implement efficient security solutions, lead and assist multi-disciplined, multi-national teams in achieving security efficiency. Professional Qualifications: • Degree Bachelor of Technology (Computer Science ) • CGPA 6.36/10 • Institute University Institute of Engg. & Tech. (MDU), Rohtak Academic Qualifications: • Completed XII standard from Hamdard Public School (CBSE) in with 79% • Completed X standard from Amrita Public School (CBSE) in with 81% CERTIFICATIONS • Sophos Certified Architect for UTM by RED Education. • Sophos Certified Engineer for Endpoint, MDM, Email protection, Encryption. • GFI (Languard, FAX maker, Mail essential & Cloud, Endpoint security • CEH version 7 training from net hub. • ECSA (E-council) 412-79 complete training from net hub. • Smooth Wall Certified engineer and Operator Certified. • McAfee certified for McAfee VSE, EPO, Mobile Management, HIPS and Mail. • Symantec Partner certification and Advanced Threat Protection. • Certified Information Security and Ethical hacking (C.I.S.E) from innobuzz. • Infowatch (DLP) training on endpoint and network level. • Qualys Vulnerability Expert. • C++ and .NET certification from Aptech, South Extension (Delhi) Professional Synopsis: Currently:- Working with Mckinsey & Company, Gurgaon, India as Security Engineer. - Mainly working with ATP projects. - Anti-phishing program - Other Operations 2015 to 2016 with CSC (Computer Science & Corporation), Noida - Sandboxing and Malware clean-up process - Identify Malware Domain and Phishing Attack vector. • Dec 2014 to Aug 2015 with ASIT, Delhi as Security Consultant. Working as UTM, SIEM, MDM and DLP architect. -

Clam Antivirus: Open-Source Virus Protection
Clam Antivirus: Open-Source Virus protection Michaël Van Canneyt March 16, 2014 Abstract Protecting your precious PC against email and other viruses doesn’t have to cost a lot of money: Clam Antivrus is an open source virus scanner which can be installed on Unix machines (suitable for integration in mail server’s MTAs) but which also has a Windows version for those that are not fortunate enough have a Unix at hand. Introducing Clam Antivirus Clam Antivirus is an open-source implementation of a virus scanner which does 1 thing only: it scans a file for known viruses. The virus scanner consists of 2 parts: One is the actual scanner, clamscan: It scans a file to see whether it is infected with a known virus. It reports on the found viruses. The known viruses are kept in a database file. The second part (freshclam) serves to keep this database up-to-date: new viruses are born every day, and existing viruses mutate to more dangerous forms regularly, it is therefore of the utmost importance to keep the database with virus definitions up-to-date. The freshclam program should be run on a regular basis, for instance in a cron job on Unix. The Unix version features also a client/server model: The scanner runs as a daemon. The clamscan program then sends the file to be scanned to the daemon, for inpection. This reduces startup time and system load, which is quite important on servers than run a heavy- load MTA service. On Windows, a small GUI frontend exists which allows to perform and schedule scans, and to perform and schedule the virus database update. -
Linux Security Review 2015
Linux Security Review 2015 www.av-comparatives.org AV-Comparatives Linux Security Review Language: English May 2015 Last revision: 26 th May 2015 www.av-comparatives.org -1- Linux Security Review 2015 www.av-comparatives.org Contents Introduction ....................................................................................................................... 3 Reviewed products ............................................................................................................... 4 Malware for Linux systems ..................................................................................................... 5 Linux security advice ............................................................................................................ 6 Items covered in the review .................................................................................................. 7 Avast File Server Security ...................................................................................................... 8 AVG Free Edition for Linux.................................................................................................... 11 Bitdefender Antivirus Scanner for Unices ................................................................................ 13 Clam Antivirus for Linux ....................................................................................................... 17 Comodo Antivirus for Linux .................................................................................................. 20 Dr.Web Anti-virus for -

MRG Effitas Real Time Protection Test Project, First Quarter (Q2 2013)
MRG Effitas Real Time Protection Test Project, First Quarter – Q2 2013 MRG Effitas Real Time Protection Test Project, First Quarter (Q2 2013) Copyright 2013 MRG Effitas Ltd. This article or any part of it must not be published or reproduced without the consent of the copyright holder. 1 MRG Effitas Real Time Protection Test Project, First Quarter – Q2 2013 Contents: Introduction 3 Security Applications Tested 3 Methodology used in the Test 4 Samples Used 5 Test Results 6 Conclusions 7 Copyright 2013 MRG Effitas Ltd. This article or any part of it must not be published or reproduced without the consent of the copyright holder. 2 MRG Effitas Real Time Protection Test Project, First Quarter – Q2 2013 Introduction: The MRG Effitas Real Time Protection Testing Project is a replacement for and an evolution of the “Flash Tests” conducted to date. For those unfamiliar with the Flash Tests, their purpose was to give an indication of product efficacy against live, ITW threats applied to the System Under Test (SUT) using a valid, real world infection vector and process. Despite using live ITW malware and realistic infection vectors, we always added the caveat that due to the small malware sample size used, the individual Flash Tests should not be used as a rigorous assessment of product efficacy and that their purpose was to give an indication of efficacy over time. The MRG Effitas Real Time Protection Testing Project is designed to overcome the limitation of the Flash Tests by using greatly increased number of malware samples and higher testing frequency. The project will run for twelve months commencing at the start of Q2 2013 and finishing at the end of Q1 2014 – in line with all our other projects. -

Windows Antivirus Support Chart for Hostscan 3.1.06073 Product Name
Windows Antivirus Support Chart for HostScan 3.1.06073 Marketing Product Data File Engine Live Version Check RTP Set RTP Language Alias Name Time Version Update Names 360Safe.co m 360 1.x ✔ ✔ ✔ ✔ ✔ English 360杀毒 Antivirus 360 3.x ✔ ✘ ✔ ✘ ✘ English Antivirus 360 Total 4.x ✔ ✔ ✔ ✘ ✘ English Security Chinese 360 360杀毒 1.x ✔ ✔ ✔ ✘ ✘ Simplified Antivirus Chinese 360 360杀毒 2.x ✔ ✔ ✔ ✘ ✘ Simplified Antivirus Chinese 360杀毒 3.x ✘ ✘ ✔ ✘ ✘ Simplified Chinese 360 360杀毒 4.x ✘ ✘ ✔ ✘ ✘ Simplified Antivirus Chinese 360 360杀毒 5.x ✘ ✘ ✔ ✘ ✘ Simplified Antivirus Other 360Safe.co x ✘ ✘ ✘ ✘ ✘ English m Antivirus AEC, spol. s r.o. TrustPort 2.x ✘ ✘ ✔ ✔ ✘ English Antivirus Other AEC, spol. s r.o. x ✘ ✘ ✘ ✘ ✘ English Antivirus Agnitum Ltd. Outpost Antivirus 7.x ✔ ✔ ✔ ✔ ✘ English Pro Outpost Antivirus 8.x ✔ ✔ ✔ ✔ ✘ English Pro Outpost Antivirus 9.x ✔ ✔ ✔ ✔ ✔ English Pro Outpost Outpost Security Antivirus 6.x ✔ ✔ ✔ ✔ ✘ English Suite Pro Pro 2009 2009 Outpost Security 7.x ✘ ✘ ✔ ✘ ✘ English Suite Free Outpost Security 7.x ✔ ✔ ✔ ✔ ✘ English Suite Pro Outpost Security 8.x ✔ ✔ ✔ ✔ ✔ English Suite Pro Outpost Security 9.x ✔ ✔ ✔ ✔ ✔ English Suite Pro Other Agnitum x ✘ ✘ ✘ ✘ ✘ English Ltd. Antivirus AhnLab, Inc. AhnLab Security 2.x ✔ ✔ ✘ ✔ ✘ English Pack AhnLab V3 Internet 7.x ✔ ✔ ✔ ✔ ✘ English Security 2007 AhnLab V3 Internet Security 7.x ✔ ✔ ✔ ✔ ✘ English 2007 Platinum AhnLab V3 Internet Security 7.x ✔ ✔ ✔ ✔ ✘ English 2008 Platinum AhnLab V3 Internet Security 7.x ✔ ✔ ✔ ✔ ✔ English 2009 Platinum AhnLab V3 Internet Security 7.0 7.x ✔ ✔ ✔ ✔ ✘ English Platinum Enterprise AhnLab V3 Internet 8.x ✔ ✔ ✔ ✔ ✔ English Security 8.0 AhnLab V3 Internet 9.x ✔ ✔ ✔ ✔ ✔ English Security 9.0 AhnLab V3 VirusBlock Internet 7.x ✔ ✔ ✘ ✔ ✘ English Security 2007 AhnLab V3 VirusBlock Internet Security 7.x ✔ ✔ ✔ ✘ ✔ English 2007 Platinum Enterprise V3 Click 1.x ✔ ✘ ✘ ✘ ✘ English V3 Lite 1.x ✔ ✔ ✔ ✔ ✔ Korean V3 Lite 3.x ✔ ✔ ✔ ✘ ✘ Korean V3 VirusBlock 6.x ✔ ✔ ✘ ✘ ✘ English 2005 V3 ウイルスブ NA ✔ ✔ ✘ ✔ ✘ Japanese ロック V3Pro 2004 6.x ✔ ✔ ✔ ✔ ✘ English Other AhnLab, x ✘ ✘ ✘ ✘ ✘ English Inc. -

Characterizing Antivirus Workload Execution
Characterizing Antivirus Workload Execution Derek Uluski, Micha Moffie and David Kaeli Computer Architecture Research Laboratory Northeastern University Boston, MA {duluski,mmoffie,kaeli}@ece.neu.edu Abstract head is introduced if we enable anti-virus scan- ning. Many users are unhappy with the per- Despite the pervasive use of anti-virus (AV) formance penalty they must pay for security. software, there has not been a systematic The amount of overhead introduced can be study of the characteristics of the execution of so significant that many users will defer virus this workload. In this paper we present a char- scanning or totally disable their anti-virus soft- acterization of four commonly used anti-virus ware. Then their system will be vulnerable to software packages. Using the Virtutech Simics viruses. Thus, it is important to address the toolset, we profile the behavior of four popu- performance overhead associated with anti- lar anti-virus packages as run on an Intel Pen- virus software execution. tiumIV platform running Microsoft Windows- Most anti-virus software packages employ a XP. range of scanning techniques to decide whether In our study, we focus on the overhead in- or not a given file is infected. More complex troduced by the anti-virus software during on- techniques also exist such as: sandboxing, dig- access execution. The overhead associated ital watermarking, and heuristic-based tech- with anti-virus execution can dominate overall niques [11]. performance. The AV-Test group has already There are two main usage models when run- reported that this overhead can range from 23- ning anti-virus software, 1) on-demand,and2) 129% on live systems running on-access exper- 1 on-access. -

Mssp Advanced Threat Protection Service
SOLUTION BRIEF SOLUTION BRIEF: MSSP ADVANCED THREAT PROTECTION SERVICE MSSP Advanced Threat Protection Service Fortinet Empowers MSSP Delivery of Complete ATP Managed Security Service The Need For ATP Managed Security Service FIGURE 1: ADVANCED PRESISTANT THREAT LIFECYCLE According to Frost & Sullivan, the global Managed Security Services (MSS) market will grow from $9B in 2013 to $15B by 2015. This business opportunity is driven by two main factors - the growing acceptance of cloud-based, Security-as-a- Service delivery and the need for enterprises and SMBs alike to reduce security related CAPEX and OPEX costs. As the threat landscape continues to evolve and grow in both volume and sophistication, MSSPs need to evolve their MSS offerings to address this growing threat and provide Advanced Threat Protection (ATP) services. Advanced Persistent Threats are well thought, multi stage processes as outlines in figure 1. Protecting against these APTs requires an equally well thought, multi stage framework that will deploy the largest number of weapons available in the MSSP’s security arsenal to provide a meaningful response for its customers’ concerns. 1 1 SOLUTION BRIEF: MSSP ADVANCED THREAT PROTECTION SERVICE Fortinet’s Advanced Threat Protection Framework for MSSPs Fortinet arms MSSPs with a structured Advanced Threat Protection Framework – to provide organizations a comprehensive solution to address this new class of advanced targeted attacks. There is no one component or technology that will guarantee protection from a sufficiently targeted and sophisticated attack. Each technology has inherent strengths and weaknesses, which, even when deployed together but independently from other technologies, may leave exploitable gaps in the network’s defense architecture. -
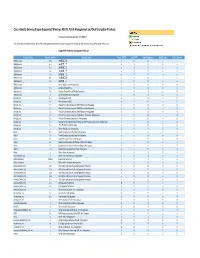
Cisco Identity Services Engine Supported Windows AV/AS/PM/DE
Cisco Identity Services Engine Supported Windows AS/AV, Patch Management and Disk Encryption Products Compliance Module Version 3.6.10363.2 This document provides Windows AS/AV, Patch Management and Disk Encryption support information on the the Cisco AnyConnect Agent Version 4.2. Supported Windows Antispyware Products Vendor_Name Product_Version Product_Name Check_FSRTP Set_FSRTP VirDef_Signature VirDef_Time VirDef_Version 360Safe.com 10.x 360安全卫士 vX X v v 360Safe.com 4.x 360安全卫士 vX X v v 360Safe.com 5.x 360安全卫士 vX X v v 360Safe.com 6.x 360安全卫士 vX X v v 360Safe.com 7.x 360安全卫士 vX X v v 360Safe.com 8.x 360安全卫士 vX X v v 360Safe.com 9.x 360安全卫士 vX X v v 360Safe.com x Other 360Safe.com Antispyware Z X X Z X Agnitum Ltd. 7.x Outpost Firewall Pro vX X X O Agnitum Ltd. 6.x Outpost Firewall Pro 2008 [AntiSpyware] v X X v O Agnitum Ltd. x Other Agnitum Ltd. Antispyware Z X X Z X AhnLab, Inc. 2.x AhnLab SpyZero 2.0 vv O v O AhnLab, Inc. 3.x AhnLab SpyZero 2007 X X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2007 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2008 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2009 Platinum AntiSpyware v v O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 7.0 Platinum Enterprise AntiSpyware v X O v O AhnLab, Inc. 8.x AhnLab V3 Internet Security 8.0 AntiSpyware v v O v O AhnLab, Inc. -
Anti-Virus Outbreak Response Testing and Impact
Insecurity in Security Software Maik Morgenstern Andreas Marx AV-Test GmbH http://www.av-test.org Virus Bulletin 2005 Conference presentation about “Insecurity in Security Software” Copyright © 2005 AV-Test GmbH, Klewitzstr. 6, D-39112 Magdeburg, Germany Phone: +49 391 6075460, Fax: +49 391 6075469, http://www.av-test.org Table of content z The paradox z Types of security software z Comparison of CVE advisories z Examples of bugs and security vulnerabilities z Why bugs occur z Vulnerability lifecycle z What to do? (for users and developers) z Trustworthy computing security development lifecycle The paradox z All software products contain security vulnerabilities (and other bugs) z AV software is widely deployed to protect companies, organizations and home users z Every week, security flaws are discovered in different AV products z The paradox: Security software is meant to secure the system, but nowadays it introduces new security holes. Types of security software z Two different groups of security software: – Home and business user software (widely used) z Firewalls z IPSec products z IDS/IPS z AV software… – Tools used by researchers (small deployment) z IDA Pro z OllyDbg z Softice… CVE advisories for vendor products (2001 quarterly average = 100, Source: © The Yankee Group) z Microsoft / Security vendors / All vendors Bugs leading to security vulnerabilities z A couple of examples from recent months (advisory titles): – ISS and the Witty Worm – Trend Micro VSAPI ARJ parsing – McAfee Virus Library – Symantec Multiple Products UPX Parsing Engine Heap Overflow – Computer Associates Vet Antivirus Library Remote Heap Overflow – Kaspersky AntiVirus "klif.sys" Privilege Escalation Vulnerability – OllyDbg "INT3 AT" Format String Vulnerability – DataRescue IDA Pro Dynamic Link Library Format String Vulnerability – Clam AntiVirus ClamAV Cabinet File Handling DoS Vulnerability Bugs vs.