Pursue the Attackers - Identify and Investigate Lateral Movement Based on Behavior Pattern
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cisco Telepresence Codec SX20 API Reference Guide
Cisco TelePresence SX20 Codec API Reference Guide Software version TC6.1 April 2013 Application Programmer Interface (API) Reference Guide Cisco TelePresence SX20 Codec D14949.03 SX20 Codec API Reference Guide TC6.1, April 2013. 1 Copyright © 2013 Cisco Systems, Inc. All rights reserved. Cisco TelePresence SX20 Codec API Reference Guide What’s in this guide? Table of Contents Introduction Using HTTP ....................................................................... 20 Getting status and configurations ................................. 20 TA - ToC - Hidden About this guide .................................................................. 4 The top menu bar and the entries in the Table of Sending commands and configurations ........................ 20 text anchor User documentation ........................................................ 4 Contents are all hyperlinks, just click on them to Using HTTP POST ......................................................... 20 go to the topic. About the API Feedback from codec over HTTP ......................................21 Registering for feedback ................................................21 API fundamentals ................................................................ 9 Translating from terminal mode to XML ......................... 22 We recommend you visit our web site regularly for Connecting to the API ..................................................... 9 updated versions of the user documentation. Go to: Password ........................................................................ -
Introduction to Linux – Part 1
Introduction to Linux – Part 1 Brett Milash and Wim Cardoen Center for High Performance Computing May 22, 2018 ssh Login or Interactive Node kingspeak.chpc.utah.edu Batch queue system … kp001 kp002 …. kpxxx FastX ● https://www.chpc.utah.edu/documentation/software/fastx2.php ● Remote graphical sessions in much more efficient and effective way than simple X forwarding ● Persistence - can be disconnected from without closing the session, allowing users to resume their sessions from other devices. ● Licensed by CHPC ● Desktop clients exist for windows, mac, and linux ● Web based client option ● Server installed on all CHPC interactive nodes and the frisco nodes. Windows – alternatives to FastX ● Need ssh client - PuTTY ● http://www.chiark.greenend.org.uk/~sgtatham/putty/download.html - XShell ● http://www.netsarang.com/download/down_xsh.html ● For X applications also need X-forwarding tool - Xming (use Mesa version as needed for some apps) ● http://www.straightrunning.com/XmingNotes/ - Make sure X forwarding enabled in your ssh client Linux or Mac Desktop ● Just need to open up a terminal or console ● When running applications with graphical interfaces, use ssh –Y or ssh –X Getting Started - Login ● Download and install FastX if you like (required on windows unless you already have PuTTY or Xshell installed) ● If you have a CHPC account: - ssh [email protected] ● If not get a username and password: - ssh [email protected] Shell Basics q A Shell is a program that is the interface between you and the operating system -

Dig, a DNS Query Tool for Windows and Replacement for Nslookup 2008-04-15 15:29
dig, a DNS query tool for Windows and replacement for nslookup 2008-04-15 15:29 Disclaimer dig (dig for Windows ) (dig is a powerful tool to investigate [digging into] the DNS system) Source of the binary is from ftp.isc.org Manual Page of dig, in the cryptic Unix style, for reference only. (1) Download: Windows 2000 or Windows XP or Windows Vista ( dig version 9.3.2) Create a folder c:\dig Download this dig-files.zip and save it to c:\dig Use winzip or equivalent to extract the files in dig-files.zip to c:\dig Note: If msvcr70.dll already exists in %systemroot%\system32\ , then you can delete c:\dig\msvcr70.dll Note: Included in dig-files.zip is a command line whois, version 4.7.11: The canonical site of the whois source code is http://ftp.debian.org/debian/pool/main/w/whois/ The whois.exe file inside dig-files.zip is compiled using cygwin c++ compiler. (2) Do a file integrity check (why ? Because some virus checkers destroy dll files) Click Start.. Run ... type CMD (a black screen pops up) cd c:\dig sha1 * You should see some SHA1 hashes (in here, SHA1 hash is used as an integrity check, similar to checksums). Compare your hashes with the following table. SHA1 v1.0 [GPLed] by Stephan T. Lavavej, http://stl.caltech.edu 6CA70A2B 11026203 EABD7D65 4ADEFE3D 6C933EDA cygwin1.dll 57487BAE AA0EB284 8557B7CA 54ED9183 EAFC73FA dig.exe 97DBD755 D67A5829 C138A470 8BE7A4F2 6ED0894C host.exe D22E4B89 56E1831F F0F9D076 20EC19BF 171F0C29 libbind9.dll 81588F0B E7D3C6B3 20EDC314 532D9F2D 0A105594 libdns.dll E0BD7187 BBC01003 ABFE7472 E64B68CD 1BDB6BAB libeay32.dll F445362E 728A9027 96EC6871 A79C6307 054974E4 libisc.dll B3255C0E 4808A703 F95C217A 91FFCD69 40E680C9 libisccfg.dll DFBDE4F9 E25FD49A 0846E97F D813D687 6DC94067 liblwres.dll 61B8F573 DB448AE6 351AE347 5C2E7C48 2D81533C msvcr70.dll BDA14B28 7987E168 F359F0C9 DD96866D 04AB189B resolv.conf 1112343A 319C3EEE E44BF261 AE196C96 289C70E2 sha1.exe 21D20035 2A5B64E2 69FEA407 4D78053F 3C7A2738 whois.exe If your hashes are the same as the above table, then your files pass the integrity check. -
Shell Variables
Shell Using the command line Orna Agmon ladypine at vipe.technion.ac.il Haifux Shell – p. 1/55 TOC Various shells Customizing the shell getting help and information Combining simple and useful commands output redirection lists of commands job control environment variables Remote shell textual editors textual clients references Shell – p. 2/55 What is the shell? The shell is the wrapper around the system: a communication means between the user and the system The shell is the manner in which the user can interact with the system through the terminal. The shell is also a script interpreter. The simplest script is a bunch of shell commands. Shell scripts are used in order to boot the system. The user can also write and execute shell scripts. Shell – p. 3/55 Shell - which shell? There are several kinds of shells. For example, bash (Bourne Again Shell), csh, tcsh, zsh, ksh (Korn Shell). The most important shell is bash, since it is available on almost every free Unix system. The Linux system scripts use bash. The default shell for the user is set in the /etc/passwd file. Here is a line out of this file for example: dana:x:500:500:Dana,,,:/home/dana:/bin/bash This line means that user dana uses bash (located on the system at /bin/bash) as her default shell. Shell – p. 4/55 Starting to work in another shell If Dana wishes to temporarily use another shell, she can simply call this shell from the command line: [dana@granada ˜]$ bash dana@granada:˜$ #In bash now dana@granada:˜$ exit [dana@granada ˜]$ bash dana@granada:˜$ #In bash now, going to hit ctrl D dana@granada:˜$ exit [dana@granada ˜]$ #In original shell now Shell – p. -

1. Run Nslookup to Obtain the IP Address of a Web Server in Europe
1. Run nslookup to obtain the IP address of a Web server in Europe. frigate:Desktop drb$ nslookup home.web.cern.ch Server: 130.215.32.18 Address: 130.215.32.18#53 Non-authoritative answer: home.web.cern.ch canonical name = drupalprod.cern.ch. Name: drupalprod.cern.ch Address: 137.138.76.28 Note that the #53 denotes the DNS service is running on port 53. 2. Run nslookup to determine the authoritative DNS servers for a university in Asia. frigate:Desktop drb$ nslookup -type=NS tsinghua.edu.cn Server: 130.215.32.18 Address: 130.215.32.18#53 Non-authoritative answer: tsinghua.edu.cn nameserver = dns2.tsinghua.edu.cn. tsinghua.edu.cn nameserver = dns.tsinghua.edu.cn. tsinghua.edu.cn nameserver = dns2.edu.cn. tsinghua.edu.cn nameserver = ns2.cuhk.edu.hk. Authoritative answers can be found from: dns2.tsinghua.edu.cn internet address = 166.111.8.31 ns2.cuhk.edu.hk internet address = 137.189.6.21 ns2.cuhk.edu.hk has AAAA address 2405:3000:3:6::15 dns2.edu.cn internet address = 202.112.0.13 dns.tsinghua.edu.cn internet address = 166.111.8.30 Note that there can be multiple authoritative servers. The response we got back was from a cached record. To confirm the authoritative DNS servers, we perform the same DNS query of one of the servers that can provide authoritative answers. frigate:Desktop drb$ nslookup -type=NS tsinghua.edu.cn dns.tsinghua.edu.cn Server: dns.tsinghua.edu.cn Address: 166.111.8.30#53 tsinghua.edu.cn nameserver = dns2.edu.cn. -
The Linux Command Line Presentation to Linux Users of Victoria
The Linux Command Line Presentation to Linux Users of Victoria Beginners Workshop August 18, 2012 http://levlafayette.com What Is The Command Line? 1.1 A text-based user interface that provides an environment to access the shell, which interfaces with the kernel, which is the lowest abstraction layer to system resources (e.g., processors, i/o). Examples would include CP/M, MS-DOS, various UNIX command line interfaces. 1.2 Linux is the kernel; GNU is a typical suite of commands, utilities, and applications. The Linux kernel may be accessed by many different shells e.g., the original UNIX shell (sh), the TENEX C shell (tcsh), Korn shell (ksh), and explored in this presentation, the Bourne-Again Shell (bash). 1.3 The command line interface can be contrasted with the graphic user interface (GUI). A GUI interface typically consists of window, icon, menu, pointing-device (WIMP) suite, which is popular among casual users. Examples include MS-Windows, or the X- Window system. 1.4 A critical difference worth noting is that in UNIX-derived systems (such as Linux and Mac OS), the GUI interface is an application launched from the command-line interface, whereas with operating systems like contemporary versions of MS-Windows, the GUI is core and the command prompt is a native MS-Windows application. Why Use The Command Line? 2.1 The command line uses significantly less resources to carry out the same task; it requires less processor power, less memory, less hard-disk etc. Thus, it is preferred on systems where performance is considered critical e.g., supercomputers and embedded systems. -
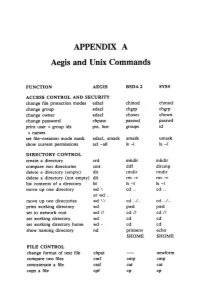
APPENDIX a Aegis and Unix Commands
APPENDIX A Aegis and Unix Commands FUNCTION AEGIS BSD4.2 SYSS ACCESS CONTROL AND SECURITY change file protection modes edacl chmod chmod change group edacl chgrp chgrp change owner edacl chown chown change password chpass passwd passwd print user + group ids pst, lusr groups id +names set file-creation mode mask edacl, umask umask umask show current permissions acl -all Is -I Is -I DIRECTORY CONTROL create a directory crd mkdir mkdir compare two directories cmt diff dircmp delete a directory (empty) dlt rmdir rmdir delete a directory (not empty) dlt rm -r rm -r list contents of a directory ld Is -I Is -I move up one directory wd \ cd .. cd .. or wd .. move up two directories wd \\ cd . ./ .. cd . ./ .. print working directory wd pwd pwd set to network root wd II cd II cd II set working directory wd cd cd set working directory home wd- cd cd show naming directory nd printenv echo $HOME $HOME FILE CONTROL change format of text file chpat newform compare two files emf cmp cmp concatenate a file catf cat cat copy a file cpf cp cp Using and Administering an Apollo Network 265 copy std input to std output tee tee tee + files create a (symbolic) link crl In -s In -s delete a file dlf rm rm maintain an archive a ref ar ar move a file mvf mv mv dump a file dmpf od od print checksum and block- salvol -a sum sum -count of file rename a file chn mv mv search a file for a pattern fpat grep grep search or reject lines cmsrf comm comm common to 2 sorted files translate characters tic tr tr SHELL SCRIPT TOOLS condition evaluation tools existf test test -
Introduction to Unix Shell
Introduction to Unix Shell François Serra, David Castillo, Marc A. Marti- Renom Genome Biology Group (CNAG) Structural Genomics Group (CRG) Run Store Programs Data Communicate Interact with each other with us The Unix Shell Introduction Interact with us Rewiring Telepathy Typewriter Speech WIMP The Unix Shell Introduction user logs in The Unix Shell Introduction user logs in user types command The Unix Shell Introduction user logs in user types command computer executes command and prints output The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output ⋮ user logs off The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output ⋮ user logs off The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output ⋮ user logs off shell The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output -

Lab Intro to Console Commands
New Lab Intro to KDE Terminal Konsole After completing this lab activity the student will be able to; Access the KDE Terminal Konsole and enter basic commands. Enter commands using a typical command line interface (CLI). Explain the use of the following commands, ls, ls –al, dir, mkdir, whoami, Explain the directory structure of a typical user. This lab activity will introduce you to one of the many command line interfaces available in Linux/UNIX operating systems and a few of the most basic commands. The command line interface you will be using for this lab activity is the console called the Konsole and is also referred to as Terminal. Note: As you notice, in the KDE system many features are written with the capital letter “K” in place of the first letter or the utility to reflect the fact it was modified for the KDE system. The original UNIX system did not use a graphical user interface GUI but rather was a command line interface (CLI) similar to the command prompt in Windows operating systems. The command line interface is referred to as a shell. Even today the command line interface (the shell) is used to issue commands on a Linux server to minimize system resources. For example, there is no need to start the GUI on the server to add a new user to an existing system. Starting the GUI will reduce the system performance because it requires RAM to run the GUI. A GUI will affect the overall performance of the server when it is supporting many users (clients). -

Command Reference Guide for Cisco Prime Infrastructure 3.9
Command Reference Guide for Cisco Prime Infrastructure 3.9 First Published: 2020-12-17 Americas Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 527-0883 THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB's public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS" WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -

Guide to Install Caffe on the Idiap Cluster Without Root Permissions
Guide to install Caffe on the idiap cluster without root permissions: Please, don’t copy and paste the commands (in italic letters) because it may be an error (a space, or a long dash, etc.) it is just better to type them manually and CHECK that makes sense to your environment. 0) Set environmental variables: export PATH=/idiap/home/$(whoami)/usr/bin/:$PATH export LD_LIBRARY_PATH=/idiap/home/$(whoami)/usr/lib/:$LD_LIBRARY_PATH 1) Install a virtual environment for Python virtualenv --system-site-packages -p /usr/bin/python2.7 caffe-py27 Note: Install everything while in the virtual environment: source caffe-py27/bin/activate Upgrade pup pip install --upgrade pip • Install some python libraries (I used this, but just install the required for you) pip install pandas pip install scipy pip install -U scikit-learn pip install Augmentor 2) Create a “usr” directory: mkdir /idiap/home/$(whoami)/usr 3) Install pre-requisites (download the packages in one folder and install in “usr” folder): • Boost curl -L -O http://sourceforge.net/projects/boost/files/boost/1.65.1/boost_1_65_1.tar.gz tar zxvf boost_1_65_1.tar.gz cd boost_1_65_1/ ./bootstrap.sh --libdir=/idiap/home/$(whoami)/usr/lib -- includedir=/idiap/home/$(whoami)/usr/include vi project-config.jam # check that the python paths correspond to your virtual environment ./b2 ./b2 install • Opencv (Note: if it is already installed, just skip this part) https://github.com/Itseez/opencv.git mkdir build cd build cmake -D CMAKE_BUILD_TYPE=RELEASE -D CMAKE_INSTALL_PREFIX=/idiap/home/$(whoami)/usr .. make make install cp /idiap/home/$(whoami)/usr/opencv-3.3.1/build/lib/cv2.so /idiap/home/$(whoami)/caffe- py27/lib/python2.7/site-packages/cv2.so • Protobuf git clone https://github.com/google/protobuf.git cd protobuf/ ./autogen.sh ./configure --prefix=/idiap/home/$(whoami)/usr make make install • glog git clone https://github.com/google/glog.git cd glog ./autogen.sh ./configure --prefix=/idiap/home/$(whoami)/usr make make install • gflags git clone https://github.com/gflags/gflags.git cd gflags mkdir build cd build ccmake . -
Tanium™ Appliance Deployment Guide
Tanium™ Appliance Deployment Guide Version 1.5.6 June 06, 2020 The information in this document is subject to change without notice. Further, the information provided in this document is provided “as is” and is believed to be accurate, but is presented without any warranty of any kind, express or implied, except as provided in Tanium’s customer sales terms and conditions. Unless so otherwise provided, Tanium assumes no liability whatsoever, and in no event shall Tanium or its suppliers be liable for any indirect, special, consequential, or incidental damages, including without limitation, lost profits or loss or damage to data arising out of the use or inability to use this document, even if Tanium Inc. has been advised of the possibility of such damages. Any IP addresses used in this document are not intended to be actual addresses. Any examples, command display output, network topology diagrams, and other figures included in this document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincidental. Please visit https://docs.tanium.com for the most current Tanium product documentation. This documentation may provide access to or information about content, products (including hardware and software), and services provided by third parties (“Third Party Items”). With respect to such Third Party Items, Tanium Inc. and its affiliates (i) are not responsible for such items, and expressly disclaim all warranties and liability of any kind related to such Third Party Items and (ii) will not be responsible for any loss, costs, or damages incurred due to your access to or use of such Third Party Items unless expressly set forth otherwise in an applicable agreement between you and Tanium.