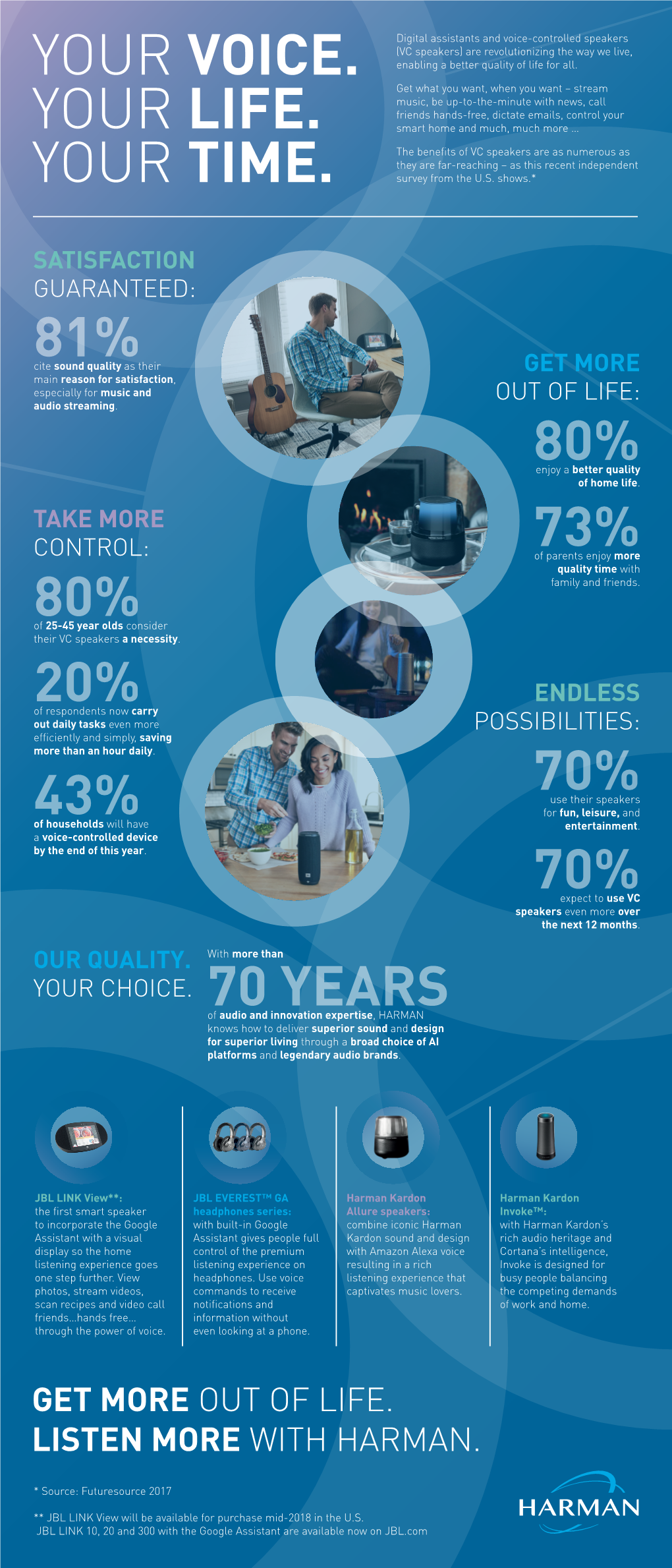
Get More out of Life. Listen More with Harman
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

FIT to WORK: IMPROVING the SECURITY of MONITORED EMPLOYEES' HEALTH DATA Elizabeth A. Brown INTRODUCTION Imagine Coming to Work
FIT TO WORK: IMPROVING THE SECURITY OF MONITORED EMPLOYEES' HEALTH DATA Elizabeth A. Brown1 INTRODUCTION Imagine coming to work one day and finding that your employer has given everyone in the company a wearable FitBit health monitor, free of charge. You pop the FitBit on, grateful for another bit of help in managing the health concerns that nag at you persistently but which never quite rise to the top of your priority list. At your next performance review, your supervisor expresses concern about your anxiety levels. Although your work output is slightly off, she notes, there has been a correlation in your lack of sleep and exercise, and she suspects you are depressed. You wonder how your employer might know these things, whether or not they are true, and then you remember the FitBit. Your supervisor then tells you that the promotion you had wanted is going to a colleague who is “better equipped to handle the demands of the job.” You interview for another job, and are asked to provide the password to the HealthDrive account that centralizes the fitness data all the apps on your iPhone collect about you during the day. Similar scenarios are playing out now in workplaces across the country, and will do so more frequently as the personal health sensor market and employee monitoring trends continue to grow. Employers are making key decisions based on employees’ biometric data, collected from specialized devices like a FitBit or the health-related apps installed on mobile phones. BP, for example, adjusts its employees’ health care premiums depending on how much physical activity their wearable FitBit devices monitor – devices that BP provides to thousands of employees, their spouses, and retirees for free. -

Your Voice Assistant Is Mine: How to Abuse Speakers to Steal Information and Control Your Phone ∗ †
Your Voice Assistant is Mine: How to Abuse Speakers to Steal Information and Control Your Phone ∗ y Wenrui Diao, Xiangyu Liu, Zhe Zhou, and Kehuan Zhang Department of Information Engineering The Chinese University of Hong Kong {dw013, lx012, zz113, khzhang}@ie.cuhk.edu.hk ABSTRACT General Terms Previous research about sensor based attacks on Android platform Security focused mainly on accessing or controlling over sensitive compo- nents, such as camera, microphone and GPS. These approaches Keywords obtain data from sensors directly and need corresponding sensor invoking permissions. Android Security; Speaker; Voice Assistant; Permission Bypass- This paper presents a novel approach (GVS-Attack) to launch ing; Zero Permission Attack permission bypassing attacks from a zero-permission Android application (VoicEmployer) through the phone speaker. The idea of 1. INTRODUCTION GVS-Attack is to utilize an Android system built-in voice assistant In recent years, smartphones are becoming more and more popu- module – Google Voice Search. With Android Intent mechanism, lar, among which Android OS pushed past 80% market share [32]. VoicEmployer can bring Google Voice Search to foreground, and One attraction of smartphones is that users can install applications then plays prepared audio files (like “call number 1234 5678”) in (apps for short) as their wishes conveniently. But this convenience the background. Google Voice Search can recognize this voice also brings serious problems of malicious application, which have command and perform corresponding operations. With ingenious been noticed by both academic and industry fields. According to design, our GVS-Attack can forge SMS/Email, access privacy Kaspersky’s annual security report [34], Android platform attracted information, transmit sensitive data and achieve remote control a whopping 98.05% of known malware in 2013. -

Smart Speakers & Their Impact on Music Consumption
Everybody’s Talkin’ Smart Speakers & their impact on music consumption A special report by Music Ally for the BPI and the Entertainment Retailers Association Contents 02"Forewords 04"Executive Summary 07"Devices Guide 18"Market Data 22"The Impact on Music 34"What Comes Next? Forewords Geoff Taylor, chief executive of the BPI, and Kim Bayley, chief executive of ERA, on the potential of smart speakers for artists 1 and the music industry Forewords Kim Bayley, CEO! Geoff Taylor, CEO! Entertainment Retailers Association BPI and BRIT Awards Music began with the human voice. It is the instrument which virtually Smart speakers are poised to kickstart the next stage of the music all are born with. So how appropriate that the voice is fast emerging as streaming revolution. With fans consuming more than 100 billion the future of entertainment technology. streams of music in 2017 (audio and video), streaming has overtaken CD to become the dominant format in the music mix. The iTunes Store decoupled music buying from the disc; Spotify decoupled music access from ownership: now voice control frees music Smart speakers will undoubtedly give streaming a further boost, from the keyboard. In the process it promises music fans a more fluid attracting more casual listeners into subscription music services, as and personal relationship with the music they love. It also offers a real music is the killer app for these devices. solution to optimising streaming for the automobile. Playlists curated by streaming services are already an essential Naturally there are challenges too. The music industry has struggled to marketing channel for music, and their influence will only increase as deliver the metadata required in a digital music environment. -
Reuters Institute: the Future of Voice and the Implications for News
DIGITAL NEWS PROJECT NOVEMBER 2018 The Future of Voice and the Implications for News Nic Newman Contents About the Author 4 Acknowledgements 4 Executive Summary 5 1. Methodology and Approach 8 2. What is Voice? 10 3. How Voice is Being Used Today 14 4. News Usage in Detail 23 5. Publisher Strategies and Monetisation 32 6. Future Developments and Conclusions 40 References 43 Appendix: List of Interviewees 44 THE REUTERS INSTITUTE FOR THE STUDY OF JOURNALISM About the Author Nic Newman is Senior Research Associate at the Reuters Institute and lead author of the Digital News Report, as well as an annual study looking at trends in technology and journalism. He is also a consultant on digital media, working actively with news companies on product, audience, and business strategies for digital transition. Acknowledgements The author is particularly grateful to media companies and experts for giving their time to share insights for this report in such an enthusiastic and open way. Particular thanks, also, to Peter Stewart for his early encouragement and for his extremely informative daily Alexa ‘flash briefings’ on the ever changing voice scene. The author is also grateful to Differentology andY ouGov for the professionalism with which they carried out the qualitative and quantitative research respectively and for the flexibility in accommodating our complex and often changing requirements. The research team at the Reuters Institute provided valuable advice on methodology and content and the author is grateful to Lucas Graves and Rasmus Kleis Nielsen for their constructive and thoughtful comments on the manuscript. Also thanks to Alex Reid at the Reuters Institute for keeping the publication on track at all times. -

Understanding and Mitigating Security Risks of Voice-Controlled Third-Party Functions on Virtual Personal Assistant Systems
Dangerous Skills: Understanding and Mitigating Security Risks of Voice-Controlled Third-Party Functions on Virtual Personal Assistant Systems Nan Zhang∗, Xianghang Mi∗, Xuan Fengy∗, XiaoFeng Wang∗, Yuan Tianz and Feng Qian∗ ∗Indiana University, Bloomington Email: fnz3, xmi, xw7, [email protected] yBeijing Key Laboratory of IOT Information Security Technology, Institute of Information Engineering, CAS, China Email: [email protected] zUniversity of Virginia Email: [email protected] Abstract—Virtual personal assistants (VPA) (e.g., Amazon skills by Amazon and actions by Google1) to offer further Alexa and Google Assistant) today mostly rely on the voice helps to the end users, for example, order food, manage bank channel to communicate with their users, which however is accounts and text friends. In the past year, these ecosystems known to be vulnerable, lacking proper authentication (from the user to the VPA). A new authentication challenge, from the VPA are expanding at a breathtaking pace: Amazon claims that service to the user, has emerged with the rapid growth of the VPA already 25,000 skills have been uploaded to its skill market to ecosystem, which allows a third party to publish a function (called support its VPA (including the Alexa service running through skill) for the service and therefore can be exploited to spread Amazon Echo) [1] and Google also has more than one thousand malicious skills to a large audience during their interactions actions available on its market for its Google Home system with smart speakers like Amazon Echo and Google Home. In this paper, we report a study that concludes such remote, large- (powered by Google Assistant). -

View Annual Report
As filed with the Securities and Exchange Commission on March 29, 2019 UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 Form 20-F (Mark One) ‘ REGISTRATION STATEMENT PURSUANT TO SECTION 12(b) OR (g) OF THE SECURITIES EXCHANGE ACT OF 1934 OR È ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the fiscal year ended December 31, 2018 OR ‘ TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 OR ‘ SHELL COMPANY REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 Date of event requiring this shell company report For the transition period from to Commission file number 001-37821 LINE Kabushiki Kaisha (Exact name of Registrant as specified in its charter) LINE Corporation Japan (Translation of Registrant’s name into English) (Jurisdiction of incorporation or organization) JR Shinjuku Miraina Tower, 23rd Floor 4-1-6 Shinjuku Shinjuku-ku, Tokyo, 160-0022, Japan (Address of principal executive offices) Satoshi Yano Telephone: +81-3-4316-2050; E-mail: [email protected]; Facsimile: +81-3-4316-2131 (Name, telephone, e-mail and/or facsimile number and address of company contact person) Securities registered or to be registered pursuant to Section 12(b) of the Act. Title of Each Class Name of Each Exchange on Which Registered American Depositary Shares, each representing New York Stock Exchange, Inc. one share of common stock Common Stock * New York Stock Exchange, Inc. * Securities registered or to be registered pursuant to Section 12(g) of the Act. -

Remote Connect 2016
The Convenience of Remote Connect 2016 TOYOTA APP SMARTWATCH GOOGLE AMAZON Remote Connect As a Companion of the Smartphone ASSISTANT ALEXA Toyota Action Toyota Skill Toyota offers an incredible array of convenience and connectivity features. These features now includeGoogle Assistant and Amazon Alexa3 capability – as well as smartwatch integration – for 2018 and later models equipped with Remote Connect². KEY FOB WITH REMOTE FUNCTIONALITY Vehicles equipped with Remote Connect² have key fob13 compatibility for Remote Start1. Connected Services registration will be required to use the complete suite of Remote Connect services, which include Smartphone, Smartwatch, and smart home devices. Audio Plus vehicle key fob functionality is available for up to 3 years. Beyond 3 years requires a subscription. Applicable for select Model Year 2018 through 2020 Remote Connect capable vehicles. Select Model Year 2020 Remote Connect capable vehicles will have functionality for up to 10 years. Premium Audio vehicle key fob functionality is available for up to 10 years. Beyond 10 years requires a subscription. Applicable for select Model Year 2018 through 2020 Remote Connect capable vehicles. Using the key fob to remote start my Toyota: 1. Press the LOCK button on the remote. 2. Press the LOCK button a second time within 1 second. 3. Press the LOCK button again, this time holding it for 3 seconds. The engine will start. Note: Key Fob Remote Start will not function if Connected Services are waived. REMOTE CONNECT EQUIPPED VEHICLES BUILT BEFORE 11/12/18 Remote Connect equipped vehicles built before 11/12/18 were required to have an active Remote Connect trial or paid subscription for the key fob to perform remote start functionality. -
2019 Annual Report
2019 ANNUAL REPORT 1 2019 ANNUAL REPORT CONTENTS 2019 ANNUAL REPORT LETTER FROM THE PRESIDENT 3 SAMSUNG IN SPAIN 4 Milestones 4 Results 5 SAMSUNG IN THE WORLD 6 OUR PHILOSOPHY 8 SUSTAINABLE DEVELOPMENT-ORIENTED 10 DRIVING... 14 The Economy 14 Innovation 22 Society: Technology With Purpose 30 CHALLENGES FOR THE FUTURE 38 2 2019 ANNUAL REPORT LETTER FROM THE PRESIDENT LETTER FROM We’ve developed flexible displays and continue to be committed to 5G, Artificial Intelligence and IoT in addition to 8K technology which positions us as THE PRESIDENT leaders in innovation Greetings, nowadays, there has been ecosystem, not to mention how cultural institutions such as the sustained growth over the safety is the main concern Prado Museum, the National Samsung Electronics, the last three years in these three and responsibility with all Archaeological Museum company I preside over in Spain indicators. Our commitment to our developments. The latest and the Royal Theatre with and Portugal, has again issued contribute beyond our income example is our commitment to progress that proves just its Annual Report concerning statement not only continues 8K for the screens of the future how technology can make a our business activities in 2019. to be strong, it’s increasing and which in our case are already a difference. What’s more, we This is the third report we’ve this is because of the efforts reality in many homes. continue to support public published in Spain and we’re and enthusiasm shown by all of schools all over Spain by quite proud because it helps us who are a part of Samsung. -

Digital Forensic Analysis of Smart Watches
TALLINN UNIVERSITY OF TECHNOLOGY School of Information Technologies Kehinde Omotola Adebayo (174449IVSB) DIGITAL FORENSIC ANALYSIS OF SMART WATCHES Bachelor’s Thesis Supervisor: Hayretdin Bahsi Research Professor Tallinn 2020 TALLINNA TEHNIKAÜLIKOOL Infotehnoloogia teaduskond Kehinde Omotola Adebayo (174449IVSB) NUTIKELLADE DIGITAALKRIMINALISTIKA Bachelor’s Thesis Juhendaja: Hayretdin Bahsi Research Professor Tallinn 2020 Author’s declaration of originality I hereby certify that I am the sole author of this thesis. All the used materials, references to the literature and the work of others have been referred to. This thesis has not been presented for examination anywhere else. Author: Kehinde Omotola Adebayo 30.04.2020 3 Abstract As wearable technology is becoming increasingly popular amongst consumers and projected to continue to increase in popularity they become probable significant source of digital evidence. One category of wearable technology is smart watches and they provide capabilities to receive instant messaging, SMS, email notifications, answering of calls, internet browsing, fitness tracking etc. which can be a great source of digital artefacts. The aim of this thesis is to analyze Samsung Gear S3 Frontier and Fitbit Versa Smartwatches, after which we present findings alongside the limitations encountered. Our result shows that we can recover significant artefacts from the Samsung Gear S3 Frontier, also more data can be recovered from Samsung Gear S3 Frontier than the accompanying mobile phone. We recovered significant data that can serve as digital evidence, we also provided a mapping that would enable investigators and forensic examiners work faster as they are shown where to look for information in the course of an investigation. We also presented the result of investigating Fitbit Versa significant artefacts like Heart rate, sleep, exercise and personal data like age, weight and height of the user of the device, this shows this device contains artefacts that might prove useful for forensic investigators and examiners. -

Adattester: Secure Online Mobile Advertisement Attestation Using Trustzone
AdAttester: Secure Online Mobile Advertisement Attestation Using TrustZone Wenhao Li, Haibo Li, Haibo Chen, Yubin Xia Institute of Parallel and Distributed Systems Shanghai Jiao Tong University ABSTRACT 1billiondollarsin2013duetothesefraudsandaroundonethird Mobile advertisement (ad for short) is a major financial pillar for of mobile ad clicks may constitute click-spam [18]. The most re- developers to provide free mobile apps. However, it is frequently cent research study [33] shows that, one of the largest click fraud thwarted by ad fraud, where rogue code tricks ad providers by forg- botnets, called ZeroAccess, induces advertising losses on the or- ing ad display or user clicks, or both. With the mobile ad market der of $100,000 per day. Ad frauds can typically be characterized growing drastically (e.g., from $8.76 billion in 2012 to $17.96 bil- into two types [26]: (1) Bot-driven frauds employ bot networks to lion in 2013), it is vitally important to provide a verifiable mobile initiate forged ad impressions and clicks; (2) Interaction frauds ma- ad framework to detect and prevent ad frauds. Unfortunately,this nipulate visual layouts of ads to trigger ad impressions and unaware is notoriously hard as mobile ads usually run in an execution envi- clicks from the end users. ronment with a huge TCB. Because of the urgent need to detecting mobile ad frauds, prior This paper proposes a verifiable mobile ad framework called approaches have made important first steps by using an offline- AdAttester, based on ARM’s TrustZone technology. AdAttester based approach [16, 26]. Specifically, they trigger the execution provides two novel security primitives, namely unforgeable clicks of mobile apps in a controlled environment to observe deviated and verifiable display.Thetwoprimitivesattestthatad-relatedop- behavior to detect ad frauds. -

Erp Modernization & Consolidation
ERP MODERNIZATION & CONSOLIDATION CASE STUDY CUSTOMER CONTEXT SUMMARY A global industrial manufacturing company was • Templatized implementation & rollout approach for rapid implementation running a legacy ERP for critical operations in supply across 54 entities in 26 months. chain, financial controlling & management incurring increasing maintenance costs & bandaging huge • ‘Process Templates’ for standardizations & synergies across processes. customization components to cover the process gaps • Optimal resources alignment in onshore-offshore mix with technical & making the adoption of a modern ERP challenges. business functions stream. PROJECT BACKGROUND SOLUTION BENEFITS • Project planned for 54 distinct entities across • Single Source of Truth across demand planning & forecasting, supply chain 22 countries. operations & financial controlling & management. • Plans executed for complex organizational • Consolidation of multiple manufacturing modes of process, discrete, structure of customer teams across entity configure to order, made to order, engineer to order. locations & shared-services based on operational • Seamless integration of B2B order management system with SAP Hybris. streams of ‘factory’, ‘distribution’, ‘sales’ & ‘finance’. PARTNER WITH AN INDUSTRY EXPERT • Integrated execution of sunsetting 5 ERP systems HARMAN (harman.com) designs and engineers & multiple satellite applications on a single ERP TOOLS / TECHNOLOGIES connected products and solutions for automakers, platform delivering post-modern application consumers, -

HKTS 9/16 Home Theater Speaker System
HKTS 9/16 Home Theater Speaker System User Guide English HKTS 9/16 Home-Theater System Owner’s Manual Table of Contents Introduction .....................................................3 Description and Features .........................................3 HKTS200SUB Subwoofer Rear-Panel Connections. 4 Speaker Placement ...............................................5 Mounting Options ................................................5 Speaker Connections .............................................6 Operation .......................................................10 Troubleshooting. .10 Specifications ...................................................11 Important Safety Instructions Please read the following precautions before use: 1. Read these instructions. 13. Unplug this apparatus during lightning storms or when unused for long periods of time. 2. Keep these instructions. 14. Refer all servicing to qualified service personnel. Servicing is required when the apparatus has been damaged in any way, such as power supply cord or plug is damaged, liquid has been 3. Heed all warnings. spilled or objects have fallen into the apparatus, the apparatus has been exposed to rain or 4. Follow all instructions. moisture, does not operate normally, or has been dropped. 5. Do not use this apparatus near water. 15. Do not expose this apparatus to dripping or splashing and ensure that no objects filled with liquids, such as vases, are placed on the apparatus. 6. Clean only with a dry cloth. 16. To completely disconnect this apparatus from the AC Mains, disconnect the power supply 7. Do not block any ventilation openings. Install in accordance with the manufacturer’s cord plug from the AC receptacle. instructions. 17. The mains plug of the power supply cord shall remain readily operable. 8. Do not install near any heat sources such as radiators, heat registers, stoves or other apparatus (including amplifiers) that produce heat. 18. Do not expose batteries to excessive heat such as sunshine, fire or the like.