Singularity Container Documentation Release 3.6
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Oracle® Linux Administrator's Solutions Guide for Release 6
Oracle® Linux Administrator's Solutions Guide for Release 6 E37355-64 August 2017 Oracle Legal Notices Copyright © 2012, 2017, Oracle and/or its affiliates. All rights reserved. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs, including any operating system, integrated software, any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and adaptation of the programs, including any operating system, integrated software, any programs installed on the hardware, and/or documentation, shall be subject to license terms and license restrictions applicable to the programs. No other rights are granted to the U.S. -

Industrial Control Via Application Containers: Migrating from Bare-Metal to IAAS
Industrial Control via Application Containers: Migrating from Bare-Metal to IAAS Florian Hofer, Student Member, IEEE Martin A. Sehr Antonio Iannopollo, Member, IEEE Faculty of Computer Science Corporate Technology EECS Department Free University of Bolzano-Bozen Siemens Corporation University of California Bolzano, Italy Berkeley, CA 94704, USA Berkeley, CA 94720, USA fl[email protected] [email protected] [email protected] Ines Ugalde Alberto Sangiovanni-Vincentelli, Fellow, IEEE Barbara Russo Corporate Technology EECS Department Faculty of Computer Science Siemens Corporation University of California Free University of Bolzano-Bozen Berkeley, CA 94704, USA Berkeley, CA 94720, USA Bolzano, Italy [email protected] [email protected] [email protected] Abstract—We explore the challenges and opportunities of control design full authority over the environment in which shifting industrial control software from dedicated hardware to its software will run, it is not straightforward to determine bare-metal servers or cloud computing platforms using off the under what conditions the software can be executed on cloud shelf technologies. In particular, we demonstrate that executing time-critical applications on cloud platforms is viable based on computing platforms due to resource virtualization. Yet, we a series of dedicated latency tests targeting relevant real-time believe that the principles of Industry 4.0 present a unique configurations. opportunity to explore complementing traditional automation Index Terms—Industrial Control Systems, Real-Time, IAAS, components with a novel control architecture [3]. Containers, Determinism We believe that modern virtualization techniques such as application containerization [3]–[5] are essential for adequate I. INTRODUCTION utilization of cloud computing resources in industrial con- Emerging technologies such as the Internet of Things and trol systems. -
Portability: Containers, Cloud
JEDI Portability Across Platforms Containers, Cloud Computing, and HPC Mark Miesch, Rahul Mahajan, Xin Zhang, David Hahn, Francois Vandenberg, Jim Rosinski, Dan Holdaway, Yannick Tremolet, Maryam Abdioskouei, Steve Herbener, Mark Olah, Benjamin Menetrier, Anna Shlyaeva, Clementine Gas Academy website http://academy.jcsda.org/june2019 ‣ Instructions for accessing AWS ‣ Activity instructions ‣ Presentation slides ‣ Doxygen documentation for fv3-bundle We will add further content throughout the week Outline I) JEDI Portability Overview ✦ Unified vision for software development and distribution II) Container Fundamentals ✦ What are they? How do they work? ✦ Docker, Charliecloud, and Singularity III) Using the JEDI Containers ✦ How they are built and deployed ✦ Mac and Windows (Vagrant) IV) HPC and Cloud Computing ✦ Environment modules ✦ Containers in HPC? V) Summary and Outlook JEDI Software Dependencies ‣ Essential ✦ Compilers, MPI ✦ CMake Common versions among users ✦ SZIP, ZLIB and developers minimize ✦ LAPACK / MKL, Eigen 3 stack-related debugging ✦ NetCDF4, HDF5 ✦ udunits ✦ Boost (headers only) ✦ ecbuild, eckit, fckit ‣ Useful ✦ ODB-API, eccodes ✦ PNETCDF ✦ Parallel IO ✦ nccmp, NCO ✦ Python tools (py-ncepbufr, netcdf4, matplotlib…) ✦ NCEP libs ✦ Debuggers & Profilers (ddt/TotalView, kdbg, valgrind, TAU…) The JEDI Portability Vision I want to run JEDI on… Development ‣ My Laptop/Workstation/PC ✦ We provide software containers ✦ Mac & Windows system need to first establish a linux environment (e.g. a Vagrant/VirtualBox virtual machine) Development -

TEE Internal Core API Specification V1.1.2.50
GlobalPlatform Technology TEE Internal Core API Specification Version 1.1.2.50 (Target v1.2) Public Review June 2018 Document Reference: GPD_SPE_010 Copyright 2011-2018 GlobalPlatform, Inc. All Rights Reserved. Recipients of this document are invited to submit, with their comments, notification of any relevant patents or other intellectual property rights (collectively, “IPR”) of which they may be aware which might be necessarily infringed by the implementation of the specification or other work product set forth in this document, and to provide supporting documentation. The technology provided or described herein is subject to updates, revisions, and extensions by GlobalPlatform. This documentation is currently in draft form and is being reviewed and enhanced by the Committees and Working Groups of GlobalPlatform. Use of this information is governed by the GlobalPlatform license agreement and any use inconsistent with that agreement is strictly prohibited. TEE Internal Core API Specification – Public Review v1.1.2.50 (Target v1.2) THIS SPECIFICATION OR OTHER WORK PRODUCT IS BEING OFFERED WITHOUT ANY WARRANTY WHATSOEVER, AND IN PARTICULAR, ANY WARRANTY OF NON-INFRINGEMENT IS EXPRESSLY DISCLAIMED. ANY IMPLEMENTATION OF THIS SPECIFICATION OR OTHER WORK PRODUCT SHALL BE MADE ENTIRELY AT THE IMPLEMENTER’S OWN RISK, AND NEITHER THE COMPANY, NOR ANY OF ITS MEMBERS OR SUBMITTERS, SHALL HAVE ANY LIABILITY WHATSOEVER TO ANY IMPLEMENTER OR THIRD PARTY FOR ANY DAMAGES OF ANY NATURE WHATSOEVER DIRECTLY OR INDIRECTLY ARISING FROM THE IMPLEMENTATION OF THIS SPECIFICATION OR OTHER WORK PRODUCT. Copyright 2011-2018 GlobalPlatform, Inc. All Rights Reserved. The technology provided or described herein is subject to updates, revisions, and extensions by GlobalPlatform. -

Domain Tips and Tricks Lab
Installing a Domain Service for Windows: Domain Tips and Tricks Lab Novell Training Services www.novell.com OES10 ATT LIVE 2012 LAS VEGAS Novell, Inc. Copyright 2012-ATT LIVE-1-HARDCOPY PERMITTED. NO OTHER PRINTING, COPYING, OR DISTRIBUTION ALLOWED. Legal Notices Novell, Inc., makes no representations or warranties with respect to the contents or use of this documentation, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc., reserves the right to revise this publication and to make changes to its content, at any time, without obligation to notify any person or entity of such revisions or changes. Further, Novell, Inc., makes no representations or warranties with respect to any software, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc., reserves the right to make changes to any and all parts of Novell software, at any time, without any obligation to notify any person or entity of such changes. Any products or technical information provided under this Agreement may be subject to U.S. export controls and the trade laws of other countries. You agree to comply with all export control regulations and to obtain any required licenses or classification to export, re-export or import deliverables. You agree not to export or re-export to entities on the current U.S. export exclusion lists or to any embargoed or terrorist countries as specified in the U.S. export laws. You agree to not use deliverables for prohibited nuclear, missile, or chemical biological weaponry end uses. -

Show Command Output Redirection
show Command Output Redirection The show Command Output Redirection feature provides the capability to redirect output from Cisco IOS command-line interface (CLI) show commands and more commands to a file. • Finding Feature Information, page 1 • Information About show Command Output Redirection, page 1 • How to Use the show Command Enhancement, page 2 • Additional References, page 2 • Feature Information for show Command Output Redirection, page 3 Finding Feature Information Your software release may not support all the features documented in this module. For the latest caveats and feature information, see Bug Search Tool and the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the feature information table at the end of this module. Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required. Information About show Command Output Redirection This feature enhances the show commands in the Cisco IOS CLI to allow large amounts of data output to be written directly to a file for later reference. This file can be saved on local or remote storage devices such as Flash, a SAN Disk, or an external memory device. For each show command issued, a new file can be created, or the output can be appended to an existing file. Command output can optionally be displayed on-screen while being redirected to a file by using the tee keyword. -
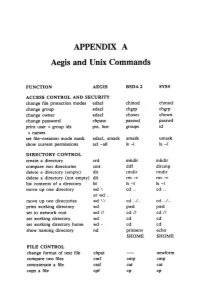
APPENDIX a Aegis and Unix Commands
APPENDIX A Aegis and Unix Commands FUNCTION AEGIS BSD4.2 SYSS ACCESS CONTROL AND SECURITY change file protection modes edacl chmod chmod change group edacl chgrp chgrp change owner edacl chown chown change password chpass passwd passwd print user + group ids pst, lusr groups id +names set file-creation mode mask edacl, umask umask umask show current permissions acl -all Is -I Is -I DIRECTORY CONTROL create a directory crd mkdir mkdir compare two directories cmt diff dircmp delete a directory (empty) dlt rmdir rmdir delete a directory (not empty) dlt rm -r rm -r list contents of a directory ld Is -I Is -I move up one directory wd \ cd .. cd .. or wd .. move up two directories wd \\ cd . ./ .. cd . ./ .. print working directory wd pwd pwd set to network root wd II cd II cd II set working directory wd cd cd set working directory home wd- cd cd show naming directory nd printenv echo $HOME $HOME FILE CONTROL change format of text file chpat newform compare two files emf cmp cmp concatenate a file catf cat cat copy a file cpf cp cp Using and Administering an Apollo Network 265 copy std input to std output tee tee tee + files create a (symbolic) link crl In -s In -s delete a file dlf rm rm maintain an archive a ref ar ar move a file mvf mv mv dump a file dmpf od od print checksum and block- salvol -a sum sum -count of file rename a file chn mv mv search a file for a pattern fpat grep grep search or reject lines cmsrf comm comm common to 2 sorted files translate characters tic tr tr SHELL SCRIPT TOOLS condition evaluation tools existf test test -
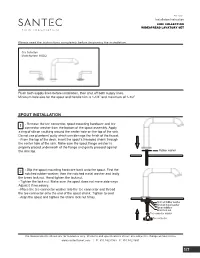
Installation Instruction
Rev 1/2020 Installation Instruction Please read the instructions completely before beginning the installation. Circ Collection Model Number: 3920CI Flush both supply lines before installation, then shut off both supply lines. Minimum hole size for the spout and handle trim is 1-1/4” and maximum of 1-1/2” SPOUT INSTALLATION 1 - Remove the tee connector, spout mounting hardware and tee connector washer from the bottom of the spout assembly. Apply a ring of silicon caulking around the center hole on the top of the sink. Do not use plumbers' putty which can damage the finish of the faucet. - From the top of the deck, insert the spout's threaded shank through the center hole of the sink. Make sure the spout flange washer is properly placed underneath of the flange and gently pressed against the sink top. Rubber washer 2 - Slip the spout mounting hardware back onto the spout. First the notched rubber washer, then the notched metal washer and lastly the brass lock nut. Hand tighten the lock nut. - Tighten the lock nut. Make sure the spout does not move side ways Adjust it if necessary. - Place the tee connector washer into the tee connector and thread the tee connector onto the end of the spout shank. Tighten to seal. - Align the spout and tighten the shank lock nut firmly. Notched rubber washer Notched metal washer Spout stabilizer Brass lock nut Tee connector washer Tee connector The measurements shown are for reference only. Products and specifications shown are subject to change without notice. www.santecfaucet.com | P: 310.542.0063 F: 310.542.5681 1/7 HANDLE TRIM INSTALLATION DO NOT DISASSEMBLE HANDLE ASSEMBLY - DROP-IN VALVES 1 - Both hot and cold side handle trims are pre-assmbled for faster installation. -

Keep TEE Probe Care Top-Of-Mind
Keep TEE Probe Care Top-Of-Mind Three Ways to Prevent Catastrophic TEE Probe Failures 1. Perform Frequent Quality Visual Inspections • When removed from storage • During removal • Before soaking in disinfectant • When set-up and connected to the scanner • After removal • After soaking in disinfectant • Before insertion • During pre-cleaning • Before storing 2. Perform Frequent and Time-based Leakage Testing Frequent • After EVERY patient exam, following a thorough visual inspection, under magnification, and prior to lengthy soak in disinfectant Time-based • Test once at the beginning of the soak cycle and once again at the end in order to reveal intermittent, slow leaks (the beginning of hard, catastrophic failures) 3. Establish a TEE Probe Preventative Maintenance Program • Address wearable items before they can contribute to larger, costly failures • Restore optimal performance and maintain uptime • Extend TEE probe lifecycyle • Suggested Intervals: • Bending rubber replacement - every 6-12 months • Articulation adjustment - every 6-12 months • Re-coating/re-labeling - every 12-18 months Industry Best-Practices for TEE Probe Care and Handling • Always use a protective tip cover when the probe is outside of the patient • Always transport TEE probes in covered bins • Don't coil the insertion tube in less than a 12-inch diameter • Use a TEE bite guard on every patient • Anytime a probe changes hands, perform a quick visual inspection of the tip, bending section and insertion tube. See below • Thoroughly inspect the tip and bending section, -

Oracle® Linux 7 Working with LXC
Oracle® Linux 7 Working With LXC F32445-02 October 2020 Oracle Legal Notices Copyright © 2020, Oracle and/or its affiliates. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial computer software" or "commercial computer software documentation" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, reproduction, duplication, release, display, disclosure, modification, preparation of derivative works, and/or adaptation of i) Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs), ii) Oracle computer documentation and/or iii) other Oracle data, is subject to the rights and limitations specified in the license contained in the applicable contract. -

Readahead: Time-Travel Techniques for Desktop and Embedded Systems
Readahead: time-travel techniques for desktop and embedded systems Michael Opdenacker Free Electrons [email protected] Abstract 1.2 Reading ahead Readahead techniques have successfully been used to The idea of reading ahead is to speed up the access to reduce boot time in recent GNU/Linux distributions like a file by preloading at least parts of its contents in page Fedora Core or Ubuntu. However, in embedded sys- cache ahead of time. This can be done when spare I/O tems with scarce RAM, starting a parallel thread read- resources are available, typically when tasks keep the ing ahead all the files used in system startup is no longer processor busy. Of course, this requires the ability to appropriate. The cached pages could be reclaimed even predict the future! before accessing the corresponding files. Fortunately, the systems we are dealing with are pre- This paper will first guide you through the heuristics dictable or even totally predictable in some situations! implemented in kernelspace, as well as through the userspace interface for preloading files or just announc- ing file access patterns. Desktop implementations will • Predictions by watching file read patterns. If pages be explained and benchmarked. We will then detail Free are read from a file in a sequential manner, it makes Electrons’ attempts to implement an easy to integrate sense to go on reading the next blocks in the file, helper program reading ahead files at the most appropri- even before these blocks are actually requested. ate time in the execution flow. • System startup. The system init sequence doesn’t This paper and the corresponding presentation target change. -

Beyond Init: Systemd Linux Plumbers Conference 2010
Beyond Init: systemd Linux Plumbers Conference 2010 Kay Sievers Lennart Poettering November 2010 Kay Sievers, Lennart Poettering Beyond Init: systemd Triggers: Boot, Socket, Bus, Device, Path, Timers, More Kay Sievers, Lennart Poettering Beyond Init: systemd Kay Sievers, Lennart Poettering Beyond Init: systemd Substantial coverage of basic OS boot-up tasks, including fsck, mount, quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Kay Sievers, Lennart Poettering Beyond Init: systemd including fsck, mount, quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, Kay Sievers, Lennart Poettering Beyond Init: systemd mount, quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, including fsck, Kay Sievers, Lennart Poettering Beyond Init: systemd quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, including fsck, mount, Kay Sievers, Lennart Poettering Beyond Init: systemd hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, including fsck, mount, quota, Kay Sievers, Lennart Poettering Beyond Init: systemd readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots.