An Exploration of Artefacts of Remote Desktop Applications on Windows
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
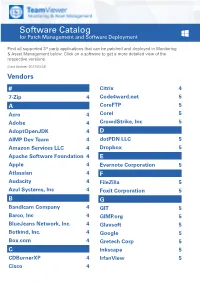
Software Catalog for Patch Management and Software Deployment
Software Catalog for Patch Management and Software Deployment Find all supported 3rd party applications that can be patched and deployed in Monitoring & Asset Management below. Click on a software to get a more detailed view of the respective versions. (Last Update: 2021/03/23) Vendors # Citrix 4 7-Zip 4 Code4ward.net 5 A CoreFTP 5 Acro 4 Corel 5 Adobe 4 CrowdStrike, Inc 5 AdoptOpenJDK 4 D AIMP Dev Team 4 dotPDN LLC 5 Amazon Services LLC 4 Dropbox 5 Apache Software Foundation 4 E Apple 4 Evernote Corporation 5 Atlassian 4 F Audacity 4 FileZilla 5 Azul Systems, Inc 4 Foxit Corporation 5 B G Bandicam Company 4 GIT 5 Barco, Inc 4 GIMP.org 5 BlueJeans Network, Inc. 4 Glavsoft 5 Botkind, Inc. 4 Google 5 Box.com 4 Gretech Corp 5 C Inkscape 5 CDBurnerXP 4 IrfanView 5 Cisco 4 Software Catalog for Patch Management and Software Deployment J P Jabra 5 PeaZip 10 JAM Software 5 Pidgin 10 Juraj Simlovic 5 Piriform 11 K Plantronics, Inc. 11 KeePass 5 Plex, Inc 11 L Prezi Inc 11 LibreOffice 5 Programmer‘s Notepad 11 Lightning UK 5 PSPad 11 LogMeIn, Inc. 5 Q M QSR International 11 Malwarebytes Corporation 5 Quest Software, Inc 11 Microsoft 6 R MIT 10 R Foundation 11 Morphisec 10 RarLab 11 Mozilla Foundation 10 Real 11 N RealVNC 11 Neevia Technology 10 RingCentral, Inc. 11 NextCloud GmbH 10 S Nitro Software, Inc. 10 Scooter Software, Inc 11 Nmap Project 10 Siber Systems 11 Node.js Foundation 10 Simon Tatham 11 Notepad++ 10 Skype Technologies S.A. -

Realvnc @ LC August 2018 LC User Meeting
RealVNC @ LC August 2018 LC User Meeting Cameron Harr Title (optional) Aug. 21, 2018 LLNL-PRES-XXXXXX This work was performed under the auspices of the U.S. Department of Energy by Lawrence Livermore National Laboratory under contract DE-AC52-07NA27344. Lawrence Livermore National Security, LLC RealVNC @ LC § What is RealVNC? § What did we have? § What do we have now? § What’s coming in the future? § How do you use it? 2 LLNL-PRES-xxxxxx Cloud versus direct with VNC Connect VNC Connect is unique among remote access software in its ability to offer both cloud and direct connectivity methods within a single product. At first glance, knowing whether to connect directly or via our cloud service can seem confusing. However, there are clear benefits to each connection method. The trick is knowing how to maximize these benefits. This brief product guide provides an overview of the differences between cloud and direct connectivity, and offers some advice on how each method can be used to your greatest advantage. Key terminology Throughout this guide, we refer to certain RealVNC-specific terminology. VNC Connect is comprised of two separate apps: VNC Server and VNC Viewer. You must install and license VNC Server on the computer you want to control. This is known as your VNC Server computer. You must then install VNC Viewer on the computer or device you want to take control from, which is known as your VNC Viewer device. You do not need to license this device, meaning you can freely connect to your VNC Server computer from as many devices as you wish. -

VNC Connect Security Whitepaper
VNC Connect security whitepaper VNC Connect security whitepaper Version 1.3 Contents Contents .................................................................................................................................................................... 2 Introduction ............................................................................................................................................................... 3 Security architecture ................................................................................................................................................. 4 Cloud infrastructure ................................................................................................................................................... 7 Client security ........................................................................................................................................................... 9 Development procedures ........................................................................................................................................ 12 Summary ................................................................................................................................................................. 13 VNC Connect security whitepaper Introduction Customer security is of paramount importance to RealVNC. As such, our security strategy is ingrained in all aspects of our VNC Connect software. We have invested extensively in our security, and take great pride in our successful -

Institutionen För Datavetenskap Department of Computer and Information Science
Institutionen för datavetenskap Department of Computer and Information Science Final thesis Implementing extended functionality for an HTML5 client for remote desktops by Samuel Mannehed LIU-IDA/LITH-EX-A—14/015--SE 6/28/14 Linköpings universitet Linköpings universitet SE-581 83 Linköping, Sweden 581 83 Linköping Final thesis Implementing extended functionality for an HTML5 client for remote desktops by Samuel Mannehed LIU-IDA/LITH-EX-A--14/015--SE June 28, 2014 Supervisors: Peter Åstrand (Cendio AB), Maria Vasilevskaya (IDA) Examiner: Prof. Simin Nadjm-Tehrani På svenska Detta dokument hålls tillgängligt på Internet – eller dess framtida ersättare – under en längre tid från publiceringsdatum under förutsättning att inga extra-ordinära omständigheter uppstår. Tillgång till dokumentet innebär tillstånd för var och en att läsa, ladda ner, skriva ut enstaka kopior för enskilt bruk och att använda det oförändrat för ickekommersiell forskning och för undervisning. Överföring av upphovsrätten vid en senare tidpunkt kan inte upphäva detta tillstånd. All annan användning av dokumentet kräver upphovsmannens medgivande. För att garantera äktheten, säkerheten och tillgängligheten finns det lösningar av teknisk och administrativ art. Upphovsmannens ideella rätt innefattar rätt att bli nämnd som upphovsman i den omfattning som god sed kräver vid användning av dokumentet på ovan beskrivna sätt samt skydd mot att dokumentet ändras eller presenteras i sådan form eller i sådant sammanhang som är kränkande för upphovsmannens litterära eller konstnärliga anseende eller egenart. För ytterligare information om Linköping University Electronic Press se förlagets hemsida http://www.ep.liu.se/ In English The publishers will keep this document online on the Internet - or its possible replacement - for a considerable time from the date of publication barring exceptional circumstances. -

Accessing Remote Desktop Using VNC on Dell Poweredge Servers
Accessing Remote Desktop using VNC on Dell PowerEdge Servers and MX7000 Modular Infrastructure This technical white paper provides information about establishing secure remote desktop connections to server host operating systems (OS) by using the standard VNC clients. Abstract Dell EMC PowerEdge servers support efficient and secure remote management tools. Virtual Network Computing (VNC) technology is incorporated in the iDRAC Enterprise firmware to support open and easy-to-use remote desktop functionality. This functionality is in addition to the browser-based remote console support accessible on the iDRAC GUI. September 2018 Dell EMC Technical White Paper Revisions Revisions Date Description Sep 2018 Initial release Acknowledgements This paper was produced by the following members of the Dell EMC Server and Infrastructure Systems team: Authors Saurabh Kishore — Software Principal Engineer Alex Rote — Software Senior Engineer The information in this publication is provided “as is.” Dell Inc. makes no representations or warranties of any kind with respect to the information in this publication, and specifically disclaims implied warranties of merchantability or fitness for a particular purpose. Use, copying, and distribution of any software described in this publication requires an applicable software license. © <Sep/12/2018> Dell Inc. or its subsidiaries. All Rights Reserved. Dell, EMC, Dell EMC and other trademarks are trademarks of Dell Inc. or its subsidiaries. Other trademarks may be trademarks of their respective owners. Dell believes the information in this document is accurate as of its publication date. The information is subject to change without notice. 2 Accessing Remote Desktop using VNC on Dell PowerEdge Servers and MX7000 Modular Infrastructure Acknowledgements Contents Revisions............................................................................................................................................................................ -

Working from Home Efficiently, Ethically and Securely by Sharon D
Working From Home Efficiently, Ethically and Securely by Sharon D. Nelson, Esq., John W. Simek and Michael C. Maschke © 2020 Sensei Enterprises, Inc. The world is trying to deal with the COVID-19 in a variety of ways. Controlling the spread of the deadly virus is at the top of the list. Travel is being restricted, and some countries have even closed their borders. The United States was slow to react, but eventually states imposed restrictions for business operations to reduce the coronavirus spread and then began re-opening in phases. Social distancing and maintaining clean hygiene practices are the normal mode of operation now. More and more businesses are allowing their employees to stay at home where possible. What does that mean for the practice of law? How will you meet with clients? Most firms have adopted a telework environment and allow their employees to work from home, even while some firms have begun re-opening. Working from home has different consequences depending on your current capabilities and whether a plan is already in place. While we can’t cover all the possibilities and capabilities of every law firm, we’ll attempt to attack some of the common considerations. Equipment Let’s start with a very basic item…the computer. Hopefully, everyone is already using a laptop as their main office machine. As expected, some popular models of laptops are still in short supply. Worst case, you may have to find a Best Buy, Target, Walmart, etc. and see if you can purchase a consumer-grade machine. If you planned properly, laptop users are already configured for remote access. -
VNC User Guide 7 About This Guide
VNC® User Guide Version 5.3 December 2015 Trademarks RealVNC, VNC and RFB are trademarks of RealVNC Limited and are protected by trademark registrations and/or pending trademark applications in the European Union, United States of America and other jursidictions. Other trademarks are the property of their respective owners. Protected by UK patent 2481870; US patent 8760366 Copyright Copyright © RealVNC Limited, 2002-2015. All rights reserved. No part of this documentation may be reproduced in any form or by any means or be used to make any derivative work (including translation, transformation or adaptation) without explicit written consent of RealVNC. Confidentiality All information contained in this document is provided in commercial confidence for the sole purpose of use by an authorized user in conjunction with RealVNC products. The pages of this document shall not be copied, published, or disclosed wholly or in part to any party without RealVNC’s prior permission in writing, and shall be held in safe custody. These obligations shall not apply to information which is published or becomes known legitimately from some source other than RealVNC. Contact RealVNC Limited Betjeman House 104 Hills Road Cambridge CB2 1LQ United Kingdom www.realvnc.com Contents About This Guide 7 Chapter 1: Introduction 9 Principles of VNC remote control 10 Getting two computers ready to use 11 Connectivity and feature matrix 13 What to read next 17 Chapter 2: Getting Connected 19 Step 1: Ensure VNC Server is running on the host computer 20 Step 2: Start VNC -
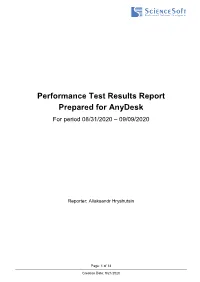
Test Result Report for Anydesk
Performance Test Results Report Prepared for AnyDesk For period 08/31/2020 – 09/09/2020 Reporter: Aliaksandr Hryshutsin Page: 1 of 13 Creation Date: 9/21/2020 Contents 1 Testing Approach ........................................................................................................................................... 3 1.1 Types of Tests ......................................................................................................................................... 3 1.2 Test set-up ............................................................................................................................................... 3 2 Summary on Test Results .............................................................................................................................. 4 2.1 Summary ................................................................................................................................................. 4 3 Test results ..................................................................................................................................................... 4 3.1 Framerate ................................................................................................................................................ 4 3.2 Latency .................................................................................................................................................... 5 3.3 Bandwidth ............................................................................................................................................... -

List of NMAP Scripts Use with the Nmap –Script Option
List of NMAP Scripts Use with the nmap –script option Retrieves information from a listening acarsd daemon. Acarsd decodes ACARS (Aircraft Communication Addressing and Reporting System) data in real time. The information retrieved acarsd-info by this script includes the daemon version, API version, administrator e-mail address and listening frequency. Shows extra information about IPv6 addresses, such as address-info embedded MAC or IPv4 addresses when available. Performs password guessing against Apple Filing Protocol afp-brute (AFP). Attempts to get useful information about files from AFP afp-ls volumes. The output is intended to resemble the output of ls. Detects the Mac OS X AFP directory traversal vulnerability, afp-path-vuln CVE-2010-0533. Shows AFP server information. This information includes the server's hostname, IPv4 and IPv6 addresses, and hardware type afp-serverinfo (for example Macmini or MacBookPro). Shows AFP shares and ACLs. afp-showmount Retrieves the authentication scheme and realm of an AJP service ajp-auth (Apache JServ Protocol) that requires authentication. Performs brute force passwords auditing against the Apache JServ protocol. The Apache JServ Protocol is commonly used by ajp-brute web servers to communicate with back-end Java application server containers. Performs a HEAD or GET request against either the root directory or any optional directory of an Apache JServ Protocol ajp-headers server and returns the server response headers. Discovers which options are supported by the AJP (Apache JServ Protocol) server by sending an OPTIONS request and lists ajp-methods potentially risky methods. ajp-request Requests a URI over the Apache JServ Protocol and displays the result (or stores it in a file). -

Unpermitted Resources
Process Check and Unpermitted Resources Common and Important Virtual Machines Parallels VMware VirtualBox CVMCompiler Windows Virtual PC Other Python Citrix Screen/File Sharing/Saving .exe File Name VNC, VPN, RFS, P2P and SSH Virtual Drives ● Dropbox.exe ● Dropbox ● OneDrive.exe ● OneDrive ● <name>.exe ● Google Drive ● etc. ● iCloud ● etc. Evernote / One Note ● Evernote_---.exe ● onenote.exe Go To Meeting ● gotomeeting launcher.exe / gotomeeting.exe TeamViewer ● TeamViewer.exe Chrome Remote ● remoting_host.exe www.ProctorU.com ● [email protected] ● 8883553043 Messaging / Video (IM, IRC) / .exe File Name Audio Bonjour Google Hangouts (chrome.exe - shown as a tab) (Screen Sharing) Skype SkypeC2CPNRSvc.exe Music Streaming ● Spotify.exe (Spotify, Pandora, etc.) ● PandoraService.exe Steam Steam.exe ALL Processes Screen / File Sharing / Messaging / Video (IM, Virtual Machines (VM) Other Saving IRC) / Audio Virtual Box Splashtop Bonjour ● iChat ● iTunes ● iPhoto ● TiVo ● SubEthaEdit ● Contactizer, ● Things ● OmniFocuse phpVirtualBox TeamViewer MobileMe Parallels Sticky Notes Team Speak VMware One Note Ventrilo Windows Virtual PC Dropbox Sandboxd QEM (Linux only) Chrome Remote iStumbler HYPERBOX SkyDrive MSN Chat Boot Camp (dual boot) OneDrive Blackboard Chat CVMCompiler Google Drive Yahoo Messenger Office (Word, Excel, Skype etc.) www.ProctorU.com ● [email protected] ● 8883553043 2X Software Notepad Steam AerooAdmin Paint Origin AetherPal Go To Meeting Spotify Ammyy Admin Jing Facebook Messenger AnyDesk -
Manual – Remote Control Page 2 of 111 7.2 Authenticating on the Remote Computer Using a Windows User Account 28
TeamViewer 10 Manual Remote Control Rev 10.3-201506 TeamViewer GmbH • Jahnstraße 30 D-73037 Göppingen www.teamviewer.com Table of contents 1 About TeamViewer 5 1.1 About the software 5 1.2 About the manual 5 2 Basics 7 2.1 How TeamViewer works 7 2.2 Description of the main TeamViewer window 7 3 Establishing a connection with TeamViewer 10 4 The Remote Control connection mode 11 4.1 Remote Control window options 11 4.2 Remote computer options in the TeamViewer Panel 18 5 The File Transfer connection mode 21 5.1 Options in File Transfer connection mode 21 5.2 Transferring files using drag and drop 23 5.3 File transfer via the Windows context menu 24 6 The VPN connection mode 25 6.1 Sample uses of TeamViewer VPN 25 6.2 Requirements for using TeamViewer VPN 25 6.3 VPN dialog box options 26 7 Other connection options 27 7.1 Establishing a LAN connection using the IP address 27 TeamViewer 10 Manual – Remote Control www.teamviewer.com Page 2 of 111 7.2 Authenticating on the Remote Computer using a Windows user account 28 7.3 Establish a connection via a Windows shortcut 29 7.4 Connections to your own computers without a password. 30 8 Computers & Contacts – Managing Contacts 32 8.1 The TeamViewer account 33 8.2 Computers & Contacts options 37 8.3 Service cases 53 8.4 Integrated system health checks 56 9 Multimedia functions 58 9.1 Options within the Session list 58 9.2 Transmitting webcam video to your partner 58 9.3 Talk to your partner via Voice over IP or conference call 59 9.4 Chatting with your partner during a TeamViewer session 61 9.5 -
Smartcode VNC Manager V5.0 Brochure
SmartCode TM VNC Manager v5.0 Award Winning Remote Computer Management Software Powerful tool to control all your computers from one program WELCOME TO NETWORK MANAGEMENT WITHOUT BARRIERS In today’s large corporate computer networks, with hundreds of computers located across the globe, the ability to effectively manage all of these computers is the key to the efficient use of staff time and can be a major cost saving factor. With SmartCode VNC Manager 5.0 you can access and control computers from anywhere. It is a powerful remote administra- tion and monitoring software application for both the business and home network environments. It is typically used for remote network management, remote system administration and in helpdesk environments. The application allows you to take remote control of any computer running VNC, Remote Desktop Services, Citrix ICA, Microsoft Hyper-V, Microsoft Virtual Server 2005, RAdmin, SSH, or Telnet servers. SmartCode VNC Manager was created to give you an easy-to-use yet powerful tool to manage, monitor and remotely control your computers. The VNC Manager software is used by thousands of small, midsized and large businesses worldwide. CENTRALIZED ADMINISTRATION VNC & Hyper-V THUMBNAILS VIEWS Administrators have quick access to all the management SmartCode VNC Manager was first application to and administration features available in a single console. introduce VNC thumbnails view. The new v5.0 release SmatrCode VNC Manager includes over twenty tools takes this feature one step further by adding support for that simplify management of Windows NT/XP/Vista/ monitoring of Microsoft Hyper-V virtual machines Windows 7 computers.