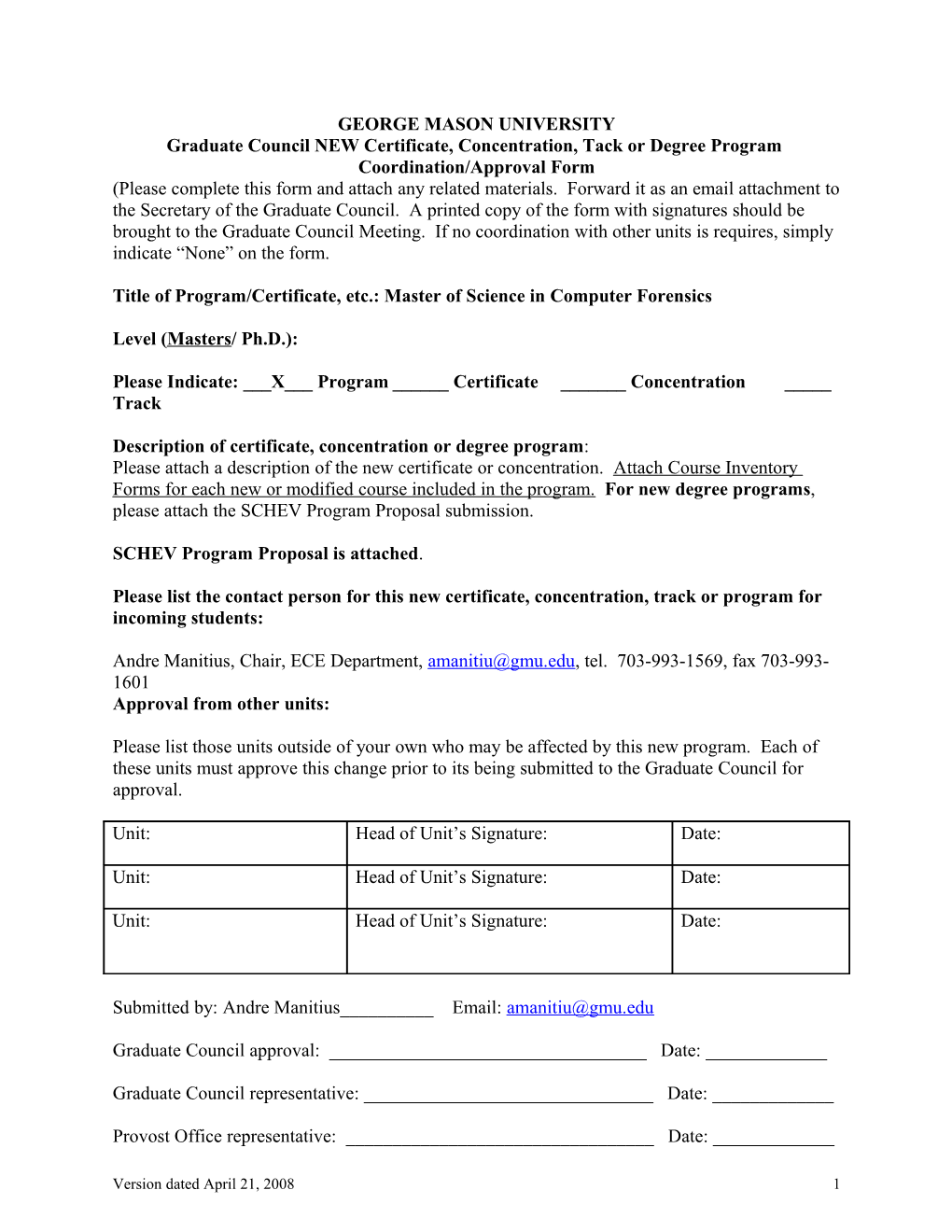
GEORGE MASON UNIVERSITY Graduate Council NEW Certificate, Concentration, Tack or Degree Program Coordination/Approval Form (Please complete this form and attach any related materials. Forward it as an email attachment to the Secretary of the Graduate Council. A printed copy of the form with signatures should be brought to the Graduate Council Meeting. If no coordination with other units is requires, simply indicate “None” on the form.
Title of Program/Certificate, etc.: Master of Science in Computer Forensics
Level (Masters/ Ph.D.):
Please Indicate: ___X___ Program ______Certificate ______Concentration _____ Track
Description of certificate, concentration or degree program: Please attach a description of the new certificate or concentration. Attach Course Inventory Forms for each new or modified course included in the program. For new degree programs, please attach the SCHEV Program Proposal submission.
SCHEV Program Proposal is attached.
Please list the contact person for this new certificate, concentration, track or program for incoming students:
Andre Manitius, Chair, ECE Department, [email protected], tel. 703-993-1569, fax 703-993- 1601 Approval from other units:
Please list those units outside of your own who may be affected by this new program. Each of these units must approve this change prior to its being submitted to the Graduate Council for approval.
Unit: Head of Unit’s Signature: Date:
Unit: Head of Unit’s Signature: Date:
Unit: Head of Unit’s Signature: Date:
Submitted by: Andre Manitius______Email: [email protected]
Graduate Council approval: ______Date: ______
Graduate Council representative: ______Date: ______
Provost Office representative: ______Date: ______
Version dated April 21, 2008 1 STATE COUNCIL OF HIGHER EDUCATION FOR VIRGINIA PROGRAM PROPOSAL COVER SHEET
1. Institution 2. Program action (Check one): George Mason University Spin-off proposal New program proposal
3. Title of proposed program 4. CIP code Computer Forensics 43.0106
5. Degree designation Master of Science 6. Term and year of initiation Spring 2009
7a. For a proposed spin-off, title and degree designation of existing degree program
7b. CIP code (existing program)
8. Term and year of first graduates Fall 2010 9. Date approved by Board of Visitors (TBD)
10. For community colleges: date approved by local board date approved by State Board for Community Colleges
11. If collaborative or joint program, identify collaborating institution(s) and attach letter(s) of intent/support from corresponding chief academic officers(s)
12. Location of program within institution (complete for every level, as appropriate).
School(s) or college(s) of Volgenau School of Information Technology and Engineering
Division(s) of Electrical and Computer Engineering
Campus (or off-campus site) Fairfax, VA
Distance Delivery (web-based, satellite, etc.) Currently Not Applicable but Planned in Future
13. Name, title, telephone number, and e-mail address of person(s) other than the institution’s chief academic officer who may be contacted by or may be expected to contact Council staff regarding this program proposal. Andre Manitius, Professor and Chair, Electrical & Computer Engineering Department 703-993-1594, [email protected]
Version dated April 21, 2008 2 TABLE OF CONTENTS
PROPOSAL FOR A MASTER OF SCIENCE DEGREE IN COMPUTER FORENSICS
DESCRIPTION OF THE PROPOSED PROGRAM...... 3
OVERVIEW...... 3 DESCRIPTION OF THE CURRICULUM……………………………………………………………………………….. 4 ADMISSION CRITERIA...... 7 ADVANCEMENT TO CANDIDACY ...………………………………………………………………………………….7 FACULTY...... 9 PROGRAM SIZE AND VIABILITY …………………………………………………………………………………… 11 PROGRAM ADMINISTRATION ……………………………………………………………………………………... 12 LEARNING OUTCOMES AND ASSESSMENT………………………………………………………………………... 15 BENCHMARKS OF SUCCESS...... 16 EXPANSION OF AN EXISTING PROGRAM...... 17 JUSTIFICATION FOR THE PROPOSED PROGRAM...... 17
RESPONSE TO CURRENT NEEDS...... 17 What is Computer Forensics ……………………………………………………………………………….18 Who Utilizes Computer Forensics …………………………………………………………………………18 Why Computer Forensics? …………………………………………………………………………………18 Impact of the Proposed Masters in Computer Forensics program on the Commonwealth of Virginia ..…..16 Evidence for the Need for Computer Forensics experts …………………………………………………...19 Historical Aspects of the proposed Masters in Computer Forensics program …………………………….19 ANTICIPATED STUDENT DEMAND ……………………………………………………………………………….. 20 No Duplication of other Programs ………………………………………………………………………21 Anticipated Employment Demand ………………………………………………………………….…….22 LETTERS OF SUPPORT ………………………………………………………………………………………...22 PROJECTED RESOURCE NEEDS...... 23 Growth Options Low Growth Option ………………………………………………………………………………………24 Medium Growth Option …………………………………………………………………….....…………25 High Growth Option ……………………………………………………………………………………...26 Projected faculty and Resource Needs …………………………………………………………27 Full-time faculty …………………………………………………………………………………………..27 Part-time faculty …… ……………………………………………………………………………………27 Adjunct faculty ……………………………………………………………………………………………27 Graduate assistants …………………………………………………………………………………….…..28 Classified positions ………………………………………………………………………………………..28 Equipment …………………………………………………………………………………………………28 APPENDIX A Brief Course Catalog Descriptions...... A-1 APPENDIX B Sample Schedule for M.S. in Computer Forensics Completion...... B-1 APPENDIX C Sample “Mini CV’s” for Faculty...... C-1 APPENDIX D Sample Job Announcement with URL and Date...... D-1 APPENDIX E Survey Instrument (and some results)...... E-1 APPENDIX F Assumptions Used in Developing Resource Projections...... E-10
Version dated April 21, 2008 3 PROPOSAL FOR THE M.S. IN COMPUTER FORENSICS Presented by the Department of Electrical and Computer Engineering George Mason University
Description of the Proposed Program
Overview
The Department of Electrical and Computer Engineering as part of George Mason University’s Volgenau School of Information Technology and Engineering (ITE) is proposing a Master of Science in Computer Forensics (CFRS). Computer forensics is the collection (seizure), processing, and analysis of digital information such that this information (evidence) can be successfully admitted into a court of law. It is interdisciplinary in its nature with an inclusion of topics and tools from computer engineering, computer science, information technology, network engineering, telecommunications, law, and ethics. Although related to information security, computer forensics is a discipline unto itself. In the last 20 years, computer forensics has evolved into its own industry. Once primarily focused on supporting criminal prosecutions, computer forensics now also supports civil prosecutions and the enforcement of the Sarbanes- Oxley Act of 2002 (Pub. L. No. 107-204, 116 Stat. 745). The proposed M.S. in Computer Forensics will prepare students for careers in industry, government, and academia by combining academic education with real world practical techniques. Emphasis is placed in the program on training students to use and apply computer forensics methods and knowledge in a variety of real life scenarios. Computer forensic examiners (CFE) work in both the public and private sectors, and the Washington, D.C. area is home to a large work force of CFEs. These CFEs work for the FBI, DEA, USSS, as well as with the vast majority of Inspectors General and local police departments. Practically all of the major accounting and consulting firms employ computer forensic examiners on staff, and there is a growing cadre of independent consultants that work in this field. The American Society of Crime Lab Directors (ASCLAD), the governing association in the field of forensics sciences, requires that all computer forensic examiners possess as a minimum a bachelors degree with significant course work in math and science, which must be supplemented by a significant period of hands-on forensics work. The FBI recruits computer forensics examiners who possess as a minimum a bachelors degree with significant mathematics and science in the curriculum, and then the FBI puts these recruits through an intensive, in-house training program. Each recruit is mentored through the training program that consists of at least five exams and five searches, and the average training program takes a year. Once through this program, the FBI assigns their recently trained CFEs to a senior partner so that additional, real- life training can take place on actual cases. The reason the FBI, and other organizations, are willing to recruit at the bachelor level and then commit to expensive in-house training, is that there are very few academic programs that are designed to produce masters in computer forensics candidates on which the FBI can draw upon for its recruits. The proposed M.S. in Computer Forensics will do this as it will provide students with the necessary skills and
Version dated April 21, 2008 4 knowledge to perform in a variety of computer forensic roles, including forensics examiner, in addition to providing an advanced degree. The distinctiveness of the George Mason’s Master’s program in Computer Forensics lies in the curriculum, which has been tailored to strengthen the employment opportunities of students in non-academic jobs, as well as prepare students who may wish to pursue a doctorate. The proposed program will incorporate faculty research and teaching interests on a range of contemporary topical issues. It will also provide students with advanced training in computer and network digital evidence, intrusion forensics, and legal and ethical issues. The distinguished M.S. in Computer Forensics program faculty are drawn from several departments, such as (in alphabetical order) Applied Information Technology, Computer Science, and Electrical and Computer Engineering. Their specializations include information security assurance, intrusion detection, network forensics, digital media forensics, operating systems, network engineering, software design, digital hardware, microelectronic chip forensics, cryptography, computer analysis of handwriting, cyber crime, digital evidence, and law and ethics. Many faculty members have experience in industry and government settings, and some have been expert witnesses in court. The Department of Electrical and Computer Engineering has been offering in the last few years a Graduate Certificate in Telecommunications, Forensics, and Security (TFAS) as a concentration within the M.S. in Telecommunications (TCOM) program. The success of the TFAS certificate demonstrates a clear demand for a reputable Computer Forensics program at the Master’s level, offered by a Virginia university.
The M.S. in Computer Forensics will contribute to Commonwealth of Virginia and George Mason University needs and goals by serving a larger graduate student population in key areas and offering advanced elective courses in areas of interest to students pursuing advanced degrees in other George Mason programs. Among those programs are Computer Science, Information Security Assurance, Electrical Engineering, Computer Engineering, and Telecommunications. George Mason University’s location in Northern Virginia; the teaching capabilities and capacity within the Volgenau School of Information Technology and Engineering (VSITE), the ECE department, and the university as a whole; and the status as a program within the Commonwealth of Virginia’s university system provides a unique advantage in offering students an excellent and affordable program that will prepare them to effectively use computer forensics skills and knowledge in their careers.
Description of the Curriculum
The field of forensics science as applied to digital technologies has evolved over a range of disciplines in the last two decades. The initial concentration of effort was in protecting the communications links and storage devices from intrusion, theft, and sabotage. George Mason University’s School of IT&E developed, within the former Information Systems Department (now within the Computer Science Department), a broad range of courses and research concentrations that focuses on security of networks, computers, and data storage facilities. Other Departments and Schools within George Mason University used their range of faculty talents to address issues such as ethics and fraud within the framework of accounting, law, and
Version dated April 21, 2008 5 communications. The Department of Electrical and Computer Engineering, within the School of IT&E, both through its M.S. in Computer Engineering program and its M.S. in Telecommunications program, explored topics related to cryptography and network security, network engineering, network forensics, and digital media forensics. The stage was therefore set to draw upon this existing, wide-ranging interdisciplinary pool of talent when cyber crime started to become a major issue.
With the apparently increasing vulnerability of digital information, whether in transit or stored, the likely corruption or theft of digital data was such as to require a new capability: computer forensics. Clearly, the basis for the development of this new capability was in the field of computer engineering: a range of digital techniques needs to be mastered by any student seeking to be a practitioner in this field. However, the ability to trace the theft or corruption of digital information is not sufficient. The search results must be able to withstand the scrutiny of a court of law. The engineering knowledge of computer forensics has therefore to be supplemented by a strong understanding of both ethical and legal issues to ensure that the evidence will hold up under the strongest scrutiny. The proposed M.S. in Computer Forensics program seeks to blend an exacting engineering, ethics, and legal issues plan of study to ensure that the graduates are thoroughly grounded in the skills necessary to work in both commercial and law enforcement areas, and are equipped to enter into an academic research path or a professional career. The proposed M.S. in Computer Forensics (CFRS) requires the completion of a minimum of 30 hours of graduate course work with a GPA of 3.000, or higher. The CFRS program is split into two elements: a Core component of 18 credit hours (15 credit hours plus a mandatory, 3-credit, capstone course that is taken towards the end of the degree) and an Elective component of 12 credit hours. The CFRS course names are given in Table 1 with the course descriptions given in detail in appendix A. All courses without the CFRS designation are existing graduate courses within the university. Core Component: The Core component consists of four elements, with each individual course being 3 credit hours: - A mandatory introductory course must be taken as the first course, or as one of the first courses, in the first semester of the student’s M.S. in Computer Forensics degree program. This course may be either CFRS 500 or ISA 562. (3 credits) - Three Forensics courses (CFRS 660, 661, and 663) that may be taken in any order, but which should be completed within the first 18 credit hours of the student’s degree program (total of 9 credits) - One Ethics course that may be selected from a pair of Ethics courses (CFRS 760 and 770), and which may be taken at any point in the program (3 credits); and - A Capstone Project Course (CFRS 790) that may not be taken until at least 18 credit hours have been earned within the CFRS degree program (3 credits). Elective (Specialty) Component:
Version dated April 21, 2008 6 The Elective component consists of a number of specialty topic courses, again each of 3 credit hours, and students are required to select 4 of these courses. Some students may wish to broaden their curriculum with a sociology or law course, while others may wish to focus on information security assurance (ISA) or computer engineering (ECE) courses as part of their preparation for a Ph.D. program. Table 1 includes a detailed plan of the curriculum. Please refer to Appendix A for detailed course descriptions. Coursework will progress from core courses to more advanced specialty courses, culminating in a capstone project course. Both 600 and 700-level core courses are designed to establish a solid foundation for subsequent work beyond the master’s level. The basic core course CFRS 500 (or alternatively ISA 562) will be offered every semester, while the other core courses will be offered each year, probably in alternate semesters, until the CFRS student body builds up to warrant those courses being given in every semester. The Specialty courses are designed to provide students with advanced, more specialized, graduate level studies in the area that they feel will help their career the best, whether it will be academic or professional. The non-CFRS specialty courses listed in Table 1A number, e.g. ISA 774 Intrusion Detection and INFS 785 Data Mining for Homeland Security, are not necessarily the only specialty courses that may be taken. It is likely that additional elective courses will be added as the field of forensics expands, both in breadth and depth. One example could be the area of Multimedia Forensics, an international conference on which was held in August 2008. The URL for this conference (http://home.simula.no/~yanzhang/MUSIC/) listed topics in many forensics areas, including multimedia forensics.
The strong networking element of the CFRS program requires students to have detailed TCP/IP and Internet Routing knowledge before entering the main CFRS program. If students lack this background, they should take TCOM 509/529 (IP/Advanced IP) and TCOM 515 (Internet Routing Lab), or equivalents, prior to CFRS 500. TCOM 509/529 and TCOM 515 are existing courses offered every fall, spring, and summer as part of the M.S. in Telecommunications degree program.
It is worth noting that seven (7) courses within the proposed M.S. in Computer Forensics program are existing courses that are taught in companion programs. Three (3) of these courses are in the core component and four (4) are in the elective component of the proposed M.S. in Computer Forensics program. Only five (5) brand new courses need to be developed, and their detailed content, together with all of the other courses to be taught in the M.S. in Computer Forensics program, are given in Appendix A to this proposal. The requisite faculty are already available to teach all of these courses and so no additional funds are requested for new faculty positions for teaching within the proposed program. However, a Program Director of the M.S. in Computer Forensics will be appointed as a faculty member in the ECE department to run the program and an administrative assistant will be appointed in a staff position within the ECE department to assist in the running of the M.S. in Computer Forensics office. It is intended to fill these positions by the proposed start of the program in Spring (or Fall) 2009. Depending on the growth in enrollments, a second faculty position, and maybe a third, is anticipated to be needed within four or five years. The associated costs of these positions are discussed later in this proposal.
Version dated April 21, 2008 7 Appendix B provides sample schedules for the CFRS degree completion for both full-time and part-time students. Time to completion may involve more or less time depending on student work load and courses chosen, and on the number of courses offered each semester, which is concomitant on the number of students who register. Three growth projections are used in developing the plan of study: (i) a low growth option with 20 students admitted each semester; (ii) a medium growth option with 20 students in the first semester, 30 new students in the second semester, and then a stable count of 40 new students per semester thereafter; and (iii) a high growth option with 20, 40, then a stable count of 60 new students per semester. Appendix B gives more details. It is anticipated that full-time students will graduate in two years or less, while most part-time students will take between two and four years. These durations match those of all 30 credit hour masters programs currently offered by George Mason University.
Admission Criteria
Students who hold a B.S. or B.A. degree from an accredited college or university in engineering, math, science, computer science, business (with a quantitative background), economics, or other analytical disciplines, or students who have equivalent work experience indicating analytical aptitude, may apply to the M.S in Computer Forensics. Depending on their background, some applicants may be required to complete 3 to 6 credits of preliminary course work before they are allowed to enroll in any of the core courses or specialty courses in the program. The anticipated courses some students will be required to take as a condition for admittance to the M.S. in Computer Forensics program are TCOM 509 (Internet Protocols; 1.5 credits), TCOM 529 (Advanced Internet Protocols; 1.5 credits), TCOM 515 (Internet Routing lecture and lab; 3 credits), and TCOM 575 (Quantitative Fundamentals; 3 credits). Other courses: TCOM 509, 529, 515, and 575 may not be taken for credit in the proposed M.S. in Computer Forensics program. A minimum undergraduate GPA of 3.00 is required for acceptance. Students may be admitted to the M.S. program, or they may be admitted for non-degree study within the program, which allows them to take individual courses. Students in the non-degree program have the option of transferring into the regular program, provided their GPA within the M.S. in Computer Forensics program is 3.00 or above. Up to 12 credits earned in non-degree study may be transferred into the regular program, provided each of the courses to be transferred in was passed with a grade of B, or above. These conditions are the same as those currently applied to most graduate degrees at George Mason University
Advancement to Candidacy
There is no dissertation or thesis requirement for this program and so all candidates admitted under regular master’s status to the proposed M.S. in Computer Forensics program are candidates for the degree. They graduate under the normal conditions that apply to master’s candidates: completion of the required core courses, including the capstone course; completion of the elective element of the program; completion of the total of at least 30 credit hours with a minimum GPA of 3.000, no more than 6 credit hours worth of C grades.
Version dated April 21, 2008 8 Version dated April 21, 2008 9 Table 1: M.S. in Computer Forensics curriculum (proposed) Mandatory Core Component (18 credits from 21 credits)
Course Title Credits Either CFRS 500* Intro to Technologies of Value to Forensics 3 Or ISA 522 Information Security Essentials 3 Or ISA 562 Information Security Theory and Practice 3 CFRS 660 Network Forensics 3 (Currently TCOM 660) CFRS 661 Digital Media Forensics 3 (Currently TCOM 661) CFRS 663 Operations of Intrusion Detection for Forensics 3 (Currently TCOM 663) Either CFRS 760 * ++ Legal and Ethics in IT 3 Or CFRS 770 * ++ Fraud and Forensics in Accounting 3
CFRS 790 * +++ Advanced Computer Forensics 3 (CFRS Degree Capstone Course) Specialty Courses (12 credits from the courses below) TCOM 662 Advanced Secure Networking 3 ECE 646 Cryptography and Computer-Network Security 3 ECE 746 Secure Telecommunication Systems 3 ECE 511 Microprocessors 3 CFRS 760 * ++ Legal and Ethics in IT 3 CFRS 770 * ++ Fraud and Forensics in Accounting 3 CFRS 780 * Special Topics Course 3 INFS 785 Data Mining for Homeland Security 3 ISA 650 Security Policy 3 ISA 652 Security Audit/Compliance Testing 3 ISA 656 Network Security 3 ISA 674 Intrusion Detection 3 ISA 785 Research in Digital Forensics 3 LAW 181 Communications Law 3 SOCI 607 Criminology 3 (*) Represents proposed new courses (++) Both of these courses may be taken but only one may be used in the core component (+++) CFRS 790 is the Capstone CFRS Course and may only be taken after a total of 18 credit hours have been completed in the CFRS program, which shall consist of CFRS 500; at least two courses drawn from TCOM 660, 661, and 663; and at least one course from CFRS 760 and 770.
Version dated April 21, 2008 10 Faculty
The M.S. in Computer Forensics will utilize the large and diverse capabilities of the faculty of the Volgenau School of Information Technology and Engineering (IT&E) where many courses are currently taught in a variety of master’s level programs with a security or forensics emphasis. The CS department houses the strong M.S. in Information Security Assurance (ISA) program, in addition to a broad M.S. in Information Systems (INFS) program that forms a strong element of the Ph.D. in Information Technology available within the Volgenau School of Information Technology and Engineering (VSITE). The ECE department has an M.S. in Computer Engineering program with faculty specializing in cryptography and security of digital devices, and additional faculty members in areas such as microelectronic chip design for applications in digital forensics and DNA forensics on a chip. The ECE department also has experience with offering a Graduate Certificate in Telecommunications, Forensics, and Security (TFAS), a precursor of the presently proposed Master of Science in Computer Forensics. The Applied Information Technology (AIT) department has faculty who are experts in research on computer analysis of handwriting, which adds an extra dimension to computer forensics. Additional courses may be added to the program at a later date to provide these additional topics to the students. A number of interdisciplinary programs exist that allow faculty from other schools within George Mason University to teach within VSITE programs. Examples are the School of Public Policy and the Law School that offer courses within VSITE programs.
In addition to regular faculty, the Volgenau School of IT&E is fortunate to have a large pool of experienced adjunct faculty with outstanding computer forensics experience in industry or federal government, who will be called on to teach within the M.S. in Computer Forensics program. The use of current working forensics professionals and tenure, or tenure-track, George Mason University faculty pursuing in-house research will ensure that the course content remains relevant and the instruction is at the level that both the students and the organizations to be served by this program demand. The proposed M.S. in Computer Forensics program will be supported by GMU faculty members with the following collective credentials: information security, intrusion detection, digital media forensics, network forensics, cryptography, digital devices security, forensics applications of microelectronics, cyber crime, digital evidence, telecommunications law, and ethics.
A key element in the proposed M.S. in Computer Forensics program is that it will not be starting from scratch: the majority of the components necessary for the success of the program already exist. At the undergraduate level within the Volgenau School of Information Technology and Engineering (V-SITE), the thriving Bachelors of Science in Information Technology (BSIT) program already has a very well populated concentration that is a natural precursor to the M.S. in Computer Forensics area: the Information Security and Networking(ISN) concentration. The number of students in the BSIT program in 2005 and 2006 academic years who have elected to concentrate on ISN is shown in Table 2 below. As can be seen in Table 2, in academic year 2005 almost half of the students (377 of 784) elected ISN as their major and the number was even larger in 2006 (419 of 723). The numbers remained essentially the same in 2007 and the start of 2008.
Version dated April 21, 2008 11 At the graduate level in V-SITE, there is a Graduate Certificate in Telecommunications Forensics and Security (TFAS) that is currently offered within the existing M.S. in Telecommunications (TCOM) program. The TFAS certificate has attracted a significant group of students who have entered the M.S. in Telecommunications program, with about 10% of the TCOM students electing to take the TFAS certificate. There are currently about 220 TCOM students and about 8 of the 80 TCOM students who graduated in each of the last two years (2005/6 and 2006/7) earned TFAS certificates. Details of the courses and structure of the TFAS certificate are in given in Table 3 below. Table 2. BSIT Enrollments by Concentration 2005 and 2006
2005 FT Other Freshmen Freshmen Sophomores Juniors Seniors TOTAL ISN 4 10 47 106 210 377 CGW 0 2 7 25 62 96 DBMP 0 0 1 1 2 Undeclared 42 40 94 87 46 309
TOTAL 784
2006 FT Other Freshmen Freshmen Sophomores Juniors Seniors TOTAL ISN 20 9 57 113 220 419 CGW 11 7 19 22 48 107 DBMP 6 5 4 10 5 30 Undeclared 11 22 69 22 43 167
TOTAL 723
______Table source: http://irr.gmu.edu/off%5Fenrl%5Fconc/ Data extracted and prepared by Anne Marchant September 28th, 2007 Key ISN = Information Security and Networking CGW = Computer Graphics and Web DBMP = Database Management and Programming
Version dated April 21, 2008 12 Table 3. Telecommunications, Forensics, and Security (TFAS) Graduate Certificate program (existing)
Mandatory Core Courses (9 credits from 15 credits) TCOM 548/556 Security Issues in Telecom/Cryptography and Network Security (1.5 credits each; total of 3 credits) or TCOM 515 Internet Protocol Routing (3 credits) TCOM 562 Network Security Fundamentals (3 credits)
And either TCOM 660 (*) Network Forensics (3 credits) Or TCOM 661 (*) Digital Media Forensics (3 credits)
Specialty Courses (6 credits from 15 credits) TCOM 660 (*) Network Forensics (3 credits)
TCOM 661 (*) Digital Media Forensics (3 credits)
TCOM 662 Advanced Secure Networking (3 credits)
TCOM 663 Operations of Intrusion Detection for Forensics (3 credits)
ISA 562 (+) Information systems Security (formerly INFS 762) (3 credits)
(*) TCOM 660 and TCOM 661 cannot be taken twice for credit. If either course is taken in the core element, it cannot be taken again in the specialty element.
Program Size and Viability
There are around 400 BSIT students graduating each year with an Information Security and Networking (ISN) concentration from George Mason University. If 20% of this graduating pool were to go on to graduate school the next year (a conservative estimate) and 20% of these were attracted into the proposed M.S. in Computer Forensics program (again, a conservative estimate), there would be 16 prospective incoming students a year, just from the BIS program at George Mason University. More likely the number would be 3 times larger, giving an intake pool of more than 50 applicants to draw from. It is also anticipated that the proposed M.S. in Computer Forensics will attract those students within the M.S. in Telecommunications program who elected to take the TFAS certificate within their TCOM program. Based on the strong demand for well qualified applicants in the area of computer forensics in the local, and nationwide, job market, it is confidently expected that the proposed program will attract at least 100 viable applicants a year by the end of the second year of the program (growth option (ii) discussed earlier in this proposal). This confidence is justified by the results of a web-based survey
Version dated April 21, 2008 13 conducted in October 2007. Of the 149 total respondents to the survey, 91% (135 of 149) were interested in enrolling in the M.S. in Computer Forensics program; 82% (121 of 147) were currently enrolled at George Mason University; 64% (75 of 117) are currently working full time; 87% (103 of 118) live in Virginia; and 94% (132 of 141) plan to live in their current state for the next 3 or 4 years. The detailed responses to the Survey Instrument, together with the Survey Instrument, are shown in Appendix E.
The area of computer forensics is growing rapidly. In February 2008, a three day trade show was held in Washington, D.C., to showcase the products being developed by companies in computer forensics. More than 50 companies were represented at the show, which was very well attended. See http://www.computerforensicshow.com/. The IEEE Signal Processing Magazine has recently issued a call for papers for a special issue on Digital Forensics that will be published in March 2009 – well timed for the start of the proposed M.S. in Computer Forensics at George Mason University. All this supports the assertion that the field of computer forensics is growing rapidly and that it will require a significant injection of well trained professionals to fill the positions that will be created. The proposed M.S. in Computer Forensics is designed to produce such professionals.
Program Administration
The proposed M.S. in Computer Forensics will be administered by the Electrical and Computer Engineering (ECE) department of the Volgenau School of Information Technology and Engineering (V-SITE). The M.S. in Telecommunications (TCOM) is one of three master’s degrees offered within the ECE department (the other two being an M.S. in Electrical Engineering and an M.S. in Computer Engineering), and the Graduate Certificate TFAS is one of three advanced certificates offered within the M.S. TCOM program, and one of the total of six offered by the ECE Department.
It is anticipated that a director of the M.S. in Computer Forensics program will be appointed by Spring 2009, which is when the first courses are planned to be offered. The director of the M.S. in Computer Forensics will have a full-time administrative assistant who will assist in the running of the M.S. in Computer Forensics office. In addition to scheduling the course offerings and hiring such adjunct faculty as are needed for each semester, the director of the M.S. in Computer Forensics will engage local organizations who have an interest in computer forensics in order to explore cooperative ventures, such as an expansion of computer forensics lab capabilities on the George Mason University campus. As the program grows, the revenues will not only sustain both the position of the director of the program and his or her assistant, but also the recruitment of one or two faculty to both teach and conduct research.
The following full-time faculty members of V-SITE are currently identified by the agreement of the respective departments and approval of the Dean as willing to support this new program by teaching courses and advising students on potential research directions and career paths. They are listed by their departments, and the departments are listed alphabetically. Short bios of these faculty members are shown in Appendix C to this document.
Version dated April 21, 2008 14 Applied Information Technology Department (AIT)
Dr. Donald Gantz (AIT) – Statistical methods applied to computer analysis of handwriting
Dr. Anne Marchant (AIT) – Computer Crime, Forensics, Auditing, Ethics
Computer Science Department (CS)
Dr. Daniel Barbara (CS) – Data Mining and its Applications
Dr. Xuxian Jiang (CS) – System and Network Security, Virtualization Technology, Distributed Computing
Dr. Edgar Sibley (CS) – Information Systems Policy, Organizational Informatics
Dr. Bob Simon (CS) – Computer Networks, Distributed Multimedia and Real-time Systems, Computer-Supported Cooperative Work, Performance Modeling and Simulation, Multimedia Databases and Video-on-Demand Systems
Dr. Angelos Stavrou (CS) – Large Systems Security and Survivability, Secure Peer-to-Peer and Overlay Networking, Distributed Systems Reliability, Fairness and Statistical Inference, and Privacy and Anonymity
Dr. Frank Wang (CS) – Network Security, Intrusion Source Tracing, Active Intrusion Response
Dr. Duminda Wijesekera (CS) – Security, Multimedia, Networks, Control and Signaling, Logic
Electrical and Computer Engineering Department (ECE)
Dr. Kris Gaj (ECE) – Cryptography, computer arithmetic, reconfigurable computing, software- hardware co-design, and computer-network security. Dr. Ken Hintz (ECE) – Syntactic pattern recognition applied to ground penetrating radar images for landmine detection and classification, information-based real-time sensor management, X-ray, thermal, and visual, image processing, as well as computer architectures and algorithms for real time signal processing.
Version dated April 21, 2008 15 Dr. David Hwang (ECE) – Secure embedded systems, cryptographic hardware for embedded system security. Digital signal processing architectures (FPGA/ASIC), VLSI digital systems and circuits.
Dr. Jens-Peter Kaps (ECE) – Ultra-low-power cryptographic hardware design, computer arithmetic, efficient
cryptographic algorithms, and computer and network security
Dr. Qiliang Li (ECE)
– Nanoelectronic devices, with potential applications.
Dr. Rao Mulpuri (ECE) – Large band-gap semiconductor materials, microelectronics devices, material and device characterization, and chip forensics (supported by DOJ).
The following adjunct faculty members are identified as candidates for instructors in this new program. They have been teaching courses in the Graduate Certificate of Telecommunications, Telecommunications, Forensics and Security (TFAS) certificate within the TCOM program over the past several years:
Special Agent Robert Osgood (FBI) – Digital media forensics, network forensics, digital evidence, cyber crime. Special Agent James R. Durie (FBI)
– Computer forensics and virtual worlds, identification, testing, and validation of new tools for use in forensic examinations.
Ms. Angela Orebaugh – Information security, intrusion detection, network forensics. Co-author of books on intrusion detection and network security.
Dr. Aleksandar Lazarevich – Information security, digital evidence, computer and network forensics, advanced network security, basic switching lab.
Dr. Thomas Shackelford – Information security, digital evidence, computer and network forensics, advanced network security, basic switching lab
Version dated April 21, 2008 16 Advisory – Steering Committee In addition to faculty currently active in teaching within the TFAS certificate and the INFS and ISA programs within the Volgenau school of Information Technology and Engineering, the M.S. in Computer Forensics will have under an Advisory Committee. The following is the preliminary composition of the committee. Additional, external members will be invited when the program is approved. Dr. Jeremy Allnutt – Professor in ECE and director of the TCOM program Telecommunications, Satellite Communications, Digital Communications Dr. Donald Gantz, – Professor in AIT, Chair of the Department of AIT, expert in computer analysis of handwriting
Dr. Andre Z. Manitius – Chair of the Electrical and Computer Engineering department. Applied Mathematics, Digital Signal Processing, Control Systems Dr. Anne Marchant – Associate Professor in AIT Computer Crime, Forensics, Auditing, Ethics Dr. Bob Simon – Associate Professor in CS Computer Networks, Distributed Multimedia and Real-time Systems, Computer-Supported Cooperative Work, Performance Modeling and Simulation, Multimedia Databases and Video-on-Demand Systems
The advisory committee will provide advice to the management of the M.S. in Computer Forensics program and curriculum.
Learning Outcomes and Assessment
Graduates from the M.S. in Computer Forensics will demonstrate superior academic skills in computer forensics methods and practice. Students will have an understanding of the laws associated with computer forensics and be able to present digital evidence in a court of law. They will also be able to successfully seize, image, deconstruct, and analyze digital media, analyze logs, decipher network traffic, and report this information in a suitable format. They will be able to implement an intrusion detection system, construct signatures, and apply intrusion detection in the forensics area. Students will be able to apply their classroom learning in a variety of computer forensics positions in industry, government, and academia. They will also demonstrate a foundation for advanced research in the computer forensics field.
Version dated April 21, 2008 17 As with all academic programs in George Mason University, assessment of student learning in the proposed M.S. in Computer Forensics will take place at the levels of the student, the course, and the program. Students will be assessed in a number of ways throughout the program. Scholarly ability will be evaluated through course grading in seminar-style classes. Oral, written, and analytical skills will be considered in course grading. The capstone class, CFRS 790, will assess the students overall learning with a project that consolidates the various courses in the curriculum. Course evaluations are conducted in every course in every term, providing the student’s perspective on course effectiveness. Overall, the program will be reviewed on the 6-year cycle typical of programs within the Volgenau school of Information Technology and Engineering. Program review takes place under the guidance of the Office of institutional Assessment and requires three semesters to complete. The outcomes of the process are a series of deliverables – a self-assessment report and academic plan written by program faculty and a report by a review team external to the program – and changes made to enhance the program. The Department of Electrical and Computer Engineering is scheduled for review of its programs in 2008-09.
Benchmarks of Success
The program’s goal is to train students to use their computer forensics knowledge and methods effectively in industry, government, or academic positions. Specific benchmarks for success will be based upon the program’s ability to attract high-quality applicants, the timely graduation of qualified students, and job market placement. Given the success of the Graduate Certificate TFAS in the M.S. in Telecommunications program, which has been in place for a little over two years, it is anticipated that the Master’s Program in Computer Forensics will receive academically well-qualified applications for admission. The quality of applicants will be measured against comparable Master’s programs in Computer Forensics. Success must also be measured by the ways in which the program affects career trajectories and job mobility once a student has completed the program. The projected length of the program for a full-time student is eighteen months to two years. For part-time students, it is difficult to estimate completion time, but it is approximately two to four years, depending on the number of classes in which part-time students enroll each semester. Appendix B provides sample schedules for degree completion for both full and part time students under one of three growth scenarios. Follow-up surveys will evaluate the success of graduated students in the job market. It is expected that for individuals who enter the program from a career position, they will most likely derive the benefit of promotion upon completion of the Master’s. Individuals who enter the program from a work position that is not connected closely to computer forensics, it is strongly expected that gaining the M.S. in Computer Forensics will permit that student to compete very effectively in the job market for a CFE position. For students who desire to enter academia, relevant faculty will assist graduates with obtaining entrance into a doctoral program at an appropriate institution of higher learning. If program benchmarks are not achieved, the program faculty will examine its marketing and recruiting practices, admissions requirements, curriculum, instructional methods, advising practices, and course evaluations to determine necessary program
Version dated April 21, 2008 18 modifications. It is anticipated that as the program continues, higher benchmarks in the areas of admission requirements and job placement will be developed and applied. Expansion of an Existing Program
The success of the Graduate Certificate in Telecommunications, Forensics and Security (TFAS) within the M.S. in Telecommunications program offered a stimulus for the development of a stand-alone M.S. in Computer Forensics degree program. The M.S. in Computer Forensics degree program is designed to both supersede, and enhance, the present course offerings in Forensics and Security within the M.S. in Telecommunications program. The modifications are designed to enhance the rigor of the forensics certificate. The M.S. in Computer Forensics is not offered in collaboration with external academic institutions. However, the School of IT&E proposes to collaborate with other programs at George Mason University, notably Sociology, Law, Computer Science, and Information Systems. Students currently registered for the TFAS certificate at the time of approval of the M.S. in Computer Forensics will be offered the opportunity of transferring to the M.S. in Computer Forensics, subject to a review of their individual progress to date, or to continue within the TFAS certificate program until they graduate. The M.S. in Computer Forensics will therefore not entail the requirement for additional teaching resources, but it will require the addition of one faculty position and one staff position (assistant to the director) at the outset of the program. Other positions would be filled on an as-required basis. It is strongly anticipated the program will be self-sufficient within two years and, if the projections of student demand are even half those expected, will generate sufficient revenues to grow the faculty positions in the short-to-medium term to at least three. The Graduate Certificate in Telecommunications Forensics and Security (TFAS) is a 15-credit program (please see Table 3 on page 10) designed to provide students with an in-depth understanding of forensics and security as they apply both to networks and digital storage media. The TFAS certificate was developed both in response to student demand and to provide a specific concentration area within the M.S. in Telecommunications degree program. The TFAS certificate is the foundation of the proposed Master’s degree in Computer Forensics, with three TCOM courses within the TFAS degree specifically adapted for the proposed M.S. in Computer Forensics program. Details of the TFAS certificate can be found earlier in Table 3.
Justification for the Proposed Program
Response to Current Needs
This section provides background information on the proposed program, a description of what is occurring in the field that warrants the proposed Masters in Computer Forensics program, and evidence that the Commonwealth of Virginia needs this program to address emerging current demands. Earlier sections have detailed the emergence of the TFAS certificate in response to student demand, the success of the TFAS certificate program, and the overwhelmingly positive responses obtained via the Survey Instrument (see appendix E) of student interest in a Master of Science in Computer Forensics program. It is anticipated that the work place demands for skilled computer forensics will only expand in the future, leading to strong growth, and sustainability, in the proposed program. What follows explains the area of study, which organizations will employ the graduates, why the area has come into demand, and the impact of
Version dated April 21, 2008 19 the program on the State of Virginia.
What is Computer Forensics?
Computer forensics is the collection (seizure), processing, and analysis of information that has either been transmitted or stored in digital form in such a way that this information (evidence) can be successfully admitted into a court of law. Computer forensics is interdisciplinary in nature with an emphasis on computer science, network engineering, telecommunications, law, and ethics. There are two main subsets to the field of computer forensics:
(a) Digital media acquisition and analysis; and
(b) Network traffic collection, reconstitution, and analysis.
Although related to information security, computer forensics is a discipline unto itself.
Who Utilizes Computer Forensics?
Law enforcement utilizes computer forensics extensively in the investigation of all types of crimes that involve the sending or storing of digital information. Computer forensics has been successfully applied in so-called white collar crime that involves, amongst other things, computer intrusion, identity theft, and child pornography matters. It has also been used extensively in the investigation and prosecution of homicides, sexual exploitation, illegal drug distribution, and just about every other crime that you can think of. The search and seizure of evidence almost always involves the investigation of digital storage media or digital network access either as the primary or secondary means for the commission of the suspected crime. The digital information can range from the SIM cards of cell phones to complex network instructions.
Computer forensics is not for law enforcement alone. The private sector utilizes computer forensics extensively. In fact, computer forensics is an integral part of civil cases. Organizations also use computer forensics internally for quality control and investigative matters. With the advent of the Sarbanes-Oxley Act of 2002 making corporate executives personally responsible for the financial statements of the company, computer forensics is playing a crucial role in the identification and presentation of key information that executives need to effectively run and report operations.1
Why Computer Forensics?
The design and development of digital media or digital networks requires a certain skill set that is taught in a number of programs, one of which is the current Masters in Telecommunications at
1 www.ijde.org, Patzakis, John, New Accounting Reform Laws Push For Technology-Based Document Retention Practices, International Journal of Digital Evidence, Spring 2003, Volume 2, Issue 1
Version dated April 21, 2008 20 George Mason University. However, when a security breach has occurred in the storage or transport of digital information, or has been suspected to have occurred, the examination of the digital media or digital networks for evidence of wrongdoing cannot be undertaken in a haphazard manner. For the information uncovered in the examination of digital media or digital networks to be admissible in a court of law, there are rigorous standards set, which must be followed exactly. The Master of Science in Computer Forensics program will offer to all those who take the program the policies, procedures, and techniques that can be applied across a myriad of situations. Whether it is the seizure of digital media in support of a criminal prosecution, civil dispute, or internal corporate matter, the tools and techniques that computer forensics offer are invaluable. These will be taught in the proposed M.S. in Computer Forensics.
Impact of the proposed M.S. in Computer Forensics on the Commonwealth of Virginia
The Commonwealth of Virginia with its propinquity to the federal government, is the home of computer forensic programs of many federal agencies that include: the Federal Bureau of Investigation (FBI), Internal Revenue Service (IRS), United States State Department (USSD), United States Postal Service (USPS), Drug Enforcement Administration (DEA), and Defense Criminal Investigative Service (DCIS), just to name a few. Across the river in Washington D.C. you will find the computer forensic programs of the Department of Homeland Defense (DHS) and the United States Secret Service (USSS). On the state/local horizon, The Virginia State Police (VSP), the Fairfax County Police (FCP), Arlington County Police (ACP), Prince William County Police (PWCP), and other departments too numerous to mention have active computer forensics requirements that necessitate both internal and external programs of instructions for those employed by those agencies or forces. It is worth noting here that the Regional Computer Forensics Group holds its annual meeting at George Mason University every summer. Please visit http://rcfg.org for additional information. The most recent meeting was held from the 6th to the 10th of August, 2007.
Corporate computer forensic presence in the Commonwealth include: Kroll Inc., MANDIANT, Deloitte Touch, BearingPoint, Northrop Grumman, and Booz Allen Hamilton, again just to name few. All of these organizations have both an internal instructional program and a requirement for more formal external instruction. There was also a recent computer forensics show in Washington, D.C., where more than 50 companies participated2.
The availability of a high quality Master of Science in Computer Forensics program at George Mason University will enable local branches of federal agencies, as well as the various departments and police forces in the State of Virginia, to send their officers and personnel for training in the formal requirements of digital media and network forensics procedures. The impact on the State of Virginia is expected to be very positive, both in the development of a cadre of forensics experts who can assist in crime prevention and prosecution, and in the overall reputation of the state for fostering such a program.
Evidence for the need for Computer Forensics experts
2 http://www.computerforensicshow.com/ and http://enewschannels.com/2008/01/16/enc2505_015731.php
Version dated April 21, 2008 21 The Computer Security Institute, with the participation of the San Francisco Federal Bureau of Investigation’s Computer Intrusion Squad, produces an annual report on computer crime and information security titled: “Computer Crime and Security Survey.” In this survey published each year for the last 11 years, the rising tide of virus attacks, unauthorized access, and theft of proprietary information (i.e., intellectual property) account for 74% of financial loss. In the most recently published (2006) survey, 313 respondents identified over $52 million in losses due to cyber crime. 50 percent of the survey respondents agreed with the statement “compliance with the Sarbanes–Oxley Act has raised my organization’s level of interest in information security. 3 There is clearly a current demand for experts in Computer Forensics, both in the commercial and government (civilian and military) areas, and it is unlikely that this demand will decrease. If anything, it will grow rapidly over the foreseeable future, as evidenced by the effects of the Sarbanes–Oxley law. Computer forensics is a strong growth area.
Historical aspects of the proposed Master of Science in Computer Forensics program
The Master of Science in Computer Forensics program is not a spin-off degree program from another M.S. program. However, the present program proposal had its derivation in a concentration that is currently available in the Masters in Telecommunications program. This concentration is the Telecommunications Forensics and Security (TFAS) certificate that is a concentration requiring 15 credit hours to be taken within the 30-credit M.S. in Telecommunications program. The proposed M.S. in Computer Forensics program will expand upon the TFAS certificate, but it will not require the allocation of new teaching resources to George Mason University. It will, however, require the addition of two new positions: a director to run the proposed program and an assistant for that director to manage the office. Details of the existing certificate program (TFAS) have been given earlier. Table 3 showed the courses in the TFAS certificate and, by reference to Table 1, the ratio of new courses to be developed to existing can be seen to be less than 50%.
Anticipated Student Demand
This was covered to some extent under “Program Size and Viability” on page 10, and is expanded on below.
The first group of students who undertook the Graduate Certificate in Telecommunications, Forensics and Security (TFAS) within their M.S. in Telecommunications degree graduated in May 2006 with the second group following in May 2007. There were 9 students with TFAS certificates in both of these graduating classes of about 90 students. The current enrollments in the TFAS certificate are running at a little above this level (10%), and so it is anticipated that about a dozen students would graduate each year with their TFAS certificate within their M.S. in Telecommunications degree. All of the students who graduated were part-time students employed in the Northern Virginia region, almost all taking 6 credit hours each semester. The average time to graduation is therefore 30 months for the degree, giving a cadre of about 30 students who are engaged in elements of the TFAS certificate at any one time. It is anticipated
3 www.gocsi.com.
Version dated April 21, 2008 22 that the emergence of the M.S. in computer forensics degree program will attract more students to the discipline, perhaps 40 to 50 students per semester, with about double this number applying each year for entry. The majority of the current undergraduate students within the BSIT program at George Mason University have chosen to take the Information Security and Networking (ISN) concentration (please see Table 2 on page 8). If historical trends continue, in addition to those who have currently declared ISN as their major, more than half of the undeclared students will also elect the ISN concentration, yielding around 100 graduates a year in this concentration.
The Survey Instrument given in Appendix E (pages E-1 and E-2) was posted on the web on Friday, October 5th, 2007. Within four days, about 150 responses had been logged into the web site (surveymonkey.com). The survey responses are shown on pages E-4 to E-9 in Appendix E. The responses were overwhelmingly positive, with about 90% of those responding showing a strong interest in such a program. If just 20% of those who responded positively were to sign up, there would be 30 students registering for the program. The vast majority of those who responded were: undergraduates who are currently in the BSIT program; currently living in Virginia; preferred to come to the Fairfax campus for the forensics program; and felt it would enhance their careers.
It is anticipated that the demand for the TFAS certificate within the TCOM program will drop markedly when the proposed M.S. in Computer Forensics is offered, and an assessment will be carried out about two years after the M.S. in Computer Forensics has been running to see whether it is necessary to continue the TFAS certificate. When offered, classroom registration for GMU’s three computer forensic courses: TCOM 660 (Network Forensics), TCOM 661 (Digital Media Forensics), and TCOM 663 (Intrusion Detection and Forensics), averages 20 students per class per semester, indicating that the demand for these courses is higher than those who are just focusing on the TFAS certificate. It is very likely that students not in the proposed masters in computer forensics program, but who are pursuing a different master’s degree in VSITE, will take one or two courses in the computer forensics program as part of their master’s program. Most master’s level programs in the VSITE permit students to take up to 6 credit hours outside of their stated master’s degree to gain additional insights into other career options. These 6 credit hours are usually referred to as “out of area” courses.
No Duplication of the Computer Forensics at other Virginia State Universities
The SCHEV web site giving enrollments in State Universities in Virginia (http://research.schev.edu/enrollment/programmaticenrollment.asp) was opened and it was found that there were no graduate programs that offered any of the computer forensics degrees analogous to the proposed Master of Science in Computer Forensics at George Mason University. The only Virginia State University offering undergraduate programs in the same approximate discipline was Virginia Commonwealth College (VCU), which has a Bachelor of Science and Master of Science in Forensic science (BCHE). Those programs are focused on lab forensics involving chemical analysis tools but not on computer forensics. VCU graduated 11 students from the BS program in 2003, 19 in 2004, and 29 in 2005. It would appear that the BCHE program is a strong growth area at VCU, just like a similar undergraduate program (the Network and Security Concentration in the BSIT program) at George Mason University.
Version dated April 21, 2008 23 As of academic year 2007 – 2008, there are currently no Commonwealth Universities that offer a Master of Science in Computer Forensics, or similar topic. George Washington University, based in the District of Columbia, currently offers a Master of Forensic Sciences degree with a Concentration in High Technology Crime Investigation with approximately 80 students enrolled.
As a result of the lack of computer forensics programs in the Commonwealth of Virginia, GMU’s program in not duplicative.
Anticipated Employment Demand
As can be seen in the information provided in preceding sections and in Appendix D and G, there is expected to be a strong, and increasing, demand for graduates of the M.S. in Computer Forensics program by the large number of federal, state, and local government agencies situated in Virginia directly involved in the field of computer forensics, as well as private sector representation. The field of computer forensics is a thriving activity in commercial business affairs, Virginia State agencies and forces, and federal agencies and forces.
As reported by about.com, a simple search on the text string (key phrase) computer forensics at Dice, a popular technical job bank, returned 145 jobs and consulting gigs. Monster.com, a popular job bank that lists jobs of many types, returned 199.4 Please note that, for reasons given earlier, few of these jobs demand a master’s in computer forensics degree simply because there are so very few students out there with a master’s degree in the area of forensics. Hardly anyone would apply!
[NOTE: Employment advertisements must reflect information obtained within six months of submitting the proposal to SCHEV. SCHEV expects a PDF file of downloaded job announcements that show the URL and date. Job announcements must show that a degree (at the appropriate level) is required or preferred. See Appendix B for example. Print announcements from the Web; do not incorporate them in your document. The Office of the Provost will create the PDF.]
URL’s to be provided for SCHEV proposal
4 http://jobsearchtech.about.com/od/computerjob13/a/comp_forensics.htm
Version dated April 21, 2008 24 Letters of Support for the Proposed M.S. in Computer Forensics
Letters of support were received from the following individuals.
1. Dr. Lam D. Nguyen Stroz Friedberg, LLC Boston, MA 02110
2. Ms. Sandra E. Ring PikeWerks Madison, AL 35738
3. Mr. James Durie Special Agent, FBI
Projected Resource Needs
In developing the Projected Resource Needs, three growth scenarios were reviewed. The first is called the “Low Growth” option; the second the “Medium Growth” option; and the last the “High Growth” option. These are shown in charts 1, 2 and 3 on the following pages. It is likely that the anticipated demand will track the high growth option in the initial student registration, but that natural attrition will decrease the student count to closer to the medium growth option. (Almost all graduate programs have a natural attrition rate of about 20% due to students moving out of the area, students changing program options, and students failing the program – in that order). The likely student cadre when the program student count stabilizes in the third year will be around 250, with about 100 graduating each year. [Note: the assumption of an average of 6 credit hours per semester may be slightly low, as some students will be full time, taking 9 credit hours, or more, a semester. In addition, if the student body does grow to above 200 students, one or two courses will be offered in the summer, which will bring the average length of a typical M.S. student’s degree program to 24 months (from 30 months). The 24 month program would be made up of 6 credits per regular semester and 3 credits in the summer.
Version dated April 21, 2008 25 Low Growth Option
In this growth option, the assumption is that 20 students are admitted in the first semester, 20 in the second, 20 in the third semester, and in each subsequent semester. Assuming that each student registers for two courses (6 credits each semester), the program will build to a cadre of 100 students in five semesters. From the fifth semester, 20 students will graduate each semester, a total of 40 graduates a year. This is shown in Chart 1 below, with the horizontal axis being the semester (1 is fall 2009, 2 is spring 2010, and so on)
120
100
80
60
40
20
0 1 2 3 4 5 6 7 8
Chart 1 Low Growth option for the M.S. in Computer Forensics
Version dated April 21, 2008 26 Medium Growth Option
In this growth option, the assumption is that 20 students are admitted in the first semester, 30 in the second, and 40 thereafter. Assuming that each student registers for two courses (6 credits each semester), the program will build to a cadre of 200 students in seven semesters. In the fifth semester, 20 students will graduate; 30 will graduate in the sixth semester, and from the seventh semester, 40 students will graduate each semester. This is shown in Chart 2 below, with the horizontal axis being the semester (1 is fall 2009, 2 is spring 2010, and so on). Thus in academic year 2011/12, 50 students will graduate, and 80 students will graduate in each academic year thereafter.
250
200
150
100
50
0 1 2 3 4 5 6 7 8
Chart 2 Medium Growth option for the M.S. in Computer Forensics
Version dated April 21, 2008 27 High Growth Option
In this growth option, the assumption is that 20 students are admitted in the first semester, 40 in the second, and 60 thereafter. Assuming that each student registers for two courses (6 credits each semester), the program will build to a cadre of 300 students in seven semesters. In the fifth semester, 20 students will graduate; 40 will graduate in the sixth semester and from the seventh semester, 60 students will graduate each semester. This is shown in Chart 3 below, with the horizontal axis being the semester (1 is fall 2009, 2 is spring 2010, and so on). Thus in academic year 2011/12, 60 students will graduate, and 120 students will graduate in each academic year thereafter.
350
300
250
200
150
100
50
0 1 2 3 4 5 6 7 8
Chart 3 High Growth option for the M.S. in Computer Forensics
Version dated April 21, 2008 28 Using the medium growth option, and assuming 1 FTE = 12 students taking a 3 credit hour course = 36 credit hours equivalent, the breakdown of student numbers and course hours will be as follows:
Year 1 – 20 entering in fall semester; 6 credits per semester; 120 credit hours = 3.333 FTE – 30 entering in spring semester; total of 50 students; 6 credits per student; 300 credit hours = 8.33 FTE; Total FTE for academic year = 11.667
Year 2 – 40 entering in fall semester; 6 credits per semester; 240 credit hours = 6.667 FTE; 50 students already in program; 6 credits per semester; 300 credit hours = 8.333 FTE; – 40 entering in spring semester; 6 credits per semester; 240 credit hours = 6.667 FTE; 90 students already in program; 6 credits per semester; 540 credit hours = 15.000 FTE; Total FTE for academic year = 36.667
Year 3 – 40 entering in fall semester; 6 credits per semester; 240 credit hours = 6.667 FTE; 130 students already in program; 6 cr. per semester; 390 credit hours = 10.833 FTE; 20 students graduate fall 2011 (start of year 3) – 40 entering in spring semester; 6 credits per semester; 240 credit hours = 6.667 FTE; net 150 students already in program; 6 cr. per semester; 900 credit hours = 25.000 FTE; 30 students graduate spring 2012 (end of year 3) Total FTE for academic year = 49.167
Year 4 – 40 entering in fall semester; 6 credits per semester; 240 credit hours = 6.667 FTE; net 160 already in program; 6 cr. per student; 960 credit hours = 26.667 FTE; 40 students graduate fall 2012 (start of year 4) – 40 entering in fall semester; 6 credits per semester; 240 credit hours = 6.667 FTE; net 160 already in program; 6 cr. per student; 960 credit hours = 26.667 FTE; 40 students graduate spring 2013 (end of year 4) Total FTE count = 66.667
Year 5 - As above, and for each subsequent year.
Version dated April 21, 2008 29 STATE COUNCIL OF HIGHER EDUCATION FOR VIRGINIA SUMMARY OF PROJECTED ENROLLMENTS IN PROPOSED PROGRAM
Projected enrollment: A) If the program starts in Spring 2009, it will attract approximately 15 students B) In subsequent years the program will attract students as shown below. Those numbers would be added to the initial group of 15.
Year 1 Year 2 Year 3 Year 4 Target Year
2009 - 2010 2010 - 2011 2011 - 2012 2012 - 2013 2013 - 2014
HDCT FTES HDCT FTES HDCT FTES HDCT FTES HDCT FTES GRAD 20 (f) 3.33 50(c) 15 + 130(c) 17.5 + 160(c) 33.33+ As on As on 80 + + + 21.67 + 31.67 + 33.33 2012- 2012- students 30(s) 8.33 40(f) 40(f) 40(f) 2013 2013 a year + -20(*) -40(*) 40(s) +40(s) +40(s) -30(*) -40(*)
Total Total Total Total Total Total Total Total is 130 is 160 is 200 is 50 11.67 36.67 49.167 66.67
(*) This is the number of students graduating in that semester f = fall semester s = spring semester c = continuing in program (existing students from prior semester)
Projected Faculty and Resource Needs
As noted on page 12 under the topic “Expansion of an Existing program”, it is not anticipated that any additional teaching faculty will be required for this program. Sufficient regular and adjunct professors are already available to take on the teaching assignments anticipated within this program. However, a program director will need to be in place at the start of program, together with an office assistant, to run the program.
At some point in the future, as the program expands, it is expected that additional computer lab resources will be required of a different nature to those currently used within the TFAS program. These computer lab resources will entail the use of isolated computer nets so that students undergoing training in forensics methods can conduct investigations that would not be appropriate for an open network, or one that is connected to the various university networks. It
Version dated April 21, 2008 30 is anticipated that the computer lab will be a cooperative venture within various university departments (or even schools) and some outside entities who have a strong interest in fostering computer forensics within their own establishments.
Full-time Faculty
It is anticipated that a new faculty position will be created to support the program. That faculty member could also become a candidate for the position of Director of the Master in Computer Forensics (CFRS) program. A support staff position will be needed. That position may be shared with another current staff position in a related program until the M.S. in Computer Forensics program becomes fully established. It is not anticipated that the proposed M.S. CFRS program will require any new regular faculty or staff resources in the initial year or two. Should the program grow as expected, additional full time faculty may be needed to enhance the teaching and research components and assist the director in running the program. These requests would be made through the normal university process at the appropriate time.
Part-time Faculty from Other Academic Units
No part-time faculty from other academic units are anticipated to be used specifically within the proposed CFRS program. However, it is anticipated that some of the CFRS students will opt to take elective courses in other academic units that are permitted elective courses within their CFRS degree. Those courses would be taken as part of that other academic unit’s regular program (e.g. LAW 181) and so the teaching function would be not within the CFRS unit, but in the other academic unit’s regular course offerings.
Adjunct Faculty
George Mason University is fortunate to have a relatively large pool of experienced adjunct faculty who not only regularly teach within George Mason University’s undergraduate and graduate programs, but who are also experts in their field. The proposed CFRS program will make use of a number of such topic experts, and experienced teachers. Examples include Mr. Robert Osgood (FBI Agent), Dr. Alexander Lazarevich, Dr. Tom Shackelford, and Ms. Angela Orebaugh (VSITE doctoral candidate). Contact has been made with other forensics experts who have indicated a strong desire to teach in the proposed CFRS program. All of the above adjunct faculty have taught for a number of years within related graduate programs (in particular the M.S. in Telecommunications and the TFAS certificate) and so it is anticipated that there will be good continuity within the teaching element of the program.
Graduate Assistants
It is anticipated that there will be graduate teaching assistants assigned to the proposed CFRS program should the number of enrolled students rise to the level where such support is granted by the dean. Typically, a class has to grow to at least 20 registered students before a TA is assigned to that class to assist the faculty member assigned to teach the class. In the initial stages of the CFRS program, it is not anticipated that an active research component will be in place, but
Version dated April 21, 2008 31 it is expected that a research element will develop around faculty recruited to teach the forensics courses. When an active research program develops, research assistants (RAs) will be recruited to assist in that portion of the program. The TA compensation will be drawn, as is usual, from the allocation provided by the School. RA compensation would be drawn from the research contract the faculty member was engaged in.
Classified Positions
It is anticipated that classified support will be required for the proposed CFRS program to assist the director of that program. For the first year of the CFRS program, a current staff member in another program may be assigned to handle the CFRS staff position duties in addition to those already allocated until the CFRS student body builds up. As currently projected, the staff position that will share the duties is that of the current M.S. in Telecommunications staff position. If, as expected, the CFRS program grows significantly, then the FTEs generated will permit the allocation of a full-time staff position to the CFRS program.
Targeted Financial Aid
No financial aid has been specifically targeted for the introduction of the CFRS program. However, it is likely that there are financial sources in the Washington, DC, area that would be very interested in being associated with the program and who would look favorably on supporting expansion of the program, particularly in the area of laboratory resources.
Equipment
For the first year of the proposed CFRS program, no additional equipment are anticipated to be needed to run the program as currently envisaged. However, it is anticipated that the program will grow in the complexity of the coursework undertaken, which will probably necessitate the development of additional computer laboratory resources. These resources would be capable of being totally separated from any other network on the campus so that advanced forensics search and research work can be undertaken without putting other networking resources at risk.
Library
No additional library resources will be required to start or run this program. It is anticipated that the normal library facilities would be used by the CFRS students, but nothing in addition to what is currently available is expected to be needed.
Telecommunications
Version dated April 21, 2008 32 The telecommunications requirements (telephone, FAX, etc.) will be handled for the first year, and possibly the second, through the M.S. in Telecommunications budget, and no significant additional resources are anticipated for this period. Should the CFRS program grow substantially, as expected, then this aspect will be revisited. Any additional (i.e. new) resources for the CFRS telecommunications budget under these growth situations would be funded out of the increased FTEs generated for the university.
Space
Adequate space will be available for this program. Currently, no additional space allocations are required over those that are currently envisioned in the new building in The Volgenau School of Information Technology and Engineering (VSITE) that will open in late Spring 2009. That building has sufficient space to accommodate the program. In addition, the existing Networking Lab serving the M.S. TCOM program in the Johnson Learning Center (room G10, 1400 sq.ft.) is equipped with significant network capabilities and computers and is perfectly capable of accommodating additional lab equipment to serve the growing needs of the M.S. CFRS program.
Other Resources
No other resources are anticipated for the proposed CFRS program, other than those already identified.
Version dated April 21, 2008 33 PROJECTED RESOURCE NEEDS FOR PROPOSED PROGRAM
Part A: Answer the following questions about general budget information.
Has or will the institution submit an addendum budget request to cover one-time costs? Yes No x Has or will the institution submit an addendum budget request to cover operating costs? Yes No x Will there be any operating budget requests for this program that would exceed normal operating budget guidelines (for example, unusual faculty mix, faculty salaries, or resources)? Yes No x Will each type of space for the proposed program be within projected guidelines? Yes x No Will a capital outlay request in support of this program be forthcoming? Yes No x
Part B: Fill in the number of FTE positions needed for the program.
Total expected by Program initiation year target enrollment year 2009 - 2010 2012 - 2013 Ongoing and Added Total FTE reallocated (new) Added* positions
Full-time faculty 0.00 1.00 1.00 2.00 Part-time faculty [faculty FTE split with other unit(s)] 0.00 0.00 0.00 0.00
Adjunct faculty 1.00 0.00 1.00 2.00
Graduate assistants 0.00 0.00 2.00 2.00
Classified positions 0.50 0.00 (#)1.00 (#)1.00
TOTAL 1.50 1.00 5.00 7.00
*Added after the program initiation year # 0.5 position originally from TCOM returned and a new 1.0 position allocated to CFRS
Version dated April 21, 2008 34 Part C: Estimated $$ resources to initiate and operate the program.
Total expected by Program initiation year target enrollment year 20__ - 20__ 20__ - 20__ Ongoing and Added Total reallocated (new) Added* resources Full-time faculty salaries $ $ $ $ fringe benefits $ $ $ $ Part-time faculty [faculty FTE split with other unit(s)] salaries $ $ $ $ fringe benefits $ $ $ $ Adjunct faculty salaries $ $ $ $ fringe benefits $ $ $ $ Graduate assistants salaries $ $ $ $ fringe benefits $ $ $ $ Classified positions salaries $ $ $ $ fringe benefits $ $ $ $ Total personnel costs salaries $ $ $ $ fringe benefits $ $ $ $ TOTAL personnel costs $ $ $ $ Equipment $ $ $ $ Library $ $ $ $ Telecommunication costs $ $ $ $ Other costs (specify) $ $ $ $ TOTAL $ $ $ $
*Added after program initiation year
Part D: Certification Statement(s)
The institution will require additional state funding to initiate and sustain this program.
Yes Signature of Chief Academic Officer
x No Signature of Chief Academic Officer
If “no,” please complete Items 1, 2, and 3 below.
Version dated April 21, 2008 35 1. Estimated $$ and funding source to initiate and operate the program.
Program initiation year Target enrollment year Funding Source 20__- 20__ 20__ - 20__ Reallocation within the department or school (Note below the impact this will have within the school or department.) Reallocation within the institution (Note below the impact this will have within the school or department.) Other funding sources (Please specify and note if these are currently available or anticipated.)
2. Statement of Impact/Other Funding Sources.
3. Secondary Certification. If resources are reallocated from another unit to support this proposal, the institution will not subsequently request additional state funding to restore those resources for their original purpose.
x Agree Signature of Chief Academic Officer
Disagree Signature of Chief Academic Officer
Version dated April 21, 2008 36 APPENDIX A Course Descriptions
(a) Basic Catalog descriptions
CFRS 500* Intro to Technologies of Forensics Value This course will present an overview of technologies of interest to forensics examiners. It will provide an introduction to operating systems, software, and hardware. ISA 522 Information Security Essentials
This course introduces basic concepts and techniques in applied information security. The course covers main concepts in information security, and their applications outside of the traditional engineering disciplines, such as healthcare, business, law and sociology. The course begins introducing the student to basic concepts of security including confidentiality, Integrity, Availability, and current concerns of anonymity, privacy and safety of web-based transactions, forensics investigations etc. It also covers the main safeguards available in security such as authentication, authorizations, network security. The course shows how these techniques are applied to the concerns of business, health care, nursing, sociology and law. ISA 562 Information Security Theory and Practice This course is a broad introduction to the theory and practice of information security. It serves as the first security course for the M.S.-ISA degree and is required as a prerequisite for all subsequent ISA courses (at the 600 and 700 levels). It also serves as an entry-level course available to non-ISA students, including M.S.-CS, M.S.-ISE, and M.S.-SWE students. CFRS 660 (Currently TCOM 660) Network Forensics This course deals with the collection, preservation, and analysis of network generated digital evidence such that this evidence can be successfully presented in a court of law (both civil and criminal). The relevant federal laws will be examined as well as private sector applications. The capture/intercept of digital evidence, the analysis of audit trails, the recordation of running processes, and the reporting of such information will be examined.
CFRS 661 (Currently TCOM 661) Digital Media Forensics This course deals with the collection, preservation, and analysis of digital media such that this evidence can be successfully presented in a court of law (both civil and criminal). The relevant federal laws will be examined as well as private sector applications. The seizure, preservation, and analysis of digital media will be examined in this course.
CFRS 663 (Currently TCOM 663) Operations of Intrusion Detection for Forensics Introduces students to network and computer intrusion detection and its relation to forensics. It addresses intrusion detection architecture, system types, packet analysis, and products. It also presents advanced intrusion detection topics such as intrusion prevention and active response, decoy systems, alert correlation, data mining, and proactive forensics.
1 CFRS 760* Legal and Ethics in IT This course will present legal and ethics topics in a forensics context. It will include cyber legal principles and types of crimes, witness testimony, and forensics report writing. CFRS 770* Fraud and Forensics in Accounting This course will present an overview of fraud discovered in digital accounting systems and the forensics of such systems.
CFRS 780* Advanced Topics Course Advanced topics from recent developments and applications in various areas of computer forensics are covered in this course. The advanced topics are chosen in such a way that they do not duplicate existing CFRS courses. Active participation of the students is encouraged in the form of writing and presenting papers in various research areas of the advanced topic. The course is designed to enhance the professional engineering community’s understanding of breakthrough developments in specific areas of computer forensics. Examples of topics are enterprise hardware systems and RAID, steganography, and cell phone and personal digital assistant (PDA) forensics. CFRS 790* Advanced Computer Forensics This course will be a capstone course that consolidates training before graduation and results in the completion of a major applied project. Some class time used for discussion of projects, either to monitor progress or explore alternative approaches. Readings, class-time discussion of current trends, difficulties, and new opportunities for industry most relevant to module. Concludes with presentations of projects. TCOM 662 Advanced Secure Networking This course deals with the advanced technologies in network security that can be applied to enhance enterprise and ISP’s network security. It covers the network perimeter defense concept and the various components for a complete layered defense system. It examines each component and its technologies, including TCP/IP protocol vulnerabilities, router access control list (ACL), dynamic ACL, firewall, network address translation (NAT), virtual private network (VPN), IPSec tunnels, intrusion detection system (IDS), routing protocol security, denial-of-service (DOS) attack, DOS detection and mitigation techniques.
ECE 511 Microprocessors
Introduces microprocessor software and hardware architecture. Includes fundamentals of microprocessor system integration, instruction set design, programming memory interfacing, input/output, direct memory access, interrupt interfacing, and microprocessor architecture evolution. Studies Intel family of microprocessors, and reviews other microprocessor families and design trends.
ECE 646 Cryptography and Computer-Network Security Topics include need for security services in computer networks, basic concepts of cryptology, historical ciphers, modern symmetric ciphers, public key cryptography (RSA, elliptic curve
2 cryptosystems), efficient hardware and software implementations of cryptographic primitives, requirements for implementation of cryptographic modules, data integrity and authentication, digital signature schemes, key exchange and key management, standard protocols for secure mail, www and electronic payments, security aspects of mobile communications, key escrow schemes, zero-knowledge identification schemes, Smart cards, quantum cryptography, and quantum computing. ECE 746 Secure Telecommunication Systems Discusses integration of cryptographic algorithms with standard and emerging communication protocols. Includes issues related to implementation of security services in different kinds of telecommunication networks and at different layers of network model; and selected cryptographic algorithms, including Advanced Encryption Standard and Elliptic Curve Crypto systems. Offers choice of cryptographic algorithm depending on type of network and implementation medium. Analyzes various means of implementing cryptographic transformations, including smart cards, desktop computers, routers, accelerator boards, and stand-alone devices. Criteria of choice between software and hardware implementations of cryptography.
INFS 785 Data Mining for Homeland Security Covers analytic techniques for investigative analysis. Topics include small world graphs as way to model groups and organizations, relational data mining with emphasis in predictive models, alias discovery techniques, and profiling.
ISA 562 Information Security Theory and Practice
This course is a broad introduction to the theory and practice of information security. It serves as the first security course for the M.S.-ISA degree and is required as a prerequisite for all subsequent ISA courses (at the 600 and 700 levels). It also serves as an entry-level course available to non-ISA students, including M.S.-CS, M.S.-ISE, and M.S.-SWE students.
ISA 650 Security Policy
The course focuses on security policy and its management for information systems having national and international connectivity. Issues include legal, international, cultural, and local factors. Students are expected to participate regularly in presenting material, in discussion of recent security issues, and by writing short papers on major current issues.
ISA 652 Security Audit and Compliance Testing
This course presents the fundamental concepts of the IT-security audit and control process that is being conducted in a plethora of environments, including government, financial industry and healthcare industry. The goal of this course is to enable the students to structure and perform audits based on the specifications of Sarbanes-Oxley, HIPAA and FISMA audit programs. The
3 course covers all the CISA certification requirements in depth and the students completing the course are encouraged to attempt the certification exam on their own.
ISA 656 Network Security
This course is an in-depth introduction to the theory and practice of network security. It assumes basic knowledge of cryptography and its applications in modern network protocols. The course studies firewalls architectures and virtual private networks and provides deep coverage of widely used network security protocols such as SSL, TLS, SSH, Kerberos, IPSec, IKE, and LDAP. It covers countermeasures to distributed denial of service attacks, security of routing protocols and the Domain Name System, e-mail security and spam countermeasures, wireless security, multicast security, and trust negotiation.
ISA 674 Intrusion Detection
Studies methodologies, techniques, and tools for monitoring events in computer system or network, with the objective of preventing and detecting unwanted process activity and recovering from malicious behavior. Topics include types of threats, host-based and network- based information sources, vulnerability analysis, denial of service, deploying and managing intrusion detection systems, passive vs. active responses, and designing recovery solutions.
ISA 785 Digital Forensics Research Focuses on research-related aspects of digital forensics including open problems in digital forensics, countermeasures against digital forensics, and fundamental and practical limitations of current digital forensics techniques. The course also covers currently established techniques and tools for digital forensics as well as common legal and ethical issues
LAW 181 Communications Law A treatment of basic telecommunications law, policy, and regulation.
SOCI 607 Criminology Crime and crime causation. Topics include social basis of law, administration of justice, and control and prevention of crime.
(b) Detailed Additional New Course Descriptions
These will be developed and submitted for approval through the regular university governance channels.
4 APPENDIX B Sample Schedules for M.S. in Computer Forensics Completion
(a)Course Offering Pattern (Only CFRS and ISA 562 course shown; electives will be taken as available in a given semester) Spring 2009 CFRS 500 and 660, and ISA 562 or ISA 522 Fall 2009: CFRS 500 and 660, and ISA 562 or ISA 522 Spring 2010: CFRS 500, 660, 661, 663, and ISA 562 or ISA 522 Fall 2010: CFRS 500, 660, 661, 663, 760, 770, and ISA 562 or ISA 522 Spring 2011: CFRS 500, 660, 661, 663, 760, 770, 780,790, and ISA 562 or ISA 522 The sequence is now complete
Note: depending on the student numbers, a summer course (or two) may be offered, in particular CFRS 500 and ISA 562.
(b)Example of a Full Time Student’s Plan of Study starting in Fall 2009
Year 1 Fall CFRS 500 or ISA 562, CFRS 660, CFRS 663 Spring Law 181, SOCI 607, CFRS 661
Year 2 Fall TCOM 662,CFRS 760, CFRS 770 Spring CFRS 790
(c)Example of a Part-Time Student’s Plan of Study starting in Fall 2009
Year 1 Fall CFRS 500 or ISA 562, CFRS 660 Spring Law 181, SOCI 607
Year 2 Fall CFRS 663, CFRS 760 Spring CFRS 661, TCOM 662
Year 3 Fall CFRS 780, CFRS 790 Spring
1 APPENDIX C Sample short bios for Faculty The full-time faculty members are listed grouped in departments. The departments are listed in alphabetical order. This listing is then followed by the list of current adjunct faculty members.
Applied Information Technology faculty (full time)
Dr. Don Gantz earned his MA in 1971 and his Ph.D. in 1974 from the University of Rochester. He is Professor and Chair of the Applied Information Technology Department. Among his research interests is identification of images such as those of fingerprints by computer analysis. His other research interests include mathematical economics, applied statistics, flight test analysis, computer performance engineering and capacity planning, computer simulation, and management decision systems. In recent years Dr. Gantz has developed cutting edge IT methodologies for the quantification and analysis of handwriting and is applying these methodologies to multi-language document exploitation and biometric identification. Handwriting derived computer biometric identification can be utilized in forensic document examination. Forensic document examination by computer combines the identification of individual handwriting samples based on personal features unique to each writer with a statistical foundation that will support expert witness testimony in court cases.
Dr. Anne Marchant received her PhD from UC Berkeley in 1990. She is currently an Associate Professor in the Department of Applied Information Technology teaching IT in the Global Economy, Information Warfare, and Computer Crime, Forensics, and Auditing. She won a GMU Teaching Excellence Award in 1999 while she was an instructor in the Computer Science Dept teaching programming. Prior to coming to George Mason, she was an instructor for the College of Engineering at UC Berkeley from 1990-1994. Her research interests include UAVs, computer forensics, as well as technology related ethical and social issues.
Computer Science faculty (full time)
Dr. Daniel Barbara is a professor in CS who earned his Ph.D. at Princeton University in 1985. He has had industrial experience with Bellcore and Matsushita, as well as experience on the faculty of Princeton and the Universidad Simon Bolivar, Caracas, Venezuela, before joining the faculty of George Mason University in 1997, where he is a full professor. His interests are in data mining and its applications.
Dr. Xuxian Jiang earned his Ph.D. from Purdue University in 2006, and is an assistant professor in the CS department. His research interests include system and network security, virtualization technology, distributed computing, with a specific research interest in virtual machines (VMs) and security.
Dr. Edgar H. Sibley has the permanent position of University Professor and Eminent Scholar with appointments in both the School of Information Technology and Engineering (Department of Information and Software Systems Engineering) and The Institute for Public Policy at George Mason University in Fairfax VA. He earned his ScD degree from MIT in 1967. He has been
1 active in all areas of large scale information and general systems design for many major governmental agencies and business organizations. This has recently included work with the IRS, Department of Defense, and Department of Energy, as well as joint contract efforts with the Boeing Corporation, Batelle, and SAIC, and many small businesses in the DC area. He has also acted as an expert witness for four law firms.
Dr. Robert Simon received his Ph.D. in Computer Science from the University of Pittsburgh in August 1996. He also has a B.A. in History and Political Science from the University of Rochester. His research specialization is in the field of distributed systems, networks, performance modeling and simulation. He teaches courses in networks, mobile and wireless computing, operating systems, computer architecture and computer security.
Dr. Frank Wang earned his Ph.D. from North Carolina State University in 2004. He is an assistant professor in the CS department with research interests in network security, intrusion source tracing, and active intrusion response. He is particularly interested in computer and network security, with particular reference to network-based intrusion source tracing problem under various settings. His other areas include intrusion detection and response, botnet, virus and worm, VoIP security, information hiding, steganography, privacy and anonymity and their interactions with security.
Dr. Duminda Wijesekera earned two doctorates, one from the University of Minnesota and one from Cornell. Both doctorates were in computer science and logic. He is an associate professor in the CS department, although he holds courtesy appointments at the Center for Secure Information Systems (CSIS) and the Center for Command, Control, Communication and Intelligence (C4I) at George Mason University, and the Potomac Institute of Policy Studies in Arlington, VA. During various times, his research interests have been in security, multimedia, networks, secure signaling (telecom, railway and SCADA), avionics, missile systems, web and theoretical computer science. Prior to GMU, he was at Honeywell Military Avionics, Army High Performance Research Center at the University of Minnesota, and the University of Wisconsin.
Electrical and Computer Engineering faculty (full time)
Dr. Kris Gaj received his the M.Sc. and Ph.D. degrees in Electrical Engineering from Warsaw University of Technology, Warsaw, Poland. His research interests include cryptography, computer arithmetic, reconfigurable computing, software-hardware co-design, and computer- network security.
Dr. David Hwang received the B.S., M.S., and Ph.D. degrees in electrical engineering from the University of California, Los Angeles (UCLA) in 1997, 2001, and 2005, respectively. His research interests include secure embedded systems, cryptographic hardware and circuits, digital signal processing architectures (FPGA/ASIC), and VLSI digital systems and circuits.
Dr. Jens-Peter Kaps earned a Dipl. Ing. at the Fachhochschule München (Munich University of Applied Sciences) in 1996, an M.Sc. from Worcester Polytechnic Institute in , followed by a Ph.D. from Worcester Polytechnic Institute in 2006. He is an assistant professor of electrical and
2 computer engineering at the Volgenau School of Information Technology at George Mason University. His research interests include ultra-low-power cryptographic hardware design, computer arithmetic, efficient cryptographic algorithms, and computer and network security.
Dr. Ken Hintz received his B.S. degree in Electrical Engineering from Purdue University, West Lafayette, Indiana in 1967 and his M.S. and Ph.D. degrees in Electrical Engineering from the University of Virginia in 1979 and 1981 respectively. Since 1987 he has been an Associate Professor in the Department of Electrical and Computer Engineering at George Mason University. He designed and established the Bachelor and Masters in Computer Engineering Degree Programs at GMU which were approved by SCHEV in June 1998 and 1999, respectively. Before joining GMU, Dr. Hintz was with the Naval Surface Warfare Center, Dahlgren, VA, working in electronic warfare and radar signal processing where he designed and built the AN/ULQ-16, variations of which are still in production. Prior to working at NSWC, Dr. Hintz was with the U. S. Navy as a designated Naval Aviator stationed for 3 years in Rota, Spain flying Electronic Warfare Reconnaissance with Fleet Air Reconnaissance Squadron Two (VQ- 2). During that time be became designated Electronic Warfare Aircraft Commander (EWAC) in both the EC-121 and EP-3E aircraft. He holds seven patents, is a Senior Member of IEEE, a member of SPIE, and is lead author on a book on Microcontrollers. His current research interest is in syntactic pattern recognition applied to ground penetrating radar images for landmine detection and classification. His other research interests are in information-based real-time sensor management, X-ray, thermal, and visual, image processing, as well as computer architectures and algorithms for real time signal and image processing.
Dr. Qiliang Li Received the B.S. and M.S. degrees in physics from Nanjing University, Nanjing, China, in 1996 and 1999 respectively. He received the Ph.D. in electrical and computer engineering from North Carolina State University in 2004. Dr. Li joined GMU in Fall 2007 as an Assistant Professor of Electrical and Computer Engineering and a Virginia Microelectronics Consortium Professor. He is an expert in nano-devices, with potential applications to forensics.
Dr. Rao Mulpuri received the Bachelor of Technology in electronics and communications engineering from Jawaharlal Nehru Technological University (Kakinada, India) in 1977. In 1979, he received the Master of Technology degree in material science from the Indian Institute of Technology (Bombay) and in 1983 received the M.S. degree in electrical engineering from Oregon State University, followed by the Ph.D. degree in electrical engineering from Oregon State University in 1985. Dr. Mulpuri's present areas of research interest are large bandgap semiconductor (SiC, GaN, etc) materials, and devices (ion-implantation doping, ohmic contacts, device fabrication, material and device characterization). Recently he led a research project on micro-chip forensics. He joined GMU in September 1984, and became a Professor of Electrical and Computer Engineering in September 1993.
Dr. Andre Z. Manitius received his Ph.D. degree from the Polytechnical University of Warsaw, Warsaw, Poland in 1968. From 1968 to 1972 he held a junior faculty position with the Institute of Automatics of the Polytechnical University of Warsaw. In 1972 and 1973 he was a Visiting Associate Professor with the Center for Control Sciences at the University of Minnesota. He subsequently joined the Mathematical Research Center at the University of Montreal, Quebec, Canada, where he was an Associate and then Full Research Professor until 1981. From 1981 to
3 1988 he was a Professor in the Mathematical Sciences Department of the Rensselaer Polytechnic Institute (RPI) in Troy, New York. While on leave from RPI, he served as Program Director for Applied Mathematics (1986-1987) and Deputy Director, Division of Mathematical Sciences (1987-88) at the National Science Foundation in Washington, D.C. He joined George Mason University in September 1988 as Professor of Electrical and Computer Engineering. Dr. Manitius’ research interests include mathematical aspects of control theory, including control of distributed parameter and delay systems, optimal control, optimization, numerical and computational methods in dynamical systems and control systems. He has published over 70 papers in his fields of interest, and held various editorial positions with several professional journals. In 1991 he received American Mathematical Society's Citation for Public Service related to his earlier work at the NSF.
Dr. Jeremy Allnutt earned his B.Sc. and Ph.D. in electrical engineering from the University of Salford, UK, in 1966 and 1970, respectively. From 1970 to 1977 he was at the Appleton Laboratory in Slough, England, where he ran propagation experiments with the US satellite ATS-6 and the European satellites SIRIO and OTS. In 1977 he moved to BNR, now Nortel, in Ottawa, Canada, and worked on satellite and rural communications projects before joining the International Telecommunications Satellite Organization (INTELSAT) in Washington, DC, in 1979. Dr. Allnutt spent 15 years at INTELSAT in various departments. During this period he ran experimental programs in Europe, Asia, Africa, North and South America, Australia, and New Zealand, finishing as Chief, Communications Research Section. Dr. Allnutt spent one year as Professor of Telecommunications Systems at the University of York, England, and then joined the Northern Virginia Center of Virginia Tech in 1986, where he later ran the masters program in ECE as well as being on the team that designed and set up the Masters in Information Technology program. In August of 2000 he moved to George Mason University with dual appointments: Director of the new Masters in Telecommunications program (http://telecom.gmu.edu/) and Professor in the ECE department. Dr. Allnutt has published 100 papers in conferences and journals and written one book, most in his special field: radiowave propagation. He is a Fellow of the UK IEE (now called IET) and a Fellow of the US IEEE.
Part time faculty (Adjunct professors)
Special Agent Bob Osgood is currently Chief of Digital Media exploitation for the FBI’s Counterterrorism Division. He has over 20 years of experience in the fields of computer forensics and Cyber crime. SA Osgood has an M.S. in Network Engineering, is a Cisco engineer, A+ and Net + certified. SA Osgood currently teaches Digital Media Forensics and Network Forensics in the GMU TFAS program.
Special Agent James R. Durie is currently Field Operations Program Manager for the FBI’s Computer Analysis Response Team (CART). He has over 20 years of experience in law enforcement and forensics including seven years a FBI Computer Forensic Examiner. Mr. Durie has a BS in Police Science and Law Enforcement and a Juris Doctorate. He is A+ certified and is an Encase Certified Examiner (EnCE). Mr. Durie currently teaches Computer Forensics for New Agents at the FBI Academy and lectures around the world on Computer Forensics and related topics. He also testifies across the country on Adam Walsh Act discovery issues. He has
4 testified in over 100 hearings and trials as a lead investigator or an expert witness. Mr. Durie developed dual processor computers as a computer forensic platform with forensic network support. He also experimented with Distributed Network Analysis networks for password identification. He is researching computer forensics and virtual worlds and coordinates the identification, testing, and validation of new tools for use in forensic examinations for the FBI's computer forensics program.
Ms. Angela Orebaugh is an internationally recognized security technologist, scientist, and author, with over 15 years of experience. Ms. Orebaugh is a Guest Researcher for the National Institute of Standards and Technology (NIST), where she leads several security initiatives including the authoring of security special publications, the National Vulnerability Database (NVD), and electronic voting. At GMU she developed and taught the Intrusion Detection curriculum, a core requirement of the TFAS program. Her current research interests include peer-reviewed publications in the areas of intrusion detection and prevention, data mining, attacker profiling, user behavior analysis, and network forensics. Ms. Orebaugh has a broad spectrum of professional experience in information security, with hands-on expertise in security architecture design and analysis, perimeter defense, vulnerability assessment and penetration testing, forensics, intrusion detection and prevention, and incident handling and response. Ms. Orebaugh is the author of several books on information security, and is currently scheduled to defend her Ph.D. dissertation in spring 2008.
Dr. Aleksandar Lazarevich is a Senior Computer/Electronics Engineer with the Defense Information Systems Agency. He is the operations managers and the Test Evaluation lead for the DoD PKI program. He is an adjunct Professor with George Mason University and Masters Degree program chair for the University of Fairfax. He has been the IT College Campus Chair and the Area Chair for Networking and Operating Systems at the Northern Virginia campus of University of Phoenix for two years and the IT department chair at WIU for four years. He has over 33 years experience of Federal Civil Service in the field of Information Systems security engineering and computer forensics. He holds the rank of Senior Member of the Institute of Electrical and Electronics Engineers. He completed a PhD in Information Technology with an emphasis in Information Assurance and computer forensics at George Mason University. His research has been in the area of artificial intelligence modeling of evidence assessment. He primarily teaches information security and computer forensic classes. He has represented the U.S. Government in international forums for over three decades and has received recognition for his expertise from numerous nations. Dr. Lazarevich was responsible for major information system programs for such organizations as the White House Communications Agency, Executive Office of the President and the Deputy Under Secretary of Defense for Logistics. He was elected to the 2001 International Who’s Who of Information Technology.
Dr. Thomas Shackelford has been working with computers and software design since 1986, where his primary focus was with database administration, data management, and data analysis. From here his career has taken him through various programming and network engineering disciplines from main frames through client server environments. He currently works as the Information Assurance Manager overseeing security design and implementation for a major financial system. He received his Bachelors of Science Degree in Computer Science from Chapman University, a Master of Science Degree in Information Systems Engineering from
5 Western International University, and a Doctorate in Philosophy degree in Information Technology with a special emphasis in computer security from George Mason University. His Dissertation topic was “The Use of Advanced Data Mining Techniques to Develop Measures of Document Relevance”. The purpose of the papers was to study how document relevance could be used to track insider threat in a networked environment. Dr. Shackelford’s interests are in Network engineering, Computer Security, Data Mining, Text Categorization, Insider Threat Detection, and Data Forensics.
6 APPENDIX D Sample Job Announcements with URL and Date
Most advanced computer forensics positions are listed on the web site of the leading computer forensics association, the International High Technology Crime Investigation Association (with the acronym HTCIA, rather than IHTCIA) - http://www.htcia.org/cgi-bin/chapters.cgi
There are 41 chapters currently affiliated with the HTCIA, some international (Brazil, Canada, UK) but most in the USA. The chapter that covers Virginia is the “Mid-Atlantic Chapter” (http://www.htcia.org/cgi-bin/chapters.cgi?idChapter=7)
All chapters have job postings that are for the area covered by the chapter. On the Mid-Atlantic chapter’s web site, there were 18 positions advertised, the oldest dating from May 8th, 2007 and the most recent October 4th, 2007. The positions range from what could be considered to be entry level positions (Computer Forensics Specialist – Washington, DC) to senior level positions (Senior Electronic Data Examiner, Falls Church, VA). Both positions are given below, extracted on October 8 th , 2007.
Employment Opportunity – Computer Forensic Specialist (Washington, D.C.)
(No pdf; the advertisement was extracted in Word format from the web listing http://www.htcia.org/cgi-bin/chapters.cgi?idChapter=7 selecting the listing with the above title on October 8th, 2007)
The High Technology Investigative Unit (HTIU) within the Child Exploitation and Obscenity Section (CEOS) of the U.S. Department of Justice initiates investigations and conducts forensic analysis on computer evidence in federal cases involving child exploitation and obscenity crimes. It works closely with federal law enforcement agencies such as the FBI, Immigration and Customs Enforcement (ICE), Secret Service, and the Postal Inspection Service; as well as federal prosecutors all across the country. The mission of the HTIU is simple: Provide the most accurate, up-to-date expertise on computer forensic matters and assist law enforcement in bringing criminals who peddle in child exploitation and obscenity to justice.
The HTIU goes far beyond the bits and bytes of standard computer forensic examinations. HTIU specialists are routinely asked to assist in national operations involving child exploitation over the internet, special investigative initiatives, and research and develop new investigative tools and techniques. In addition, HTIU specialists may be asked to assist in drafting proposed legislation, developing and delivering training for law enforcement agencies, and testify as experts in federal court. HTIU specialists frequently travel to various field offices to assist in the prosecution of some of the worst criminal offenders.
The HTIU is expanding and currently has a need for qualified computer forensic investigators. Candidates should have extensive knowledge in computer forensics and computer investigations, Internet technologies, and an educational background in CS or similar degree. Previous programming and applications development experience as well as experience in *nix OSs are highly desirable.
1 Salary range is $46,041 to $103,220.
For how to apply, see Vacancy No. 07-CRM-KS-049 at www.usajobs.gov
For additional information about this position, please contact [email protected]
Senior Electronic Data Examiner, Falls Church, VA (http://www.htcia.org/classified/sedfe.pdf October 8th, 2007)
Capital Legal Solutions is a highly innovative electronic service provider headquartered in Falls Church, VA, part of the metro DC area region. Founded in 2002, we have rapidly expanded from a vision to equip the legal community with cost effective, technology driven litigation support to an industry leading electronic discovery provider.
Currently we are seeking a qualified SENIOR ELECTRONIC DATA FORENSICS EXAMINER.
The ideal candidate will have: Superior management and client relationship skills Experience overseeing fully defensible preservation of electronic data (including by HD image acquisition) within large corporations The ability to forensically harvest data from a wide variety of sources and storage media Extensive background in preparing written reports General networking and strong hardware knowledge are necessities Be familiar with providing expert testimony ENCASE certification and familiarity with FTK and LINUX is a plus. Compensation will be highly competitive and based upon experience, training and educational background.
To apply for this position, please send your resume to: Robert Eisenberg Vice President—E-Discovery Consulting CAPITAL LEGAL SOLUTIONS, LLC 150 S. WASHINGTON ST. SUITE 500 FALLS CHURCH, VA 22046 Tel: 703-226-1544 Fax: 703-226-1550 Email: [email protected] For more information about our company and this position, please visit our website at www.capitallegals.com .
2 APPENDIX E Survey Instrument
George Mason University is developing a Master’s in Computer Forensics program for implementation beginning in Spring 2009. The proposed M.S. in Computer Forensics will prepare students for careers in industry, government, and academia by combining academic education with real world practical techniques. Emphasis is placed in the program on training students to use and apply computer forensics methods and knowledge in a variety of real life scenarios. Computer forensic examiners (CFE) work in both the public and private sectors, and the Washington, D. C. area is home to a large work force of CFEs. These CFEs work for the FBI, DEA, USSS, as well as with the vast majority of Inspectors General and local police departments. Practically all of the major accounting and consulting firms employ computer forensic examiners on staff, and there is a growing cadre of independent consultants that work in this field. The American Society of Crime Lab Directors (ASCLAD), the governing association in the field forensics sciences, requires that all computer forensic examiners possess a bachelors degree with significant course work in math and science. As a result of successfully completing this program, students should have the necessary skills and knowledge to perform in a variety of computer forensic roles, including forensics examiner, and the ability to earn an advanced degree. We have prepared the survey below to gauge interest in the program. Your answers to the following questions will be used in summary form only. No personally-identifiable information will be released. Please feel free to contact Dr. Jeremy Allnutt at [email protected] if you would like more information about the proposed program.
Thank you.
3 1. Would you be interested in enrolling in a program like this? Yes No (If no, then skip to question 3.)
2. If yes, would you prefer to attend the program on a full-time or part-time basis? Full- Part- time time Not sure 3. Have you ever applied to an institution offering a similar program? If so, which program, at which school? Yes No
4. Are you currently attending George Mason University? Yes No If so, in what program:
5. FOR STUDENTS CURRENTLY IN MASON PROGRAM.S. AT THE SAME LEVEL: Yes No If this program had been available when you initially applied to Mason, would you have applied for admission to it?
6. FOR STUDENTS CURRENTLY IN MASON PROGRAM.S. AT THE SAME LEVEL: Are you currently Yes No enrolled, or are thinking of enrolling in, a certificate as part of your master’s degree? If you answered yes, could you please put down the name or acronym of the certificate (e.g. TFAS, ANPT, and WIRE).
Certificate program:……………………………………………….
7. FOR STUDENTS WHO LEFT MASON TO PURSUE EDUCATION ELSEWHERE: Yes No If this program had been available when you completed your current program, would you have applied for admission?
8. FOR STUDENTS WHO LEFT MASON BUT HAVE NOT PURSUED FURTHER EDUCATION: If this program had been available when you completed your current program, would you have applied for Yes No admission?
9. FOR STUDENTS WHO ANSWERED “Yes” TO QUESTIONS 5, 7, OR, 8, COULD YOU PLEASE TELL US WHAT YOUR PRINCIPAL BACKGROUND IS IN TERM.S. OF YOUR CURRENT JOB OR INTEREST (Please check the most appropriate area below) (a) IT …………. ………. (b) Legal …………..……….. (c) ADJ ….....…………….
(d) Accounting ………… (e) Law enforcement ………. (f) Teacher ……………….
(g) Other ……………… (Please explain below)
10. FOR STUDENTS WHO ANSWERED “Yes” TO QUESTIONS 5, 7, OR, 8, COULD YOU PLEASE TELL US WHAT PART OF COMPUTER FORENSICS INTERESTS YOU THE MOST (Please check the appropriate area bellow) (a) Hardware Forensics ………………. (b) Software Forensics ……………….
(c) Network Forensics .……………….. (d) Search and Seizure ……………….
(e) Trap and Trace ……………………. (f) Law and Ethics as related to
4 Computer Forensics ……………… (g) Other (Please explain bellow)
11. In which state do you currently live? Virginia Maryland If you answered “Other”, which state or country (if not the USA) do you live in?
………………………………………………………………….. DC Other
12. Do you plan to live in this state or country for the next three or four years? Yes No
13. Are you currently employed? (If not, then skip to 17.) Yes No
14. If you are employed, please identify the state in which you work. Virginia Maryland If you answered “Other”, could you please tell us where you currently work
……………………………………. DC Other
15. If you are employed, are you employed full-time or part-time? Full- Part- time time
16. If you are employed, would the proposed program help you in your work? Yes No
17. Please feel free to provide below any additional comments about the proposed program
5 Responses on October 8th, 2007 to the web-based questionnaire The Questionnaire became “live” on Friday, October 5th, 2007. The responses below were taken over the Columbus Day weekend.
Q1. Would you be interested in enrolling in a program like this?
Response answer options Percent Response Count Yes 90.6% 135 No 10.1% 15 answered question 149 skipped question 0
Q2. Would you prefer to attend the program on a full-time or part-time basis?
Response answer options Percent Response Count Full-time 28.0% 37 Part-time 60.6% 80 Not sure 11.4% 15 answered question 132 skipped question 17
Q3. Which campus of George Mason would you prefer:
Response answer options Percent Response Count Fairfax 73.5% 97 Prince William 24.2% 32 Loudon 2.3% 3 answered question 132 skipped question 17
Q4. Which type of classes do you prefer:
Response answer options Percent Response Count Distance Education (online) 3.0% 4 Traditional Lecture (face-to-face) 44.4% 59 A combination of both distance and traditional. 52.6% 70 answered question 133 skipped question 16
Q5. Have you ever applied to an institution offering a similar program?
6 Response answer options Percent Response Count Yes 1.4% 2 No 98.6% 145 answered question 147 skipped question 2
Q6. If so, which program, at which school?
Response Response answer options Percent Count Program 100.0% 4 School 100.0% 4 answered question 4 skipped question 145
Q7. Are you currently attending George Mason University?
Response Response answer options Percent Count No 17.7% 26 Yes 82.3% 121 (Please specify program) 110 answered question 147 skipped question 2
Q8. Are you a former GMU student?
Response Response answer options Percent Count Yes 65.4% 17 No 34.6% 9 answered question 26 skipped question 123
Q9. FOR STUDENTS WHO LEFT MASON TO PURSUE EDUCATION ELSEWHERE: If this program had been available when you completed your current program would you have applied for admission?
Response Response answer options Percent Count Yes 80.0% 4
7 No 20.0% 1 answered question 5 skipped question 144
Q10. FOR STUDENTS WHO LEFT MASON BUT HAVE NOT PURSUED FURTHER EDUCATION: If this program had been available when you completed your current program, would you have applied for admission?
Response Response answer options Percent Count Yes 70.0% 7 No 30.0% 3 answered question 10 skipped question 139
Q11. FOR STUDENTS CURRENTLY IN MASON PROGRAM.S. AT THE SAME LEVEL: If this program had been available when you initially applied to Mason would you have applied for admission to it?"
Response Response answer options Percent Count Yes 74.4% 61 No 25.6% 21 answered question 82 skipped question 67
Q12. FOR STUDENTS CURRENTLY IN MASON PROGRAM.S. AT THE SAME LEVEL: Are you currently enrolled, or are thinking of enrolling in, a certificate as part of your master’s degree?
Response Response answer options Percent Count Yes 49.4% 39 No 50.6% 40 answered question 79 skipped question 70
Q13. Please enter the name or acronym of the certificate (e.g. TFAS, ANPT, and WIRE).
Response Count 22 answered question 22 skipped question 127
Q14. Please tell us what your principal background is in terms of your current job or interest:
answer options Response Response
8 Percent Count IT 94.7% 125 Legal 0.0% 0 Law Enforcement 3.8% 5 Administration of Justice 0.8% 1 Accounting 0.0% 0 Teacher 0.8% 1 Other (please specify) 15 answered question 132 skipped question 17
Q15. Please tell us what part of computer forensics interests you the most:
answer options Response Percent Response Count Hardware Forensics 19.0% 26 Software Forensics 22.6% 31 Network Forensics 38.7% 53 Search and Seizure 6.6% 9 Law and Ethics 6.6% 9 Trap and Trace 6.6% 9 Other (please specify) 2 answered question 137 skipped question 12
Q16. In which state do you currently live?
answer options Response Percent Response Count DC 0.7% 1 Maryland 0.0% 0 Virginia 99.3% 140 Other (please specify) 0 answered question 141 skipped question 8
Q17. Do you plan to live in this state or country for the next three or four years?
answer options Response Percent Response Count Yes 93.6% 132 No 6.4% 9 answered question 141 skipped question 8
Q18. Are you currently employed?
answer options Response Percent Response Count Yes 83.0% 117
9 No 17.0% 24 answered question 141 skipped question 8
Q19. Please identify the state in which you work:
answer Response options Percent Response Count DC 8.5% 10 Maryland 4.2% 5 Virginia 87.3% 103 Other (please specify) 0 answered question 118 skipped question 31
Q20. Are you employed full-time or part-time?
answer Response options Percent Response Count Full-time 64.1% 75 Part-time 35.9% 42 answered question 117 skipped question 32
Q21. Would the proposed program help you in your work?
answer Response options Percent Response Count Yes 65.8% 77 No 34.2% 40 answered question 117 skipped question 32
Q22. Please feel free to provide below any additional comments about the proposed program:
Response Count 30 answered question 30 skipped question 119
10 APPENDIX F Assumptions Used in Developing Resource Projections
Faculty FTE
Undergraduate: 18 student FTE = 1 faculty FTE Graduate: 12 student FTE = 1 faculty FTE Adjunct: 8 3-credit courses/year = 1 faculty FTE GTA: 4 3-credit courses/year = 1 full-time GTA = 0.5 FTE
Salary
Full professor: $90,000 Assistant professor: $60,000 Adjunct: $1,070/credit (undergraduate) $1,150/credit (graduate) 1 FTE = 8 classes * 3 credits/class * adjunct rate GTA: $22,000 ($10,000 stipend + $12,000 tuition) GRA: $24,000 ($12,000 stipend + $12,000 tuition) Pres. Scholar GRA: $30,000 ($18,000 stipend + $12,000 tuition)
Fringe benefits
Full-time faculty: .2765 Adjunct: .0765 Classified: .3541 Admin faculty: .2825 GTA: 0
Equipment
New full-time faculty and staff get a computer: $2,000 New full-time faculty and staff get a desk and chair: $3,000
Telecommunications
New faculty and staff get a telephone: $750 Annual charges: $240
11