Reference List of Indexed Articles
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Concurrent Objects and Linearizability Concurrent Computaton
Concurrent Objects and Concurrent Computaton Linearizability memory Nir Shavit Subing for N. Lynch object Fall 2003 object © 2003 Herlihy and Shavit 2 Objectivism FIFO Queue: Enqueue Method • What is a concurrent object? q.enq( ) – How do we describe one? – How do we implement one? – How do we tell if we’re right? © 2003 Herlihy and Shavit 3 © 2003 Herlihy and Shavit 4 FIFO Queue: Dequeue Method Sequential Objects q.deq()/ • Each object has a state – Usually given by a set of fields – Queue example: sequence of items • Each object has a set of methods – Only way to manipulate state – Queue example: enq and deq methods © 2003 Herlihy and Shavit 5 © 2003 Herlihy and Shavit 6 1 Pre and PostConditions for Sequential Specifications Dequeue • If (precondition) – the object is in such-and-such a state • Precondition: – before you call the method, – Queue is non-empty • Then (postcondition) • Postcondition: – the method will return a particular value – Returns first item in queue – or throw a particular exception. • Postcondition: • and (postcondition, con’t) – Removes first item in queue – the object will be in some other state • You got a problem with that? – when the method returns, © 2003 Herlihy and Shavit 7 © 2003 Herlihy and Shavit 8 Pre and PostConditions for Why Sequential Specifications Dequeue Totally Rock • Precondition: • Documentation size linear in number –Queue is empty of methods • Postcondition: – Each method described in isolation – Throws Empty exception • Interactions among methods captured • Postcondition: by side-effects -
Computer Science 322 Operating Systems Topic Notes: Process
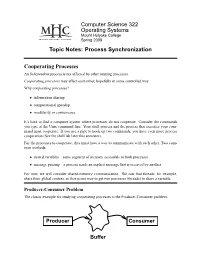
Computer Science 322 Operating Systems Mount Holyoke College Spring 2008 Topic Notes: Process Synchronization Cooperating Processes An Independent process is not affected by other running processes. Cooperating processes may affect each other, hopefully in some controlled way. Why cooperating processes? • information sharing • computational speedup • modularity or convenience It’s hard to find a computer system where processes do not cooperate. Consider the commands you type at the Unix command line. Your shell process and the process that executes your com- mand must cooperate. If you use a pipe to hook up two commands, you have even more process cooperation (See the shell lab later this semester). For the processes to cooperate, they must have a way to communicate with each other. Two com- mon methods: • shared variables – some segment of memory accessible to both processes • message passing – a process sends an explicit message that is received by another For now, we will consider shared-memory communication. We saw that threads, for example, share their global context, so that is one way to get two processes (threads) to share a variable. Producer-Consumer Problem The classic example for studying cooperating processes is the Producer-Consumer problem. Producer Consumer Buffer CS322 OperatingSystems Spring2008 One or more produces processes is “producing” data. This data is stored in a buffer to be “con- sumed” by one or more consumer processes. The buffer may be: • unbounded – We assume that the producer can continue producing items and storing them in the buffer at all times. However, the consumer must wait for an item to be inserted into the buffer before it can take one out for consumption. -

4. Process Synchronization
Lecture Notes for CS347: Operating Systems Mythili Vutukuru, Department of Computer Science and Engineering, IIT Bombay 4. Process Synchronization 4.1 Race conditions and Locks • Multiprogramming and concurrency bring in the problem of race conditions, where multiple processes executing concurrently on shared data may leave the shared data in an undesirable, inconsistent state due to concurrent execution. Note that race conditions can happen even on a single processor system, if processes are context switched out by the scheduler, or are inter- rupted otherwise, while updating shared data structures. • Consider a simple example of two threads of a process incrementing a shared variable. Now, if the increments happen in parallel, it is possible that the threads will overwrite each other’s result, and the counter will not be incremented twice as expected. That is, a line of code that increments a variable is not atomic, and can be executed concurrently by different threads. • Pieces of code that must be accessed in a mutually exclusive atomic manner by the contending threads are referred to as critical sections. Critical sections must be protected with locks to guarantee the property of mutual exclusion. The code to update a shared counter is a simple example of a critical section. Code that adds a new node to a linked list is another example. A critical section performs a certain operation on a shared data structure, that may temporar- ily leave the data structure in an inconsistent state in the middle of the operation. Therefore, in order to maintain consistency and preserve the invariants of shared data structures, critical sections must always execute in a mutually exclusive fashion. -

The Critical Section Problem Problem Description
The Critical Section Problem Problem Description Informally, a critical section is a code segment that accesses shared variables and has to be executed as an atomic action. The critical section problem refers to the problem of how to ensure that at most one process is executing its critical section at a given time. Important: Critical sections in different threads are not necessarily the same code segment! Concurrent Software Systems 2 1 Problem Description Formally, the following requirements should be satisfied: Mutual exclusion: When a thread is executing in its critical section, no other threads can be executing in their critical sections. Progress: If no thread is executing in its critical section, and if there are some threads that wish to enter their critical sections, then one of these threads will get into the critical section. Bounded waiting: After a thread makes a request to enter its critical section, there is a bound on the number of times that other threads are allowed to enter their critical sections, before the request is granted. Concurrent Software Systems 3 Problem Description In discussion of the critical section problem, we often assume that each thread is executing the following code. It is also assumed that (1) after a thread enters a critical section, it will eventually exit the critical section; (2) a thread may terminate in the non-critical section. while (true) { entry section critical section exit section non-critical section } Concurrent Software Systems 4 2 Solution 1 In this solution, lock is a global variable initialized to false. A thread sets lock to true to indicate that it is entering the critical section. -

OPTIMAL SOLUTIONS and RANKS in the MAX-CUT SDP Daniel
COVER PAGE: OPTIMAL SOLUTIONS AND RANKS IN THE MAX-CUT SDP Daniel Hong, Skyline High School, Sammamish, WA, USA Hyunwoo Lee, Interlake High School, Bellevue, WA, USA Alex Wei, Interlake High School, Bellevue, WA, USA Instructor: Diego Cifuentes, Massachusetts Institute of Technology, Cam- bridge, MA, USA 1 OPTIMAL SOLUTIONS AND RANKS IN THE MAX-CUT SDP DANIEL HONG, HYUNWOO LEE, AND ALEX WEI Abstract. The max-cut problem is a classical graph theory problem which is NP-complete. The best polynomial time approximation scheme relies on semidefinite programming (SDP). We study the conditions under which graphs of certain classes have rank 1 solutions to the max-cut SDP. We apply these findings to look at how solutions to the max-cut SDP behave under simple combinatorial constructions. Our results determine when solutions to the max-cut SDP for cycle graphs is rank 1. We find the solutions to the max-cut SDP of the vertex sum of two graphs. We then characterize the SDP solutions upon joining two triangle graphs by an edge sum. Keywords: Max-cut, Semidefinite program, Rank, Cycle graphs, Ver- tex sum, Edge sum Contents 1. Introduction 2 Related work 3 Structure 3 2. Background 4 2.1. Semidefinite programs 4 2.2. Max-cut SDP 4 2.3. Clique sums of graphs 6 3. Experiments on rank of max-cut SDP 6 4. Solutions and Ranks for Particular Classes of Graphs 7 4.1. Rank 1 solutions for cycles 7 4.2. Max-cut SDP for a vertex sum 8 4.3. Max-cut SDP for a diamond graph 9 5. -

Rtos Implementation of Non-Linear System Using Multi Tasking, Scheduling and Critical Section
Journal of Computer Science 10 (11): 2349-2357, 2014 ISSN: 1549-3636 © 2014 M. Sujitha et al ., This open access article is distributed under a Creative Commons Attribution (CC-BY) 3.0 license doi:10.3844/jcssp.2014.2349.2357 Published Online 10 (11) 2014 (http://www.thescipub.com/jcs.toc) RTOS IMPLEMENTATION OF NON-LINEAR SYSTEM USING MULTI TASKING, SCHEDULING AND CRITICAL SECTION 1Sujitha, M., 2V. Kannan and 3S. Ravi 1,3 Department of ECE, Dr. M.G.R. Educational and Research Institute University, Chennai, India 2Jeppiaar Institute of Technology, Kanchipuram, India Received 2014-04-21; Revised 2014-07-19; Accepted 2014-12-16 ABSTRACT RTOS based embedded systems are designed with priority based multiple tasks. Inter task communication and data corruptions are major constraints in multi-tasking RTOS system. This study we describe about the solution for these issues with an example Real-time Liquid level control system. Message queue and Mail box are used to perform inter task communication to improve the task execution time and performance of the system. Critical section scheduling is used to eliminate the data corruption. In this application process value monitoring is considered as critical. In critical section the interrupt disable time is the most important specification of a real time kernel. RTOS is used to keep the interrupt disable time to a minimum. The algorithm is studied with respect to task execution time and response of the interrupts. The study also presents the comparative analysis of the system with critical section and without critical section based on the performance metrics. Keywords: Critical Section, RTOS, Scheduling, Resource Sharing, Mailbox, Message Queue 1. -
![Math.RA] 25 Sep 2013 Previous Paper [3], Also Relying in Conceptually Separated Tools from Them, Such As Graphs and Digraphs](https://docslib.b-cdn.net/cover/3906/math-ra-25-sep-2013-previous-paper-3-also-relying-in-conceptually-separated-tools-from-them-such-as-graphs-and-digraphs-1213906.webp)
Math.RA] 25 Sep 2013 Previous Paper [3], Also Relying in Conceptually Separated Tools from Them, Such As Graphs and Digraphs
Certain particular families of graphicable algebras Juan Núñez, María Luisa Rodríguez-Arévalo and María Trinidad Villar Dpto. Geometría y Topología. Facultad de Matemáticas. Universidad de Sevilla. Apdo. 1160. 41080-Sevilla, Spain. [email protected] [email protected] [email protected] Abstract In this paper, we introduce some particular families of graphicable algebras obtained by following a relatively new line of research, ini- tiated previously by some of the authors. It consists of the use of certain objects of Discrete Mathematics, mainly graphs and digraphs, to facilitate the study of graphicable algebras, which are a subset of evolution algebras. 2010 Mathematics Subject Classification: 17D99; 05C20; 05C50. Keywords: Graphicable algebras; evolution algebras; graphs. Introduction The main goal of this paper is to advance in the research of a novel mathematical topic emerged not long ago, the evolution algebras in general, and the graphicable algebras (a subset of them) in particular, in order to obtain new results starting from those by Tian (see [4, 5]) and others already obtained by some of us in a arXiv:1309.6469v1 [math.RA] 25 Sep 2013 previous paper [3], also relying in conceptually separated tools from them, such as graphs and digraphs. Concretely, our goal is to find some particular types of graphicable algebras associated with well-known types of graphs. The motivation to deal with evolution algebras in general and graphicable al- gebras in particular is due to the fact that at present, the study of these algebras is very booming, due to the numerous connections between them and many other branches of Mathematics, such as Graph Theory, Group Theory, Markov pro- cesses, dynamic systems and the Theory of Knots, among others. -

Shared Memory Programming Models I
Shared Memory Programming Models I Stefan Lang Interdisciplinary Center for Scientific Computing (IWR) University of Heidelberg INF 368, Room 532 D-69120 Heidelberg phone: 06221/54-8264 email: [email protected] WS 14/15 Stefan Lang (IWR) Simulation on High-Performance Computers WS14/15 1/45 Shared Memory Programming Models I Communication by shared memory Critical section Mutual exclusion: Petersons algorithm OpenMP Barriers – Synchronisation of all processes Semaphores Stefan Lang (IWR) Simulation on High-Performance Computers WS14/15 2/45 Critical Section What is a critical section? We consider the following situation: Application consists of P concurrent processes, these are thus executed simultaneously instructions executed by one process are subdivided into interconnected groups ◮ critical sections ◮ uncritical sections Critical section: Sequence of instructions, that perform a read or write access on a shared variable. Instructions of a critical section that may not be performed simultaneously by two or more processes. → it is said only a single process may reside within the critical section. Stefan Lang (IWR) Simulation on High-Performance Computers WS14/15 3/45 Mutual Exclusion I 2 Types of synchronization can be distinguished Conditional synchronisation Mutual exclusion Mutual exclusion consists of an entry protocol and an exit protocol: Programm (Introduction of mutual exclusion) parallel critical-section { process Π[int p ∈{0,..., P − 1}] { while (1) { entry protocol; critical section; exit protocol; uncritical section; } } } Stefan Lang (IWR) Simulation on High-Performance Computers WS14/15 4/45 Mutual Exclusion II The following criteria have to be matched: 1 Mutual exclusion. At most one process executed the critical section at a time. -

The Mutual Exclusion Problem Part II: Statement and Solutions
56b The Mutual Exclusion Problem Part II: Statement and Solutions L. Lamport1 Digital Equipment Corporation 6 October 1980 Revised: 1 February 1983 1 May 1984 27 February 1985 June 26, 2000 To appear in Journal of the ACM 1Most of this work was performed while the author was at SRI International, where it was supported in part by the National Science Foundation under grant number MCS-7816783. Abstract The theory developed in Part I is used to state the mutual exclusion problem and several additional fairness and failure-tolerance requirements. Four “dis- tributed” N-process solutions are given, ranging from a solution requiring only one communication bit per process that permits individual starvation, to one requiring about N! communication bits per process that satisfies every reasonable fairness and failure-tolerance requirement that we can conceive of. Contents 1 Introduction 3 2TheProblem 4 2.1 Basic Requirements ........................ 4 2.2 Fairness Requirements ...................... 6 2.3 Premature Termination ..................... 8 2.4 Failure ............................... 10 3 The Solutions 14 3.1 The Mutual Exclusion Protocol ................. 15 3.2 The One-Bit Solution ...................... 17 3.3 A Digression ........................... 21 3.4 The Three-Bit Algorithm .................... 22 3.5 FCFS Solutions .......................... 26 4Conclusion 32 1 List of Figures 1 The One-Bit Algorithm: Process i ............... 17 2 The Three-Bit Algorithm: Process i .............. 24 3TheN-Bit FCFS Algorithm: Process i............. 28 4TheN!-Bit FCFS Algorithm: Process i. ............ 31 2 1 Introduction This is the second part of a two-part paper on the mutual exclusion problem. In Part I [9], we described a formal model of concurrent systems and used it to define a primitive interprocess communication mechanism (communica- tion variables) that assumes no underlying mutual exclusion. -

Interlace Polynomials of Friendship Graphs
Electronic Journal of Graph Theory and Applications 6 (2) (2018), 269–281 Interlace polynomials of friendship graphs Christina Eubanks-Turnera, Aihua Lib aDepartment of Mathematics, Loyola Marymount University, 90045 bDepartment of Mathematical Sciences, Montclair State University, 07043 [email protected], [email protected] Abstract In this paper, we study the interlace polynomials of friendship graphs, that is, graphs that satisfy the Friendship Theorem given by Erdos,¨ Renyi´ and Sos. Explicit formulas, special values, and behaviour of coefficients of these polynomials are provided. We also give the interlace polynomials of other similar graphs, such as, the butterfly graph. Keywords: graph polynomial, interlace polynomial, friendship graph, butterfly graph Mathematics Subject Classification : 05C31, 05C50 DOI: 10.5614/ejgta.2018.6.2.7 1. Introduction Sequencing by hybridization is a method of reconstructing a long DNA string from its nu- cleotide sequence. Since gaining a unique reconstruction from the substrings is not always possi- ble, a major question that arises in this study is “For a random string, how many reconstructions are possible?” In [2], Arratia, Bollobas,´ Coppersmith, and Sorkin answer an important question related to DNA sequencing by converting this to a question about Euler circuits in a 2-in, 2-out graph that have been “toggled” (interlaced). The previously mentioned authors introduced the in- terlace polynomial of a graph, a polynomial that represents the information gained from doing the toggling process on the graph, see [2]. Interlace polynomials are similar to other graph polynomi- als, such as, Tutte and Martin polynomials, see [5]. Some researchers have studied different types of graph polynomials, such as genus polynomials, [7]. -

Minor-Obstructions for Apex Sub-Unicyclic Graphs1
Minor-Obstructions for Apex Sub-unicyclic Graphs1 Alexandros Leivaditis2 Alexandros Singh3 Giannos Stamoulis3 Dimitrios M. Thilikos4,2,3,5 Konstantinos Tsatsanis3 Vasiliki Velona6,7,8 Abstract A graph is sub-unicyclic if it contains at most one cycle. We also say that a graph G is k-apex sub-unicyclic if it can become sub-unicyclic by removing k of its vertices. We identify 29 graphs that are the minor-obstructions of the class of 1-apex sub-unicyclic graphs, i.e., the set of all minor minimal graphs that do not belong in this class. For bigger values of k, we give an exact structural characterization of all the cactus graphs that are minor-obstructions of k-apex sub- unicyclic graphs and we enumerate them. This implies that, for every k, the class of k-apex sub-unicyclic graphs has at least 0.34 · k−2.5(6.278)k minor-obstructions. Keywords: Graph Minors, Obstruction set, Sub-unicyclc graphs. 1 Introduction A graph is called unicyclic [17] if it contains exactly one cycle and is called sub-unicyclic if it contains at most one cycle. Notice that sub-unicyclic graphs are exactly the subgraphs of unicyclic graphs. A graph H is a minor of a graph G if a graph isomorphic to H can be obtained by some subgraph of G after a series of contractions. We say that a graph class G is minor-closed if every minor of every graph in G also belongs in G. We also define obs(G), called the minor-obstruction set of G, as the set of minor-minimal graphs not in G. -

4-Prime Cordiality of Some Cycle Related Graphs
Available at Applications and Applied http://pvamu.edu/aam Mathematics: Appl. Appl. Math. An International Journal ISSN: 1932-9466 (AAM) Vol. 12, Issue 1 (June 2017), pp. 230 – 240 4-Prime cordiality of some cycle related graphs 1R. Ponraj, 2Rajpal Singh, & 1S. Sathish Narayanan 1Department of Mathematics Sri Paramakalyani College Alwarkurichi-627412, India [email protected]; [email protected] & 2Research Scholar Department of Mathematics Manonmaniam Sundaranar University Abishekapatti, Tirunelveli - 627012, Tamilnadu, India [email protected] Received: June 18, 201; Accepted: October 20, 2016 Abstract Recently three prime cordial labeling behavior of path, cycle, complete graph, wheel, comb, subdivison of a star, bistar, double comb, corona of tree with a vertex, crown, olive tree and other standard graphs were studied. Also four prime cordial labeling behavior of complete graph, book, flower were studied. In this paper, we investigate the four prime cordial labeling behavior of corona of wheel, gear, double cone, helm, closed helm, butterfly graph, and friendship graph. Keywords: Wheel; Gear; Double Cone; Helm; Butterfly Graph MSC 2010 No.: Primary 05C78, Secondary 05C38 1. Introduction Throughout this paper we have considered only simple and undirected graph. Terms and defini- tions not defined here are used in the sense of Harary (2001) and Gallian (2015). 230 AAM: Intern. J., Vol. 12, Issue 1 (June 2017) 231 Let G = (V;E) be a (p;q) graph. The cardinality of V is called the order of G and the cardinality of E is called the size of G. Rosa (1967) introduced graceful labelling of graphs which was the foundation of the graph labelling.