Design of Stream Ciphers and Cryptographic Properties of Nonlinear Functions
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Vector Boolean Functions: Applications in Symmetric Cryptography
Vector Boolean Functions: Applications in Symmetric Cryptography José Antonio Álvarez Cubero Departamento de Matemática Aplicada a las Tecnologías de la Información y las Comunicaciones Universidad Politécnica de Madrid This dissertation is submitted for the degree of Doctor Ingeniero de Telecomunicación Escuela Técnica Superior de Ingenieros de Telecomunicación November 2015 I would like to thank my wife, Isabel, for her love, kindness and support she has shown during the past years it has taken me to finalize this thesis. Furthermore I would also liketo thank my parents for their endless love and support. Last but not least, I would like to thank my loved ones such as my daughter and sisters who have supported me throughout entire process, both by keeping me harmonious and helping me putting pieces together. I will be grateful forever for your love. Declaration The following papers have been published or accepted for publication, and contain material based on the content of this thesis. 1. [7] Álvarez-Cubero, J. A. and Zufiria, P. J. (expected 2016). Algorithm xxx: VBF: A library of C++ classes for vector Boolean functions in cryptography. ACM Transactions on Mathematical Software. (In Press: http://toms.acm.org/Upcoming.html) 2. [6] Álvarez-Cubero, J. A. and Zufiria, P. J. (2012). Cryptographic Criteria on Vector Boolean Functions, chapter 3, pages 51–70. Cryptography and Security in Computing, Jaydip Sen (Ed.), http://www.intechopen.com/books/cryptography-and-security-in-computing/ cryptographic-criteria-on-vector-boolean-functions. (Published) 3. [5] Álvarez-Cubero, J. A. and Zufiria, P. J. (2010). A C++ class for analysing vector Boolean functions from a cryptographic perspective. -

Towards the Generation of a Dynamic Key-Dependent S-Box to Enhance Security
Towards the Generation of a Dynamic Key-Dependent S-Box to Enhance Security 1 Grasha Jacob, 2 Dr. A. Murugan, 3Irine Viola 1Research and Development Centre, Bharathiar University, Coimbatore – 641046, India, [email protected] [Assoc. Prof., Dept. of Computer Science, Rani Anna Govt College for Women, Tirunelveli] 2 Assoc. Prof., Dept. of Computer Science, Dr. Ambedkar Govt Arts College, Chennai, India 3Assoc. Prof., Dept. of Computer Science, Womens Christian College, Nagercoil, India E-mail: [email protected] ABSTRACT Secure transmission of message was the concern of early men. Several techniques have been developed ever since to assure that the message is understandable only by the sender and the receiver while it would be meaningless to others. In this century, cryptography has gained much significance. This paper proposes a scheme to generate a Dynamic Key-dependent S-Box for the SubBytes Transformation used in Cryptographic Techniques. Keywords: Hamming weight, Hamming Distance, confidentiality, Dynamic Key dependent S-Box 1. INTRODUCTION Today communication networks transfer enormous volume of data. Information related to healthcare, defense and business transactions are either confidential or private and warranting security has become more and more challenging as many communication channels are arbitrated by attackers. Cryptographic techniques allow the sender and receiver to communicate secretly by transforming a plain message into meaningless form and then retransforming that back to its original form. Confidentiality is the foremost objective of cryptography. Even though cryptographic systems warrant security to sensitive information, various methods evolve every now and then like mushroom to crack and crash the cryptographic systems. NSA-approved Data Encryption Standard published in 1977 gained quick worldwide adoption. -
Hardness Evaluation of Solving MQ Problems
MQ Challenge: Hardness Evaluation of Solving MQ Problems Takanori Yasuda (ISIT), Xavier Dahan (ISIT), Yun-Ju Huang (Kyushu Univ.), Tsuyoshi Takagi (Kyushu Univ.), Kouichi Sakurai (Kyushu Univ., ISIT) This work was supported by “Strategic Information and Communications R&D Promotion Programme (SCOPE), no. 0159-0091”, Ministry of Internal Affairs and Communications, Japan. The first author is supported by Grant-in-Aid for Young Scientists (B), Grant number 24740078. Fukuoka MQ challenge MQ challenge started on April 1st. https://www.mqchallenge.org/ ETSI Quantum Safe Workshop 2015/4/3 2 Why we need MQ challenge? • Several public key cryptosystems held contests which solve the associated basic mathematical problems. o RSA challenge(RSA Laboratories), ECC challenge(Certicom), Lattice challenge(TU Darmstadt) • Lattice challenge (http://www.latticechallenge.org/) o Target: Short vector problem o 2008 – now continued • Multivariate public-key cryptsystem (MPKC) also need to evaluate the current state-of-the-art in practical MQ problem solvers. We planed to hold MQ challenge. ETSI Quantum Safe Workshop 2015/4/3 3 Multivariate Public Key Cryptosystem (MPKC) • Advantage o Candidate for post-quantum cryptography o Used for both encryption and signature schemes • Encryption: Simple Matrix scheme (ABC scheme), ZHFE scheme • Signature: UOV, Rainbow o Efficient encryption and decryption and signature generation and verification. • Problems o Exact estimate of security of MPKC schemes o Huge length of secret and public keys in comparison with RSA o New application and function ETSI Quantum Safe Workshop 2015/4/3 4 MQ problem MPKC are public key cryptosystems whose security depends on the difficulty in solving a system of multivariate quadratic polynomials with coefficients in a finite field . -
Side Channel Analysis Attacks on Stream Ciphers
Side Channel Analysis Attacks on Stream Ciphers Daehyun Strobel 23.03.2009 Masterarbeit Ruhr-Universität Bochum Lehrstuhl Embedded Security Prof. Dr.-Ing. Christof Paar Betreuer: Dipl.-Ing. Markus Kasper Erklärung Ich versichere, dass ich die Arbeit ohne fremde Hilfe und ohne Benutzung anderer als der angegebenen Quellen angefertigt habe und dass die Arbeit in gleicher oder ähnlicher Form noch keiner anderen Prüfungsbehörde vorgelegen hat und von dieser als Teil einer Prüfungsleistung angenommen wurde. Alle Ausführungen, die wörtlich oder sinngemäß übernommen wurden, sind als solche gekennzeichnet. Bochum, 23.März 2009 Daehyun Strobel ii Abstract In this thesis, we present results from practical differential power analysis attacks on the stream ciphers Grain and Trivium. While most published works on practical side channel analysis describe attacks on block ciphers, this work is among the first ones giving report on practical results of power analysis attacks on stream ciphers. Power analyses of stream ciphers require different methods than the ones used in todays most popular attacks. While for the majority of block ciphers it is sufficient to attack the first or last round only, to analyze a stream cipher typically the information leakages of many rounds have to be considered. Furthermore the analysis of hardware implementations of stream ciphers based on feedback shift registers inevitably leads to methods combining algebraic attacks with methods from the field of side channel analysis. Instead of a direct recovery of key bits, only terms composed of several key bits and bits from the initialization vector can be recovered. An attacker first has to identify a sufficient set of accessible terms to finally solve for the key bits. -

Petawatt and Exawatt Class Lasers Worldwide
Petawatt and exawatt class lasers worldwide Colin Danson, Constantin Haefner, Jake Bromage, Thomas Butcher, Jean-Christophe Chanteloup, Enam Chowdhury, Almantas Galvanauskas, Leonida Gizzi, Joachim Hein, David Hillier, et al. To cite this version: Colin Danson, Constantin Haefner, Jake Bromage, Thomas Butcher, Jean-Christophe Chanteloup, et al.. Petawatt and exawatt class lasers worldwide. High Power Laser Science and Engineering, Cambridge University Press, 2019, 7, 10.1017/hpl.2019.36. hal-03037682 HAL Id: hal-03037682 https://hal.archives-ouvertes.fr/hal-03037682 Submitted on 3 Dec 2020 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. High Power Laser Science and Engineering, (2019), Vol. 7, e54, 54 pages. © The Author(s) 2019. This is an Open Access article, distributed under the terms of the Creative Commons Attribution licence (http://creativecommons.org/ licenses/by/4.0/), which permits unrestricted re-use, distribution, and reproduction in any medium, provided the original work is properly cited. doi:10.1017/hpl.2019.36 Petawatt and exawatt class lasers worldwide Colin N. Danson1;2;3, Constantin Haefner4;5;6, Jake Bromage7, Thomas Butcher8, Jean-Christophe F. Chanteloup9, Enam A. Chowdhury10, Almantas Galvanauskas11, Leonida A. -

Cryptographic Sponge Functions
Cryptographic sponge functions Guido B1 Joan D1 Michaël P2 Gilles V A1 http://sponge.noekeon.org/ Version 0.1 1STMicroelectronics January 14, 2011 2NXP Semiconductors Cryptographic sponge functions 2 / 93 Contents 1 Introduction 7 1.1 Roots .......................................... 7 1.2 The sponge construction ............................... 8 1.3 Sponge as a reference of security claims ...................... 8 1.4 Sponge as a design tool ................................ 9 1.5 Sponge as a versatile cryptographic primitive ................... 9 1.6 Structure of this document .............................. 10 2 Definitions 11 2.1 Conventions and notation .............................. 11 2.1.1 Bitstrings .................................... 11 2.1.2 Padding rules ................................. 11 2.1.3 Random oracles, transformations and permutations ........... 12 2.2 The sponge construction ............................... 12 2.3 The duplex construction ............................... 13 2.4 Auxiliary functions .................................. 15 2.4.1 The absorbing function and path ...................... 15 2.4.2 The squeezing function ........................... 16 2.5 Primary aacks on a sponge function ........................ 16 3 Sponge applications 19 3.1 Basic techniques .................................... 19 3.1.1 Domain separation .............................. 19 3.1.2 Keying ..................................... 20 3.1.3 State precomputation ............................ 20 3.2 Modes of use of sponge functions ......................... -

Hardware Implementation of Four Byte Per Clock RC4 Algorithm Rourab Paul, Amlan Chakrabarti, Senior Member, IEEE, and Ranjan Ghosh
JOURNAL OF LATEX CLASS FILES, VOL. 6, NO. 1, JANUARY 2007 1 Hardware Implementation of four byte per clock RC4 algorithm Rourab Paul, Amlan Chakrabarti, Senior Member, IEEE, and Ranjan Ghosh, Abstract—In the field of cryptography till date the 2-byte in 1-clock is the best known RC4 hardware design [1], while 1-byte in 1-clock [2], and the 1-byte in 3 clocks [3][4] are the best known implementation. The design algorithm in[2] considers two consecutive bytes together and processes them in 2 clocks. The design [1] is a pipelining architecture of [2]. The design of 1-byte in 3-clocks is too much modular and clock hungry. In this paper considering the RC4 algorithm, as it is, a simpler RC4 hardware design providing higher throughput is proposed in which 6 different architecture has been proposed. In design 1, 1-byte is processed in 1-clock, design 2 is a dynamic KSA-PRGA architecture of Design 1. Design 3 can process 2 byte in a single clock, where as Design 4 is Dynamic KSA-PRGA architecture of Design 3. Design 5 and Design 6 are parallelization architecture design 2 and design 4 which can compute 4 byte in a single clock. The maturity in terms of throughput, power consumption and resource usage, has been achieved from design 1 to design 6. The RC4 encryption and decryption designs are respectively embedded on two FPGA boards as co-processor hardware, the communication between the two boards performed using Ethernet. Keywords—Computer Society, IEEEtran, journal, LATEX, paper, template. -
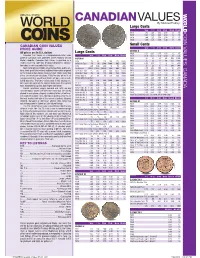
*UPDATED Canadian Values 07-04 201 7/26/2016 4:42:21 PM *UPDATED Canadian Values 07-04 202 COIN VALUES: CANADA 02 .0 .0 12
CANADIAN VALUES By Michael Findlay Large Cents VG-8 F-12 VF-20 EF-40 MS-60 MS-63R 1917 1.00 1.25 1.50 2.50 13. 45. CANADA COIN VALUES: 1918 1.00 1.25 1.50 2.50 13. 45. 1919 1.00 1.25 1.50 2.50 13. 45. 1920 1.00 1.25 1.50 3.00 18. 70. CANADIAN COIN VALUES Small Cents PRICE GUIDE VG-8 F-12 VF-20 EF-40 MS-60 MS-63R GEORGE V All prices are in U.S. dollars LargeL Cents C t 1920 0.20 0.35 0.75 1.50 12. 45. Canadian Coin Values is a comprehensive retail value VG-8 F-12 VF-20 EF-40 MS-60 MS-63R 1921 0.50 0.75 1.50 4.00 30. 250. guide of Canadian coins published online regularly at Coin VICTORIA 1922 20. 23. 28. 40. 200. 1200. World’s website. Canadian Coin Values is provided as a 1858 70. 90. 120. 200. 475. 1800. 1923 30. 33. 42. 55. 250. 2000. reader service to collectors desiring independent informa- 1858 Coin Turn NI NI 2500. 5000. BNE BNE 1924 6.00 8.00 11. 16. 120. 800. tion about a coin’s potential retail value. 1859 4.00 5.00 6.00 10. 50. 200. 1925 25. 28. 35. 45. 200. 900. Sources for pricing include actual transactions, public auc- 1859 Brass 16000. 22000. 30000. BNE BNE BNE 1926 3.50 4.50 7.00 12. 90. 650. tions, fi xed-price lists and any additional information acquired 1859 Dbl P 9 #1 225. -

Security Evaluation of the K2 Stream Cipher
Security Evaluation of the K2 Stream Cipher Editors: Andrey Bogdanov, Bart Preneel, and Vincent Rijmen Contributors: Andrey Bodganov, Nicky Mouha, Gautham Sekar, Elmar Tischhauser, Deniz Toz, Kerem Varıcı, Vesselin Velichkov, and Meiqin Wang Katholieke Universiteit Leuven Department of Electrical Engineering ESAT/SCD-COSIC Interdisciplinary Institute for BroadBand Technology (IBBT) Kasteelpark Arenberg 10, bus 2446 B-3001 Leuven-Heverlee, Belgium Version 1.1 | 7 March 2011 i Security Evaluation of K2 7 March 2011 Contents 1 Executive Summary 1 2 Linear Attacks 3 2.1 Overview . 3 2.2 Linear Relations for FSR-A and FSR-B . 3 2.3 Linear Approximation of the NLF . 5 2.4 Complexity Estimation . 5 3 Algebraic Attacks 6 4 Correlation Attacks 10 4.1 Introduction . 10 4.2 Combination Generators and Linear Complexity . 10 4.3 Description of the Correlation Attack . 11 4.4 Application of the Correlation Attack to KCipher-2 . 13 4.5 Fast Correlation Attacks . 14 5 Differential Attacks 14 5.1 Properties of Components . 14 5.1.1 Substitution . 15 5.1.2 Linear Permutation . 15 5.2 Key Ideas of the Attacks . 18 5.3 Related-Key Attacks . 19 5.4 Related-IV Attacks . 20 5.5 Related Key/IV Attacks . 21 5.6 Conclusion and Remarks . 21 6 Guess-and-Determine Attacks 25 6.1 Word-Oriented Guess-and-Determine . 25 6.2 Byte-Oriented Guess-and-Determine . 27 7 Period Considerations 28 8 Statistical Properties 29 9 Distinguishing Attacks 31 9.1 Preliminaries . 31 9.2 Mod n Cryptanalysis of Weakened KCipher-2 . 32 9.2.1 Other Reduced Versions of KCipher-2 . -

Cryptanalysis of Sfinks*
Cryptanalysis of Sfinks? Nicolas T. Courtois Axalto Smart Cards Crypto Research, 36-38 rue de la Princesse, BP 45, F-78430 Louveciennes Cedex, France, [email protected] Abstract. Sfinks is an LFSR-based stream cipher submitted to ECRYPT call for stream ciphers by Braeken, Lano, Preneel et al. The designers of Sfinks do not to include any protection against algebraic attacks. They rely on the so called “Algebraic Immunity”, that relates to the complexity of a simple algebraic attack, and ignores other algebraic attacks. As a result, Sfinks is insecure. Key Words: algebraic cryptanalysis, stream ciphers, nonlinear filters, Boolean functions, solving systems of multivariate equations, fast algebraic attacks on stream ciphers. 1 Introduction Sfinks is a new stream cipher that has been submitted in April 2005 to ECRYPT call for stream cipher proposals, by Braeken, Lano, Mentens, Preneel and Varbauwhede [6]. It is a hardware-oriented stream cipher with associated authentication method (Profile 2A in ECRYPT project). Sfinks is a very simple and elegant stream cipher, built following a very classical formula: a single maximum-period LFSR filtered by a Boolean function. Several large families of ciphers of this type (and even much more complex ones) have been in the recent years, quite badly broken by algebraic attacks, see for exemple [12, 13, 1, 14, 15, 2, 18]. Neverthe- less the specialists of these ciphers counter-attacked by defining and applying the concept of Algebraic Immunity [7] to claim that some designs are “secure”. Unfortunately, as we will see later, the notion of Algebraic Immunity protects against only one simple alge- braic attack and ignores other algebraic attacks. -

Fast Correlation Attacks: Methods and Countermeasures
Fast Correlation Attacks: Methods and Countermeasures Willi Meier FHNW, Switzerland Abstract. Fast correlation attacks have considerably evolved since their first appearance. They have lead to new design criteria of stream ciphers, and have found applications in other areas of communications and cryp- tography. In this paper, a review of the development of fast correlation attacks and their implications on the design of stream ciphers over the past two decades is given. Keywords: stream cipher, cryptanalysis, correlation attack. 1 Introduction In recent years, much effort has been put into a better understanding of the design and security of stream ciphers. Stream ciphers have been designed to be efficient either in constrained hardware or to have high efficiency in software. A synchronous stream cipher generates a pseudorandom sequence, the keystream, by a finite state machine whose initial state is determined as a function of the secret key and a public variable, the initialization vector. In an additive stream cipher, the ciphertext is obtained by bitwise addition of the keystream to the plaintext. We focus here on stream ciphers that are designed using simple devices like linear feedback shift registers (LFSRs). Such designs have been the main tar- get of correlation attacks. LFSRs are easy to implement and run efficiently in hardware. However such devices produce predictable output, and cannot be used directly for cryptographic applications. A common method aiming at destroy- ing the predictability of the output of such devices is to use their output as input of suitably designed non-linear functions that produce the keystream. As the attacks to be described later show, care has to be taken in the choice of these functions. -

The WG Stream Cipher
The WG Stream Cipher Yassir Nawaz and Guang Gong Department of Electrical and Computer Engineering University of Waterloo Waterloo, ON, N2L 3G1, CANADA [email protected], [email protected] Abstract. In this paper we propose a new synchronous stream cipher, called WG ci- pher. The cipher is based on WG (Welch-Gong) transformations. The WG cipher has been designed to produce keystream with guaranteed randomness properties, i.e., bal- ance, long period, large and exact linear complexity, 3-level additive autocorrelation, and ideal 2-level multiplicative autocorrelation. It is resistant to Time/Memory/Data tradeoff attacks, algebraic attacks and correlation attacks. The cipher can be imple- mented with a small amount of hardware. 1 Introduction A synchronous stream cipher consists of a keystream generator which produces a sequence of binary digits. This sequence is called the running key or simply the keystream. The keystream is added (XORed) to the plaintext digits to produce the ciphertext. A secret key K is used to initialize the keystream generator and each secret key corresponds to a generator output sequence. Since the secret key is shared between the sender and the receiver, an identical keystream can be generated at the receiving end. The addition of this keystream with the ciphertext recovers the original plaintext. Stream ciphers can be divided into two major categories: bit-oriented stream ci- phers and word-oriented stream ciphers. The bit-oriented stream ciphers are usually based on binary linear feedback shift registors (LFSRs) (regularly clocked or irregu- larly clocked) together with filter or combiner functions. They can be implemented in hardware very efficiently.