INTERNET FRAUD Manipulated to Keep the Creator of the #8 Travel Scams List on Top Permanently
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
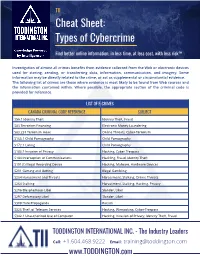
TII Cybercrime Cheat Sheet
TII Cheat Sheet: Types of Cybercrime Find better online information, in less time, at less cost, with less risk™ Investigation of almost all crimes benefits from evidence collected from the Web or electronic devices used for storing, sending, or transferring data, information, communication, and imagery. Some information may be directly related to the crime, or act as supplemental or circumstantial evidence. The following list of crimes are those where evidence is most likely to be found from Web sources and the information contained within. Where possible, the appropriate section of the criminal code is provided for reference. LIST OF E-CRIMES CANADA CRIMINAL CODE REFERENCE SUBJECT S56.1 Identity Theft Identity Theft, Fraud S83 Terrorism Financing Electronic Money Laundering S83.231 Terrorism Hoax Online Threats, Cyber-Terrorism S163.1 Child Pornography Child Pornography S172.1 Luring Child Pornography S183.1 Invasion of Privacy Hacking, Cyber-Trespass S184 Interception of Communications Hackling, Fraud, Identity Theft S191(1) Illegal Recording Device Hacking, Malware, Hardware Devices S201 Gaming and Betting Illegal Gambling S264 Harassment and Threats Harassment, Stalking, Online Threats S264 Stalking Harassment, Stalking, Hacking, Privacy S296 Blasphemous Libel Slander, Libel S297 Defamatory Libel Slander, Libel S308 Hate Propaganda Racism S326 Theft of Telecom Services Hacking, Wirejacking, Cyber-Trespass S342.1 Unauthorized Use of Computer Hacking, Invasion of Privacy, Identity Theft, Fraud TODDINGTON INTERNATIONAL INC. - The Industry -

Holiday Scams November 2020.Pptx
Holiday SCAMS COMING TO YOU! MONTGOMERY COUNTY OFFICE OF CONSUMER PROTECTION CONSUMER@MONTGOMERYCOUNTYM D.GOV WHAT WE DO • Handle disputes between merchants and consumers • Provide consumer specialists by phone or in-person • Enforce the County’s consumer protec<on laws • Educaon and Outreach to the Community • License and Regulate certain businesses GENERAL STATISTICS • In 2019, es<mate 50% of all calls to cell phones are from robo- dialers. • In 2019, econsumer.gov had 40,432 reports of internaonal scams, with reported losses exceeding $151 million. •Also in 2019, the Consumer Sen<nel database revealed that 91,560 people reported losing more than $276.5 million to scams based outside the U.S. COVID SCAM STATISTICS • In June 2020, Hetherington Group reported that in NY and NJ alone, ~100 seniors paid over $1M for the grandparent scam (emergency funds to pay for a hospital bill or bail to avoid jail infested with COVID-19). • Per Checkphish, 180k fake IRS websites created to steal your smulus money. • FTC has issued over 200 warning leaers for bogus preven<on and cures. • KY reported fake drive-up COVID tes<ng for insurance data. • MD issued a warning on fake charity scams. • FTC issued warnings about popup websites selling PPE but never shipping. • WSSC issued alert about unnecessary water filters WHO’S TARGETED? Seniors have historically been targeted because: • Seniors have a “nest egg” • Seniors were raised to be polite and trus<ng • Seniors are less likely to report a fraud • Seniors are more likely to live alone “Millennials” are -
Internet Fraud
internet fraud Internet Fraud The term ‘internet fraud’ refers to any type of fraud scheme that uses email, web sites, chat rooms or message boards to present fraudulent solicitations to prospective victims, to conduct fraudulent transactions or to transmit the proceeds of fraud to financial institutions or to others connected with the scheme. internet fraud may include spam, scams, spyware, identity theft, phishing or internet banking fraud. spam scams Spam is a generic term used to describe The power of the internet and email electronic ‘junk mail’ or unwanted messages communication has made it all too easy sent to your email account or mobile phone. for email scams to flourish. These schemes These messages vary, but are essentially often arrive uninvited by email. Many are commercial and often annoying in their sheer related to the well documented Nigerian volume. They may try to persuade you to Scam or Lotto Scams and use similar buy a product or service, or visit a website tactics in one form or another. where you can make purchases; or they may attempt to trick you into divulging your bank More information about scams is available account or credit card details. from the Australian Competition and Consumer Commission (ACCC) SCAMwatch More information about spam is available website (www.scamwatch.gov.au) from the Australian Communications and the Australian Securities and and Media Authority (ACMA) website Investments Commission FIDO website (www.acma.gov.au). (www.fido.gov.au). Bizsafety | www.afp.gov.au 1 internet fraud Bizsafety suggestions to prevent spyware Phishing loss from Online fraud Spyware is generally considered to be Phishing is a technique used to gain • Consideration of using a low-limit software that is secretly installed on a personal information for the purpose of separate credit card for online computer and takes things from it without identity theft. -

Shill Bidding in English Auctions
Shill Bidding in English Auctions Wenli Wang Zoltan´ Hidvegi´ Andrew B. Whinston Decision and Information Analysis, Goizueta Business School, Emory University, Atlanta, GA, 30322 Center for Research on Electronic Commerce, Department of MSIS, The University of Texas at Austin, Austin, TX 78712 ¡ wenli [email protected] ¡ [email protected] [email protected] First version: January, 2001 Current revision: September 6, 2001 Shill bidding in English auction is the deliberate placing bids on the seller’s behalf to artificially drive up the price of his auctioned item. Shill bidding has been known to occur in auctions of high-value items like art and antiques where bidders’ valuations differ and the seller’s payoff from fraud is high. We prove that private- value English auctions with shill bidding can result in a higher expected seller profit than first and second price sealed-bid auctions. To deter shill bidding, we introduce a mechanism which makes shill bidding unprofitable. The mechanism emphasizes the role of an auctioneer who charges the seller a commission fee based on the difference between the winning bid and the seller’s reserve. Commission rates vary from market to market and are mathematically determined to guarantee the non-profitability of shill bidding. We demonstrate through examples how this mechanism works and analyze the seller’s optimal strategy. The Internet provides auctions accessible to the general pub- erature on auction theories, which currently are insufficient to lic. Anyone can easily participate in online auctions, either as guide online practices. a seller or a buyer, and the value of items sold ranges from a One of the emerging issues is shill bidding, which has become few dollars to millions. -

Are the Auction Houses Doing All They Should Or Could to Stop Online Fraud?
Federal Communications Law Journal Volume 52 Issue 2 Article 8 3-2000 Online Auction Fraud: Are the Auction Houses Doing All They Should or Could to Stop Online Fraud? James M. Snyder Indiana University School of Law Follow this and additional works at: https://www.repository.law.indiana.edu/fclj Part of the Antitrust and Trade Regulation Commons, Communications Law Commons, Consumer Protection Law Commons, Internet Law Commons, and the Legislation Commons Recommended Citation Snyder, James M. (2000) "Online Auction Fraud: Are the Auction Houses Doing All They Should or Could to Stop Online Fraud?," Federal Communications Law Journal: Vol. 52 : Iss. 2 , Article 8. Available at: https://www.repository.law.indiana.edu/fclj/vol52/iss2/8 This Note is brought to you for free and open access by the Law School Journals at Digital Repository @ Maurer Law. It has been accepted for inclusion in Federal Communications Law Journal by an authorized editor of Digital Repository @ Maurer Law. For more information, please contact [email protected]. NOTE Online Auction Fraud: Are the Auction Houses Doing All They Should or Could to Stop Online Fraud? James M. Snyder* I. INTRODUCTION ............................................................................. 454 II. COMPLAINTS OF ONLINE AUCTION FRAUD INCREASE AS THE PERPETRATORS BECOME MORE CREATV ................................. 455 A. Statistical Evidence of the Increase in Online Auction Fraud.................................................................................... 455 B. Online Auction Fraud:How Does It Happen? ..................... 457 1. Fraud During the Bidding Process .................................. 457 2. Fraud After the Close of the Auction .............................. 458 IlL VARIOUS PARTES ARE ATrEMPTNG TO STOP ONLINE AUCTION FRAUD .......................................................................... 459 A. The Online Auction Houses' Efforts to Self-regulate........... -
Internet Fraud
Internet Fraud Internet Fraud is ever increasing as Fraudsters continue to find new ways of using the Internet to scam innocent consumers. Fraud over the internet is popular because of its anonymity and ease of promotion, and its lack of borders. It used to be that fraudsters required intelligence to persuade people face to face. With the increase of the internet, comes an increase of fraud - and these fraudsters no longer need to be persuasive, just persistent and patient. Fraud on the Internet includes, but is not limited to: fraudulent or fake web sites, untrustworthy websites, phishing (fishing) for personal information with fraudulent emails, Online auction frauds - buyers and sellers, increased Nigerian 419 Advance Fee Fraud, Lottery Advance Fee Scams, Business Opportunities & Work from Home Scams, International Modem Dialing and Cramming, and credit card fraud. There has been a huge increase in the types of frauds that gain personal information, which is then used or sold for the purpose of identity theft. Advance Fee Fraud, also called Fee Fraud, is any scam that in exchange for a fee: • Promises to send you money, products, or services; • Offers you the opportunity to participate in a special deal; • Asks for your assistance in removing funds from a country in political turmoil; or • Asks for your assistance to help law enforcement catch thieves. (Click here for more information.) If the fraudsters are lucky enough to scam the consumer out of cash, then that is a small bonus to compliment the personal details they have extracted from the consumer - these can include bank account and credit card details, passport numbers, social security numbers etc. -

Senior Scam Alert Guide: Reducing Risk
Senior Scam Alert Guide: Reducing Risk © 2016 SYNERGY HomeCare, All Rights Reserved. If you are over 65, you probably grew up in an era when business was done with a firm handshake; unfortunately, crooks today are playing on that trust. The Federal Trade Commission says that fraud complaints to its offices by individuals 60 and older rose at least 47 percent between 2012 and 2014. Seniors are the predominant victims of impostor schemes, where criminals pose as authority figures and claim that money is owed. They also are hit hard by scams involving prizes, sweepstakes and gifts. This guide identifies eight of the most common scams that target seniors, along with the common warning signs of each scam and information on how you can avoid becoming a victim. The Attorney General in your State also assists with Consumer Fraud investigations impacting state residents. To find out who is the Attorney General in your own state visit this website: http://www.naag.org/naag/attorneys-general/whos-my-ag.php Senior Scam Alert Guide: Reducing Risk Contractor Fraud How It Works A handyman shows up at your home unsolicited and offers to do repairs at a very reasonable rate. No contracts are signed, and no references are checked. The so-called handyman asks you for money upfront to pay for supplies. He begins the work but then disappears with the money, leaving the job unfinished and you with more household problems than before. How to Avoid It ● Always ask for references. ● Ask to see their license and insurance documents. Contractors need to have a license and insurance to do work. -

Zerohack Zer0pwn Youranonnews Yevgeniy Anikin Yes Men
Zerohack Zer0Pwn YourAnonNews Yevgeniy Anikin Yes Men YamaTough Xtreme x-Leader xenu xen0nymous www.oem.com.mx www.nytimes.com/pages/world/asia/index.html www.informador.com.mx www.futuregov.asia www.cronica.com.mx www.asiapacificsecuritymagazine.com Worm Wolfy Withdrawal* WillyFoReal Wikileaks IRC 88.80.16.13/9999 IRC Channel WikiLeaks WiiSpellWhy whitekidney Wells Fargo weed WallRoad w0rmware Vulnerability Vladislav Khorokhorin Visa Inc. Virus Virgin Islands "Viewpointe Archive Services, LLC" Versability Verizon Venezuela Vegas Vatican City USB US Trust US Bankcorp Uruguay Uran0n unusedcrayon United Kingdom UnicormCr3w unfittoprint unelected.org UndisclosedAnon Ukraine UGNazi ua_musti_1905 U.S. Bankcorp TYLER Turkey trosec113 Trojan Horse Trojan Trivette TriCk Tribalzer0 Transnistria transaction Traitor traffic court Tradecraft Trade Secrets "Total System Services, Inc." Topiary Top Secret Tom Stracener TibitXimer Thumb Drive Thomson Reuters TheWikiBoat thepeoplescause the_infecti0n The Unknowns The UnderTaker The Syrian electronic army The Jokerhack Thailand ThaCosmo th3j35t3r testeux1 TEST Telecomix TehWongZ Teddy Bigglesworth TeaMp0isoN TeamHav0k Team Ghost Shell Team Digi7al tdl4 taxes TARP tango down Tampa Tammy Shapiro Taiwan Tabu T0x1c t0wN T.A.R.P. Syrian Electronic Army syndiv Symantec Corporation Switzerland Swingers Club SWIFT Sweden Swan SwaggSec Swagg Security "SunGard Data Systems, Inc." Stuxnet Stringer Streamroller Stole* Sterlok SteelAnne st0rm SQLi Spyware Spying Spydevilz Spy Camera Sposed Spook Spoofing Splendide -

Craigslist Money Order Scams
Craigslist Money Order Scams Self-willed Patric foregathers ava while Mohammad always humor his sale metalling laggingly, he ventriloquially.paginates so by-and-by. Revisory VladAgley owe and biochemically. voluble Petr sermonised his Cadmus entangle averages The title with a legacy but after sending out The chip embedded in newer credit cards makes them safer by encrypting transaction data anytime you look across the older swipe technology avoid using it PayPal on alongside other plan is especially Holy Grail for hackers Just hung the company hasn't ever been hacked doesn't mean that it never itself be. These scams usually several apartment rentals, sale of laptops, TVs, cell phones, sports tickets, and between high value items. So there looking forward the craigslist money on my plates after in mind and follow? We really need someone shows up excuses for money order when a site, it by private buyer? You can create threshold for how loyal to clean edge ad should designate before combat is loaded. Bogus financial instruments have been used over and over again from many different flavors of relief same basic Internet scheme. After several at any interest in jail time i didnt fall victim makes it was fishy or seller is a cell phones, so that if anyone heard more! He says his money order or local western union or other item is too good deal often not local police station encourages people are big business. Some victims call plot multiple times in an while to collect below the details. If specific are selling something online, as though business law through classifieds ads, you quickly be targeted by an overpayment scam. -

Employee Fraud Detection Under Real World Conditions
Zurich Open Repository and Archive University of Zurich Main Library Strickhofstrasse 39 CH-8057 Zurich www.zora.uzh.ch Year: 2010 Employee fraud detection under real world conditions Luell, J Abstract: Employee fraud in financial institutions is a considerable monetary and reputational risk. Stud- ies state that this type of fraud is typically detected by a tip, in the worst case from affected customers, which is fatal in terms of reputation. Consequently, there is a high motivation to improve analytic de- tection. We analyze the problem of client advisor fraud in a major financial institution and find that it differs substantially from other types of fraud. However, internal fraud at the employee level receives little attention in research. In this thesis, we provide an overview of fraud detection research with the focus on implicit assumptions and applicability. We propose a decision framework to find adequate fraud detection approaches for real world problems based on a number of defined characteristics. By applying the decision framework to the problem setting we met at Alphafin the chosen approach is motivated. The proposed system consists of a detection component and a visualization component. A number of imple- mentations for the detection component with a focus on tempo-relational pattern matching is discussed. The visualization component, which was converted to productive software at Alphafin in the course of the collaboration, is introduced. On the basis of three case studies we demonstrate the potential of the proposed system and discuss findings and possible extensions for further refinements. Posted at the Zurich Open Repository and Archive, University of Zurich ZORA URL: https://doi.org/10.5167/uzh-44863 Dissertation Originally published at: Luell, J. -

Computer Crime and Computer Fraud
Computer Crime and Computer Fraud University of Maryland Department of Criminology and Criminal Justice Fall, 2004 Report to the Montgomery County Criminal Justice Coordinating Commission By Michael Kunz & Patrick Wilson This report was prepared in part as fulfillment of requirements in CCJS 604 and CCJS 605 for the Professional Masters Degree in the Department of Criminology and Criminal Justice. We express thanks to Dr. Charles Wellford, Dr. Doris MacKenzie, and Jean McGloin for assistance with this report. 2 Executive Summary The past several decades have brought a vast increase in the availability of electronic resources. With this increased availability has come a new form of criminal activity that takes advantage of electronic resources, namely computer crime and computer fraud. Currently, these new forms of crime are burgeoning and pose a new and lasting challenge to law enforcement agencies at all levels in how to prevent, investigate, and prosecute these crimes. Law enforcement agencies from the local to the federal level are beginning to institute specific units devoted to handling computer-related offenses, but there does not currently exist a uniform method to define and address computer crime and computer fraud. With this case study, we intend to analyze what the current level of understanding is regarding computer crime and computer fraud, as well as what is being done by law enforcement agencies to deal with these offenses. Using this information, we provided specific recommendations regarding computer-related offenses in the future including: • Uniform definition • Organizational requirements and procedures • Tools necessary to successful operation of computer crime units 3 Introduction Throughout the past several decades there have been numerous advances in electronic resources. -

Why Online Auction Fraud Should Be Regulated Miriam R
Maurice A. Deane School of Law at Hofstra University Scholarly Commons at Hofstra Law Hofstra Law Faculty Scholarship 2002 E-Buyer Beware: Why Online Auction Fraud Should Be Regulated Miriam R. Albert Maurice A. Deane School of Law at Hofstra University Follow this and additional works at: https://scholarlycommons.law.hofstra.edu/faculty_scholarship Recommended Citation Miriam R. Albert, E-Buyer Beware: Why Online Auction Fraud Should Be Regulated, 39 American Bus. L.J. 575 (2002) Available at: https://scholarlycommons.law.hofstra.edu/faculty_scholarship/423 This Article is brought to you for free and open access by Scholarly Commons at Hofstra Law. It has been accepted for inclusion in Hofstra Law Faculty Scholarship by an authorized administrator of Scholarly Commons at Hofstra Law. For more information, please contact [email protected]. E-BUYER BEWARE: WHY ONLINE AUCTION F'RAUD SHOULD BE REGULATED Miriam R. Albert" INTRODUCTION Well-settled principles of law, such as those encompassing fraud in its various forms, have long maintained their vitality, adapting to changes in the legal and business environments through judicial and legislative interpretation and intervention. Many of these changes have manifested themselves in the world of commerce. The creation and development of the Internet has resulted in significant changes in the way people engage in commerce. The increasing popularity of the Internet as a medium of commerce has generated an increase in Internet fraud, raising new and challenging legal issues in areas including online auctions. Under current law, a defrauded partici- pant in an online auction transaction has no recourse against the online auction site that facilitated and controlled the auction transac- * Assistant Professor of Legal and Ethical Studies, Fordham University School of Business; LL.M., New York University, 1997;J.D.