Boot the System
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The GNOME Census: Who Writes GNOME?
The GNOME Census: Who writes GNOME? Dave Neary & Vanessa David, Neary Consulting © Neary Consulting 2010: Some rights reserved Table of Contents Introduction.........................................................................................3 What is GNOME?.............................................................................3 Project governance...........................................................................3 Why survey GNOME?.......................................................................4 Scope and methodology...................................................................5 Tools and Observations on Data Quality..........................................7 Results and analysis...........................................................................10 GNOME Project size.......................................................................10 The Long Tail..................................................................................11 Effects of commercialisation..........................................................14 Who does the work?.......................................................................15 Who maintains GNOME?................................................................17 Conclusions........................................................................................22 References.........................................................................................24 Appendix 1: Modules included in survey...........................................25 2 Introduction What -

1. D-Bus a D-Bus FAQ Szerint D-Bus Egy Interprocessz-Kommunikációs Protokoll, És Annak Referenciamegvalósítása
Az Udev / D-Bus rendszer - a modern asztali Linuxok alapja A D-Bus rendszer minden modern Linux disztribúcióban jelen van, sőt mára már a Linux, és más UNIX jellegű, sőt nem UNIX rendszerek (különösen a desktopon futó változatok) egyik legalapvetőbb technológiája, és az ismerete a rendszergazdák számára lehetővé tesz néhány rendkívül hasznos trükköt, az alkalmazásfejlesztőknek pedig egyszerűen KÖTELEZŐ ismerniük. Miért ilyen fontos a D-Bus? Mit csinál? D-Bus alapú technológiát teszik lehetővé többek között azt, hogy közönséges felhasználóként a kedvenc asztali környezetünkbe bejelentkezve olyan feladatokat hajtsunk végre, amiket a kernel csak a root felasználónak engedne meg. Felmountolunk egy USB meghajtót? NetworkManagerrel konfiguráljuk a WiFi-t, a 3G internetet vagy bármilyen más hálózati csatolót, és kapcsolódunk egy hálózathoz? Figyelmeztetést kapunk a rendszertől, hogy új szoftverfrissítések érkeztek, majd telepítjük ezeket? Hibernáljuk, felfüggesztjük a gépet? A legtöbb esetben ma már D-Bus alapú technológiát használunk ilyen esetben. A D-Bus lehetővé teszi, hogy egymástól függetlenül, jellemzően más UID alatt indított szoftverösszetevők szabványos és biztonságos módon igénybe vegyék egymás szolgáltatásait. Ha valaha lesz a Linuxhoz professzionális desktop tűzfal vagy vírusirtó megoldás, a dolgok jelenlegi állasa szerint annak is D- Bus technológiát kell használnia. A D-Bus technológia legfontosabb ihletője a KDE DCOP rendszere volt, és mára a D-Bus leváltotta a DCOP-ot, csakúgy, mint a Gnome Bonobo technológiáját. 1. D-Bus A D-Bus FAQ szerint D-Bus egy interprocessz-kommunikációs protokoll, és annak referenciamegvalósítása. Ezen referenciamegvalósítás egyik összetevője, a libdbus könyvtár a D- Bus szabványnak megfelelő kommunikáció megvalósítását segíti. Egy másik összetevő, a dbus- daemon a D-Bus üzenetek routolásáért, szórásáért felelős. -

Dell™ Gigaos 6.5 Release Notes July 2015
Dell™ GigaOS 6.5 Release Notes July 2015 These release notes provide information about the Dell™ GigaOS release. • About Dell GigaOS 6.5 • System requirements • Product licensing • Third-party contributions • About Dell About Dell GigaOS 6.5 For complete product documentation, visit http://software.dell.com/support/. System requirements Not applicable. Product licensing Not applicable. Third-party contributions Source code is available for this component on http://opensource.dell.com/releases/Dell_Software. Dell will ship the source code to this component for a modest fee in response to a request emailed to [email protected]. This product contains the following third-party components. For third-party license information, go to http://software.dell.com/legal/license-agreements.aspx. Source code for components marked with an asterisk (*) is available at http://opensource.dell.com. Dell GigaOS 6.5 1 Release Notes Table 1. List of third-party contributions Component License or acknowledgment abyssinica-fonts 1.0 SIL Open Font License 1.1 ©2003-2013 SIL International, all rights reserved acl 2.2.49 GPL (GNU General Public License) 2.0 acpid 1.0.10 GPL (GNU General Public License) 2.0 alsa-lib 1.0.22 GNU Lesser General Public License 2.1 alsa-plugins 1.0.21 GNU Lesser General Public License 2.1 alsa-utils 1.0.22 GNU Lesser General Public License 2.1 at 3.1.10 GPL (GNU General Public License) 2.0 atk 1.30.0 LGPL (GNU Lesser General Public License) 2.1 attr 2.4.44 GPL (GNU General Public License) 2.0 audit 2.2 GPL (GNU General Public License) 2.0 authconfig 6.1.12 GPL (GNU General Public License) 2.0 avahi 0.6.25 GNU Lesser General Public License 2.1 b43-fwcutter 012 GNU General Public License 2.0 basesystem 10.0 GPL (GNU General Public License) 3 bash 4.1.2-15 GPL (GNU General Public License) 3 bc 1.06.95 GPL (GNU General Public License) 2.0 bind 9.8.2 ISC 1995-2011. -

The Fedora Project
Introduction Fedora Features Security Important Packages Spins and Remixes Contributing to Fedora The Fedora Project A. Mani Member, Calcutta Mathematical Society Fedora QA-Ambassador-Documentation Indian GNU/Linux Users Group, Kolkata Chapter (ILUG-CALInfo) E-Mail: a:mani@member:ams:org Homepage: http://www.logicamani.co.cc SOFTWARE FREEDOM DAY, KOLKATA 15th Sept'2009 Introduction Fedora Features Security Important Packages Spins and Remixes Contributing to Fedora ABSTRACT An overview of the Fedora project is presented. Apart from giving a feel of the structure and working of the Fedora community, we also mention some important technical features of the Fedora Linux operating system. Introduction Fedora Features Security Important Packages Spins and Remixes Contributing to Fedora Outline 1 Introduction 2 Fedora Features 3 Security 4 Important Packages 5 Spins and Remixes 6 Contributing to Fedora Introduction Fedora Features Security Important Packages Spins and Remixes Contributing to Fedora What is Fedora? • 100% Free, Legal, Redistributable OS • Has over 25,000 Contributors • Includes the Latest Upstream Developments • Is a Stable, Secure, Powerful and User-Friendly OS • Is Upstream for RHEL, OLPC and Others • Has Over 10,000 Packages Introduction Fedora Features Security Important Packages Spins and Remixes Contributing to Fedora FOSS Fedora guarantees the Four Freedoms: • The freedom to run the program, for any purpose • The freedom to study how the program works, and adapt it to your needs • The freedom to redistribute copies so you can help others • The freedom to improve the program, and release your improvements to the public, so that the whole community benefits Introduction Fedora Features Security Important Packages Spins and Remixes Contributing to Fedora Who uses Fedora? • Roadrunner, the number one Supercomputer in the world • Over a hundred derivative distributions • RHEL and OLPC • Even some Robots do • Many universities and institutes in West Bengal • A. -
GL250 Enterprise Linux Systems Administration
EVALUATION COPY Unauthorized Reproduction or Enterprise Distribution Linux Systems AdministrationProhibited Student Workbook EVALUATION COPY Unauthorized Reproduction GL250 ENTERPRISE LINUX SYSTEMS ADMINISTRATION RHEL7 SLES12 or Distribution The contents of this course and all its modules and related materials, including handouts to audience members, are copyright ©2017 Guru Labs L.C. No part of this publication may be stored in a retrieval system, transmitted or reproduced in any way, including, but not limited to, photocopy, photograph, magnetic, electronic or other record, without the prior written permission of Guru Labs. This curriculum contains proprietary information which is for the exclusive use of customers of Guru Labs L.C., and is not to be shared with personnel other than those in attendance at this course. This instructional program, including all material provided herein, is supplied without any guarantees from Guru Labs L.C. Guru Labs L.C. assumes no liability for damages or legal action arising from Prohibited the use or misuse of contents or details contained herein. Photocopying any part of this manual without prior written consent of Guru Labs L.C. is a violation of federal law. This manual should not appear to be a photocopy. If you believe that Guru Labs training materials are being photocopied without permission, please email [email protected] or call 1-801-298-5227. Guru Labs L.C. accepts no liability for any claims, demands, losses, damages, costs or expenses suffered or incurred howsoever arising from or in connection -
Technical Notes All Changes in Fedora 13
Fedora 13 Technical Notes All changes in Fedora 13 Edited by The Fedora Docs Team Copyright © 2010 Red Hat, Inc. and others. The text of and illustrations in this document are licensed by Red Hat under a Creative Commons Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available at http://creativecommons.org/licenses/by-sa/3.0/. The original authors of this document, and Red Hat, designate the Fedora Project as the "Attribution Party" for purposes of CC-BY-SA. In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must provide the URL for the original version. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, JBoss, MetaMatrix, Fedora, the Infinity Logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. For guidelines on the permitted uses of the Fedora trademarks, refer to https:// fedoraproject.org/wiki/Legal:Trademark_guidelines. Linux® is the registered trademark of Linus Torvalds in the United States and other countries. Java® is a registered trademark of Oracle and/or its affiliates. XFS® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. All other trademarks are the property of their respective owners. Abstract This document lists all changed packages between Fedora 12 and Fedora 13. -
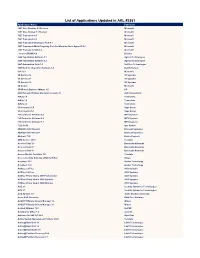
List of Applications Updated in ARL #2581
List of Applications Updated in ARL #2581 Application Name Publisher .NET Core Runtime 3.0 Preview Microsoft .NET Core Toolset 3.1 Preview Microsoft .NET Framework 4.5 Microsoft .NET Framework 4.6 Microsoft .NET Framework Developer Pack 4.7 Microsoft .NET Framework Multi-Targeting Pack for Windows Store Apps 4.5 RC Microsoft .NET Framework SDK 4.8 Microsoft _connect.BRAIN 4.8 Bizerba 2200 TapeStation Software 3.1 Agilent Technologies 2200 TapeStation Software 3.2 Agilent Technologies 24x7 Automation Suite 3.6 SoftTree Technologies 3500 Rack Configuration Software 6.0 Bently Nevada 365 16.0 Microsoft 3D Sprint 2.10 3D Systems 3D Sprint 2.11 3D Systems 3D Sprint 2.12 3D Systems 3D Viewer Microsoft 3PAR Host Explorer VMware 4.0 HP 4059 Extended Edition Attendant Console 2.1 ALE International 4uKey 1.4 Tenorshare 4uKey 1.6 Tenorshare 4uKey 2.2 Tenorshare 50 Accounts 21.0 Sage Group 50 Accounts 25.1 Sage Group 793 Controller Software 5.8 MTS Systems 793 Controller Software 5.9 MTS Systems 793 Controller Software 6.1 MTS Systems 7-Zip 19.00 Igor Pavlov ABAQUS 2018 Student Dassault Systemes ABAQUS 2019 Student Dassault Systemes Abstract 73.0 Elastic Projects ABU Service 14.10 Teradata Access Client 3.5 Barracuda Networks Access Client 3.7 Barracuda Networks Access Client 4.1 Barracuda Networks Access Module for Azure 15.1 Teradata Access Security Gateway (ASG) Soft Key Avaya AccuNest 10.3 Gerber Technology AccuNest 11.0 Gerber Technology ACDSee 2.3 Free ACD Systems ACDSee 2.4 Free ACD Systems ACDSee Photo Studio 2019 Professional ACD Systems -
Gl615 Linux for Unix Administrators Rhel7 Sles12
EVALUATION COPY Unauthorized Reproduction or Distribution Linux for Unix AdministratorsProhibited Student Workbook EVALUATION COPY Unauthorized Reproduction GL615 LINUX FOR UNIX ADMINISTRATORS RHEL7 SLES12 or Distribution The contents of this course and all its modules and related materials, including handouts to audience members, are copyright ©2017 Guru Labs L.C. No part of this publication may be stored in a retrieval system, transmitted or reproduced in any way, including, but not limited to, photocopy, photograph, magnetic, electronic or other record, without the prior written permission of Guru Labs. This curriculum contains proprietary information which is for the exclusive use of customers of Guru Labs L.C., and is not to be shared with personnel other than those in attendance at this course. This instructional program, including all material provided herein, is supplied without any guarantees from Guru Labs L.C. Guru Labs L.C. assumes no liability for damages or legal action arising from Prohibited the use or misuse of contents or details contained herein. Photocopying any part of this manual without prior written consent of Guru Labs L.C. is a violation of federal law. This manual should not appear to be a photocopy. If you believe that Guru Labs training materials are being photocopied without permission, please email [email protected] or call 1-801-298-5227. Guru Labs L.C. accepts no liability for any claims, demands, losses, damages, costs or expenses suffered or incurred howsoever arising from or in connection with the -
Red Hat Enterprise Linux 7 Migration Planning Guide
Red Hat Enterprise Linux 7 Migration Planning Guide Key differences between Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7 Last Updated: 2021-09-21 Red Hat Enterprise Linux 7 Migration Planning Guide Key differences between Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7 Legal Notice Copyright © 2021 Red Hat, Inc. The text of and illustrations in this document are licensed by Red Hat under a Creative Commons Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available at http://creativecommons.org/licenses/by-sa/3.0/ . In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must provide the URL for the original version. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, the Red Hat logo, JBoss, OpenShift, Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. Linux ® is the registered trademark of Linus Torvalds in the United States and other countries. Java ® is a registered trademark of Oracle and/or its affiliates. XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. MySQL ® is a registered trademark of MySQL AB in the United States, the European Union and other countries. Node.js ® is an official trademark of Joyent. -

Replugging the Modern Desktop
Replugging the Modern Desktop Kay Sievers <[email protected]> David Zeuthen <[email protected]> Linux Plumbers Conference Portland, OR, Sept 2009 History ● Back in the day ● /sbin/hotplug, scan entire /dev, /proc/scsi/scsi, /proc/partitions ● magicdev, supermount, subfs ● User conf / passwords stored in /etc or hard-coded ● Millions of LOC running as uid 0 History ● Back in the day ● /sbin/hotplug, scan entire /dev, /proc/scsi/scsi, /proc/partitions ● magicdev, supermount, subfs ● User conf / passwords stored in /etc or hard-coded ● Millions of LOC running as uid 0 ● Early Desktop Integration ● HAL, D-Bus, PolicyKit ● Separate Mechanism and Policy ● But... Implementation too complex, not scalable, not focused, too many abstractions ● Cutting the same cake in a different way ● 1st piece: Move device discovery/enumeration, classification, quirks, probing, event propagation to udev ● 2nd piece: Write libudev ● 3rd piece: Dedicated system services for major subsystems – DeviceKit-disks, DeviceKit-power, NetworkManager, PulseAudio, Bluez, Gypsy, ... ● 4th piece: Port the world to subsystem services – Apps using simple subsystems use libudev (Cheese) ApplicationApplication libudevlibudev Login Session udevd Kernel Space Kernel Application Application libdbus Login Session Subsystem System ApplicationServices Space libudevlibudev udevd Kernel Space Kernel Application Application Application Application Application Application libudevlibudev libudevlibudev libdbus ... Session 1 Session 2 Subsystem System ApplicationServices Space libudevlibudev udevd Kernel Space Kernel Application Application Application Application Application Application libudevlibudev libudevlibudev libdbus ... Session 1 Session 2 Other Services: Subsystem System System Message Bus ApplicationServices Space (D-Bus) libudevlibudev Session Tracking (ConsoleKit) Authority (PolicyKit) udevd ... Kernel Space Kernel kernel devices show up in a device tree in /sys /sys/devices |-- pci0000:00 .. -
Power Management Guide
Red Hat Enterprise Linux 7 Power Management Guide Managing and optimizing power consumption on RHEL 7 Last Updated: 2020-08-11 Red Hat Enterprise Linux 7 Power Management Guide Managing and optimizing power consumption on RHEL 7 Marie Doleželová Red Hat Customer Content Services [email protected] Jana Heves Red Hat Customer Content Services Jacquelynn East Red Hat Customer Content Services Don Domingo Red Hat Customer Content Services Rüdiger Landmann Red Hat Customer Content Services Jack Reed Red Hat Customer Content Services Red Hat, Inc. Legal Notice Copyright © 2017 Red Hat, Inc. This document is licensed by Red Hat under the Creative Commons Attribution-ShareAlike 3.0 Unported License. If you distribute this document, or a modified version of it, you must provide attribution to Red Hat, Inc. and provide a link to the original. If the document is modified, all Red Hat trademarks must be removed. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, the Red Hat logo, JBoss, OpenShift, Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. Linux ® is the registered trademark of Linus Torvalds in the United States and other countries. Java ® is a registered trademark of Oracle and/or its affiliates. XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. -

Installed Packages Red Hat Enterprise Linux
Installed Packages 389-ds-base.x86_64 1.2.11.15-60.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 389-ds-base-libs.x86_64 1.2.11.15-60.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 ConsoleKit.x86_64 0.4.1-3.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 ConsoleKit-libs.x86_64 0.4.1-3.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 ConsoleKit-x11.x86_64 0.4.1-3.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 DeviceKit-power.x86_64 014-3.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 GConf2.x86_64 2.28.0-6.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 GConf2-devel.x86_64 2.28.0-6.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 GConf2-gtk.x86_64 2.28.0-6.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 ImageMagick.x86_64 6.7.2.7-2.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 MAKEDEV.x86_64 3.24-6.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 ModemManager.x86_64 0.4.0-5.git20100628.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 MySQL-python.x86_64 1.2.3-0.3.c1.1.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 NetworkManager.x86_64 1:0.8.1-99.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 NetworkManager-glib.x86_64 1:0.8.1-99.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 NetworkManager-gnome.x86_64 1:0.8.1-99.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7 ORBit2.x86_64 2.14.17-5.el6 @anaconda-RedHatEnterpriseLinux-201507020259.x86_64/6.7