Building Socket-Aware BPF Programs Joe Stringer Cilium.Io [email protected]
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
An Introduction to Linux IPC
An introduction to Linux IPC Michael Kerrisk © 2013 linux.conf.au 2013 http://man7.org/ Canberra, Australia [email protected] 2013-01-30 http://lwn.net/ [email protected] man7 .org 1 Goal ● Limited time! ● Get a flavor of main IPC methods man7 .org 2 Me ● Programming on UNIX & Linux since 1987 ● Linux man-pages maintainer ● http://www.kernel.org/doc/man-pages/ ● Kernel + glibc API ● Author of: Further info: http://man7.org/tlpi/ man7 .org 3 You ● Can read a bit of C ● Have a passing familiarity with common syscalls ● fork(), open(), read(), write() man7 .org 4 There’s a lot of IPC ● Pipes ● Shared memory mappings ● FIFOs ● File vs Anonymous ● Cross-memory attach ● Pseudoterminals ● proc_vm_readv() / proc_vm_writev() ● Sockets ● Signals ● Stream vs Datagram (vs Seq. packet) ● Standard, Realtime ● UNIX vs Internet domain ● Eventfd ● POSIX message queues ● Futexes ● POSIX shared memory ● Record locks ● ● POSIX semaphores File locks ● ● Named, Unnamed Mutexes ● System V message queues ● Condition variables ● System V shared memory ● Barriers ● ● System V semaphores Read-write locks man7 .org 5 It helps to classify ● Pipes ● Shared memory mappings ● FIFOs ● File vs Anonymous ● Cross-memory attach ● Pseudoterminals ● proc_vm_readv() / proc_vm_writev() ● Sockets ● Signals ● Stream vs Datagram (vs Seq. packet) ● Standard, Realtime ● UNIX vs Internet domain ● Eventfd ● POSIX message queues ● Futexes ● POSIX shared memory ● Record locks ● ● POSIX semaphores File locks ● ● Named, Unnamed Mutexes ● System V message queues ● Condition variables ● System V shared memory ● Barriers ● ● System V semaphores Read-write locks man7 .org 6 It helps to classify ● Pipes ● Shared memory mappings ● FIFOs ● File vs Anonymous ● Cross-memoryn attach ● Pseudoterminals tio a ● proc_vm_readv() / proc_vm_writev() ● Sockets ic n ● Signals ● Stream vs Datagram (vs uSeq. -
Linux and Free Software: What and Why?
Linux and Free Software: What and Why? (Qué son Linux y el Software libre y cómo beneficia su uso a las empresas para lograr productividad económica y ventajas técnicas?) JugoJugo CreativoCreativo Michael Kerrisk UniversidadUniversidad dede SantanderSantander UDESUDES © 2012 Bucaramanga,Bucaramanga, ColombiaColombia [email protected] 77 JuneJune 20122012 http://man7.org/ man7.org 1 Who am I? ● Programmer, educator, and writer ● UNIX since 1987; Linux since late 1990s ● Linux man-pages maintainer since 2004 ● Author of a book on Linux programming man7.org 2 Overview ● What is Linux? ● How are Linux and Free Software created? ● History ● Where is Linux used today? ● What is Free Software? ● Source code; Software licensing ● Importance and advantages of Free Software and Software Freedom ● Concluding remarks man7.org 3 ● What is Linux? ● How are Linux and Free Software created? ● History ● Where is Linux used today? ● What is Free Software? ● Source code; Software licensing ● Importance and advantages of Free Software and Software Freedom ● Concluding remarks man7.org 4 What is Linux? ● An operating system (sistema operativo) ● (Operating System = OS) ● Examples of other operating systems: ● Windows ● Mac OS X Penguins are the Linux mascot man7.org 5 But, what's an operating system? ● Two definitions: ● Kernel ● Kernel + package of common programs man7.org 6 OS Definition 1: Kernel ● Computer scientists' definition: ● Operating System = Kernel (núcleo) ● Kernel = fundamental program on which all other programs depend man7.org 7 Programs can live -
Jitk: a Trustworthy In-Kernel Interpreter Infrastructure
Jitk: A trustworthy in-kernel interpreter infrastructure Xi Wang, David Lazar, Nickolai Zeldovich, Adam Chlipala, Zachary Tatlock MIT and University of Washington Modern OSes run untrusted user code in kernel In-kernel interpreters - Seccomp: sandboxing (Linux) - BPF: packet filtering - INET_DIAG: socket monitoring - Dtrace: instrumentation Critical to overall system security - Any interpreter bugs are serious! 2/30 Many bugs have been found in interpreters Kernel space bugs - Control flow errors: incorrect jump offset, ... - Arithmetic errors: incorrect result, ... - Memory errors: buffer overflow, ... - Information leak: uninitialized read Kernel-user interface bugs - Incorrect encoding/decoding User space bugs - Incorrect input generated by tools/libraries Some have security consequences: CVE-2014-2889, ... See our paper for a case study of bugs 3/30 How to get rid of all these bugs at once? Theorem proving can help kill all these bugs seL4: provably correct microkernel [SOSP'09] CompCert: provably correct C compiler [CACM'09] This talk: Jitk - Provably correct interpreter for running untrusted user code - Drop-in replacement for Linux's seccomp - Built using Coq proof assistant + CompCert 5/30 Theorem proving: overview specification proof implementation Proof is machine-checkable: Coq proof assistant Proof: correct specification correct implementation Specification should be much simpler than implementation 6/30 Challenges What is the specification? How to translate systems properties into proofs? How to extract a running -

Chapter 1. Origins of Mac OS X
1 Chapter 1. Origins of Mac OS X "Most ideas come from previous ideas." Alan Curtis Kay The Mac OS X operating system represents a rather successful coming together of paradigms, ideologies, and technologies that have often resisted each other in the past. A good example is the cordial relationship that exists between the command-line and graphical interfaces in Mac OS X. The system is a result of the trials and tribulations of Apple and NeXT, as well as their user and developer communities. Mac OS X exemplifies how a capable system can result from the direct or indirect efforts of corporations, academic and research communities, the Open Source and Free Software movements, and, of course, individuals. Apple has been around since 1976, and many accounts of its history have been told. If the story of Apple as a company is fascinating, so is the technical history of Apple's operating systems. In this chapter,[1] we will trace the history of Mac OS X, discussing several technologies whose confluence eventually led to the modern-day Apple operating system. [1] This book's accompanying web site (www.osxbook.com) provides a more detailed technical history of all of Apple's operating systems. 1 2 2 1 1.1. Apple's Quest for the[2] Operating System [2] Whereas the word "the" is used here to designate prominence and desirability, it is an interesting coincidence that "THE" was the name of a multiprogramming system described by Edsger W. Dijkstra in a 1968 paper. It was March 1988. The Macintosh had been around for four years. -

Linux Kernel and Driver Development Training Slides
Linux Kernel and Driver Development Training Linux Kernel and Driver Development Training © Copyright 2004-2021, Bootlin. Creative Commons BY-SA 3.0 license. Latest update: October 9, 2021. Document updates and sources: https://bootlin.com/doc/training/linux-kernel Corrections, suggestions, contributions and translations are welcome! embedded Linux and kernel engineering Send them to [email protected] - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 1/470 Rights to copy © Copyright 2004-2021, Bootlin License: Creative Commons Attribution - Share Alike 3.0 https://creativecommons.org/licenses/by-sa/3.0/legalcode You are free: I to copy, distribute, display, and perform the work I to make derivative works I to make commercial use of the work Under the following conditions: I Attribution. You must give the original author credit. I Share Alike. If you alter, transform, or build upon this work, you may distribute the resulting work only under a license identical to this one. I For any reuse or distribution, you must make clear to others the license terms of this work. I Any of these conditions can be waived if you get permission from the copyright holder. Your fair use and other rights are in no way affected by the above. Document sources: https://github.com/bootlin/training-materials/ - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 2/470 Hyperlinks in the document There are many hyperlinks in the document I Regular hyperlinks: https://kernel.org/ I Kernel documentation links: dev-tools/kasan I Links to kernel source files and directories: drivers/input/ include/linux/fb.h I Links to the declarations, definitions and instances of kernel symbols (functions, types, data, structures): platform_get_irq() GFP_KERNEL struct file_operations - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 3/470 Company at a glance I Engineering company created in 2004, named ”Free Electrons” until Feb. -

Packet Capture Procedures on Cisco Firepower Device
Packet Capture Procedures on Cisco Firepower Device Contents Introduction Prerequisites Requirements Components Used Steps to Capture Packets Copy a Pcap File Introduction This document describes how to use the tcpdump command in order to capture packets that are seen by a network interface of your Firepower device. It uses Berkeley Packet Filter (BPF) syntax. Prerequisites Requirements Cisco recommends that you have knowledge of the Cisco Firepower device and the virtual device models. Components Used This document is not restricted to specific software and hardware versions. The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command. Warning: If you run tcpdump command on a production system, it can impact network performance. Steps to Capture Packets Log in to the CLI of your Firepower device. In versions 6.1 and later, enter capture-traffic. For example, > capture-traffic Please choose domain to capture traffic from: 0 - eth0 1 - Default Inline Set (Interfaces s2p1, s2p2) In versions 6.0.x.x and earlier, enter system support capture-traffic. For example, > system support capture-traffic Please choose domain to capture traffic from: 0 - eth0 1 - Default Inline Set (Interfaces s2p1, s2p2) After you make a selection, you will be prompted for options: Please specify tcpdump options desired. (or enter '?' for a list of supported options) Options: In order to capture sufficient data from the packets, it is necessary to use the -s option in order to set the snaplength correctly. -

Ebpf-Based Content and Computation-Aware Communication for Real-Time Edge Computing
eBPF-based Content and Computation-aware Communication for Real-time Edge Computing Sabur Baidya1, Yan Chen2 and Marco Levorato1 1Donald Bren School of Information and Computer Science, UC Irvine e-mail: fsbaidya, [email protected] 2America Software Laboratory, Huawei, e-mail: [email protected] Abstract—By placing computation resources within a one-hop interference constraints on IoT data streams and facilitate their wireless topology, the recent edge computing paradigm is a key coexistence. enabler of real-time Internet of Things (IoT) applications. In In this paper, we propose a computation-aware commu- the context of IoT scenarios where the same information from a sensor is used by multiple applications at different locations, the nication control framework for real-time IoT applications data stream needs to be replicated. However, the transportation generating high-volume data traffic processed at the network of parallel streams might not be feasible due to limitations in the edge. Driven by QoC requirements, the framework provides capacity of the network transporting the data. To address this real-time user-controlled packet replication and forwarding issue, a content and computation-aware communication control inside the in-kernel Virtual Machines (VM) using an extended framework is proposed based on the Software Defined Network (SDN) paradigm. The framework supports multi-streaming using Berkeley Packet Filter (eBPF) [9]. The implementation uses the extended Berkeley Packet Filter (eBPF), where the traffic flow the concepts of SDN and NFV to achieve highly program- and packet replication for each specific computation process is able and dynamic packet replication. Resource allocation is controlled by a program running inside an in-kernel Virtual Ma- semantic and content-aware, and, in the considered case, chine (VM). -
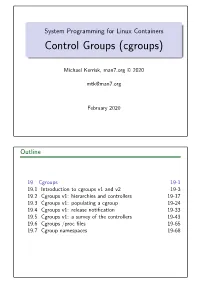
Control Groups (Cgroups)
System Programming for Linux Containers Control Groups (cgroups) Michael Kerrisk, man7.org © 2020 [email protected] February 2020 Outline 19 Cgroups 19-1 19.1 Introduction to cgroups v1 and v2 19-3 19.2 Cgroups v1: hierarchies and controllers 19-17 19.3 Cgroups v1: populating a cgroup 19-24 19.4 Cgroups v1: release notification 19-33 19.5 Cgroups v1: a survey of the controllers 19-43 19.6 Cgroups /procfiles 19-65 19.7 Cgroup namespaces 19-68 Outline 19 Cgroups 19-1 19.1 Introduction to cgroups v1 and v2 19-3 19.2 Cgroups v1: hierarchies and controllers 19-17 19.3 Cgroups v1: populating a cgroup 19-24 19.4 Cgroups v1: release notification 19-33 19.5 Cgroups v1: a survey of the controllers 19-43 19.6 Cgroups /procfiles 19-65 19.7 Cgroup namespaces 19-68 Goals Cgroups is a big topic Many controllers V1 versus V2 interfaces Our goal: understand fundamental semantics of cgroup filesystem and interfaces Useful from a programming perspective How do I build container frameworks? What else can I build with cgroups? And useful from a system engineering perspective What’s going on underneath my container’s hood? System Programming for Linux Containers ©2020, Michael Kerrisk Cgroups 19-4 §19.1 Focus We’ll focus on: General principles of operation; goals of cgroups The cgroup filesystem Interacting with the cgroup filesystem using shell commands Problems with cgroups v1, motivations for cgroups v2 Differences between cgroups v1 and v2 We’ll look briefly at some of the controllers System Programming for Linux Containers ©2020, Michael Kerrisk Cgroups 19-5 §19.1 -

Security Bugs in Embedded Interpreters
Security bugs in embedded interpreters The MIT Faculty has made this article openly available. Please share how this access benefits you. Your story matters. Citation Haogang Chen, Cody Cutler, Taesoo Kim, Yandong Mao, Xi Wang, Nickolai Zeldovich, and M. Frans Kaashoek. 2013. Security bugs in embedded interpreters. In Proceedings of the 4th Asia-Pacific Workshop on Systems (APSys '13). ACM, New York, NY, USA, Article 17, 7 pages. As Published http://dx.doi.org/10.1145/2500727.2500747 Publisher Edition Open Access Version Author's final manuscript Citable link http://hdl.handle.net/1721.1/86887 Terms of Use Creative Commons Attribution-Noncommercial-Share Alike Detailed Terms http://creativecommons.org/licenses/by-nc-sa/4.0/ Security bugs in embedded interpreters Haogang Chen Cody Cutler Taesoo Kim Yandong Mao Xi Wang Nickolai Zeldovich M. Frans Kaashoek MIT CSAIL Abstract Embedded interpreters raise interesting security con- Because embedded interpreters offer flexibility and per- cerns. First, many real-world systems do not adopt sand- formance, they are becoming more prevalent, and can be boxing techniques such as process isolation [20] or soft- found at nearly every level of the software stack. As one ware fault isolation [28] for embedded interpreters, possi- example, the Linux kernel defines languages to describe bly due to performance considerations. Consequently, a packet filtering rules and uses embedded interpreters to compromise of the interpreter is likely to lead to a com- filter packets at run time. As another example, theRAR promise of the host system as well. Second, embedded in- archive format allows embedding bytecode in compressed terpreters often validate untrusted bytecode using ad-hoc files to describe reversible transformations for decompres- rules, which is error-prone. -

Open Source Software
OPEN SOURCE SOFTWARE Product AVD9x0x0-0010 Firmware and version 3.4.57 Notes on Open Source software The TCS device uses Open Source software that has been released under specific licensing requirements such as the ”General Public License“ (GPL) Version 2 or 3, the ”Lesser General Public License“ (LGPL), the ”Apache License“ or similar licenses. Any accompanying material such as instruction manuals, handbooks etc. contain copyright notes, conditions of use or licensing requirements that contradict any applicable Open Source license, these conditions are inapplicable. The use and distribution of any Open Source software used in the product is exclusively governed by the respective Open Source license. The programmers provided their software without ANY WARRANTY, whether implied or expressed, of any fitness for a particular purpose. Further, the programmers DECLINE ALL LIABILITY for damages, direct or indirect, that result from the using this software. This disclaimer does not affect the responsibility of TCS. AVAILABILITY OF SOURCE CODE: Where the applicable license entitles you to the source code of such software and/or other additional data, you may obtain it for a period of three years after purchasing this product, and, if required by the license conditions, for as long as we offer customer support for the device. If this document is available at the website of TCS and TCS offers a download of the firmware, the offer to receive the source code is valid for a period of three years and, if required by the license conditions, for as long as TCS offers customer support for the device. TCS provides an option for obtaining the source code: You may obtain any version of the source code that has been distributed by TCS for the cost of reproduction of the physical copy. -
Greg Kroah-Hartman [email protected] Github.Com/Gregkh/Presentation-Kdbus
kdbus IPC for the modern world Greg Kroah-Hartman [email protected] github.com/gregkh/presentation-kdbus Interprocess Communication ● signal ● synchronization ● communication standard signals realtime The Linux Programming Interface, Michael Kerrisk, page 878 POSIX semaphore futex synchronization named eventfd unnamed semaphore System V semaphore “record” lock file lock file lock mutex threads condition variables barrier read/write lock The Linux Programming Interface, Michael Kerrisk, page 878 data transfer pipe communication FIFO stream socket pseudoterminal POSIX message queue message System V message queue memory mapping System V shared memory POSIX shared memory shared memory memory mapping Anonymous mapping mapped file The Linux Programming Interface, Michael Kerrisk, page 878 Android ● ashmem ● pmem ● binder ashmem ● POSIX shared memory for the lazy ● Uses virtual memory ● Can discard segments under pressure ● Unknown future pmem ● shares memory between kernel and user ● uses physically contigous memory ● GPUs ● Unknown future binder ● IPC bus for Android system ● Like D-Bus, but “different” ● Came from system without SysV types ● Works on object / message level ● Needs large userspace library ● NEVER use outside an Android system binder ● File descriptor passing ● Used for Intents and application separation ● Good for small messages ● Not for streams of data ● NEVER use outside an Android system QNX message passing ● Tight coupling to microkernel ● Send message and control, to another process ● Used to build complex messages -

Host-Based Anomaly Detection with Extended BPF
Host-Based Anomaly Detection with Extended BPF COMP4906 Honours Thesis William Findlay April 5, 2020 Under the supervision of Dr. Anil Somayaji Carleton University Abstract William Findlay Abstract System introspection is becoming an increasingly attractive option for maintaining operating system stability and security. This is primarily due to the many recent advances in system introspection technology; in particular, the 2013 introduction of Extended Berkeley Packet Filter (eBPF ) into the Linux Kernel [63, 64] along with the recent development of more usable interfaces such as the BPF Compiler Collection (bcc)[29] has resulted in a highly compelling, performant, and (perhaps most importantly) safe subsystem for both kernel and userland instrumentation. The scope, safety, and performance of eBPF system introspection has potentially powerful applications in the domain of computer security. In order to demonstrate this, I present ebpH, an eBPF implementation of Somayaji’s [58] Process Homeostasis (pH ). ebpH is an intrusion detection system (IDS) that uses eBPF programs to instrument system calls and establish normal behavior for processes, building a profile for each executable on the system; subsequently, ebpH can warn the user when it detects process behavior that violates the established profiles. Experimental results show that ebpH can detect anomalies in process behavior with negligible overhead. Furthermore, ebpH’s anomaly detection comes with zero risk to the system thanks to the safety guarantees of eBPF, rendering it an ideal solution for monitoring production systems. This thesis will discuss the design and implementation of ebpH along with the technical challenges which occurred along the way. It will then present experimental data and per- formance benchmarks that demonstrate ebpH’s ability to monitor process behavior with minimal overhead.