Do-Not-Track As Default Joshua A.T
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Web Never Forgets: Persistent Tracking Mechanisms in the Wild
The Web Never Forgets: Persistent Tracking Mechanisms in the Wild Gunes Acar1, Christian Eubank2, Steven Englehardt2, Marc Juarez1 Arvind Narayanan2, Claudia Diaz1 1KU Leuven, ESAT/COSIC and iMinds, Leuven, Belgium {name.surname}@esat.kuleuven.be 2Princeton University {cge,ste,arvindn}@cs.princeton.edu ABSTRACT 1. INTRODUCTION We present the first large-scale studies of three advanced web tracking mechanisms — canvas fingerprinting, evercookies A 1999 New York Times article called cookies compre and use of “cookie syncing” in conjunction with evercookies. hensive privacy invaders and described them as “surveillance Canvas fingerprinting, a recently developed form of browser files that many marketers implant in the personal computers fingerprinting, has not previously been reported in the wild; of people.” Ten years later, the stealth and sophistication of our results show that over 5% of the top 100,000 websites tracking techniques had advanced to the point that Edward employ it. We then present the first automated study of Felten wrote “If You’re Going to Track Me, Please Use Cook evercookies and respawning and the discovery of a new ev ies” [18]. Indeed, online tracking has often been described ercookie vector, IndexedDB. Turning to cookie syncing, we as an “arms race” [47], and in this work we study the latest present novel techniques for detection and analysing ID flows advances in that race. and we quantify the amplification of privacy-intrusive track The tracking mechanisms we study are advanced in that ing practices due to cookie syncing. they are hard to control, hard to detect and resilient Our evaluation of the defensive techniques used by to blocking or removing. -
Do Not Track a Nokia Browser Look
Do Not Track Nokia Browser Position - Vikram Malaiya Copyright: Nokia Corporation, 2011 Our understanding of Do Not Track (DNT) • DNT is a technology to enables users to opt out of third-party web tracking • No agreed upon definition of DNT. There are currently 3 major technology proposals for responding to third-party privacy concern. 1. Stanford University and Mozilla’s DNT HTTP Header technique. 2. Blacklist based technique such as Microsoft’s ‘Tracking Protection’ which is part of IE9 3. Network Advertising Initiative’s model of a per company opt-out cookie. Opt-out cookie approach is being promoted by Google. DNT as HTTP Header The Browser adds ‘DNT’/ ‘X-Do-Not-Track’ to its http header. The header is sent out to the server with every web request. This header acts as a signal to the server suggesting that the user wishes to opt out of tracking. Adoption: Firefox 4, IE9 DNT as HTTP Header • Pros: – Scope: Server could apply restrictions to all third party entities and tracking mechanisms – Persistent: No reconfiguration needed once set – Simple: Easy to implement on the browser side • Cons: – Only work as long as the server honors users preferences – No way to enforce national regulations/legislations to servers located beyond country boundaries Block(Black) List / Tracking Protection This is a consumer opt-in mechanism which blocks web connections from known tracking domains that are compiled on a list. First party Third party Adoption: ‘Tracking Protection’ in Internet Explorer 9 cy.analytix.com The downloadable Tracking allow Protection Lists enable IE9 xy.ads.com consumers to control what deny third-party site content can deny track them when they’re ads.tracker.com Tracking Protection online. -

Internet Explorer 9 Previewed 17 March 2010, by Lin Edwards
Internet Explorer 9 previewed 17 March 2010, by Lin Edwards translation necessary. This will improve performance because there is a massive difference in speed between compiled and interpreted code. This, and the speed gain by using the GPU, was demonstrated at the conference with a display of increasing numbers of spinning three-dimensional icons, which the IE9 preview could handle far better than any other browser. Since less of the first core of CPU is being used, the display is much faster, and will also allow developers to create a new class of Web applications. Another change in the new browser is an emphasis on browser interoperability, so that programs (PhysOrg.com) -- Microsoft has released the written for IE9 should run properly on other preview version of Internet Explorer 9, which has browsers as well. Hachamovitch said that as HTML5 integration, background compiled Internet Explorer supports more of the markups Javascript, and scalable vector graphics (SVG) used by websites, their Acid score will improve. capability. (This is a test run by W3C, the official Internet standards body.) The preview browser engine The preview code for the Internet browser’s scored 55 out of 100, which is a significant rendering engine was revealed at Microsoft’s improvement on the previous version’s score of 20. MIX10 developer conference in Las Vegas yesterday. The major goals for the new engine are It is not yet known when the new browser will be support for the emerging Web standards such as released as a beta or final version. Meanwhile, the SVG and HTML5, and greater speed. -

WSJ 2010. Microsoft Quashed Effort to Boost Online Privacy.Pdf
http://online.wsj.com/article/SB10001424052748703467304575383530439838568.html?mod=WSJ_hpp_LEADSecondNewsCollection#pr... WHAT THEY KNOW AUGUST 2, 2010 Microsoft Quashed Effort to Boost Online Privacy By NICK WINGFIELD The online habits of most people who use the world's dominant Web browser are an open book to advertisers. That wasn't the plan at first. In early 2008, Microsoft Corp.'s product planners for the Internet Explorer 8.0 browser intended to give users a simple, effective way to avoid being tracked online. They wanted to design the software to automatically thwart common tracking tools, unless a user deliberately switched to settings affording less privacy. That triggered heated debate inside Microsoft. As the leading maker of Web browsers, the gateway software to the Internet, Microsoft must balance conflicting interests: helping people surf the Web with its browser to keep their mouse clicks private, and helping advertisers who want to see those clicks. In the end, the product planners lost a key part of the debate. The winners: executives who argued that giving automatic privacy to consumers would make it tougher for Microsoft to profit from selling online ads. Microsoft built its browser so that users must deliberately turn on privacy settings every time they start up the software. Microsoft's original privacy plans for the new Explorer were "industry-leading" and technically superior to privacy features in earlier browsers, says Simon Davies, a privacy-rights advocate in the U.K. whom Microsoft consulted while forming its browser privacy plans. Most users of the final product aren't even aware its privacy settings are available, he says. -

Hunting for Hackers, N.S.A. Secretly Expands Internet Spying at U.S. Border - Nytimes.Com
6/4/2015 Hunting for Hackers, N.S.A. Secretly Expands Internet Spying at U.S. Border - NYTimes.com http://nyti.ms/1dP5ida POLITICS Hunting for Hackers, N.S.A. Secretly Expands Internet Spying at U.S. Border By CHARLIE SAVAGE, JULIA ANGWIN, JEFF LARSON and HENRIK MOLTKE JUNE 4, 2015 WASHINGTON — Without public notice or debate, the Obama administration has expanded the National Security Agency’s warrantless surveillance of Americans’ international Internet traffic to search for evidence of malicious computer hacking, according to classified N.S.A. documents. In mid-2012, Justice Department lawyers wrote two secret memos permitting the spy agency to begin hunting on Internet cables, without a warrant and on American soil, for data linked to computer intrusions originating abroad — including traffic that flows to suspicious Internet addresses or contains malware, the documents show. The Justice Department allowed the agency to monitor only addresses and “cybersignatures” — patterns associated with computer intrusions — that it could tie to foreign governments. But the documents also note that the N.S.A. sought permission to target hackers even when it could not establish any links to foreign powers. http://www.nytimes.com/2015/06/05/us/hunting-for-hackers-nsa-secretly-expands-internet-spying-at-us-border.html?emc=eta1&_r=0 1/6 6/4/2015 Hunting for Hackers, N.S.A. Secretly Expands Internet Spying at U.S. Border - NYTimes.com The disclosures, based on documents provided by Edward J. Snowden, the former N.S.A. contractor, and shared with The New York Times and ProPublica, come at a time of unprecedented cyberattacks on American financial institutions, businesses and government agencies, but also of greater scrutiny of secret legal justifications for broader government surveillance. -

Statement of Justin Brookman Director, Consumer Privacy Center for Democracy & Technology Before the U.S. Senate Committee O
Statement of Justin Brookman Director, Consumer Privacy Center for Democracy & Technology Before the U.S. Senate Committee on Commerce, Science, and Transportation Hearing on “A Status Update on the Development of Voluntary Do-Not-Track Standards” April 24, 2013 Chairman Rockefeller, Ranking Member Thune, and Members of the Committee: On behalf of the Center for Democracy & Technology (CDT), I thank you for the opportunity to testify today. We applaud the leadership the Chairman has demonstrated in examining the challenges in developing a consensus Do Not Track standard and appreciate the opportunity to address the continued insufficiency of self-regulatory consumer privacy protections. CDT is a non-profit, public interest organization dedicated to preserving and promoting openness, innovation, and freedom on the decentralized Internet. I currently serve as the Director of CDT’s Consumer Privacy Project. I am also an active participant in the Worldwide Web Consortium’s Tracking Protection Working Group, where I serve as editor of the “Tracking Compliance and Scope” specification — the document that purports to define what Do Not Track should mean. My testimony today will briefly describe the history of online behavioral advertising and the genesis of the Do Not Track initiative. I will then describe the current state of the World Wide Web Consortium’s efforts to create Do Not Track standards and the challenges going forward to implement Do Not Track tools successfully. I will conclude with my thoughts on the future of Do Not Track. and why I believe that this protracted struggle demonstrates the need for the fundamental reform of our nation’s privacy protection framework for commercial and government collection and use of personal information. -

Amazon Silk Developer Guide Amazon Silk Developer Guide
Amazon Silk Developer Guide Amazon Silk Developer Guide Amazon Silk: Developer Guide Copyright © 2015 Amazon Web Services, Inc. and/or its affiliates. All rights reserved. The following are trademarks of Amazon Web Services, Inc.: Amazon, Amazon Web Services Design, AWS, Amazon CloudFront, AWS CloudTrail, AWS CodeDeploy, Amazon Cognito, Amazon DevPay, DynamoDB, ElastiCache, Amazon EC2, Amazon Elastic Compute Cloud, Amazon Glacier, Amazon Kinesis, Kindle, Kindle Fire, AWS Marketplace Design, Mechanical Turk, Amazon Redshift, Amazon Route 53, Amazon S3, Amazon VPC, and Amazon WorkDocs. In addition, Amazon.com graphics, logos, page headers, button icons, scripts, and service names are trademarks, or trade dress of Amazon in the U.S. and/or other countries. Amazon©s trademarks and trade dress may not be used in connection with any product or service that is not Amazon©s, in any manner that is likely to cause confusion among customers, or in any manner that disparages or discredits Amazon. All other trademarks not owned by Amazon are the property of their respective owners, who may or may not be affiliated with, connected to, or sponsored by Amazon. AWS documentation posted on the Alpha server is for internal testing and review purposes only. It is not intended for external customers. Amazon Silk Developer Guide Table of Contents What Is Amazon Silk? .................................................................................................................... 1 Split Browser Architecture ...................................................................................................... -
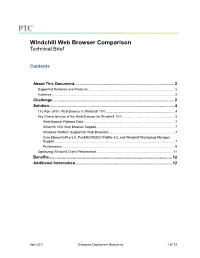
Windchill Web Browser Comparison Technical Brief
Windchill Web Browser Comparison Technical Brief Contents About This Document ........................................................................................... 2 Supported Releases and Products ................................................................................................ 2 Audience ........................................................................................................................................ 2 Challenge ............................................................................................................... 2 Solution ................................................................................................................. 4 The Role of the Web Browser in Windchill 10.0 ............................................................................ 4 Key Characteristics of the Web Browser for Windchill 10.0 .......................................................... 5 Web Browser Release Date ..................................................................................................... 7 Windchill 10.0 Web Browser Support ....................................................................................... 7 Windows Platform Support for Web Browsers ......................................................................... 7 Creo Elements/Pro 5.0, Pro/ENGINEER Wildfire 4.0, and Windchill Workgroup Manager Support ..................................................................................................................................... 7 Performance ............................................................................................................................ -

I Can't Generalize a Whole Lot About the Maxthon Cloud Browser, Which Got
I can’t generalize a whole lot about the Maxthon Cloud Browser, which got a major upgrade to Version 4.x in a December preview and was officially released on February 25. Maxthon Cloud Browser versions are available for Windows, OS X, iOS and Android, and it’s designed to provide users with a seamless and unified user experience across multiple devices and platforms. I can’t speak to the Windows and Android versions, but I’m unevenly impressed with the OS X and iOS variants. I found myself quickly becoming a fan of the OS X version; it’s a lot like Google’s Chrome browser—very fast and slick with super-smooth performance—but more so. It incorporates pretty much everything I like about Chrome, such as an automatic Google Translate machine translation option. The iOS version isn’t bad, just not nearly as outstanding as the OS X version. Interestingly, that would be my assessment of Google Chrome for iOS compared with Chrome for OS X, as well, and I think the reason in both instances is Apple’s imposition on its own WebKit technology on iOS browsers. Using Maxthon Cloud Browser for iOS is not terribly different from the standard iOS Safari experience in terms of speed, but the iOS version of Maxthon has an absolutely maddening bug that sporadically turns the screen brightness on my iPad 2 down to minimum, obliging a trip to the iOS Settings to restore it. I suspect that Maxthon for iOS’s Brightness Control feature that purportedly lets you adjust screen brightness from within the browser, and/or Night Mode that adjusts screen brightness in low light situations are responsible for this behavior. -

Stanford Students Create 'Do Not Track' Software 3 December 2010, by Adam Gorlick
Stanford students create 'do not track' software 3 December 2010, By Adam Gorlick such as Firefox requests content or sends data using HTTP - the protocol that underlies the web - it can optionally include extra information called a "header." Do Not Track adds a header that signals the user does not want to be tracked. The technology can now be installed as an add-on for Firefox, and Mayer and Narayanan are working to make it operate with Chrome. Safari and Internet Explorer do not support their software. Once the add-on is installed, the user doesn't have to do anything else. Each time a website is visited, a do- "We always thought Do Not Track was a great technical not-track message is automatically sent. idea, and it has a real impact that's feasible," said Jonathan Mayer, one of two researchers who created The students, who have been working with the software. computer science Professor John Mitchell, are also creating ways to configure web servers to honor their code. As a government agency pushes for a "do not Sending businesses and advertisers the message track" mechanism to protect online consumer that you don't want to be tracked is one thing. But privacy, a pair of Stanford researchers is getting them to respect your privacy is another - developing the technology to make it work. and it's something that hinges on government enforcement. For about four months before Wednesday's release of the Federal Trade Commission's "At the end of day, Congress would probably have recommendations for increasing Internet privacy, to pass a law empowering the FTC to enforce this," Jonathan Mayer and Arvind Narayanan have been said Ryan Calo, director of the Consumer Privacy creating software that would let users opt out of Project for Stanford Law School's Center for third-party web tracking and tell advertisers to stop Internet and Society. -

Regulating the Zero-Day Vulnerability Trade: A
REGULATING THE ZERO-DAY VULNERABILITY TRADE: A PRELIMINARY ANALYSIS MAILYN FIDLER* I. INTRODUCTION In April 2014, computer security experts revealed “Heartbleed,” a vulnerability in software encrypting information transmitted over the Internet.1 The bug existed in OpenSSL, which up to two- thirds of websites use to encrypt Internet traffic.2 Heartbleed exposed large swaths of data to interception and exploitation. Initially, news stories speculated the U.S. government knew about Heartbleed, and, rather than disclosing it, had been using it or keeping it for intelligence or other purposes, leaving Internet users at risk.3 Although the Heartbleed speculation seems to have been unfounded, public concerns about Heartbleed, combined with distrust created by Edward Snowden’s disclosures about the National Security Agency (NSA), forced the U.S. government to detail4 how it deals with software vulnerabilities it knows about but that remain unknown to software vendors or users – “zero-day” vulnerabilities or “zero-days.”5 The Obama administration’s response to Heartbleed raised further questions about U.S. policy on zero- day vulnerabilities, including the U.S. government’s role in purchasing vulnerabilities from the zero-day market. * Marshall Scholar, Department of Politics and International Relations, University of Oxford. I would like to thank the following people for their advice, input, and support during my work on this research: Lily Ablon, Richard Bejtlich, Fred Cate, Scott Charney, Jack Goldsmith, Jennifer Granick, Herb Lin, Jonathan Mayer, Chris Soghoian, Michael Sulmeyer, and Peter Swire. 1 Nicole Perlroth, Experts Find a Door Ajar in an Internet Security Method Thought Safe, N.Y. TIMES (Apr. -

Web Tracking: Mechanisms, Implications, and Defenses Tomasz Bujlow, Member, IEEE, Valentín Carela-Español, Josep Solé-Pareta, and Pere Barlet-Ros
ARXIV.ORG DIGITAL LIBRARY 1 Web Tracking: Mechanisms, Implications, and Defenses Tomasz Bujlow, Member, IEEE, Valentín Carela-Español, Josep Solé-Pareta, and Pere Barlet-Ros Abstract—This articles surveys the existing literature on the of ads [1], [2], price discrimination [3], [4], assessing our methods currently used by web services to track the user online as health and mental condition [5], [6], or assessing financial well as their purposes, implications, and possible user’s defenses. credibility [7]–[9]. Apart from that, the data can be accessed A significant majority of reviewed articles and web resources are from years 2012 – 2014. Privacy seems to be the Achilles’ by government agencies and identity thieves. Some affiliate heel of today’s web. Web services make continuous efforts to programs (e.g., pay-per-sale [10]) require tracking to follow obtain as much information as they can about the things we the user from the website where the advertisement is placed search, the sites we visit, the people with who we contact, to the website where the actual purchase is made [11]. and the products we buy. Tracking is usually performed for Personal information in the web can be voluntarily given commercial purposes. We present 5 main groups of methods used for user tracking, which are based on sessions, client by the user (e.g., by filling web forms) or it can be collected storage, client cache, fingerprinting, or yet other approaches. indirectly without their knowledge through the analysis of the A special focus is placed on mechanisms that use web caches, IP headers, HTTP requests, queries in search engines, or even operational caches, and fingerprinting, as they are usually very by using JavaScript and Flash programs embedded in web rich in terms of using various creative methodologies.