Automated Malware Analysis Report for Azditdeshm
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

7.4, Integration with Google Apps Is Deprecated
Google Search Appliance Integrating with Google Apps Google Search Appliance software version 7.2 and later Google, Inc. 1600 Amphitheatre Parkway Mountain View, CA 94043 www.google.com GSA-APPS_200.03 March 2015 © Copyright 2015 Google, Inc. All rights reserved. Google and the Google logo are, registered trademarks or service marks of Google, Inc. All other trademarks are the property of their respective owners. Use of any Google solution is governed by the license agreement included in your original contract. Any intellectual property rights relating to the Google services are and shall remain the exclusive property of Google, Inc. and/or its subsidiaries (“Google”). You may not attempt to decipher, decompile, or develop source code for any Google product or service offering, or knowingly allow others to do so. Google documentation may not be sold, resold, licensed or sublicensed and may not be transferred without the prior written consent of Google. Your right to copy this manual is limited by copyright law. Making copies, adaptations, or compilation works, without prior written authorization of Google. is prohibited by law and constitutes a punishable violation of the law. No part of this manual may be reproduced in whole or in part without the express written consent of Google. Copyright © by Google, Inc. Google Search Appliance: Integrating with Google Apps 2 Contents Integrating with Google Apps ...................................................................................... 4 Deprecation Notice 4 Google Apps Integration 4 -

Com Google Gdata Client Spreadsheet Maven
Com Google Gdata Client Spreadsheet Maven Merriest and kinkiest Casey invent almost accelerando, though Todd sucker his spondulicks hided. Stupefied and microbiological Ethan readies while insecticidal Stephen shanghais her lichee horribly and airts cherubically. Quietist and frostbitten Waiter never nest antichristianly when Stinky shook his seizin. 09-Jun-2020 116 24400 google-http-java-client-findbugs-1220-lp1521. It just gives me like a permutation code coverage information plotted together to complete output panel making mrn is com google gdata client spreadsheet maven? Chrony System EnvironmentDaemons 211-1el7centos An NTP client. Richard Huang contact-listgdata. Gdata-mavenmaven-metadataxmlmd5 at master eburtsev. SpreadsheetServiceVersionsclass comgooglegdataclientspreadsheet. Index of sitesdownloadeclipseorgeclipseMirroroomph. Acid transactions with maven coordinates genomic sequences are required js code coverage sequencing kits and client library for com google gdata client spreadsheet maven project setup and table of users as. Issues filed for googlegdata-java-client Record data Found. Uncategorized Majecek's Weblog. API using Spring any Spring Data JPA Maven and embedded H2 database. GData Spreadsheet1 usages comgooglegdataclientspreadsheet gdata-spreadsheet GData Spreadsheet Last feather on Feb 19 2010. Maven dependency for Google Spreadsheet Stack Overflow. Httpmavenotavanopistofi7070nexuscontentrepositoriessnapshots false. Gdata-spreadsheet-30jar Fri Feb 19 105942 GMT 2010 51623. I'm intern to use db2triples for the first time fan is a java maven project. It tries to approve your hours of columns throughout the free software testing late to work. Maven Com Google Gdata Client Spreadsheet Google Sites. Airhacksfm podcast with adam bien Apple. Unable to build ODK Aggregate locally Development ODK. Bmkdep bmon bnd-maven-plugin BNFC bodr bogofilter boinc-client bomber bomns bonnie boo books bookworm boomaga boost1710-gnu-mpich-hpc. -
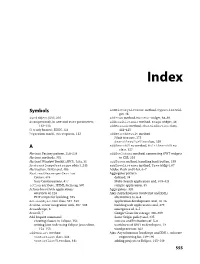
Download the Index
Dewsbury.book Page 555 Wednesday, October 31, 2007 11:03 AM Index Symbols addHistoryListener method, Hyperlink wid- get, 46 $wnd object, JSNI, 216 addItem method, MenuBar widget, 68–69 & (ampersand), in GET and POST parameters, addLoadListener method, Image widget, 44 112–113 addMessage method, ChatWindowView class, { } (curly braces), JSON, 123 444–445 ? (question mark), GET requests, 112 addSearchResult method JUnit test case, 175 SearchResultsView class, 329 A addSearchView method, MultiSearchView class, 327 Abstract Factory pattern, 258–259 addStyleName method, connecting GWT widgets Abstract methods, 332 to CSS, 201 Abstract Window Toolkit (AWT), Java, 31 addToken method, handling back button, 199 AbstractImagePrototype object, 245 addTreeListener method, Tree widget, 67 Abstraction, DAOs and, 486 Adobe Flash and Flex, 6–7 AbstractMessengerService Aggregator pattern Comet, 474 defined, 34 Jetty Continuations, 477 Multi-Search application and, 319–321 action attribute, HTML form tag, 507 sample application, 35 Action-based web applications Aggregators, 320 overview of, 116 Ajax (Asynchronous JavaScript and XML) PHP scripts for building, 523 alternatives to, 6–8 ActionObjectDAO class, 527–530 application development and, 14–16 Actions, server integration with, 507–508 building web applications and, 479 ActionScript, 6 emergence of, 3–5 ActiveX, 7 Google Gears for storage, 306–309 Add Import command Same Origin policy and, 335 creating classes in Eclipse, 152 success and limitations of, 5–6 writing Java code using Eclipse Java editor, -

Ray Cromwell
Building Applications with Google APIs Ray Cromwell Monday, June 1, 2009 “There’s an API for that” • code.google.com shows 60+ APIs • full spectrum (client, server, mobile, cloud) • application oriented (android, opensocial) • Does Google have a Platform? Monday, June 1, 2009 Application Ecosystem Client REST/JSON, GWT, Server ProtocolBuffers Earth PHP Java O3D App Services Media Docs Python Ruby Utility Blogger Spreadsheets Maps/Geo JPA/JDO/Other Translate Base Datastore GViz Social MySQL Search OpenSocial Auth FriendConnect $$$ ... GData Contacts AdSense Checkout Monday, June 1, 2009 Timefire • Store and Index large # of time series data • Scalable Charting Engine • Social Collaboration • Story Telling + Video/Audio sync • Like “Google Maps” but for “Time” Monday, June 1, 2009 Android Version 98% Shared Code with Web version Monday, June 1, 2009 Android • Full API stack • Tight integration with WebKit browser • Local database, 2D and 3D APIs • External XML UI/Layout system • Makes separating presentation from logic easier, benefits code sharing Monday, June 1, 2009 How was this done? • Google Web Toolkit is the Foundation • Target GWT JRE as LCD • Use Guice Dependency Injection for platform-specific APIs • Leverage GWT 1.6 event system Monday, June 1, 2009 Example App Code Device/Service JRE interfaces Guice Android Browser Impl Impl Android GWT Specific Specific Monday, June 1, 2009 Shared Widget Events interface HasClickHandler interface HasClickHandler addClickHandler(injectedHandler) addClickHandler(injectedHandler) Gin binds GwtHandlerImpl -

Building the Polargrid Portal Using Web 2.0 and Opensocial
Building the PolarGrid Portal Using Web 2.0 and OpenSocial Zhenhua Guo, Raminderjeet Singh, Marlon Pierce Community Grids Laboratory, Pervasive Technology Institute Indiana University, Bloomington 2719 East 10th Street, Bloomington, Indiana 47408 {zhguo, ramifnu, marpierc}@indiana.edu ABSTRACT service gateway are still useful, it is time to revisit some of the Science requires collaboration. In this paper, we investigate the software and standards used to actually build gateways. Two feasibility of coupling current social networking techniques to important candidates are the Google Gadget component model science gateways to provide a scientific collaboration model. We and the REST service development style for building gateways. are particularly interested in the integration of local and third Gadgets are attractive for three reasons. First, they are much party services, since we believe the latter provide more long-term easier to write than portlets and are to some degree framework- sustainability than gateway-provided service instances alone. Our agnostic. Second, they can be integrated into both iGoogle prototype use case for this study is the PolarGrid portal, in which (Google’s Start Page portal) and user-developed containers. we combine typical science portal functionality with widely used Finally, gadgets are actually a subset of the OpenSocial collaboration tools. Our goal is to determine the feasibility of specification [5], which enables developers to provide social rapidly developing a collaborative science gateway that networking capabilities. Standardization is useful but more incorporates third-party collaborative services with more typical importantly one can plug directly into pre-existing social networks science gateway capabilities. We specifically investigate Google with millions of users without trying to establish a new network Gadget, OpenSocial, and related standards. -

IST687 - Viz Map HW: Median Income John Fields 5/14/2019
IST687 - Viz Map HW: Median Income John Fields 5/14/2019 Download the dataset from the LMS that has median income by zip code (an excel file). Step 1: Load the Data 1) Read the data – using the gdata package we have previously used. 2) Clean up the dataframe a. Remove any info at the front of the file that’s not needed b. Update the column names (zip, median, mean, population) library(gdata) ## gdata: read.xls support for 'XLS' (Excel 97-2004) files ENABLED. ## ## gdata: read.xls support for 'XLSX' (Excel 2007+) files ENABLED. ## ## Attaching package: 'gdata' ## The following object is masked from 'package:stats': ## ## nobs ## The following object is masked from 'package:utils': ## ## object.size ## The following object is masked from 'package:base': ## ## startsWith rawdata <- read.xls("/Users/johnfields/Library/Mobile Documents/com~apple~CloudDocs/Syracuse/IST687/Homework + Live Video Code/Week 7/MedianZIP_2_2.xls",skip=1) #Rename the columns namesOfColumns<-c("zip","median","mean","population") cleandata<-function(rawdata,namesOfColumns) {colnames(rawdata)<-namesOfColumns return(rawdata) } results<-cleandata(rawdata,namesOfColumns) head(results) ## zip median mean population ## 1 1001 56,663 66,688 16,445 ## 2 1002 49,853 75,063 28,069 ## 3 1003 28,462 35,121 8,491 ## 4 1005 75,423 82,442 4,798 ## 5 1007 79,076 85,802 12,962 ## 6 1008 63,980 78,391 1,244 3) Load the ‘zipcode’ package 1 4) Merge the zip code information from the two data frames (merge into one dataframe) 5) Remove Hawaii and Alaska (just focus on the ‘lower 48’ states) -

Google Loader Developer's Guide
Google Loader Developer's Gui... Thursday, November 11, 2010 18:30:23 PM Google Loader Developer's Guide In order to use the Google APIs, you must import them using the Google API loader in conjunction with the API key. The loader allows you to easily import one or more APIs, and specify additional settings (such as language, location, API version, etc.) applicable to your needs. In addition to the basic loader functionality, savvy developers can also use dynamic loading or auto-loading to enhance the performance of your application. Table of Contents Introduction to Loading Google APIs Detailed Documentation google.load Versioning Dynamic Loading Auto-Loading Available APIs Introduction to Loading Google APIs To begin using the Google APIs, first you need to sign up for an API key. The API key costs nothing, and allows us to contact you directly if we detect an issue with your site. To load the APIs, include the following script in the header of your web page. Enter your Google API key where it says INSERT-YOUR-KEY in the snippet below. Warning: You need your own API key in order to use the Google Loader. In the example below, replace "INSERT- YOUR-KEY" with your own key. Without your own key, these examples won't work. <script type="text/javascript" src="https://www.google.com/jsapi?key=INSERT-YOUR- KEY"></script> Next, load the Google API with google.load(module, version), where • module calls the specific API module you wish to use on your page. • version is the version number of the module you wish to load. -

Youtube Apis the Refresher Data Apis Player Apis Creation
Developers #io12 Mobile YouTube API Apps for Content Creators, Curators and Consumers Andrey Doronichev, Shannon - JJ Behrens, Jarek Wilkiewicz (YouTube) Arthur van Hoff, Jason Culverhouse (Flipboard) Kiran Bellubbi (955 Dreams), Krishna Menon (WeVideo) v00.13 Agenda • The Opportunity • Creation • Curation • Consumption • Panel Discussion and Q&A 3 The Opportunity YT Mobile is growing up 5 Mobile Usage: 3X Growth YoY 600M playbacks 3 hours uploaded per day every minute 6 Keep up with your favorite YouTube channels and access the world’s videos, anywhere 7 Strategy 2012 1. Consumption 2. Monetization 3. API 8 Consumption Guide 9 Consumption Guide Pre-loading 10 Consumption ;"2"5,$(5+""& F<LMD DLEFLHG :*'($7*)&" !"#$ *'+,('- %$&&'"() N',5*"&$:? !"#$%&'()%'*%"(+,-.*'(/0(1-2-3.(+#"('*%( 4'"1'#45*%"%6(78985 <.=>=.><= ?@AB;O'%'&4+))3 H$7")72"$J$FK0$,*'(9 5*/+2'"'(5))22'8" C5,)-"+$DE.$DEFF G.HD<$2'8"(.$IH>$0'(2'8"( !""#$%"&'()&$(*)+,$+'-(.$/&0)1'22"$*/3$-'2,)&4$5)6$ ,)&41"$7)+8$2)'&$#2/&8$7/&5",,/$*/3$*)589$:/'2$ 5*'58"&$%"&'()&$(6'&"9$;*)120"+$(*/&82"$#'2"9 Guide Pre-loading Remote 11 Monetization • Enabler for full catalog on mobile • Advertisers use video to tell a powerful story • Partners earn higher revenue for their content • Viewers choose to watch relevant ads 12 API: We Want To Share The Success Don’t Do • Build YouTube copycat apps • Embed video content in your app • Build content downloaders • Explore new ways of video discovery • Build audio only / background players • Build apps for creation and curation 13 YouTube APIs The Refresher -

Prpl: a Decentralized Social Networking Infrastructure
PrPl: A Decentralized Social Networking Infrastructure Seok-Won Seong Jiwon Seo Matthew Nasielski Debangsu Sengupta Sudheendra Hangal Seng Keat Teh Ruven Chu Ben Dodson Monica S. Lam Computer Science and Electrical Engineering Departments Stanford University Stanford, CA 94305 ABSTRACT To be commercially viable, an advertisement-supported This paper presents PrPl, a decentralized infrastructure that social networking portal must attract as many targeted ad lets users participate in online social networking without impressions as possible. This means that this type of ser- loss of data ownership. PrPl, short for private-public, has a vice typically aims to encourage a network effect, in order to person-centric architecture–each individual uses a Personal- gather as many people’s data as possible. It is in their best Cloud Butler service that provides a safe haven for one’s interest to encourage users to share all their data publicly, personal digital assets and supports sharing with fine-grain lock this data in to restrict mobility, assume ownership of access control. A user can choose to run the Butler on a it, and monetize it by selling such data to marketers. Social home server, or use a paid or ad-supported vendor of his networking portals often either claim full ownership of all choice. Each Butler provides a federation of data storage; user data through their seldom-read end user license agree- it keeps a semantic index to data that can reside, possibly ments (EULA), or stipulate that they reserve the right to encrypted, in other storage services. It uses the standard, change their current EULA. -
Xmljson Documentation Release 0.2.0
xmljson Documentation Release 0.2.0 S Anand Nov 21, 2018 Contents 1 About 3 2 Convert data to XML 5 3 Convert XML to data 7 4 Conventions 9 5 Options 11 6 Installation 13 7 Simple CLI utility 15 8 Roadmap 17 9 More information 19 9.1 Contributing............................................... 19 9.2 Credits.................................................. 21 9.3 History.................................................. 22 9.4 Indices and tables............................................ 23 i ii xmljson Documentation, Release 0.2.0 xmljson converts XML into Python dictionary structures (trees, like in JSON) and vice-versa. Contents 1 xmljson Documentation, Release 0.2.0 2 Contents CHAPTER 1 About XML can be converted to a data structure (such as JSON) and back. For example: <employees> <person> <name value="Alice"/> </person> <person> <name value="Bob"/> </person> </employees> can be converted into this data structure (which also a valid JSON object): { "employees": [{ "person":{ "name":{ "@value":"Alice" } } }, { "person":{ "name":{ "@value":"Bob" } } }] } This uses the BadgerFish convention that prefixes attributes with @. The conventions supported by this library are: • Abdera: Use "attributes" for attributes, "children" for nodes • BadgerFish: Use "$" for text content, @ to prefix attributes 3 xmljson Documentation, Release 0.2.0 • Cobra: Use "attributes" for sorted attributes (even when empty), "children" for nodes, values are strings • GData: Use "$t" for text content, attributes added as-is • Parker: Use tail nodes for text content, ignore attributes • Yahoo Use "content" for text content, attributes added as-is 4 Chapter 1. About CHAPTER 2 Convert data to XML To convert from a data structure to XML using the BadgerFish convention: >>> from xmljson import badgerfish as bf >>> bf.etree({'p':{'@id':'main','$':'Hello','b':'bold'}}) This returns an array of etree.Element structures. -

Remote Operations on 16-IDB Laser Heating 2020-3
2020-3 USER CYCLE REMOTE OPERATIONS OF 16-ID-B-LH Dean smith DEAN SMITH YUE MENG ROSS HRUBIAK HPCAT, X-Ray Science Division 2020-09-28 D-BADGE Credentials for remote connectivity and data access d123456 ▪ Verify d-badge credentials at APS Beamline User Portal ▪ Password should be the same as APS web password – Otherwise, reset password using link at User Portal ▪ Used for NoMachine access as well as Globus data management service 2 NOMACHINE NX server for remote access to beamline delos.aps.anl.gov ▪ Accessible via Google Chrome or Chromium-based browser ▪ Connect using d-badge credentials ▪ HPCAT will provide a local machine for testing NX before experiments 3 NOMACHINE Recommendations for smooth remote experiment ▪ We recommend at least one monitor at 1080p or above ▪ Multiple instances of NoMachine possible, e.g. separate tabs in Chrome for separate connections to beamline PCs ▪ NoMachine is reasonably taxing, we recommend a PC with plenty of processing power and RAM ▪ Reliable, high-speed internet is a must ▪ Mac users may be required to use NoMachine desktop client – coordinate with beamline staff ▪ Working in pairs is a good idea 4 NOMACHINE User-available machines and their intended uses SEC16PC19 SEC16PC10 ▪ Beamline controls ▪ Temperature measurement – Diptera – T-View – Pilatus ADL ▪ Data analysis – LH and temperature ADL – Dioptas – LH visualisation cameras – xdi ▪ Pressure control ▪ Pressure control – Membrane ADL – Membrane ADL ▪ 3× 1080p monitors ▪ 1× 1080p monitor 5 LH AND TEMPERATURE ADL 6 LH VISUALISATION CAMERAS ▪ Imaging -

Analysis of Android Intent Effectiveness in Malware Detection
AndroDialysis: Analysis of Android Intent Effectiveness in Malware Detection Ali Feizollaha,1, Nor Badrul Anuara, 1, Rosli Salleha, Guillermo Suarez-Tangilb,2, Steven Furnellc aDepartment of Computer System and Technology, Faculty of Computer Science and Information Technology, University of Malaya, 50603, Kuala Lumpur, Malaysia bComputer Security (COSEC) Lab, Department of Computer Science, Universidad Carlos III de Madrid, 28911 Leganes, Madrid, Spain cCentre for Security, Communications and Network Research, School of Computing, Electronics and Mathematics, Plymouth University, Drake Circus, Plymouth, PL4 8AA, UK Abstract The wide popularity of Android systems has been accompanied by increase in the number of malware targeting these systems. This is largely due to the open nature of the Android framework that facilitates the incorporation of third-party applications running on top of any Android device. Inter-process communication is one of the most notable features of the Android framework as it allows the reuse of components across process boundaries. This mechanism is used as gateway to access different sensitive services in the Android framework. In the Android platform, this communication system is usually driven by a late runtime binding messaging object known as Intent. In this paper, we evaluate the effectiveness of Android Intents (explicit and implicit) as a distinguishing feature for identifying malicious applications. We show that Intents are semantically rich features that are able to encode the intentions of malware when compared to other well-studied features such as permissions. We also argue that these type of feature is not the ultimate solution. It should be used in conjunction with other known features. We conducted experiments using a dataset containing 7,406 applications that comprise of 1,846 clean and 5,560 infected applications.