The 128-Bit Blockcipher CLEFIA Design Rationale
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Data Encryption Standard (DES) – History
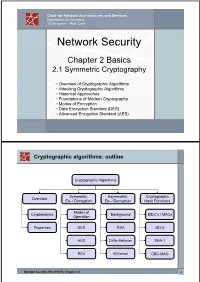
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -

Zero Correlation Linear Cryptanalysis on LEA Family Ciphers
Journal of Communications Vol. 11, No. 7, July 2016 Zero Correlation Linear Cryptanalysis on LEA Family Ciphers Kai Zhang, Jie Guan, and Bin Hu Information Science and Technology Institute, Zhengzhou 450000, China Email: [email protected]; [email protected]; [email protected] Abstract—In recent two years, zero correlation linear Zero correlation linear cryptanalysis was firstly cryptanalysis has shown its great potential in cryptanalysis and proposed by Andrey Bogdanov and Vicent Rijmen in it has proven to be effective against massive ciphers. LEA is a 2011 [2], [3]. Generally speaking, this cryptanalytic block cipher proposed by Deukjo Hong, who is the designer of method can be concluded as “use linear approximation of an ISO standard block cipher - HIGHT. This paper evaluates the probability 1/2 to eliminate the wrong key candidates”. security level on LEA family ciphers against zero correlation linear cryptanalysis. Firstly, we identify some 9-round zero However, in this basic model of zero correlation linear correlation linear hulls for LEA. Accordingly, we propose a cryptanalysis, the data complexity is about half of the full distinguishing attack on all variants of 9-round LEA family code book. The high data complexity greatly limits the ciphers. Then we propose the first zero correlation linear application of this new method. In FSE 2012, multiple cryptanalysis on 13-round LEA-192 and 14-round LEA-256. zero correlation linear cryptanalysis [4] was proposed For 13-round LEA-192, we propose a key recovery attack with which use multiple zero correlation linear approximations time complexity of 2131.30 13-round LEA encryptions, data to reduce the data complexity. -

Block Ciphers
Block Ciphers Chester Rebeiro IIT Madras CR STINSON : chapters 3 Block Cipher KE KD untrusted communication link Alice E D Bob #%AR3Xf34^$ “Attack at Dawn!!” message encryption (ciphertext) decryption “Attack at Dawn!!” Encryption key is the same as the decryption key (KE = K D) CR 2 Block Cipher : Encryption Key Length Secret Key Plaintext Ciphertext Block Cipher (Encryption) Block Length • A block cipher encryption algorithm encrypts n bits of plaintext at a time • May need to pad the plaintext if necessary • y = ek(x) CR 3 Block Cipher : Decryption Key Length Secret Key Ciphertext Plaintext Block Cipher (Decryption) Block Length • A block cipher decryption algorithm recovers the plaintext from the ciphertext. • x = dk(y) CR 4 Inside the Block Cipher PlaintextBlock (an iterative cipher) Key Whitening Round 1 key1 Round 2 key2 Round 3 key3 Round n keyn Ciphertext Block • Each round has the same endomorphic cryptosystem, which takes a key and produces an intermediate ouput • Size of the key is huge… much larger than the block size. CR 5 Inside the Block Cipher (the key schedule) PlaintextBlock Secret Key Key Whitening Round 1 Round Key 1 Round 2 Round Key 2 Round 3 Round Key 3 Key Expansion Expansion Key Key Round n Round Key n Ciphertext Block • A single secret key of fixed size used to generate ‘round keys’ for each round CR 6 Inside the Round Function Round Input • Add Round key : Add Round Key Mixing operation between the round input and the round key. typically, an ex-or operation Confusion Layer • Confusion layer : Makes the relationship between round Diffusion Layer input and output complex. -

On the Feistel Counterpart of the Boomerang Connectivity Table Introduction and Analysis of the FBCT
IACR Transactions on Symmetric Cryptology ISSN 2519-173X, Vol. 2020, No. 1, pp. 331–362. DOI:10.13154/tosc.v2020.i1.331-362 On the Feistel Counterpart of the Boomerang Connectivity Table Introduction and Analysis of the FBCT Hamid Boukerrou, Paul Huynh, Virginie Lallemand, Bimal Mandal and Marine Minier Université de Lorraine, CNRS, Inria, LORIA, F-54000 Nancy, France [email protected] Abstract. At Eurocrypt 2018, Cid et al. introduced the Boomerang Connectivity Table (BCT), a tool to compute the probability of the middle round of a boomerang distinguisher from the description of the cipher’s Sbox(es). Their new table and the following works led to a refined understanding of boomerangs, and resulted in a series of improved attacks. Still, these works only addressed the case of Substitution Permutation Networks, and completely left out the case of ciphers following a Feistel construction. In this article, we address this lack by introducing the FBCT, the Feistel counterpart of the BCT. We show that the coefficient at row ∆i, ∇o corresponds to the number of times the second order derivative at points (∆i, ∇o) cancels out. We explore the properties of the FBCT and compare it to what is known on the BCT. Taking matters further, we show how to compute the probability of a boomerang switch over multiple rounds with a generic formula. Keywords: Cryptanalysis · Feistel cipher · Boomerang attack · Boomerang switch 1 Introduction Boomerang attacks date back to 1999, when David Wagner introduced them at FSE to break COCONUT98 [Wag99]. When presented, this variant of differential attacks [BS91] shook up the conventional thinking that consisted in believing that a cipher with only small probability differentials is secure. -
Symmetric Encryption: AES
Symmetric Encryption: AES Yan Huang Credits: David Evans (UVA) Advanced Encryption Standard ▪ 1997: NIST initiates program to choose Advanced Encryption Standard to replace DES ▪ Why not just use 3DES? 2 AES Process ▪ Open Design • DES: design criteria for S-boxes kept secret ▪ Many good choices • DES: only one acceptable algorithm ▪ Public cryptanalysis efforts before choice • Heavy involvements of academic community, leading public cryptographers ▪ Conservative (but “quick”): 4 year process 3 AES Requirements ▪ Secure for next 50-100 years ▪ Royalty free ▪ Performance: faster than 3DES ▪ Support 128, 192 and 256 bit keys • Brute force search of 2128 keys at 1 Trillion keys/ second would take 1019 years (109 * age of universe) 4 AES Round 1 ▪ 15 submissions accepted ▪ Weak ciphers quickly eliminated • Magenta broken at conference! ▪ 5 finalists selected: • MARS (IBM) • RC6 (Rivest, et. al.) • Rijndael (Belgian cryptographers) • Serpent (Anderson, Biham, Knudsen) • Twofish (Schneier, et. al.) 5 AES Evaluation Criteria 1. Security Most important, but hardest to measure Resistance to cryptanalysis, randomness of output 2. Cost and Implementation Characteristics Licensing, Computational, Memory Flexibility (different key/block sizes), hardware implementation 6 AES Criteria Tradeoffs ▪ Security v. Performance • How do you measure security? ▪ Simplicity v. Complexity • Need complexity for confusion • Need simplicity to be able to analyze and implement efficiently 7 Breaking a Cipher ▪ Intuitive Impression • Attacker can decrypt secret messages • Reasonable amount of work, actual amount of ciphertext ▪ “Academic” Ideology • Attacker can determine something about the message • Given unlimited number of chosen plaintext-ciphertext pairs • Can perform a very large number of computations, up to, but not including, 2n, where n is the key size in bits (i.e. -

Non-Monopolizable Caches: Low-Complexity Mitigation of Cache Side Channel Attacks
A Non-Monopolizable Caches: Low-Complexity Mitigation of Cache Side Channel Attacks Leonid Domnitser, State University of New York at Binghamton Aamer Jaleel, Intel Corporation, VSSAD, Hudson, MA Jason Loew, Nael Abu-Ghazaleh and Dmitry Ponomarev, State University of New York at Binghamton We propose a flexibly-partitioned cache design that either drastically weakens or completely eliminates cache-based side channel attacks. The proposed Non-Monopolizable (NoMo) cache dynamically reserves cache lines for active threads and prevents other co-executing threads from evicting reserved lines. Unreserved lines remain available for dynamic sharing among threads. NoMo requires only simple modifications to the cache replacement logic, making it straightforward to adopt. It requires no software support enabling it to automatically protect pre-existing binaries. NoMo results in performance degradation of about 1% on average. We demonstrate that NoMo can provide strong security guarantees for the AES and Blowfish encryption algorithms. Categories and Subject Descriptors: C.1.0 [Computer Systems Organization]: Processor Architectures General Terms: Design, Security, Performance Additional Key Words and Phrases: Side-Channel Attacks, Shared Caches, Secure Architectures 1. INTRODUCTION In recent years, security has emerged as a key design consideration in computing and commu- nication systems. Security solutions center around the use of cryptographic algorithms, such as symmetric ciphers, public-key ciphers, and hash functions. The strength of modern cryptography makes it infeasible for the attackers to uncover the secret keys using brute-force trials, differen- tial analysis [E.Biham and Shamir 1991] or linear cryptanalysis [Matsui 1994]. Instead, almost all known attacks today exploit weaknesses in the physical implementation of the system performing the encryption, rather than exploiting the mathematical properties of the cryptographic algorithms themselves. -

Low Probability Differentials and the Cryptanalysis of Full-Round
Low Probability Differentials and the Cryptanalysis of Full-Round CLEFIA-128 Sareh Emami2, San Ling1, Ivica Nikoli´c1?, Josef Pieprzyk3 and Huaxiong Wang1 1 Nanyang Technological University, Singapore 2 Macquarie University, Australia 3 Queensland University of Technology, Australia Abstract. So far, low probability differentials for the key schedule of block ciphers have been used as a straightforward proof of security against related-key differential analysis. To achieve resistance, it is believed that for cipher with k-bit key it suffices the upper bound on the probabil- ity to be 2−k. Surprisingly, we show that this reasonable assumption is incorrect, and the probability should be (much) lower than 2−k. Our counter example is a related-key differential analysis of the well estab- lished block cipher CLEFIA-128. We show that although the key sched- ule of CLEFIA-128 prevents differentials with a probability higher than 2−128, the linear part of the key schedule that produces the round keys, and the Feistel structure of the cipher, allow to exploit particularly cho- sen differentials with a probability as low as 2−128. CLEFIA-128 has 214 such differentials, which translate to 214 pairs of weak keys. The prob- ability of each differential is too low, but the weak keys have a special structure which allows with a divide-and-conquer approach to gain an advantage of 27 over generic analysis. We exploit the advantage and give a membership test for the weak-key class and provide analysis of the hashing modes. The proposed analysis has been tested with computer experiments on small-scale variants of CLEFIA-128. -

Optimization of Core Components of Block Ciphers Baptiste Lambin
Optimization of core components of block ciphers Baptiste Lambin To cite this version: Baptiste Lambin. Optimization of core components of block ciphers. Cryptography and Security [cs.CR]. Université Rennes 1, 2019. English. NNT : 2019REN1S036. tel-02380098 HAL Id: tel-02380098 https://tel.archives-ouvertes.fr/tel-02380098 Submitted on 26 Nov 2019 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. THÈSE DE DOCTORAT DE L’UNIVERSITE DE RENNES 1 COMUE UNIVERSITE BRETAGNE LOIRE Ecole Doctorale N°601 Mathématique et Sciences et Technologies de l’Information et de la Communication Spécialité : Informatique Par Baptiste LAMBIN Optimization of Core Components of Block Ciphers Thèse présentée et soutenue à RENNES, le 22/10/2019 Unité de recherche : IRISA Rapporteurs avant soutenance : Marine Minier, Professeur, LORIA, Université de Lorraine Jacques Patarin, Professeur, PRiSM, Université de Versailles Composition du jury : Examinateurs : Marine Minier, Professeur, LORIA, Université de Lorraine Jacques Patarin, Professeur, PRiSM, Université de Versailles Jean-Louis Lanet, INRIA Rennes Virginie Lallemand, Chargée de Recherche, LORIA, CNRS Jérémy Jean, ANSSI Dir. de thèse : Pierre-Alain Fouque, IRISA, Université de Rennes 1 Co-dir. de thèse : Patrick Derbez, IRISA, Université de Rennes 1 Remerciements Je tiens à remercier en premier lieu mes directeurs de thèse, Pierre-Alain et Patrick. -

Performance Evaluation of Newly Proposed Lightweight Cipher, BRIGHT
Received: January 22, 2019 71 Performance Evaluation of Newly Proposed Lightweight Cipher, BRIGHT Deepti Sehrawat1* Nasib Singh Gill1 1Department of Computer Science & Applications, Maharshi Dayanand University, Rohtak, Haryana, India * Corresponding author’s Email: [email protected] Abstract: Lightweight security algorithms are tailored for resource-constrained environment. To improve the efficiency of an algorithm, usually, a tradeoff is involved in lightweight cryptography in terms of its memory requirements and speed. By adopting several performance enhancement techniques, a security framework for IoT enabled applications is presented in this paper. Proposed BRIGHT family of ciphers is comparably better than existing lightweight ciphers and support a range of block and key sizes for constraint environment. It enables users to match their security needs with application requirements by supporting a range of cryptographic solutions. The BRIGHT family of ciphers is a software-oriented design. The performance of BRIGHT family of lightweight ciphers is evaluated on different parameters. All versions of BRIGHT family ciphers fulfill Strict Avalanche Criteria, key sensitivity test, and randomness test. BRIGHT family ciphers show better performance in terms of memory requirements, cost and speed as compared to existing lightweight ciphers. Keywords: Performance evaluation, BRIGHT, Cryptographic solutions, Lightweight block cipher, ARX, GFN, Feistel block ciphers. devices information security is evidently necessary 1. Introduction [3]. To provide high security and privacy, cryptographic solutions must be used. However, due In IoT field, various resource constraints devices to very low available energy, the limited size of ROM communicate in the network using RFID (Radio and RAM consumption and high-security demand in Frequency Identification Devices) which is a fast- a resource-constrained environment, lightweight growing technology that allows automated cryptographic security solutions are required [4]. -

Network Security H B ACHARYA
Network Security H B ACHARYA NETWORK SECURITY Day 2 NETWORK SECURITY Encryption Schemes NETWORK SECURITY Basic Problem ----- ----- ? Given: both parties already know the same secret How is this achieved in practice? Goal: send a message confidentially Any communication system that aims to guarantee confidentiality must solve this problem NETWORK SECURITY slide 4 One-Time Pad (Vernam Cipher) ----- 10111101… ----- = 10111101… 10001111… = 00110010… 00110010… = Key is a random bit sequence as long as the plaintext Decrypt by bitwise XOR of ciphertext and key: ciphertext key = (plaintext key) key = Encrypt by bitwise XOR of plaintext (key key) = plaintext and key: plaintext ciphertext = plaintext key Cipher achieves perfect secrecy if and only if there are as many possible keys as possible plaintexts, and every key is equally likely (Claude Shannon, 1949) NETWORK SECURITY slide 5 Advantages of One-Time Pad Easy to compute ◦ Encryption and decryption are the same operation ◦ Bitwise XOR is very cheap to compute As secure as theoretically possible ◦ Given a ciphertext, all plaintexts are equally likely, regardless of attacker’s computational resources ◦ …if and only if the key sequence is truly random ◦ True randomness is expensive to obtain in large quantities ◦ …if and only if each key is as long as the plaintext ◦ But how do the sender and the receiver communicate the key to each other? Where do they store the key? NETWORK SECURITY slide 6 Problems with One-Time Pad Key must be as long as the plaintext ◦ Impractical in most realistic -

Applied Cryptography and Data Security
Lecture Notes APPLIED CRYPTOGRAPHY AND DATA SECURITY (version 2.5 | January 2005) Prof. Christof Paar Chair for Communication Security Department of Electrical Engineering and Information Sciences Ruhr-Universit¨at Bochum Germany www.crypto.rub.de Table of Contents 1 Introduction to Cryptography and Data Security 2 1.1 Literature Recommendations . 3 1.2 Overview on the Field of Cryptology . 4 1.3 Symmetric Cryptosystems . 5 1.3.1 Basics . 5 1.3.2 A Motivating Example: The Substitution Cipher . 7 1.3.3 How Many Key Bits Are Enough? . 9 1.4 Cryptanalysis . 10 1.4.1 Rules of the Game . 10 1.4.2 Attacks against Crypto Algorithms . 11 1.5 Some Number Theory . 12 1.6 Simple Blockciphers . 17 1.6.1 Shift Cipher . 18 1.6.2 Affine Cipher . 20 1.7 Lessons Learned | Introduction . 21 2 Stream Ciphers 22 2.1 Introduction . 22 2.2 Some Remarks on Random Number Generators . 26 2.3 General Thoughts on Security, One-Time Pad and Practical Stream Ciphers 27 2.4 Synchronous Stream Ciphers . 31 i 2.4.1 Linear Feedback Shift Registers (LFSR) . 31 2.4.2 Clock Controlled Shift Registers . 34 2.5 Known Plaintext Attack Against Single LFSRs . 35 2.6 Lessons Learned | Stream Ciphers . 37 3 Data Encryption Standard (DES) 38 3.1 Confusion and Diffusion . 38 3.2 Introduction to DES . 40 3.2.1 Overview . 41 3.2.2 Permutations . 42 3.2.3 Core Iteration / f-Function . 43 3.2.4 Key Schedule . 45 3.3 Decryption . 47 3.4 Implementation . 50 3.4.1 Hardware . -

Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1
International Journal of Grid and Distributed Computing Vol. 10, No. 11 (2017), pp.79-98 http://dx.doi.org/10.14257/ijgdc.2017.10.11.08 Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1 Rahul Saha1, G. Geetha2, Gulshan Kumar3 and Hye-Jim Kim4 1,3School of Computer Science and Engineering, Lovely Professional University, Punjab, India 2Division of Research and Development, Lovely Professional University, Punjab, India 4Business Administration Research Institute, Sungshin W. University, 2 Bomun-ro 34da gil, Seongbuk-gu, Seoul, Republic of Korea Abstract Cryptography has always been a core component of security domain. Different security services such as confidentiality, integrity, availability, authentication, non-repudiation and access control, are provided by a number of cryptographic algorithms including block ciphers, stream ciphers and hash functions. Though the algorithms are public and cryptographic strength depends on the usage of the keys, the ciphertext analysis using different functions and operations used in the algorithms can lead to the path of revealing a key completely or partially. It is hard to find any survey till date which identifies different operations and functions used in cryptography. In this paper, we have categorized our survey of cryptographic functions and operations in the algorithms in three categories: block ciphers, stream ciphers and cryptanalysis attacks which are executable in different parts of the algorithms. This survey will help the budding researchers in the society of crypto for identifying different operations and functions in cryptographic algorithms. Keywords: cryptography; block; stream; cipher; plaintext; ciphertext; functions; research problems 1. Introduction Cryptography [1] in the previous time was analogous to encryption where the main task was to convert the readable message to an unreadable format.