Generic Attacks on Stream Ciphers
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Failures of Secret-Key Cryptography D
Failures of secret-key cryptography D. J. Bernstein University of Illinois at Chicago & Technische Universiteit Eindhoven http://xkcd.com/538/ 2011 Grigg{Gutmann: In the past 15 years \no one ever lost money to an attack on a properly designed cryptosystem (meaning one that didn't use homebrew crypto or toy keys) in the Internet or commercial worlds". 2011 Grigg{Gutmann: In the past 15 years \no one ever lost money to an attack on a properly designed cryptosystem (meaning one that didn't use homebrew crypto or toy keys) in the Internet or commercial worlds". 2002 Shamir:\Cryptography is usually bypassed. I am not aware of any major world-class security system employing cryptography in which the hackers penetrated the system by actually going through the cryptanalysis." Do these people mean that it's actually infeasible to break real-world crypto? Do these people mean that it's actually infeasible to break real-world crypto? Or do they mean that breaks are feasible but still not worthwhile for the attackers? Do these people mean that it's actually infeasible to break real-world crypto? Or do they mean that breaks are feasible but still not worthwhile for the attackers? Or are they simply wrong: real-world crypto is breakable; is in fact being broken; is one of many ongoing disaster areas in security? Do these people mean that it's actually infeasible to break real-world crypto? Or do they mean that breaks are feasible but still not worthwhile for the attackers? Or are they simply wrong: real-world crypto is breakable; is in fact being broken; is one of many ongoing disaster areas in security? Let's look at some examples. -

A Uniform Framework for Cryptanalysis of the Bluetooth E0
1 A Uniform Framework for Cryptanalysis of the Bluetooth E0 Cipher Ophir Levy and Avishai Wool School of Electrical Engineering, Tel Aviv University, Ramat Aviv 69978, ISRAEL. [email protected], [email protected] . Abstract— In this paper we analyze the E0 cipher, which “short key” attacks, that need at most 240 known is the encryption system used in the Bluetooth specification. keystream bits and are applicable in the Bluetooth We suggest a uniform framework for cryptanalysis of the setting; and “long key” attacks, that are applicable only E0 cipher. Our method requires 128 known bits of the if the E0 cipher is used outside the Bluetooth mode of keystream in order to recover the initial state of the LFSRs, operation. which reflects the secret key of this encryption engine. In one setting, our framework reduces to an attack of 1) Short Key Attacks: D. Bleichenbacher has shown D. Bleichenbacher. In another setting, our framework is in [1] that an attacker can guess the content of the equivalent to an attack presented by Fluhrer and Lucks. registers of the three smaller LFSRs and of the E0 − Our best attack can recover the initial state of the LFSRs combiner state registers with a probability of 2 93. Then after solving 286 boolean linear systems of equations, which the attacker can compute the the contents of the largest is roughly equivalent to the results obtained by Fluhrer and LFSR (of length 39 bit) by “reverse engineering” it Lucks. from the outputs of the other LFSRs and the combiner states. This attack requires a total of 128 bits of known I. -

Key Differentiation Attacks on Stream Ciphers
Key differentiation attacks on stream ciphers Abstract In this paper the applicability of differential cryptanalytic tool to stream ciphers is elaborated using the algebraic representation similar to early Shannon’s postulates regarding the concept of confusion. In 2007, Biham and Dunkelman [3] have formally introduced the concept of differential cryptanalysis in stream ciphers by addressing the three different scenarios of interest. Here we mainly consider the first scenario where the key difference and/or IV difference influence the internal state of the cipher (∆key, ∆IV ) → ∆S. We then show that under certain circumstances a chosen IV attack may be transformed in the key chosen attack. That is, whenever at some stage of the key/IV setup algorithm (KSA) we may identify linear relations between some subset of key and IV bits, and these key variables only appear through these linear relations, then using the differentiation of internal state variables (through chosen IV scenario of attack) we are able to eliminate the presence of corresponding key variables. The method leads to an attack whose complexity is beyond the exhaustive search, whenever the cipher admits exact algebraic description of internal state variables and the keystream computation is not complex. A successful application is especially noted in the context of stream ciphers whose keystream bits evolve relatively slow as a function of secret state bits. A modification of the attack can be applied to the TRIVIUM stream cipher [8], in this case 12 linear relations could be identified but at the same time the same 12 key variables appear in another part of state register. -

Ray Bradbury Creative Contest Literary Journal
32nd Annual Ray Bradbury Creative Contest Literary Journal 2016 Val Mayerik Val Ray Bradbury Creative Contest A contest of writing and art by the Waukegan Public Library. This year’s literary journal is edited, designed, and produced by the Waukegan Public Library. Table of Contents Elementary School Written page 1 Middle School Written page 23 High School Written page 52 Adult Written page 98 Jennifer Herrick – Designer Rose Courtney – Staff Judge Diana Wence – Staff Judge Isaac Salgado – Staff Judge Yareli Facundo – Staff Judge Elementary School Written The Haunted School Alexis J. In one wonderful day there was a school-named “Hyde Park”. One day when, a kid named Logan and his friend Mindy went to school they saw something new. Hyde Park is hotel now! Logan and Mindy Went inside to see what was going on. So they could not believe what they say. “Hyde Park is also now haunted! When Logan took one step they saw Slender Man. Then they both walk and there was a scary mask. Then mummies started coming out of the grown and zombies started coming from the grown and they were so stinky yuck! Ghost came out all over the school and all the doors were locked. Now Mindy had a plan to scare all the monsters away. She said “we should put all the monsters we saw all together. So they make Hyde Park normal again. And they live happy ever after and now it is back as normal. THE END The Haunted House Angel A. One day it was night. And it was so dark a lot of people went on a house called “dead”. -
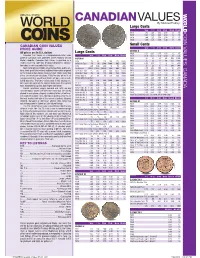
*UPDATED Canadian Values 07-04 201 7/26/2016 4:42:21 PM *UPDATED Canadian Values 07-04 202 COIN VALUES: CANADA 02 .0 .0 12
CANADIAN VALUES By Michael Findlay Large Cents VG-8 F-12 VF-20 EF-40 MS-60 MS-63R 1917 1.00 1.25 1.50 2.50 13. 45. CANADA COIN VALUES: 1918 1.00 1.25 1.50 2.50 13. 45. 1919 1.00 1.25 1.50 2.50 13. 45. 1920 1.00 1.25 1.50 3.00 18. 70. CANADIAN COIN VALUES Small Cents PRICE GUIDE VG-8 F-12 VF-20 EF-40 MS-60 MS-63R GEORGE V All prices are in U.S. dollars LargeL Cents C t 1920 0.20 0.35 0.75 1.50 12. 45. Canadian Coin Values is a comprehensive retail value VG-8 F-12 VF-20 EF-40 MS-60 MS-63R 1921 0.50 0.75 1.50 4.00 30. 250. guide of Canadian coins published online regularly at Coin VICTORIA 1922 20. 23. 28. 40. 200. 1200. World’s website. Canadian Coin Values is provided as a 1858 70. 90. 120. 200. 475. 1800. 1923 30. 33. 42. 55. 250. 2000. reader service to collectors desiring independent informa- 1858 Coin Turn NI NI 2500. 5000. BNE BNE 1924 6.00 8.00 11. 16. 120. 800. tion about a coin’s potential retail value. 1859 4.00 5.00 6.00 10. 50. 200. 1925 25. 28. 35. 45. 200. 900. Sources for pricing include actual transactions, public auc- 1859 Brass 16000. 22000. 30000. BNE BNE BNE 1926 3.50 4.50 7.00 12. 90. 650. tions, fi xed-price lists and any additional information acquired 1859 Dbl P 9 #1 225. -

Stream Ciphers (Contd.)
Stream Ciphers (contd.) Debdeep Mukhopadhyay Assistant Professor Department of Computer Science and Engineering Indian Institute of Technology Kharagpur INDIA -721302 Objectives • Non-linear feedback shift registers • Stream ciphers using LFSRs: – Non-linear combination generators – Non-linear filter generators – Clock controlled generators – Other Stream Ciphers Low Power Ajit Pal IIT Kharagpur 1 Non-linear feedback shift registers • A Feedback Shift Register (FSR) is non-singular iff for all possible initial states every output sequence of the FSR is periodic. de Bruijn Sequence An FSR with feedback function fs(jj−−12 , s ,..., s jL − ) is non-singular iff f is of the form: fs=⊕jL−−−−+ gss( j12 , j ,..., s jL 1 ) for some Boolean function g. The period of a non-singular FSR with length L is at most 2L . If the period of the output sequence for any initial state of a non-singular FSR of length L is 2L , then the FSR is called a de Bruijn FSR, and the output sequence is called a de Bruijn sequence. Low Power Ajit Pal IIT Kharagpur 2 Example f (,xxx123 , )1= ⊕⊕⊕ x 2 x 3 xx 12 t x1 x2 x3 t x1 x2 x3 0 0 0 0 4 0 1 1 1 1 0 0 5 1 0 1 2 1 1 0 6 0 1 0 3 1 1 1 3 0 0 1 Converting a maximal length LFSR to a de-Bruijn FSR Let R1 be a maximum length LFSR of length L with linear feedback function: fs(jj−−12 , s ,..., s jL − ). Then the FSR R2 with feedback function: gs(jj−−12 , s ,..., s jL − )=⊕ f sjj−−12 , s ,..., s j −L+1 is a de Bruijn FSR. -
Methods for Symmetric Key Cryptography and Cryptanalysis EWM Phd Summer School, Turku, June 2009
Methods for Symmetric Key Cryptography and Cryptanalysis EWM PhD Summer School, Turku, June 2009 Kaisa Nyberg [email protected] Department of Information and Computer Science Helsinki University of Technology and Nokia, Finland Methods for Symmetric Key Cryptography and Cryptanalysis – 1/32 This lecture is dedicated to the memory of Professor Susanne Dierolf a dear and supporting friend, a highly respected colleague, and a great European Woman in Mathematics, who passed away in May 2009 at the age of 64 in Trier, Germany. Methods for Symmetric Key Cryptography and Cryptanalysis – 2/32 Outline 1. Boolean function Linear approximation of Boolean function Related probability distribution 2. Cryptographic encryption primitives Linear approximation of block cipher Linear approximation of stream cipher 3. Cryptanalysis and attack scenarios Key information deduction on block cipher Distinguishing attack on stream cipher Initial state recovery of stream cipher 4. Conclusions Methods for Symmetric Key Cryptography and Cryptanalysis – 3/32 Boolean Functions Methods for Symmetric Key Cryptography and Cryptanalysis – 4/32 Binary vector space n Z 2 the space of n-dimensional binary vectors ¨ sum modulo 2 Given two vectors 1 n 1 n n a = ´a ; : : : ; a µ; b = ´b ; : : : ; b µ ¾ Z 2 the inner product (dot product) is defined as 1 1 n n a ¡ b = a b ¨ ¡ ¡ ¡ ¨ a b : Then a is called the linear mask of b. Methods for Symmetric Key Cryptography and Cryptanalysis – 5/32 Boolean function n f : Z 2 Z 2 Boolean function. Linear Boolean function is of the form f ´x µ = u ¡ x for some n fixed linear mask u ¾ Z 2. -

Politecnico Di Torino
POLITECNICO DI TORINO Master Degree Course in Electronic Engineering Master Degree Thesis Evaluation of Encryption Algorithm Security in Heterogeneous Platform against Differential Power Analysis Attack Supervisor: Candidate: Prof. Stefano DI CARLO Fiammetta VOLPE Student ID: 235145 A.A. 2017/2018 Summary An embedded system security can be violated at different levels of abstraction: the vulnerability is not only present from software point of view, but also the hardware can be attacked. This thesis is focused on an hardware attack at logic/microelectronic level called Differential Power Analysis (DPA), included in the larger categories of the Power Analysis (PA) and Side-Channel Anal- ysis, catalogued like a passive and non-invasive attack, since it includes the observation of the normal behaviour of the device without any physical alteration. As a consequence, this kind of attack could be extremely dangerous and it doesn’t leave any trace. A DPA attack is essentially based on the principle that the power consumption is correlated to the activity of the device during data encryption, so also to the used encryption key. Thus, using statistical analysis on a sufficiently large number of power traces, it is possible to detect the correct hypothesis for the key. Due to the improvement of FPGAs in terms of capacity and performance and the significant in- crement of the value of handled data, it is essential to do an analysis of the level of vulnerability of the device. For this reason, the MachXO2-7000 FPGA included, together with a STM32F4 CPU and a SLJ52G SECURITY CONTROLLER-SMART CARD, inside the BGA chip SEcubeTM, appositely designed for security goals, is the chosen target for this thesis. -

RC4-2S: RC4 Stream Cipher with Two State Tables
RC4-2S: RC4 Stream Cipher with Two State Tables Maytham M. Hammood, Kenji Yoshigoe and Ali M. Sagheer Abstract One of the most important symmetric cryptographic algorithms is Rivest Cipher 4 (RC4) stream cipher which can be applied to many security applications in real time security. However, RC4 cipher shows some weaknesses including a correlation problem between the public known outputs of the internal state. We propose RC4 stream cipher with two state tables (RC4-2S) as an enhancement to RC4. RC4-2S stream cipher system solves the correlation problem between the public known outputs of the internal state using permutation between state 1 (S1) and state 2 (S2). Furthermore, key generation time of the RC4-2S is faster than that of the original RC4 due to less number of operations per a key generation required by the former. The experimental results confirm that the output streams generated by the RC4-2S are more random than that generated by RC4 while requiring less time than RC4. Moreover, RC4-2S’s high resistivity protects against many attacks vulnerable to RC4 and solves several weaknesses of RC4 such as distinguishing attack. Keywords Stream cipher Á RC4 Á Pseudo-random number generator This work is based in part, upon research supported by the National Science Foundation (under Grant Nos. CNS-0855248 and EPS-0918970). Any opinions, findings and conclusions or recommendations expressed in this material are those of the author (s) and do not necessarily reflect the views of the funding agencies or those of the employers. M. M. Hammood Applied Science, University of Arkansas at Little Rock, Little Rock, USA e-mail: [email protected] K. -

(Not) to Design and Implement Post-Quantum Cryptography
SoK: How (not) to Design and Implement Post-Quantum Cryptography James Howe1 , Thomas Prest1 , and Daniel Apon2 1 PQShield, Oxford, UK. {james.howe,thomas.prest}@pqshield.com 2 National Institute of Standards and Technology, USA. [email protected] Abstract Post-quantum cryptography has known a Cambrian explo- sion in the last decade. What started as a very theoretical and mathe- matical area has now evolved into a sprawling research ˝eld, complete with side-channel resistant embedded implementations, large scale de- ployment tests and standardization e˙orts. This study systematizes the current state of knowledge on post-quantum cryptography. Compared to existing studies, we adopt a transversal point of view and center our study around three areas: (i) paradigms, (ii) implementation, (iii) deployment. Our point of view allows to cast almost all classical and post-quantum schemes into just a few paradigms. We highlight trends, common methodologies, and pitfalls to look for and recurrent challenges. 1 Introduction Since Shor's discovery of polynomial-time quantum algorithms for the factoring and discrete logarithm problems, researchers have looked at ways to manage the potential advent of large-scale quantum computers, a prospect which has become much more tangible of late. The proposed solutions are cryptographic schemes based on problems assumed to be resistant to quantum computers, such as those related to lattices or hash functions. Post-quantum cryptography (PQC) is an umbrella term that encompasses the design, implementation, and integration of these schemes. This document is a Systematization of Knowledge (SoK) on this diverse and progressive topic. We have made two editorial choices. -

Hardware Implementation of the Salsa20 and Phelix Stream Ciphers
Hardware Implementation of the Salsa20 and Phelix Stream Ciphers Junjie Yan and Howard M. Heys Electrical and Computer Engineering Memorial University of Newfoundland Email: {junjie, howard}@engr.mun.ca Abstract— In this paper, we present an analysis of the digital of battery limitations and portability, while for virtual private hardware implementation of two stream ciphers proposed for the network (VPN) applications and secure e-commerce web eSTREAM project: Salsa20 and Phelix. Both high speed and servers, demand for high-speed encryption is rapidly compact designs are examined, targeted to both field increasing. programmable (FPGA) and application specific integrated circuit When considering implementation technologies, normally, (ASIC) technologies. the ASIC approach provides better performance in density and The studied designs are specified using the VHDL hardware throughput, but an FPGA is reconfigurable and more flexible. description language, and synthesized by using Synopsys CAD In our study, several schemes are used, catering to the features tools. The throughput of the compact ASIC design for Phelix is of the target technology. 260 Mbps targeted for 0.18µ CMOS technology and the corresponding area is equivalent to about 12,400 2-input NAND 2. PHELIX gates. The throughput of Salsa20 ranges from 38 Mbps for the 2.1 Short Description of the Phelix Algorithm compact FPGA design, implemented using 194 CLB slices to 4.8 Phelix is claimed to be a high-speed stream cipher. It is Gbps for the high speed ASIC design, implemented with an area selected for both software and hardware performance equivalent to about 470,000 2-input NAND gates. evaluation by the eSTREAM project. -

Weak Keys for AEZ, and the External Key Padding Attack
Weak Keys for AEZ, and the External Key Padding Attack Bart Mennink1;2 1 Dept. Electrical Engineering, ESAT/COSIC, KU Leuven, and iMinds, Belgium [email protected] 2 Digital Security Group, Radboud University, Nijmegen, The Netherlands [email protected] Abstract. AEZ is one of the third round candidates in the CAESAR competition. We observe that the tweakable blockcipher used in AEZ suffers from structural design issues in case one of the three 128-bit sub- keys is zero. Calling these keys \weak," we show that a distinguishing attack on AEZ with weak key can be performed in at most five queries. Although the fraction of weak keys, around 3 out of every 2128, seems to be too small to violate the security claims of AEZ in general, they do reveal unexpected behavior of the scheme in certain use cases. We derive a potential scenario, the \external key padding," where a user of the authenticated encryption scheme pads the key externally before it is fed to the scheme. While for most authenticated encryption schemes this would affect the security only marginally, AEZ turns out to be com- pletely insecure in this scenario due to its weak keys. These observations open a discussion on the significance of the \robustness" stamp, and on what it encompasses. Keywords. AEZ, tweakable blockcipher, weak keys, attack, external key padding, robustness. 1 Introduction Authenticated encryption aims to offer both privacy and authenticity of data. The ongoing CAESAR competition [8] targets the development of a portfolio of new, solid, authenticated encryption schemes. It received 57 submissions, 30 candidates advanced to the second round, and recently, 16 of those advanced to the third round.