Introduction
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Vectorcast Installation Guide for Vectorcast 2021
New editions of this guide incorporate all material added or changed since the previous edition. Update packages may be used between editions. The manual printing date changes when a new edition is printed. The contents and format of this manual are subject to change without notice. Generated: 7/25/2021, 8:48 PM Rev: 33d0493 Part Number: VectorCAST Installation Guide for VectorCAST 2021 VectorCAST is a trademark of Vector Informatik, GmbH © Copyright 2021, Vector Informatik, GmbH All rights reserved. No part of the material protected by this copyright notice may be reproduced or utilized in any form or by any means, electronic or mechanical, including photocopying, recording, or by any informational storage and retrieval system, without written permission from the copyright owner. U.S. Government Restricted Rights This computer software and related documentation are provided with Restricted Rights. Use, duplication or disclosure by the Government is subject to restrictions as set forth in the governing Rights in Technical Data and Computer Software clause of DFARS 252.227-7015 (June 1995) and DFARS 227.7202-3(b). Manufacturer is Vector North America, Inc. East Greenwich RI 02818, USA. Vector Informatik reserves the right to make changes in specifications and other information contained in this document without prior notice. Contact Vector Informatik to determine whether such changes have been made. Third-Party copyright notices are contained in the file: 3rdPartyLicenses.txt, located in the VectorCAST installation directory. 2 TABLE OF -

Flexnet Server
FlexNet Server Administration Guide Copyright Copyright © 2019 CAXperts GmbH. All Rights Reserved. Including software, file formats, and audio-visual displays; may be used pursuant to applicable software licence agreement; contains confidential and proprietary information of CAXperts and/or third parties which is protected by copyright law, trade secret law, and international treaty, and may not be provided or otherwise made available without proper authorisation. Restricted Rights Legend Rights reserved under the copyright laws of the Federal Republic of Germany. Warranties and Liabilities All warranties given by CAXperts about equipment or software are set forth in your purchase contract, and nothing stated in, or implied by, this document or its contents shall be considered or deemed a modification or amendment of such warranties. CAXperts believes the information in this publication is accurate as of its publication date. The information and the software discussed in this document are subject to change without notice and are subject to applicable technical product descriptions. CAXperts is not responsible for any error that may appear in this document. The software discussed in this document is furnished under a licence and may be used or copied only in accordance with the terms of this licence. THE USER OF THE SOFTWARE IS EXPECTED TO MAKE THE FINAL EVALUATION AS TO THE USEFULNESS OF THE SOFTWARE IN HIS OWN ENVIRONMENT. Trademarks CAXperts is a registered trademark of CAXperts GmbH. Intergraph, the Intergraph logo, SmartSketch, FrameWorks, SmartPlant, INtools, MARIAN, PDS, IGDS, RIS and IntelliShip are registered trademarks of Intergraph Corporation. IGDS file formats ©1987-1994 Intergraph Corporation. Microsoft and Windows are registered trademarks of Microsoft Corporation. -

Flexnet Publisher Release Notes
FlexNet Publisher 2018 R4 (11.16.2) Release Notes December 2018 Revision 00 Enhancements ................................................................................................................................. 3 Security Updates.............................................................................................................................. 3 Dongle Updates ............................................................................................................................... 4 Platform Updates............................................................................................................................. 4 11.16.2 Updates ............................................................................................................................................4 Windows........................................................................................................................................................................................................ 4 macOS/OS X ................................................................................................................................................................................................ 4 Integrated Products and Tested Versions........................................................................................................................................ 4 11.16.1 Updates ............................................................................................................................................4 -

License Administration Guide Flexnet Publisher Licensing Toolkit 11.10.1 Legal Information
License Administration Guide FlexNet Publisher Licensing Toolkit 11.10.1 Legal Information Book Name: License Administration Guide Part Number: FNP-11101-LAG00 Product Release Date: February 2012 Copyright Notice Copyright © 2012 Flexera Software LLC. All Rights Reserved. This product contains proprietary and confidential technology, information and creative works owned by Flexera Software LLC and its licensors, if any. Any use, copying, publication, distribution, display, modification, or transmission of such technology in whole or in part in any form or by any means without the prior express written permission of Flexera Software LLC is strictly prohibited. Except where expressly provided by Flexera Software LLC in writing, possession of this technology shall not be construed to confer any license or rights under any Flexera Software LLC intellectual property rights, whether by estoppel, implication, or otherwise. All copies of the technology and related information, if allowed by Flexera Software LLC, must display this notice of copyright and ownership in full. FlexNet Publisher incorporates software developed by others and redistributed according to license agreements. Copyright notices and licenses for these external libraries are provided in a supplementary document that accompanies this one. Trademarks Flexera Software, AdminStudio, FlexEnabled, FlexLM, FlexNet, FlexNet Connect, FlexNet Manager, FlexNet Publisher, InstallAnywhere, InstallShield, InstallShield Professional, and PackageExpert are registered trademarks or trademarks -

License Activation Center Administration Quick Start
License Activation Center Administration Quick Start This Quick Start for License Activation Center (LAC) administrators takes you through a simple example to quickly learn how to: 1. Log into the administrative area of LAC. 2. Add a license generator. 3. Add a product and product features. 4. Create templates for the product. 5. Add customers. 6. Create license orders using product templates. 7. Activate a license. Logging into LAC First, log into the administrative area of LAC by going to https://license.x-formation.com. From this page, log in by entering your username and password in the login box. If the login box is asking for an activation key, you are on the end-user login page. Click the Log in as a license administrator link at the bottom of the login box to switch to the administrator login. Note: LAC does not support concurrent logins using the same user credentials. If a user logs into LAC using the same username and password as another user that is currently logged into LAC, the currently logged in user will be signed out of LAC automatically. (Users are also automatically signed out after 1 hour of idleness when using the UI or 3 hours of idleness using SOAP.) Adding a license generator You must define a license generator for each product you'll add to LAC. It's easiest to add the license generator before adding the product that will use it. Since you can use the license generator you add during this quickstart for your own LAC products, enter values that will define a real license generator for your environment. -
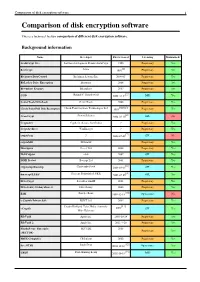
Comparison of Disk Encryption Software 1 Comparison of Disk Encryption Software
Comparison of disk encryption software 1 Comparison of disk encryption software This is a technical feature comparison of different disk encryption software. Background information Name Developer First released Licensing Maintained? ArchiCrypt Live Softwaredevelopment Remus ArchiCrypt 1998 Proprietary Yes [1] BestCrypt Jetico 1993 Proprietary Yes BitArmor DataControl BitArmor Systems Inc. 2008-05 Proprietary Yes BitLocker Drive Encryption Microsoft 2006 Proprietary Yes Bloombase Keyparc Bloombase 2007 Proprietary Yes [2] CGD Roland C. Dowdeswell 2002-10-04 BSD Yes CenterTools DriveLock CenterTools 2008 Proprietary Yes [3][4][5] Check Point Full Disk Encryption Check Point Software Technologies Ltd 1999 Proprietary Yes [6] CrossCrypt Steven Scherrer 2004-02-10 GPL No Cryptainer Cypherix (Secure-Soft India) ? Proprietary Yes CryptArchiver WinEncrypt ? Proprietary Yes [7] cryptoloop ? 2003-07-02 GPL No cryptoMill SEAhawk Proprietary Yes Discryptor Cosect Ltd. 2008 Proprietary Yes DiskCryptor ntldr 2007 GPL Yes DISK Protect Becrypt Ltd 2001 Proprietary Yes [8] cryptsetup/dmsetup Christophe Saout 2004-03-11 GPL Yes [9] dm-crypt/LUKS Clemens Fruhwirth (LUKS) 2005-02-05 GPL Yes DriveCrypt SecurStar GmbH 2001 Proprietary Yes DriveSentry GoAnywhere 2 DriveSentry 2008 Proprietary Yes [10] E4M Paul Le Roux 1998-12-18 Open source No e-Capsule Private Safe EISST Ltd. 2005 Proprietary Yes Dustin Kirkland, Tyler Hicks, (formerly [11] eCryptfs 2005 GPL Yes Mike Halcrow) FileVault Apple Inc. 2003-10-24 Proprietary Yes FileVault 2 Apple Inc. 2011-7-20 Proprietary -

Veracryptcrypt F R E E O P E N - S O U R C E O N - T H E - F L Y E N C R Y P T I O N User’S Guide
VERAVERACRYPTCRYPT F R E E O P E N - S O U R C E O N - T H E - F L Y E N C R Y P T I O N USER’S GUIDE veracrypt.codeplex.com Version Information VeraCrypt User’s Guide, version 1.19 Released by IDRIX on October 17th, 2016 Legal Notices THIS DOCUMENT IS PROVIDED "AS IS" WITHOUT WARRANTY OF ANY KIND, WHETHER EXPRESS, IMPLIED, OR STATUTORY. THE ENTIRE RISK AS TO THE QUALITY, CORRECTNESS, ACCURACY, OR COMPLETENESS OF THE CONTENT OF THIS DOCUMENT IS WITH YOU. THE CONTENT OF THIS DOCUMENT MAY BE INACCURATE, INCORRECT, INVALID, INCOMPLETE AND/OR MISLEADING. IN NO EVENT WILL ANY AUTHOR OF THE SOFTWARE OR DOCUMENTATION, OR ANY APPLICABLE COPYRIGHT OWNER, OR ANY OTHER PARTY WHO MAY COPY AND/OR (RE)DISTRIBUTE THIS SOFTWARE OR DOCUMENTATION, BE LIABLE TO YOU OR TO ANY OTHER PARTY FOR ANY DAMAGES, INCLUDING, BUT NOT LIMITED TO, ANY DIRECT, INDIRECT, GENERAL, SPECIAL, INCIDENTAL, PUNITIVE, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, CORRUPTION OR LOSS OF DATA, ANY LOSSES SUSTAINED BY YOU OR THIRD PARTIES, A FAILURE OF THIS SOFTWARE TO OPERATE WITH ANY OTHER PRODUCT, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES, OR BUSINESS INTERRUPTION), WHETHER IN CONTRACT, STRICT LIABILITY, TORT (INCLUDING, BUT NOT LIMITED TO, NEGLIGENCE) OR OTHERWISE, ARISING OUT OF THE USE, COPYING, MODIFICATION, OR (RE)DISTRIBUTION OF THIS SOFTWARE OR DOCUMENTATION (OR A PORTION THEREOF), OR INABILITY TO USE THIS SOFTWARE OR DOCUMENTATION, EVEN IF SUCH DAMAGES (OR THE POSSIBILITY OF SUCH DAMAGES) ARE/WERE PREDICTABLE OR KNOWN TO ANY (CO)AUTHOR, INTELLECTUAL-PROPERTY OWNER, OR ANY OTHER PARTY. -

Flexnet Publisher Monetize and Protect Your IP with Flexible Software Licensing—On-Premises
FlexNet Publisher Monetize and Protect Your IP with Flexible Software Licensing—On-Premises, DATASHEET SaaS, Cloud and Virtualized The software industry continues to change. Slow on-premises, SaaS, Cloud or virtualized application. “IT buyers wish to focus revenue growth, mergers and acquisitions, piracy, It enables you to monetize and protect your IP to on allocating resources virtualization, SaaS, the Cloud, and the growing realize increased revenues and experience greater more efficiently and demand for utility-based software licensing models market penetration. generating ROI, which are just a few of the forces reshaping the landscape. means negotiating the most beneficial license Cut Support Costs with Easy End-User License agreements. In this To cope with these changes, software vendors and Management environment, FlexNet intelligent device manufacturers must find ways With other licensing solutions, when customers Publisher can help to boost sales by offering customers the licensing install or move licenses, errors often occur that software vendors deliver options they want, while preventing revenue loss by frustrate end users and increase your support costs. customized licensing protecting software IP from unlicensed use. FlexNet Publisher lets you offer customers a way solutions and the terms to activate and change licenses while maintaining to go with them.” Grow Revenue with Flexible Software Licensing, compliance. With FlexNet Publisher, activations and license changes are reduced to a single click, so – Amy Konary Pricing, and Packaging Research Director FlexNet Publisher gives you flexibility to customize customers can start using your products more quickly Software Pricing, software pricing, packaging, and licensing terms for without involving your support staff. -

LAM Guide Linux, Solaris, and Windows
LAM Guide Linux, Solaris, and Windows © 2008 Landmark Graphics Corporation Part No. 161608 R5000.0.0 February 2008 © 2008 Landmark Graphics Corporation All Rights Reserved Worldwide This publication has been provided pursuant to an agreement containing restrictions on its use. The publication is also protected by Federal copyright law. No part of this publication may be copied or distributed, transmitted, transcribed, stored in a retrieval system, or translated into any human or computer language, in any form or by any means, electronic, magnetic, manual, or otherwise, or disclosed to third parties without the express written permission of: Landmark Graphics Corporation 2107 CityWest Blvd, Building 2, Houston, Texas 77042-3021, USA P.O. Box 42806, Houston, Texas 77242, USA Phone: 713-839-2000 FAX: 713-839-2401 Web: www.halliburton.com/landmark Trademark Notice 3D Drill View, 3D Drill View KM, 3DFS, 3D Surveillance, 3DView, Active Field Surveillance, Active Reservoir Surveillance, ADC, Advanced Data Transfer, ARIES, ARIES DecisionSuite, Asset Decision Solution, Asset Development Center, Asset Journal, AssetLink, AssetLink Advisor, AssetLink Director, AssetLink Observer, Asset Performance, AssetPlanner, AssetSolver, AssetSolver Online, AssetView, BLITZPAK, CasingSeat, COMPASS, Corporate Data Archiver, Corporate Data Store, Data Analyzer, DataManager, DataStar, DBPlot, DecisionSpace, DecisionsSpace 3D Drill View KM, DecisionSpace AssetLink, DecisionSpace AssetPlanner, DecisionSpace AssetSolver, DecisionSpace AssetView 2D, DecisionSpace AssetView -
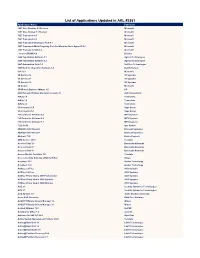
List of Applications Updated in ARL #2581
List of Applications Updated in ARL #2581 Application Name Publisher .NET Core Runtime 3.0 Preview Microsoft .NET Core Toolset 3.1 Preview Microsoft .NET Framework 4.5 Microsoft .NET Framework 4.6 Microsoft .NET Framework Developer Pack 4.7 Microsoft .NET Framework Multi-Targeting Pack for Windows Store Apps 4.5 RC Microsoft .NET Framework SDK 4.8 Microsoft _connect.BRAIN 4.8 Bizerba 2200 TapeStation Software 3.1 Agilent Technologies 2200 TapeStation Software 3.2 Agilent Technologies 24x7 Automation Suite 3.6 SoftTree Technologies 3500 Rack Configuration Software 6.0 Bently Nevada 365 16.0 Microsoft 3D Sprint 2.10 3D Systems 3D Sprint 2.11 3D Systems 3D Sprint 2.12 3D Systems 3D Viewer Microsoft 3PAR Host Explorer VMware 4.0 HP 4059 Extended Edition Attendant Console 2.1 ALE International 4uKey 1.4 Tenorshare 4uKey 1.6 Tenorshare 4uKey 2.2 Tenorshare 50 Accounts 21.0 Sage Group 50 Accounts 25.1 Sage Group 793 Controller Software 5.8 MTS Systems 793 Controller Software 5.9 MTS Systems 793 Controller Software 6.1 MTS Systems 7-Zip 19.00 Igor Pavlov ABAQUS 2018 Student Dassault Systemes ABAQUS 2019 Student Dassault Systemes Abstract 73.0 Elastic Projects ABU Service 14.10 Teradata Access Client 3.5 Barracuda Networks Access Client 3.7 Barracuda Networks Access Client 4.1 Barracuda Networks Access Module for Azure 15.1 Teradata Access Security Gateway (ASG) Soft Key Avaya AccuNest 10.3 Gerber Technology AccuNest 11.0 Gerber Technology ACDSee 2.3 Free ACD Systems ACDSee 2.4 Free ACD Systems ACDSee Photo Studio 2019 Professional ACD Systems -

Eagle Licensing Guide C R E a T I V E S O F T W a R E
macrovision EAGLE LICENSING GUIDE C R E A T I V E S O F T W A R E Eagle Licensing Guide “A resource guide to Eagle licensing for system administrators and developers” Revision Nr 3.2.1 en Page 1 May 2016 macrovision EAGLE LICENSING GUIDE C R E A T I V E S O F T W A R E Revision Nr 3.2.1 en Page 2 May 2016 macrovision EAGLE LICENSING GUIDE C R E A T I V E S O F T W A R E Contents Eagle Licensing Guide .......................................................................................................................1 Who should read this Guide? ...........................................................................................................8 1 – Introduction to Eagle Licensing ..................................................................................................9 FlexLM Plus Licensing [EOL] ..........................................................................................................9 FlexNET Licensing ..........................................................................................................................9 Hasp Dongle Licensing [EOL] ...................................................................................................... 10 Future Licensing ......................................................................................................................... 10 Virtual Machines ........................................................................................................................ 10 Further Reading ........................................................................................................................ -

Genetec Catalog
GENETEC CONFIDENTIAL Security Center SaaS SaaS Base Package Product Description MSRP (USD) Genetec Security Center SaaS Base Package. Includes 16 entities (cameras, readers, federated sites, intercoms), five (5) Security Desk client connection, five (5) Mobile client connections, five (5) Web client connections, Alarm Management, Advanced Reporting, System Partitioning, SCS-Base_1M $145.00 Incident Reports, and Dynamic Map Support for one tenant. Active Directory, Threat Level, Import Tool and Visitor Management modules are also included as well as Plan Manager for up to 25 entities, and Advanced Plan Manager for GIS Map servers, and Sipelia Base. Genetec Security Center SaaS Base Package. Includes 16 entities (cameras, readers, federated sites, intercoms), five (5) Security Desk client connection, five (5) Mobile client connections, five (5) Web client connections, Alarm Management, Advanced Reporting, System Partitioning, SCS-Base_1Y $1,595.00 Incident Reports, and Dynamic Map Support for one tenant. Active Directory, Threat Level, Import Tool and Visitor Management modules are also included as well as Plan Manager for up to 25 entities, and Advanced Plan Manager for GIS Map servers, and Sipelia Base. Genetec Security Center SaaS Base Video Package on- premises only. Includes five (5) Security Desk client connection, SCS-BaseVideo_1M five (5) Mobile client connections, five (5) Web client $0.00 connections, Alarm Management, Advanced Reporting, System Partitioning, Incident Reports. Genetec Security Center SaaS Base Video Package on- premises only. Includes five (5) Security Desk client connection, SCS-BaseVideo_1Y five (5) Mobile client connections, five (5) Web client $0.00 connections, Alarm Management, Advanced Reporting, System Partitioning, Incident Reports. Video Product Description MSRP (USD) SCS-1C_1M Subscription for 1 camera connection $11.00 SCS-1C_1Y Subscription for 1 camera connection $121.00 Yearly subscription to use the KiwiVision™ Privacy Protector™ SCS-OM-1PP_1M $10.00 module for one camera connection.