Mcafee Foundstone Fsl Update
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

An User & Developer Perspective on Immutable Oses
An User & Developer Perspective on Dario Faggioli Virtualization SW. Eng. @ SUSE Immutable OSes [email protected] dariof @DarioFaggioli https://dariofaggioli.wordpress.com/ https://about.me/dario.faggioli About Me What I do ● Virtualization Specialist Sw. Eng. @ SUSE since 2018, working on Xen, KVM, QEMU, mostly about performance related stuff ● Daily activities ⇒ how and what for I use my workstation ○ Read and send emails (Evolution, git-send-email, stg mail, ...) ○ Write, build & test code (Xen, KVM, Libvirt, QEMU) ○ Work with the Open Build Service (OBS) ○ Browse Web ○ Test OSes in VMs ○ Meetings / Video calls / Online conferences ○ Chat, work and personal ○ Some 3D Printing ○ Occasionally play games ○ Occasional video-editing ○ Maybe scan / print some document 2 ● Can all of the above be done with an immutable OS ? Immutable OS: What ? Either: ● An OS that you cannot modify Or, at least: ● An OS that you will have an hard time modifying What do you mean “modify” ? ● E.g., installing packages ● ⇒ An OS on which you cannot install packages ● ⇒ An OS on which you will have an hard time installing packages 3 Immutable OS: What ? Seriously? 4 Immutable OS: Why ? Because it will stay clean and hard to break ● Does this sound familiar? ○ Let’s install foo, and it’s dependency, libfoobar_1 ○ Let’s install bar (depends from libfoobar_1, we have it already) ○ Actually, let’s add an external repo. It has libfoobar_2 that makes foo work better! ○ Oh no... libfoobar_2 would break bar!! ● Yeah. It happens. Even in the best families distros -

The BIG Change for Opensuse Leap 15.3 About Me
The BIG Change for openSUSE Leap 15.3 About Me openSUSE Manager Hobbies ● Marketing/PR ● Fantasy Sports ● Event Organizer ● Mining ● Coordinate Event ● Series Binge Watcher Sponsorship Interesting Fact Education Christopher Reeve was ● MBA - Business to blame for me breaking my arm ● BA - Education Douglas DeMaio (Superman 1978) V International GNU Health Conference - Nov. 20 - 21, online event - #GHCon2020 The Way to openSUSE Leap 15.3 bout Me !losing the Leap Gap What is it & why does it matter. Jump 15.&.1 Leap 15.3 The efforts to change What to expect with in how a distribution is coming releases of this built openSUSE distribution What is openSUSE Leap Leap is trying to bridge “Community and Enterprise” the distribution is based on the latest version of SUSE Linux Enterprise available to the date, typically with a 12 months release cycle. Leap 15.2 Retrospective told us that users value most the installer, stability, seamless migrations, and YaST. These would be then our strengths according to users! The distribution is often profiled as the more stable one and easy to use as there should be no radical or disruptive changes in between minor updates. Some users say It’s the KDE distribution. Box says “The Linux Distribution for Beginners and Pros” !"osing the Leap Gap ● CtLG is a SUSE driven effort to bring Leap closer to SUSE Linux Enterprise than ever before. This brings quite some challenges but also open some new opportunities. ● Unification of openSUSE Leap and SUSE Linux Enterprise 15 code streams and feature set. ● Concept of building a community distribution by combining rpms from openSUSE Backports (community part) and SUSE signed SLE rpms (Enterprise part). -
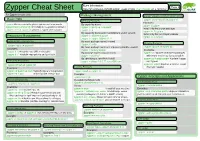
Zypper Cheat Sheet Or Type M an Zypper on a Terminal
More Information: Page 1 Zypper Cheat Sheet https://en.opensuse.org/SDB:Zypper_usage or type m an zypper on a terminal For Zypper version 1.0.9 Package Management Source Packages and Build Dependencies Basic Help Selecting Packages zypper source-install or zypper si Examples: zypper #list the available global options and commands By capability name: zypper si zypper zypper help [command] #Print help for a specific command zypper in 'perl(Log::Log4perl)' Install only the source package zypper shell or zypper sh #Open a zypper shell session zypper in qt zypper in -D zypper By capability name and/or architecture and/or version Install only the build dependencies zypper in 'zypper<0.12.10' Repository Management zypper in -d zypper zypper in zypper.i586=0.12.11 Listing Defined Repositories By exact package name (--name) Updating Packages zypper in -n ftp zypper repos or zypper lr By exact package name and repository (implies --name) zypper update or zypper up Examples: zypper in factory:zypper Examples: zypper lr -u #include repo URI on the table By package name using wildcards zypper up #update all installed packages zypper lr -P #include repo priority and sort by it zypper in yast*ftp* with newer version as far as possible By specifying a .rpm file to install zypper up libzypp zypper #update libzypp Refreshing Repositories zypper in skype-2.0.0.72-suse.i586.rpm and zypper zypper refresh or zypper ref zypper in sqlite3 #update sqlite3 or install Installing Packages Examples: if not yet installed zypper ref packman main #specify repos to be -

Snort 2.9.9.X on Opensuse Leap 42.2
Snort Installation on openSUSE Leap 42.2 64 bits Boris A. Gómez Universidad Tecnológica de Panamá July 2017 About This Guide This guide has been tested on openSUSE Leap 42.2, 64 bits, using DAQ 2.0.6 and Snort 2.9.9.0. Software was installed in a virtual machine: Virtual Machine Manager: VirtualBox 5.1.22 or KVM 1.4.0 HOST operating system: Windows 7 or openSUSE Leap 42.2 GUEST operating system: openSUSE Leap 42.2 (Snort will be installed here) For clarity, the following color code was used: Orange – commands that the user types at the shell prompt. Blue – text inside of configuration files. Purple – text to focus your attention on. This guide is based on the document "Snort 2.9.8.x on OpenSuSE 13x" by William Parker. Network Card Configuration Run VirtualBox | KVM manager and configure the network section of the guest machine to bridge mode. KVM Manager: VirtualBox Manager: Guest Machine Start your guest machine and set its network interface card to a static IP, for example 192.168.99.10, then check settings: ifconfig eth0 Link encap:Ethernet HWaddr 08:00:27:50:CA:99 inet addr: 192.168.99.10 Bcast:192.168.99.255 Mask:255.255.255.0 Verify that you can access Internet by accessing a web page, for example: https://snort.org Before proceeding, it is advisable to update the system. Required Packages Use YAST to install the following packages: gcc version 4.8.x (including libraries: libgcc_s1 (5.3.1), libgcc_s1-32bit(5.3.1)) flex (2.5.37) bison (2.7) php5-zlib (5.5.14 including zlib-devel 1.2.8) libpcap1 (1.8.1 including libpcap-devel 1.8.1) (versions must match) libpcre1 (8.39 including pcre-devel 8.39 and libpcre1-32bit 8.39) (versions must match) libdnet1 (1.12 including libdnet-devel 1.12) (versions must match) tcpdump (4.5.1). -

Integrating New Major Components on Fast and Slow Moving Distributions
IntegratingIntegrating newnew majormajor componentscomponents onon fastfast andand slowslow movingmoving distributionsdistributions How latest GNOME desktop was integrated into latest SUSE / openSUSE releases Frédéric Crozat <[email protected]> SUSE Linux Enterprise Release Manager What we don’t do What we do DistributionDistribution deliverydelivery stylesstyles 4 Three distributions styles ● Rolling: – Bleeding edge – Release as soon as possible – Example: openSUSE Tumbleweed, ArchLinux, Gentoo ● Regular: – Release one to twice a year – Update their entire stack for each release – Example: Ubuntu, Fedora, Debian ● LTS / Enterprise: – Slow cadence (yearly or even less than that) – Very few things move between sub-releases – Example: openSUSE Leap, Ubuntu LTS, SLES/SLED, RHEL 5 openSUSE/SUSE terminology ● OBS = OpenBuildService ● SLE = SUSE Linux Enterprise (Server / Desktop) – Enterprise distribution, developed by SUSE ● openSUSE Tumbleweed: – openSUSE Rolling release, by openSUSE, using only Factory packages, tested by openQA ● openSUSE Factory: – Development repository for Tumbleweed ● openSUSE Leap: – openSUSE Stable release, based on SLE common code + Packages from Factory (or specific repository) 6 IntegrationIntegration processprocess 7 OBS and Devel project ● On OBS, every source package is handled in a project which can build several packages together ● openSUSE Tumbleweed uses devel project per “topic” (KDE, GNOME, X11, …) ● Changes (patch, version update) are done in Devel projects and then, pushed to “main” distribution for -

Configuration Challenges in Linux and Ecos: a Survey
GSDLAB TECHNICAL REPORT Configuration Challenges in Linux and eCos: A Survey Arnaud Hubaux, Yingfei Xiong, Krzysztof Czarnecki GSDLAB{TR 2011{09{29 September 2011 Generative Software Development Laboratory University of Waterloo 200 University Avenue West, Waterloo, Ontario, Canada N2L 3G1 WWW page: http://gsd.uwaterloo.ca/ The GSDLAB technical reports are published as a means to ensure timely dissemination of scholarly and technical work on a non-commercial basis. Copyright and all rights therein are maintained by the authors or by other copyright holders, notwithstanding that they have offered their works here electronically. It is understood that all persons copying this information will adhere to the terms and constraints invoked by each author's copyright. These works may not be reposted without the explicit permission of the copyright holder. Configuration Challenges in Linux and eCos: A Survey Arnaud Hubaux, Yingfei Xiong, Krzysztof Czarnecki September 29, 2011 Abstract Operating systems expose sophisticated configurability to handle vari- ations in hardware platforms like desktops, servers, and mobile devices. The configuration of an operating system like Linux contains thousands of options guarded by hundreds of complex constraints. To guide users throughout the configuration activity, configurators implement various mechanisms to produce correct configurations. However, configuration still remains a difficult and challenging process. To better understand the challenges faced by users during configuration, we conducted surveys among Linux and eCos users to answer the two following questions: • What challenges do users most frequently face? • How significant is the conflict resolution problem? In this paper, we report on the results of these two surveys. 1 Linux This section focuses on the configuration tools used for the Linux kernel. -
The Growth of Android in Embedded Systems
THE GROWTH OF ANDROID IN EMBEDDED SYstEMS THE LINUX FOUNDATION TRAINING PUBLICATION Written by Benjamin Zores OVERVIEW Linux has continuously grown in the embedded systems market for over a decade, gaining market share from proprietary operating systems. The proliferation of embedded devices, the explosion of open source development, the inherent hardware support, the incredible networking capabilities and the royalty-free economic model have all helped propel use of the Linux kernel into one of the best choices for the design of new embedded systems. While the success of Linux in the embedded market can not be denied, its notoriety was once confined to mostly technical professionals. That changed in 2008 with Google’s release of the Android mobile phone operating system, based on the Linux kernel. Thus began the tremendous growth of Linux in the consumer world, with over one million Android devices being activated every day in 2012 and predictions of total Android devices shipped reaching one billion in 2013. THE GROWTH OF ANDROID 1 IN EMBEDDED SYstEMS of Android in THE GROWTH Embedded Systems In a recent The Android Operating System survey, 34% Android’s success was no accident and was the result of a long-term strategy and loads of investment from Google. The early development of the OS came from within Android Inc. of embedded in the early 2000’s; it was purchased by Google in 2005. The original system relied on a Java framework for its application layer and was not based on the Linux kernel. Only after engineers are several years of development at Google labs, and after an architecture revamping, the first Android-based smart-phone (the HTC G1) was released and based on the very first version considering of the Android software development kit (SDK). -

Nvidia Cuda Installation Guide for Linux
NVIDIA CUDA INSTALLATION GUIDE FOR LINUX DU-05347-001_v9.1 | April 2018 Installation and Verification on Linux Systems TABLE OF CONTENTS Chapter 1. Introduction.........................................................................................1 1.1. System Requirements.................................................................................... 1 1.2. About This Document.................................................................................... 2 Chapter 2. Pre-installation Actions...........................................................................3 2.1. Verify You Have a CUDA-Capable GPU................................................................ 3 2.2. Verify You Have a Supported Version of Linux.......................................................4 2.3. Verify the System Has gcc Installed................................................................... 4 2.4. Verify the System has the Correct Kernel Headers and Development Packages Installed.... 4 2.5. Choose an Installation Method......................................................................... 6 2.6. Download the NVIDIA CUDA Toolkit....................................................................6 2.7. Handle Conflicting Installation Methods.............................................................. 6 Chapter 3. Package Manager Installation....................................................................8 3.1. Overview................................................................................................... 8 3.2. Redhat/CentOS........................................................................................... -

Opensuse Leap to SLES: More Than the Sum of Its Parts
openSUSE Leap to SLES: More Than The Sum Of Its Parts... Session TUT-1418 Udo Seidel Jeff Lindholm Tech-Writer and Enterprise Architect Sales Engineering Manager Amadeus SUSE [email protected] [email protected] 1 • Udo Seidel • Jeff Lindholm – SUSE • Teacher for Math and Physics • Detroit, MI USA • Linux and Open Source since 1996 • SUSE Evangelist since 2004 • Linux • Sales Engineering Manager • Software Defined Storage • OpenSUSE Community supporter • Openstack • Technology Focus • Container • Cloud Native Infrastructure • Raspberry Pi and Co • Application Transformation • … • Enterprise Linux • Enterprise Architect and Tech-Writer 2 Agenda 1. DevOPS Experience – Developer Use Case 2. OpenSUSE Community – Flexible Developer Platform 1. OpenSUSE Tumbleweed – Rolling Release 2. OpenSUSE Leap 15 – Stable Release 3. SUSE Linux Enterprise Server 15 4. LEAP SLE Interoperability and Supported Migration Use Cases 5. Demonstration – Leap Migration 6. Questions and Answers 3 4 SUSE Solutions For DevOps A suite of flexible, modular open source solutions CODE PLAN DEPLOY OBS, PackageHub, SUSE SUSE Linux Enterprise SUSE Application Delivery, Manager, Portus, GitHub openSUSE SUSE Public Cloud, SUSE Manager, Salt, Kubernetes BUILD OBS, SUSE Studio, SUSE Manager, KIWI, Docker open source project OPERATE & MONITOR SUSE Manager, SUSE Enterprise Storage, SUSE Application Delivery, TEST & RELEASE Kubernetes openQA, Jenkins 5 SUSE & openSUSE – Working Together Stable code and contributions Mutual collaboration Upstream innovations 6 These common elements are core to all openSUSE and SUSE distributions • YaST • openSUSE Build Service • Stability and testing - openQA 7 The openSUSE Distributions 8 openSUSE Tumbleweed • The Tumbleweed distribution is a pure rolling release version of openSUSE containing the latest stable versions of all software instead of relying on rigid periodic release cycles. -
What's up with SUSE?
March 11, 2021 What’s up with SUSE? Picture Welcome to TriLug! 1.History of SUSE 2.SUSE Linux Distros 3.Other Products 4.Tease about Rancher Copyright © SUSE 2021 2 Who is this guy? • Joined SUSE in March 2018 • Formerly with Western Digital, SanDisk, Fusion-io, SteelEye Tech.,Sun Microsystems, Lockheed • MS Computer Science, West Virginia • Attending TriLug since 2007 • Takes care of his wife's chickens.... Dwain Sims Sales Engineer [email protected] [email protected] +1 919-480-1774 Copyright © SUSE 2021 3 What means SUSE? Copyright © SUSE 2021 4 S.u.S.E. Roland Dyroff, Thomas Fehr, Burchard Steinbild and Hubert Mantel found S.u.S.E., 1992. SUSE is a German acronym for "Software und System-Entwicklung" (software and systems development). Softlanding Linux System (SLS) was one of the earliest Liunx disros. (Slackware was initially based on SLS) First true S.u.S.E. Liunx distro was 4.2, in 1996. Copyright © SUSE 2021 5 How is SUSE pronounced? Copyright © SUSE 2021 6 Brief History of SUSE Copyright © SUSE 2021 7 A BOUT S US E 28 Years of Leadership in True Open Source 1992 to 2000 2001 to 2010 2011 to Present 2017 to Present Becoming strategic partner of From Linux Pioneer to The Pioneering Enabling an Always Open SAP and building a strong Software-Defined Years Data Center ecosystem Infrastructure and Edge Important Milestones 1992 2010 2020 SUSE brings Linux to the Linux-based solution Acquires enterprise with AWS Rancher Labs 2020 2008 2019 Partnership with SUSE celebrates first year of Joint innovation with SAP EQT independence 8 Copyright © SUSE 2020. -
User Guide 5
MANJAROLINUX USERGUIDE THEMANJARODEVELOPMENTTEAM Copyright © 2017 the Manjaro Development Team. Licensed under the Attribution-ShareAlike 4.0 International Licence (the “Licence”); you may not use this file except in compliance with the License. You may obtain a copy of the Licence at: https://creativecommons.org/licenses/by-sa/4.0/legalcode Unless required by applicable law or agreed to in writing, software distributed under the Licence is distributed on an “as is” basis, without warranties or conditions of any kind, either express or implied. See the Licence for the specific language governing permissions and limitations under the Licence. The source code for this documentation can be downloaded from: https://github.com/manjaro/manjaro-user-guide/ user guide 5 The Manjaro Development Team Core Team Philip Müller Owner, Project Leader, Project Management and Co- ordination, Mirrors Manager, Server Manager, Packager, De- veloper, Web Developer Guillaume Benoit Developer, Moderation Ramon Buldó Developer, Packager Stefano Capitani Maintainer, Packager Bernhard Landauer Community Manager, Packager, Maintainer, Mod- eration, News Rob McCathie Maintainer Marcus Developer, Packager Teo Mrnjavac Developer Alexandre A. Arnt Developer, Moderation Ringo de Kroon Community Hugo Posnic Developer Artwork David Linares Designer Documentation Jonathon Fernyhough Editor of the User Guide 0.8.9-0.8.13, 15.09-15.12, Community Management, Cover art of the User Guide Sabras Wiki Manuel Barrette Editor of the User Guide 16.08-16.10, 17.0 Alumni Roland Singer Founder, Designer, Developer, Web Developer, Admin- istrator Carl Duff Community, Documentation and Wiki Management, Script- ing and Configuration Cumali Cinnamon and Gnome Community Editions Maintainer 6 manjaro linux Dan S. -
Build Your Own Distro Tired of the Run-Of-The-Mill Stuff on Distrowatch? Why Not Heed Mayank Sharma and Create the Perfect Operating System for You?
Build your own distro Tired of the run-of-the-mill stuff on Distrowatch? Why not heed Mayank Sharma and create the perfect operating system for you? few issues ago, [LXF171, 50 making it your own – by removing apps and Now traditional wisdom says that creating Distros Tested], we looked at drivers that you don’t need and adding the your own Linux system is a rather difficult the best Linux distributions for ones you do. You’ll also probably change the thing to do and shouldn’t be attempted by A all kinds of users. There were factory-fitted artwork that says more about anyone other than Linux veterans. distros that were designed with ease of use the distro vendor than you. We begin the feature with graphical point- in mind, some focused on productivity, Sure that’s one way to go about it. and-click tools. Yes, you read that right. All it while others catered to specialised use You tweak and customise the distro to suit takes is a couple of clicks to craft your very cases, such as security and privacy your requirements. But wouldn’t it be really own flavour of Linux that you can pass to conscious users. But we can guarantee great if you just create your very own, custom friends and family. We’ve got tools that’ll help that there wasn’t a distro designed Linux distribution? you create and distribute customised spins specifically and entirely for you! based on Ubuntu, Fedora and While most Linux users make do OpenSUSE – the three mainstream with one of the mainstream distros out “We’ve got tools that’ll Linux distributions that house there, there’s always something or the help you create and thousands of open source software in other that’s missing.