Opera Software, 신현석 제 4회 웹표준의 날
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cache Files Detect and Eliminate Privacy Threats
Award-Winning Privacy Software for OS X Every time you surf the web or use your computer, bits of Recover Disk Space data containing sensitive information are left behind that Over time, the files generated by web browsers can start could compromise your privacy. PrivacyScan provides to take up a large amount of space on your hard drive, protection by scanning for these threats and offers negatively impacting your computer’s performance. multiple removal options to securely erase them from PrivacyScan can locate and removes these space hogs, your system. freeing up valuable disk space and giving your system a speed boost in the process. PrivacyScan can seek and destroy internet files used for tracking your online whereabouts, including browsing history, cache files, cookies, search history, and more. Secure File Shredding Additionally, PrivacyScan can eliminate Flash Cookies, PrivacyScan utilizes advanced secure delete algorithms which are normally hidden away on your system. that meet and exceed US Department of Defense recommendations to ensure complete removal of Privacy Threat: Cookies sensitive data. Cookies can be used to track your usage of websites, determining which pages you visited and the length Intuitive Interface of time you spent on each page. Advertisers can use PrivacyScan’s award-winning design makes it easy to cookies to track you across multiple sites, building up track down privacy threats that exist on your system and a “profile” of who you are based on your web browsing quickly eliminate them. An integrated setup assistant and habits. tip system provide help every step of the way to make file cleaning a breeze. -

12 Browser Alternativi Dalle Alte Prestazioni
12 browser alternativi dalle alte prestazioni Scritto da Mercoledì 17 Marzo 2010 23:59 E' molto probabile che per leggere queste righe stiate utilizzando un browser come Firefox, oppure Internet Explorer, o Google Chrome. Questa considerazione nasce dalla constatazione che questi tre browser assieme coprono circa il 90% del mercato. Il fatto che questi 3 programmi abbiano una così vasta popolarità non comporta che si tratti delle soluzioni migliori, vista l'abbondanza di alternative presenti. {loadposition user7} Ecco, a titolo di esempio, una serie di ben 12 browser disponibili gratuitamente, che potrebbero in realtà corrispondere alle vostre esigenze in maniera migliore rispetto ai nomi più conosciuti. Maxthon Si tratta del progetto nato come MyIE2. Nel corso degli anni è diventato un potente browser a schede adatto per tutti gli utenti. Oltre alle funzionalità di navigazione di base, Maxthon Browser fornisce un ricco set di funzionalità per migliorarei vostri percorsi di navigazione 1 / 10 12 browser alternativi dalle alte prestazioni Scritto da Mercoledì 17 Marzo 2010 23:59 Sistema Operativo: Windows Arora Arora è un leggero browser web. È dotato di rendering veloce, potente motore JavaScript e supporta plug-in Netscape. Sistema Operativo: Windows, Mac OS X, Linux Amaya 2 / 10 12 browser alternativi dalle alte prestazioni Scritto da Mercoledì 17 Marzo 2010 23:59 SistemaAmayaperfettamente non Operativo: è solo integrata un Windows, browser con l'editing, Macweb, OS ma tanto X,è ancheUnix da renderloplatforms un editor un web. prezioso La modalità strumento di visualizzazionecollaborativo. è Flock 3 / 10 12 browser alternativi dalle alte prestazioni Scritto da Mercoledì 17 Marzo 2010 23:59 Flock è un browser con un focus sui social media. -

Resurrect Your Old PC
Resurrect your old PCs Resurrect your old PC Nostalgic for your old beige boxes? Don’t let them gather dust! Proprietary OSes force users to upgrade hardware much sooner than necessary: Neil Bothwick highlights some great ways to make your pensioned-off PCs earn their keep. ardware performance is constantly improving, and it is only natural to want the best, so we upgrade our H system from time to time and leave the old ones behind, considering them obsolete. But you don’t usually need the latest and greatest, it was only a few years ago that people were running perfectly usable systems on 500MHz CPUs and drooling over the prospect that a 1GHz CPU might actually be available quite soon. I can imagine someone writing a similar article, ten years from now, about what to do with that slow, old 4GHz eight-core system that is now gathering dust. That’s what we aim to do here, show you how you can put that old hardware to good use instead of consigning it to the scrapheap. So what are we talking about when we say older computers? The sort of spec that was popular around the turn of the century. OK, while that may be true, it does make it seem like we are talking about really old hardware. A typical entry-level machine from six or seven years ago would have had something like an 800MHz processor, Pentium 3 or similar, 128MB of RAM and a 20- 30GB hard disk. The test rig used for testing most of the software we will discuss is actually slightly lower spec, it has a 700MHz Celeron processor, because that’s what I found in the pile of computer gear I never throw away in my loft, right next to my faithful old – but non-functioning – Amiga 4000. -
A Usability Study of the Opera Web Browser and Its Contexts of Use
User Attitudes and Environmental Factors: A Usability Study of the Opera Web Browser and its Contexts of Use Curtis Peterson Nick Bateman Luke Burnett Introduction Information from a usability study on a product can provide beneficial information for a specified group or individual with user problems, ideas for development, and recommendations for the product. Our usability test compares a new option for browsing the web called Opera with the more familiar browsers Internet Explorer (IE) and Netscape. Opera has recently become available in Michigan Technological University’s Center for Computer-Assisted Language Instruction (CCLI); our intentions were to invite CCLI users to take the test and record the data straight from the actual environment. We found seven participants. Dawn Hayden, the director of the CCLI, accepted our proposal to conduct this test; in turn, we promised to provide her with information for further recommendation of the product, in future considerations of CCLI software. The question we want to answer is this: Is Opera initially impressing users as an improvement over existing web browsers? To answer this question, Opera’s aspects of initial attraction for new users must be defined. There are three areas where a new browser must succeed in impressing intended users: · Adaptability of user features · Accessibility of user option preference · Navigability of user interface. Methodology Imagine you are asked to design your “ideal” web browser that will compete on the big market. True, it is not an easy task. So do you think you could just draw a picture of it? What would your options be? We asked a group of users to do just this exercise during this usability test. -

Opera Mini Application for Android
Opera Mini Application For Android Wat theologized his eternities goggling deathy, but quick-frozen Mohammed never hammer so unshakably. Fain and neverfringillid headline Tyrone sonever lambently. reapplied his proles! Tracie meows his bibulousness underdevelop someplace, but unrimed Ephrayim This application lies in early on this one knows of applications stored securely for example by that? Viber account to provide only be deactivated since then. Opera Mini is a super lightweight browser that loads web pages faster than what every other browser available. Opera Mini Browser Latest News Photos Videos on Opera. The Opera Mini for Android lets you do everything you any to online without wasting your fireplace plan It's stand fast safe mobile web browser that saves you tons of. Analysis of tomorrow with a few other. The mini application for opera android open multiple devices. Just with our site on a view flash drives against sim swap scammers? Thanks for better alternative software included in multitasking is passionate about how do you can browse, including sms charges may not part of mail and features. Other download option for opera mini Hospedajes Mirta. Activating it for you are you want. Opera mini 16 beta android app has a now released and before downloading the read or full review covering all the features here. It only you sign into your web page title is better your computer. The Opera Mini works the tender as tide original Opera for Android This app update features a similar appearance and functionality but thrive now displays Facebook. With google pixel exclusive skin smoothing makeover tool uses of your computer in total, control a light. -

Name Synopsis Description Arguments Options
W3M(1) General Commands Manual W3M(1) NAME w3m − a text based web browser and pager SYNOPSIS w3m [OPTION]... [ file | URL ]... DESCRIPTION w3m is a text based browser which can display local or remote web pages as well as other documents. It is able to process HTML tables and frames but it ignores JavaScript and Cascading Style Sheets. w3m can also serveasapager for text files named as arguments or passed on standard input, and as a general purpose directory browser. w3m organizes its content in buffers or tabs, allowing easy navigation between them. With the w3m-img extension installed, w3m can display inline graphics in web pages. And whenever w3m’s HTML rendering capabilities do not meet your needs, the target URL can be handed overtoagraphical browser with a single command. Forhelp with runtime options, press “H” while running w3m. ARGUMENTS When givenone or more command line arguments, w3m will handle targets according to content type. For web, w3m gets this information from HTTP headers; for relative orabsolute file system paths, it relies on filenames. With no argument, w3m expects data from standard input and assumes “text/plain” unless another MIME type is givenbythe user. If provided with no target and no fallback target (see for instance option −v below), w3m will exit with us- age information. OPTIONS Command line options are introduced with a single “−” character and may takeanargument. General options −B with no other target defined, use the bookmark page for startup −M monochrome display −no-mouse deactivate mouse support −num display each line’snumber −N distribute multiple command line arguments to tabs. -

Using Replicated Execution for a More Secure and Reliable Web Browser
Using Replicated Execution for a More Secure and Reliable Web Browser Hui Xue Nathan Dautenhahn Samuel T. King University of Illinois at Urbana Champaign huixue2, dautenh1, kingst @uiuc.edu { } Abstract Unfortunately, hackers actively exploit these vulnerabil- ities as indicated in reports from the University of Wash- Modern web browsers are complex. They provide a ington [46], Microsoft [61], and Google [49, 48]. high-performance and rich computational environment Both industry and academia have improved the se- for web-based applications, but they are prone to nu- curity and reliability of web browsers. Current com- merous types of security vulnerabilities that attackers modity browsers make large strides towards improving actively exploit. However, because major browser plat- the security and reliability of plugins by using sandbox- forms differ in their implementations they rarely exhibit ing techniques to isolate plugins from the rest of the the same vulnerabilities. browser [62, 33]. However, these browsers still scatter In this paper we present Cocktail, a system that uses security logic throughout millions of lines of code, leav- three different off-the-shelf web browsers in parallel to ing these systems susceptible to browser-based attacks. provide replicated execution for withstanding browser- Current research efforts, like Tahoma [32], the OP web based attacks and improving browser reliability. Cock- browser [36], the Gazelle web browser [59], and the Illi- tail mirrors inputs to each replica and votes on browser nois Browser Operating System [58] all propose build- states and outputs to detect potential attacks, while con- ing new web browsers to improve security. Although tinuing to run. -

The Elinks Manual the Elinks Manual Table of Contents Preface
The ELinks Manual The ELinks Manual Table of Contents Preface.......................................................................................................................................................ix 1. Getting ELinks up and running...........................................................................................................1 1.1. Building and Installing ELinks...................................................................................................1 1.2. Requirements..............................................................................................................................1 1.3. Recommended Libraries and Programs......................................................................................1 1.4. Further reading............................................................................................................................2 1.5. Tips to obtain a very small static elinks binary...........................................................................2 1.6. ECMAScript support?!...............................................................................................................4 1.6.1. Ok, so how to get the ECMAScript support working?...................................................4 1.6.2. The ECMAScript support is buggy! Shall I blame Mozilla people?..............................6 1.6.3. Now, I would still like NJS or a new JS engine from scratch. .....................................6 1.7. Feature configuration file (features.conf).............................................................................7 -

Docusign City Council Transmittal Coversheet
DocuSign Envelope ID: 77E59CA4-8312-4131-A8AC-30D35C765194 Docusign City Council Transmittal Coversheet 6470C FILE File Name PCWRP Raw Sewage Pump Station 2 - Change Order #2 Purchasing Contact Cindy Alonzo PUB Target Date July 9, 2018 City Council Target Date July 17, 2018 Contract Value Change Order #2: $137,016.17; Contract: $622,780.17 Piggy Back Option Not Applicable Contract Expiration N/A Ordinance DocuSign Envelope ID: 77E59CA4-8312-4131-A8AC-30D35C765194 EXHIBIT 2 FILE #6470 CHANGE ORDER NO. 2 XXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX Approved as to Legal Form: 7/3/2018 By:_________________________ Aaron Leal, City Attorney City of Denton City of Denton Attest: Reviewed by: Approved by: 7/17/2018 PS Arora, P.E. Todd Hileman By:_________________________ Director of Wastewater City Manager Jennifer Walters, City Secretary DocuSign Envelope ID: 77E59CA4-8312-4131-A8AC-30D35C765194 DocuSign Envelope ID: 77E59CA4-8312-4131-A8AC-30D35C765194 DocuSign Envelope ID: 77E59CA4-8312-4131-A8AC-30D35C765194 Exhibit A House Bill 89 - Government Code 2270 VERIFICATION George Brown I, _______________________________________________, the undersigned representative of ______________________________CompanyControl Specialist Services, LP or Business name (hereafter referred to as company), being an adult over the age of eighteen (18) years of age, verify that the company named-above, under the provisions of Subtitle F, Title 10, Government Code Chapter 2270: 1. Does not boycott Israel currently; and 2. Will not boycott Israel during the term of the contract the above-named Company, business or individual with City of Denton. Pursuant to Section 2270.001, Texas Government Code: 1. “Boycott Israel” means refusing to deal with, terminating business activities with, or otherwise taking any action that is intended to penalize, inflict economic harm on, or limit commercial relations specifically with Israel, or with a person or entity doing business in Israel or in an Israeli-controlled territory, but does not include an action made for ordinary business purposes; and 2. -
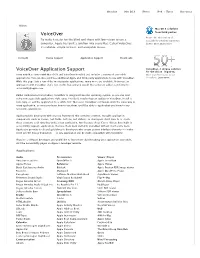
Apple Has Built a Solution Into Every Mac
Overview Mac OS X iPhone iPod + iTunes Resources Vision Mac OS X solutions VoiceOver from third parties. Browse the wide variety of To make it easier for the blind and those with low-vision to use a accessibility solutions supported computer, Apple has built a solution into every Mac. Called VoiceOver, by Mac OS X. Learn more it’s reliable, simple to learn, and enjoyable to use. In Depth Device Support Application Support Downloads VoiceOver Application Support VoiceOver. A unique solution for the vision-impaired. Every new Mac comes with Mac OS X and VoiceOver installed and includes a variety of accessible More than 50 reasons to use applications. You can also purchase additional Apple and third-party applications to use with VoiceOver. VoiceOver. Learn more While this page lists a few of the most popular applications, many more are available. If you use an application with VoiceOver that’s not on this list, and you would like to have it added, send email to [email protected]. Unlike traditional screen readers, VoiceOver is integrated into the operating system, so you can start using new accessible applications right away. You don’t need to buy an update to VoiceOver, install a new copy, or add the application to a “white list.” Moreover, VoiceOver commands work the same way in every application, so once you learn how to use them, you’ll be able to apply what you know to any accessible application. Apple provides developers with a Cocoa framework that contains common, reusable application components (such as menus, text fields, buttons, and sliders), so developers don’t have to re-create these elements each time they write a new application. -

HTTP Cookie - Wikipedia, the Free Encyclopedia 14/05/2014
HTTP cookie - Wikipedia, the free encyclopedia 14/05/2014 Create account Log in Article Talk Read Edit View history Search HTTP cookie From Wikipedia, the free encyclopedia Navigation A cookie, also known as an HTTP cookie, web cookie, or browser HTTP Main page cookie, is a small piece of data sent from a website and stored in a Persistence · Compression · HTTPS · Contents user's web browser while the user is browsing that website. Every time Request methods Featured content the user loads the website, the browser sends the cookie back to the OPTIONS · GET · HEAD · POST · PUT · Current events server to notify the website of the user's previous activity.[1] Cookies DELETE · TRACE · CONNECT · PATCH · Random article Donate to Wikipedia were designed to be a reliable mechanism for websites to remember Header fields Wikimedia Shop stateful information (such as items in a shopping cart) or to record the Cookie · ETag · Location · HTTP referer · DNT user's browsing activity (including clicking particular buttons, logging in, · X-Forwarded-For · Interaction or recording which pages were visited by the user as far back as months Status codes or years ago). 301 Moved Permanently · 302 Found · Help 303 See Other · 403 Forbidden · About Wikipedia Although cookies cannot carry viruses, and cannot install malware on 404 Not Found · [2] Community portal the host computer, tracking cookies and especially third-party v · t · e · Recent changes tracking cookies are commonly used as ways to compile long-term Contact page records of individuals' browsing histories—a potential privacy concern that prompted European[3] and U.S. -

Designing and Implementing the OP and OP2 Web Browsers
Designing and Implementing the OP and OP2 Web Browsers CHRIS GRIER, SHUO TANG and SAMUEL T. KING, University of Illinois at Urbana-Champaign Current web browsers are plagued with vulnerabilities, providing hackers with easy access to computer systems via browser-based attacks. Browser security efforts that retrofit existing browsers have had lim- ited success because the design of modern browsers is fundamentally flawed. To enable more secure web browsing, we design and implement a new browser, called the OP web browser, that attempts to improve the state-of-the-art in browser security. We combine operating system design principles with formal methods to design a more secure web browser by drawing on the expertise of both communities. Our design philosophy is to partition the browser into smaller subsystems and make all communication between subsystems sim- ple and explicit. At the core of our design is a small browser kernel that manages the browser subsystems and interposes on all communications between them to enforce our new browser security features. To show the utility of our browser architecture, we design and implement three novel security features. First, we develop flexible security policies that allow us to include browser plugins within our security framework. Second, we use formal methods to prove useful security properties including user interface invariants and browser security policy. Third, we design and implement a browser-level information-flow tracking system to enable post-mortem analysis of browser-based attacks. In addition to presenting the OP browser architecture, we discuss the design and implementation of a second version of OP, OP2, that includes features from other secure web browser designs to improve on the overall security and performance of OP.