Control-Flow Recovery from Partial Failure Reports
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Benchmarking the Stack Trace Analysis Tool for Bluegene/L
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by Juelich Shared Electronic Resources John von Neumann Institute for Computing Benchmarking the Stack Trace Analysis Tool for BlueGene/L Gregory L. Lee, Dong H. Ahn, Dorian C. Arnold, Bronis R. de Supinski, Barton P. Miller, Martin Schulz published in Parallel Computing: Architectures, Algorithms and Applications , C. Bischof, M. B¨ucker, P. Gibbon, G.R. Joubert, T. Lippert, B. Mohr, F. Peters (Eds.), John von Neumann Institute for Computing, J¨ulich, NIC Series, Vol. 38, ISBN 978-3-9810843-4-4, pp. 621-628, 2007. Reprinted in: Advances in Parallel Computing, Volume 15, ISSN 0927-5452, ISBN 978-1-58603-796-3 (IOS Press), 2008. c 2007 by John von Neumann Institute for Computing Permission to make digital or hard copies of portions of this work for personal or classroom use is granted provided that the copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page. To copy otherwise requires prior specific permission by the publisher mentioned above. http://www.fz-juelich.de/nic-series/volume38 Benchmarking the Stack Trace Analysis Tool for BlueGene/L Gregory L. Lee1, Dong H. Ahn1, Dorian C. Arnold2, Bronis R. de Supinski1, Barton P. Miller2, and Martin Schulz1 1 Computation Directorate Lawrence Livermore National Laboratory, Livermore, California, U.S.A. E-mail: {lee218, ahn1, bronis, schulzm}@llnl.gov 2 Computer Sciences Department University of Wisconsin, Madison, Wisconsin, U.S.A. E-mail: {darnold, bart}@cs.wisc.edu We present STATBench, an emulator of a scalable, lightweight, and effective tool to help debug extreme-scale parallel applications, the Stack Trace Analysis Tool (STAT). -
![Warrior1: a Performance Sanitizer for C++ Arxiv:2010.09583V1 [Cs.SE]](https://docslib.b-cdn.net/cover/1319/warrior1-a-performance-sanitizer-for-c-arxiv-2010-09583v1-cs-se-2341319.webp)
Warrior1: a Performance Sanitizer for C++ Arxiv:2010.09583V1 [Cs.SE]
Warrior1: A Performance Sanitizer for C++ Nadav Rotem, Lee Howes, David Goldblatt Facebook, Inc. October 20, 2020 1 Abstract buffer, copies the data and deletes the old buffer. As the vector grows the buffer size expands in a geometric se- This paper presents Warrior1, a tool that detects perfor- quence. Constructing a vector of 10 elements in a loop mance anti-patterns in C++ libraries. Many programs results in 5 calls to ’malloc’ and 4 calls to ’free’. These are slowed down by many small inefficiencies. Large- operations are relatively expensive. Moreover, the 4 dif- scale C++ applications are large, complex, and devel- ferent buffers pollute the cache and make the program run oped by large groups of engineers over a long period of slower. time, which makes the task of identifying inefficiencies One way to optimize the performance of this code is to difficult. Warrior1 was designed to detect the numerous call the ’reserve’ method of vector. This method will small performance issues that are the result of inefficient grow the underlying storage of the vector just once and use of C++ libraries. The tool detects performance anti- allow non-allocating growth of the vector up to the speci- patterns such as map double-lookup, vector reallocation, fied size. The vector growth reallocation is a well known short lived objects, and lambda object capture by value. problem, and there are many other patterns of inefficiency, Warrior1 is implemented as an instrumented C++ stan- some of which are described in section 3.4. dard library and an off-line diagnostics tool. -

Does the Fault Reside in a Stack Trace? Assisting Crash Localization by Predicting Crashing Fault Residence
The Journal of Systems and Software 148 (2019) 88–104 Contents lists available at ScienceDirect The Journal of Systems and Software journal homepage: www.elsevier.com/locate/jss Does the fault reside in a stack trace? Assisting crash localization by predicting crashing fault residence ∗ Yongfeng Gu a, Jifeng Xuan a, , Hongyu Zhang b, Lanxin Zhang a, Qingna Fan c, Xiaoyuan Xie a, Tieyun Qian a a School of Computer Science, Wuhan University, Wuhan 430072, China b School of Electrical Engineering and Computer Science, The University of Newcastle, Callaghan NSW2308, Australia c Ruanmou Edu, Wuhan 430079, China a r t i c l e i n f o a b s t r a c t Article history: Given a stack trace reported at the time of software crash, crash localization aims to pinpoint the root Received 27 February 2018 cause of the crash. Crash localization is known as a time-consuming and labor-intensive task. Without Revised 7 October 2018 tool support, developers have to spend tedious manual effort examining a large amount of source code Accepted 6 November 2018 based on their experience. In this paper, we propose an automatic approach, namely CraTer, which pre- Available online 6 November 2018 dicts whether a crashing fault resides in stack traces or not (referred to as predicting crashing fault res- Keywords: idence ). We extract 89 features from stack traces and source code to train a predictive model based on Crash localization known crashes. We then use the model to predict the residence of newly-submitted crashes. CraTer can Stack trace reduce the search space for crashing faults and help prioritize crash localization efforts. -
Feedback-Directed Instrumentation for Deployed Javascript Applications
Feedback-Directed Instrumentation for Deployed JavaScript Applications ∗ ∗ Magnus Madsen Frank Tip Esben Andreasen University of Waterloo Samsung Research America Aarhus University Waterloo, Ontario, Canada Mountain View, CA, USA Aarhus, Denmark [email protected] [email protected] [email protected] Koushik Sen Anders Møller EECS Department Aarhus University UC Berkeley, CA, USA Aarhus, Denmark [email protected] [email protected] ABSTRACT be available along with failure reports. For example, log files Many bugs in JavaScript applications manifest themselves may exist that contain a summary of an application's exe- as objects that have incorrect property values when a fail- cution behavior, or a dump of an application's state at the ure occurs. For such errors, stack traces and log files are time of a crash. However, such information is often of lim- often insufficient for diagnosing problems. In such cases, it ited value, because the amount of information can be over- is helpful for developers to know the control flow path from whelming (e.g., log files may span many megabytes, most the creation of an object to a crashing statement. Such of which is typically completely unrelated to the failure), or crash paths are useful for understanding where the object is woefully incomplete (e.g., a stack trace or memory dump originated and whether any properties of the object were usually provides little insight into how an application arrived corrupted since its creation. in an erroneous state). We present a feedback-directed instrumentation technique Many bugs that arise in JavaScript applications manifest for computing crash paths that allows the instrumentation themselves as objects that have incorrect property values overhead to be distributed over a crowd of users and to re- when a failure occurs. -

Stack Traces in Haskell
Stack Traces in Haskell Master of Science Thesis ARASH ROUHANI Chalmers University of Technology Department of Computer Science and Engineering G¨oteborg, Sweden, March 2014 The Author grants to Chalmers University of Technology and University of Gothen- burg the non-exclusive right to publish the Work electronically and in a non-commercial purpose make it accessible on the Internet. The Author warrants that he/she is the author to the Work, and warrants that the Work does not contain text, pictures or other material that violates copyright law. The Author shall, when transferring the rights of the Work to a third party (for example a publisher or a company), acknowledge the third party about this agreement. If the Author has signed a copyright agreement with a third party regarding the Work, the Author warrants hereby that he/she has obtained any necessary permission from this third party to let Chalmers University of Technology and University of Gothenburg store the Work electronically and make it accessible on the Internet. Stack Traces for Haskell A. ROUHANI c A. ROUHANI, March 2014. Examiner: J. SVENNINGSSON Chalmers University of Technology University of Gothenburg Department of Computer Science and Engineering SE-412 96 G¨oteborg Sweden Telephone + 46 (0)31-772 1000 Department of Computer Science and Engineering Department of Computer Science and Engineering G¨oteborg, Sweden March 2014 Abstract This thesis presents ideas for how to implement Stack Traces for the Glasgow Haskell Compiler. The goal is to come up with an implementation with such small overhead that organizations do not hesitate to use it for their binaries running in production. -

Stack Traces in Haskell
Stack Traces in Haskell Master of Science Thesis ARASH ROUHANI Chalmers University of Technology Department of Computer Science and Engineering G¨oteborg, Sweden, March 2014 The Author grants to Chalmers University of Technology and University of Gothen- burg the non-exclusive right to publish the Work electronically and in a non-commercial purpose make it accessible on the Internet. The Author warrants that he/she is the author to the Work, and warrants that the Work does not contain text, pictures or other material that violates copyright law. The Author shall, when transferring the rights of the Work to a third party (for example a publisher or a company), acknowledge the third party about this agreement. If the Author has signed a copyright agreement with a third party regarding the Work, the Author warrants hereby that he/she has obtained any necessary permission from this third party to let Chalmers University of Technology and University of Gothenburg store the Work electronically and make it accessible on the Internet. Stack Traces for Haskell A. ROUHANI c A. ROUHANI, March 2014. Examiner: J. SVENNINGSSON Chalmers University of Technology University of Gothenburg Department of Computer Science and Engineering SE-412 96 G¨oteborg Sweden Telephone + 46 (0)31-772 1000 Department of Computer Science and Engineering Department of Computer Science and Engineering G¨oteborg, Sweden March 2014 Abstract This thesis presents ideas for how to implement Stack Traces for the Glasgow Haskell Compiler. The goal is to come up with an implementation with such small overhead that organizations do not hesitate to use it for their binaries running in production. -

Addressing Failures in Exascale Computing Marc Snir Argonne National Laboratory, [email protected]
University of Nebraska - Lincoln DigitalCommons@University of Nebraska - Lincoln US Department of Energy Publications U.S. Department of Energy 2014 Addressing failures in exascale computing Marc Snir Argonne National Laboratory, [email protected] Robert W. Wisniewski Intel Corporation Jacob A. Abraham University of Texas at Austin Sarita V. Adve University of Illinois at Urbana-Champaign Saurabh Bachi Purdue University See next page for additional authors Follow this and additional works at: http://digitalcommons.unl.edu/usdoepub Snir, Marc; Wisniewski, Robert W.; Abraham, Jacob A.; Adve, Sarita V.; Bachi, Saurabh; Balaji, Pavan; Belak, Jim; Bose, Pradip; Cappello, Franck; Carlson, Bill; Chien, Andrew A.; Coteus, Paul; DeBardeleben, Nathan A.; Diniz, Pedro C.; Engelmann, Christian; Erez, Mattan; Fazzari, Saverio; Geist, Al; Gupta, Rinku; Johnson, Fred; Krishnamoorthy, Sriram; Leyffer, Sven; Liberty, Dean; Mitra, Subhasish; Munson, Todd; Schreiber, Rob; Stearley, Jon; and Van Hensbergen, Eric, "Addressing failures in exascale computing" (2014). US Department of Energy Publications. 360. http://digitalcommons.unl.edu/usdoepub/360 This Article is brought to you for free and open access by the U.S. Department of Energy at DigitalCommons@University of Nebraska - Lincoln. It has been accepted for inclusion in US Department of Energy Publications by an authorized administrator of DigitalCommons@University of Nebraska - Lincoln. Authors Marc Snir, Robert W. Wisniewski, Jacob A. Abraham, Sarita V. Adve, Saurabh Bachi, Pavan Balaji, Jim Belak, Pradip -
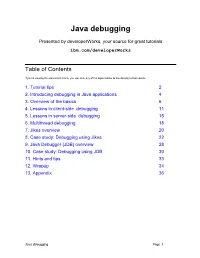
Java Debugging
Java debugging Presented by developerWorks, your source for great tutorials ibm.com/developerWorks Table of Contents If you're viewing this document online, you can click any of the topics below to link directly to that section. 1. Tutorial tips 2 2. Introducing debugging in Java applications 4 3. Overview of the basics 6 4. Lessons in client-side debugging 11 5. Lessons in server-side debugging 15 6. Multithread debugging 18 7. Jikes overview 20 8. Case study: Debugging using Jikes 22 9. Java Debugger (JDB) overview 28 10. Case study: Debugging using JDB 30 11. Hints and tips 33 12. Wrapup 34 13. Appendix 36 Java debugging Page 1 Presented by developerWorks, your source for great tutorials ibm.com/developerWorks Section 1. Tutorial tips Should I take this tutorial? This tutorial introduces Java debugging. We will cover traditional program and server-side debugging. Many developers don't realize how much getting rid of software bugs can cost. If you are a Java developer, this tutorial is a must-read. With the tools that are available today, it is vital that developers become just as good debuggers as they are programmers. This tutorial assumes you have basic knowledge of Java programming. If you have training and experience in Java programming, take this course to add to your knowledge. If you do not have Java programming experience, we suggest you take Introduction to Java for COBOL Programmers , Java for C/C++ Programmers , or another introductory Java course. If you have used debuggers with other programming languages, you can skip Section 3, "Overview of the Basics," which is geared for developers new to using debuggers. -

Backstop: a Tool for Debugging Runtime Errors Christian Murphy, Eunhee Kim, Gail Kaiser, Adam Cannon Dept
Backstop: A Tool for Debugging Runtime Errors Christian Murphy, Eunhee Kim, Gail Kaiser, Adam Cannon Dept. of Computer Science, Columbia University New York NY 10027 {cmurphy, ek2044, kaiser, cannon}@cs.columbia.edu ABSTRACT produces a detailed and helpful error message when an uncaught The errors that Java programmers are likely to encounter can runtime error (exception) occurs; it also provides debugging roughly be categorized into three groups: compile-time (semantic support by displaying the lines of code that are executed as a and syntactic), logical, and runtime (exceptions). While much program runs, as well as the values of any variables on those work has focused on the first two, there are very few tools that lines. exist for interpreting the sometimes cryptic messages that result Figures 1 and 2 compare the debugging output produced by from runtime errors. Novice programmers in particular have Backstop and the Java debugger jdb [19], respectively. Backstop difficulty dealing with uncaught exceptions in their code and the shows the changes to the variables in each line, and also displays resulting stack traces, which are by no means easy to understand. the values that were used to compute them. Additionally, it does We present Backstop, a tool for debugging runtime errors in Java not require the user to enter any commands in order to see that applications. This tool provides more user-friendly error messages information. On the other hand, jdb only provides “snapshots” of when an uncaught exception occurs, and also provides debugging the variable values on demand, without showing the results of support by allowing users to watch the execution of the program individual computations, and requires more user interaction. -

Could I Have a Stack Trace to Examine the Dependency Conflict Issue?
Could I Have a Stack Trace to Examine the Dependency Conflict Issue? Ying Wang∗, Ming Weny, Rongxin Wuyx, Zhenwei Liu∗, Shin Hwei Tanz, Zhiliang Zhu∗, Hai Yu∗ and Shing-Chi Cheungyx ∗ Northeastern University, Shenyang, China Email: {wangying8052, lzwneu}@163.com, {yuhai, zzl}@mail.neu.edu.cn y The Hong Kong University of Science and Technology, Hong Kong, China Email: {mwenaa, wurongxin, scc}@cse.ust.hk z Southern University of Science and Technology, Shenzhen, China Email: [email protected] Abstract—Intensive use of libraries in Java projects brings developers often want to have a stack trace to validate the potential risk of dependency conflicts, which occur when a risk of these warned DC issues. It echoes earlier findings that project directly or indirectly depends on multiple versions of stack traces provide useful information for debugging [9], the same library or class. When this happens, JVM loads one version and shadows the others. Runtime exceptions can [10]. We observe that developers can more effectively locate occur when methods in the shadowed versions are referenced. the problem of those DC issues accompanied by stack traces Although project management tools such as Maven are able to or test cases than those without. For instance, a DC issue give warnings of potential dependency conflicts when a project Issue #57 [11] was reported to project FasterXML with is built, developers often ask for crashing stack traces before details of the concerning library dependencies and versions. examining these warnings. It motivates us to develop RIDDLE, an automated approach that generates tests and collects crashing Nevertheless, the project developer asked for a stack trace to stack traces for projects subject to risk of dependency conflicts. -

Zero-Overhead Deterministic Exceptions: Throwing Values
Zero-overhead deterministic exceptions: Throwing values Document Number: P0709 R2 Date: 2018-10-06 Reply-to: Herb Sutter ([email protected]) Audience: EWG, LEWG Abstract Divergent error handling has fractured the C++ community into incompatible dialects, because of long-standing unresolved problems in C++ exception handling. This paper enumerates four interrelated problems in C++ error handling. Although these could be four papers, I believe it is important to consider them together. §4.1: “C++” projects commonly ban exceptions, largely because today’s dynamic exception types violate zero- overhead and determinism, which means those are not really C++ projects but use an incompatible dialect. — We must at minimum enable all C++ projects to enable exception handling and to use the standard library. This paper proposes extending C++’s exception handling to let functions declare that they throw a statically specified type by value, which is zero-overhead and fully deterministic. This doubles down on C++’s core strength of effi- cient value semantics, as we did with move semantics as a C++11 marquee feature. §4.2: Contract violations are not recoverable run-time errors and so should not be reported as such (as either exceptions or error codes). — We must express preconditions, but using a tool other than exceptions. This pa- per supports the change, already in progress, to migrate the standard library away from throwing exceptions for precondition violations, and eventually to contracts. §4.3: Heap exhaustion (OOM) is not like other recoverable run-time errors and should be treated separately. — We must be able to write OOM-hardened code, but we cannot do it with all failed memory requests throwing bad_alloc. -

Could I Have a Stack Trace to Examine the Dependency Conflict
Could I Have a Stack Trace to Examine the Dependency Conflict Issue? Ying Wang∗, Ming Weny, Rongxin Wuyx, Zhenwei Liu∗, Shin Hwei Tanz, Zhiliang Zhu∗, Hai Yu∗ and Shing-Chi Cheungyx ∗ Northeastern University, Shenyang, China Email: {wangying8052, lzwneu}@163.com, {yuhai, zzl}@mail.neu.edu.cn y The Hong Kong University of Science and Technology, Hong Kong, China Email: {mwenaa, wurongxin, scc}@cse.ust.hk z Southern University of Science and Technology, Shenzhen, China Email: [email protected] Abstract—Intensive use of libraries in Java projects brings developers often want to have a stack trace to validate the potential risk of dependency conflicts, which occur when a risk of these warned DC issues. It echoes earlier findings that project directly or indirectly depends on multiple versions of stack traces provide useful information for debugging [9], the same library or class. When this happens, JVM loads one version and shadows the others. Runtime exceptions can [10]. We observe that developers can more effectively locate occur when methods in the shadowed versions are referenced. the problem of those DC issues accompanied by stack traces Although project management tools such as Maven are able to or test cases than those without. For instance, a DC issue give warnings of potential dependency conflicts when a project Issue #57 [11] was reported to project FasterXML with is built, developers often ask for crashing stack traces before details of the concerning library dependencies and versions. examining these warnings. It motivates us to develop RIDDLE, an automated approach that generates tests and collects crashing Nevertheless, the project developer asked for a stack trace to stack traces for projects subject to risk of dependency conflicts.