Virtual Firewall Security on Virtual Machines in Cloud Environment
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Physical Or Virtual Firewall for Perimeter Protection in Cloud Computer Infrastructure
16th INTERNATIONAL CONFERENCE ON INFORMATION SYSTEMS & TECHNOLOGY MANAGEMENT - CONTECSI - 2019 DOI: 10.5748/16CONTECSI/ITM-6115 PHYSICAL OR VIRTUAL FIREWALL FOR PERIMETER PROTECTION IN CLOUD COMPUTER INFRASTRUCTURE Thiago Mello Valcesia - IPT - Instituto de Pesquisas Tecnológicas - [email protected] Antonio Luiz Rigo - IPT - Instituto de Pesquisas Tecnológicas - [email protected] SUMMARY This article presents an examination of the different types of firewalls geared toward protecting Datacenters. The idea is to perform a survey of the different ways of installation, the safety perceived by customers, the positive and negative points of each model and the market trends for perimeter protection. In addition, it is intended to categorize rules, protection filters, application inspection criteria and services offered by firewalls, by analyzing the various protection schemes available in firewalls, regardless of the structure as a service in Cloud adopted. Keywords: Physical firewall, Virtual firewall, Cloud firewall, Security, Cloud Computing. INTRODUCTION The term Digital Security is increasingly present in our daily lives. The need to protect computers or prevent corporate networks from receiving unnecessary traffic, improper access, and unknown packets, coupled with the concern of professional information security staff about content accessed by Internet users, make data control a vital task. Firewall is much more than a "fire wall" isolating the company network from the external world represented by the Internet. The Firewall function is therefore essential to raise the level of security of the internal environment, protecting it from external attacks, increasing security and reducing the vulnerability of the local network. There are currently three Firewall alternatives to install on enterprise networks that aggregate cloud network segments: 1. -
PCI DSS Virtualization Guidelines
Standard: PCI Data Security Standard (PCI DSS) Version: 2.0 Date: June 2011 Author: Virtualization Special Interest Group PCI Security Standards Council Information Supplement: PCI DSS Virtualization Guidelines Information Supplement • PCI DSS Virtualization Guidelines • June 2011 Table of Contents 1 Introduction ....................................................................................................................... 3 1.1 Audience ................................................................................................................ 3 1.2 Intended Use .......................................................................................................... 4 2 Virtualization Overview .................................................................................................... 5 2.1 Virtualization Concepts and Classes ..................................................................... 5 2.2 Virtual System Components and Scoping Guidance ............................................. 7 3 Risks for Virtualized Environments .............................................................................. 10 3.1 Vulnerabilities in the Physical Environment Apply in a Virtual Environment ....... 10 3.2 Hypervisor Creates New Attack Surface ............................................................. 10 3.3 Increased Complexity of Virtualized Systems and Networks .............................. 11 3.4 More Than One Function per Physical System ................................................... 11 3.5 Mixing VMs of -

Exploiting Cloud Management Services As an Information Leakage Channel
I Heard It through the Firewall: Exploiting Cloud Management Services as an Information Leakage Channel Hyunwook Baek∗ Eric Eide [email protected] [email protected] University of Utah University of Utah Salt Lake City, UT, USA Salt Lake City, UT, USA Robert Ricci Jacobus Van der Merwe [email protected] [email protected] University of Utah University of Utah Salt Lake City, UT, USA Salt Lake City, UT, USA ABSTRACT Though there has been much study of information leakage chan- nels exploiting shared hardware resources (memory, cache, and disk) in cloud environments, there has been less study of the ex- ploitability of shared software resources. In this paper, we analyze the exploitability of cloud networking services (which are shared among cloud tenants) and introduce a practical method for build- ing information leakage channels by monitoring workloads on the cloud networking services through the virtual firewall. We also demonstrate the practicality of this attack by implementing two different covert channels in OpenStack as well as a new classof side channels that can eavesdrop on infrastructure-level events. By utilizing a Long Short-Term Memory (LSTM) neural network model, our side channel attack could detect infrastructure level VM creation/termination events with 93.3% accuracy. CCS CONCEPTS • Security and privacy → Distributed systems security; Fire- walls; • Computer systems organization → Cloud computing; • Networks → Cloud computing; Figure 1: Resource sharing of two requests KEYWORDS cloud management, cloud security, side channel, OpenStack 1 INTRODUCTION However, shared resources also cause interference among cloud tenants and can even be exploited as information leakage channels Resource sharing is a fundamental part of cloud computing. -
Vgw Virtual Gateway Virtual Gateway Virtual
vGW Virtual Gateway Administration Guide Release 4.5 Service Pack 1 Copyright © 2011, Juniper Networks, Inc Juniper Networks, Inc. 1194 North Mathilda Avenue Sunnyvale, California 94089 USA 408-745-2000 www.juniper.net Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered trademarks of Juniper Networks, Inc. in the United States and other countries. The Juniper Networks Logo, the Junos logo, and JunosE are trademarks of Juniper Networks, Inc. All other trademarks, service marks, registered trademarks, or registered service marks are the property of their respective owners. Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify, transfer, or otherwise revise this publication without notice. Products made or sold by Juniper Networks or components thereof might be covered by one or more of the following patents that are owned by or licensed to Juniper Networks: U.S. Patent Nos. 5,473,599, 5,905,725, 5,909,440, 6,192,051, 6,333,650, 6,359,479, 6,406,312, 6,429,706, 6,459,579, 6,493,347, 6,538,518, 6,538,899, 6,552,918, 6,567,902, 6,578,186, and 6,590,785. SOFTWARE LICENSE The terms and conditions for using this software are described in the software license contained in the acknowledgment to your purchase order or, to the extent applicable, to any reseller agreement or end-user purchase agreement executed between you and Juniper Networks. By using this software, you indicate that you understand and agree to be bound by those terms and conditions. -

Who Is Ivan Pepelnjak (@Ioshints)
Virtual Firewalls Ivan Pepelnjak ([email protected]) NIL Data Communications Who is Ivan Pepelnjak (@ioshints) • Networking engineer since 1985 • Focus: real-life deployment of advanced technologies • Chief Technology Advisor @ NIL Data Communications • Consultant, blogger (blog.ioshints.info), book and webinar author • Teaching “Scalable Web Application Design” at University of Ljubljana Current interests: • Large-scale data centers and network virtualization • Networking solutions for cloud computing • Scalable application design • Core IP routing/MPLS, IPv6, VPN 2 © ipSpace.net / NIL Data Communications 2013 Virtual Firewalls Virtualization Webinars on ipSpace.net Coming in 2013 Coming in 2013 vSphere 5 Update Overlay Virtual Networking Coming in 2013 Virtual Firewalls OpenFlow and SDN Use Cases VXLAN Deep Dive OpenFlow VMware Networking Cloud Computing Networking Introduction to Virtualized Networking Availability Other options • Live sessions • Customized webinars • Recordings of individual webinars • ExpertExpress • Yearly subscription • On-site workshops 3 InterMore© ipSpace.net- DCinformation /FCoE NIL Data Communications has @ very2013 http://www.ipSpace.net/Webinars limitedVirtual use Firewalls and requires no bridging Firewalls Used To Be Easy Packet filters Application-level firewalls (WAF) Firewalls Stateful Load firewalls balancers? 4 © ipSpace.net / NIL Data Communications 2013 Virtual Firewalls Routed or Bridged? Routed (inter-subnet) Transparent (bridged) • Packet filtering and IP routing • Packet filtering and bridging -

The Virtual Firewall
The Virtual Firewall Vassilis Prevelakis Computer Science Department Drexel University 1. Introduction The trend towards portable computing means that the traditional security perimeter architecture (where a firewall protects computers in the LAN by controlling access to the outside world) is rapidly becoming obsolete. This has resulted in a number of products described as “personal firewalls” that control that computer’s access to the network and hence can protect it in the same way as a traditional firewall. Existing systems such as Windows and most Unix and Unix-like systems already provide security features that can be used to implement firewall functionality on every machine. However, the difficulty of securing general purpose operating systems has im- peded the widespread use of this approach. Moreover, it is difficult to ensure that a secured sys- tem remains secure after the user has had the opportunity to install software and perform recon- figurations and upgrades. Recognizing the futility of attempting to secure the user machines themselves, in [Prev03, Denk99] the authors proposed the use of a portable “shrink-wrapped” firewall. This was a sepa- rate machine running an embedded system that included firewall capabilities and was intended to be placed between the general purpose computer and the network. The problem of securing the firewall became much simpler as it utilized a special-purpose firewall platform with a highly controlled architecture. Sadly, the proposal saw limited adoption because carrying around yet another device is expensive and inconvenient. To make matters worse, if the external device is lost or damaged the user will be presented with a dilemma: remain disconnected from the net- work until the firewall box is replaced, or accept the risk and connect the laptop directly to the unprotected network. -

Secure Data Center Networking with Open Vswitch
Secure Data Center Networking with Open vSwitch Pa Pa Hlaing University of Computer Studies, Yangon [email protected] Abstract agility and isolation of VMs. Most physical switches deployed in conventional DCNs are not designed for either supporting such unique VM Data centers have become the next- requirements or flexible enough to augment new generation computing platforms for enterprises functionalities [7]. At the same time, VM and Internet users. This is primarily due to the networking has inherently unique characteristics, economic and technical advantages of resource such as the awareness of the migration of VMs sharing in data centers. By sharing computing and their multicast membership. Therefore, much and storage resources through services such as research has begun exploring the opportunity to cloud computing or software-as-a-service (SaaS), introduce a new, flexible and programmable users can amortize the cost of hardware and networking layer based on the knowledge of software. Because of the virtualization of VMs. resources, a new virtualized network access layer Modern data center networks consist of both has been introduced to interconnect VMs within physical networks connected by switches and the data centers. In data center, hosts have been virtual networks formed by VMs running inside recently employed virtual switch to interconnect physical hosts. Inside one computer, many VMs virtual machines (VMs) within data center can exist (as many as 120 VMs per host), each of networks. Virtual Switch is essential to control which has at least one virtual network interface and manage VM within the hosts. Open vSwitch, card (VNIC). The VNICs communicate with a network switch specifically built for Xen external networks through the host’s physical virtualization environment is presented. -

S32 - a Primer on Virtualization Tom Ray
S32 - A Primer on Virtualization Tom Ray A Primer on Virtualization Ignoring the man behind the curtain? Agenda • Top 3 things you need to know about Virtualization when you Audit it, & your IT & IT security groups. – What IS virtualization? – What are the issues? – What is a reasonable, “AUDIT-READY” secure Reference Architecture? • Discuss how to Audit a virtualized IT 2 1 What is Virtualization? 3 Some Observations • It is NOT new (but some developments are) • It is an “already expected ” cost containment technology in many IT departments • Before you can answer “what is” you need to identify which kind you are interested in • It is jargon and acronym-rich, & it’s vendor balkanized • It is (still) immature and so nothing does it full justice – no one approach, no set of standards, or vendor, or architecture, or set of components, or framework, or technology, or technique, or regulations, etc. • It will radically impact how you “do” IT & environments 4 2 What are the Issues? 5 In Summary 1. Disconnect between Logical and Physical is exploited for the technology’s benefit; not the humans’ 2. Dynamism 3. Blur & Ease of Sprawl – Increased Complexity & Interdependencies – Overlap of various roles’ capabilities 4. Resource equation is still a zero-sum game (at best) – Same staff (IT & Business) – Same Procedures? , … same Tools? 5. The technology’s Immaturity 6. Our IT Operations Immaturity 7. The CIO’s Drivers (expectations, motivations & intentions) 6 3 What is a reasonable, “AUDIT‐READY” secure Reference Architecture? 7 2 Security Reference Architectures Durable Non Compliance People / Organizations X Processes / Tasks / RnR Metrics? Threat Technologies / Constructs X Mitigation Build Specs / Contracts / Metrics? Documentation Technical-Trust Enablement 1. -
Juniper Networks Inc
JUNIPER NETWORKS INC FORM 10-K (Annual Report) Filed 02/26/13 for the Period Ending 12/31/12 Address 1194 NORTH MATHILDA AVE SUNNYVALE, CA 94089 Telephone 4087452000 CIK 0001043604 Symbol JNPR SIC Code 3576 - Computer Communications Equipment Industry Communications Equipment Sector Technology Fiscal Year 12/31 http://www.edgar-online.com © Copyright 2013, EDGAR Online, Inc. All Rights Reserved. Distribution and use of this document restricted under EDGAR Online, Inc. Terms of Use. Table of Contents UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 Form 10-K (Mark One) ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the fiscal year ended December 31, 2012 OR TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the transition period from__________ to____________ Commission file number 001-34501 JUNIPER NETWORKS, INC. (Exact name of registrant as specified in its charter) Delaware 77-0422528 (State or other jurisdiction of incorporation or organization) (IRS Employer Identification No.) 1194 North Mathilda Avenue Sunnyvale, California 94089 (408) 745-2000 (Address of principal executive offices)(Zip Code) ( Registrant's telephone number, including area code) Securities registered pursuant to Section 12(b) of the Act: Title of Each Class Name of Each Exchange on Which Registered Common Stock, par value $0.00001 per share New York Stock Exchange Securities registered pursuant to Section 12(g) of the Act: None Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. -
Juniper Networks Inc
JUNIPER NETWORKS INC FORM 10-K (Annual Report) Filed 02/26/14 for the Period Ending 12/31/13 Address 1194 NORTH MATHILDA AVE SUNNYVALE, CA 94089 Telephone 4087452000 CIK 0001043604 Symbol JNPR SIC Code 3576 - Computer Communications Equipment Industry Communications Equipment Sector Technology Fiscal Year 12/31 http://www.edgar-online.com © Copyright 2014, EDGAR Online, Inc. All Rights Reserved. Distribution and use of this document restricted under EDGAR Online, Inc. Terms of Use. UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 FORM 10-K (Mark One) ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the fiscal year ended December 31, 2013 or TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 For the transition period from__________ to____________ Commission file number 001-34501 JUNIPER NETWORKS, INC. (Exact name of registrant as specified in its charter) Delaware 77-0422528 (State or other jurisdiction of incorporation or organization) (I.R.S. Employer Identification No.) 1194 North Mathilda Avenue Sunnyvale, California 94089 (Address of principal executive offices) (Zip code) (408) 745-2000 (Registrant's telephone number, including area code) Securities registered pursuant to Section 12(b) of the Act: Title of Each Class Name of Each Exchange on Which Registered Common Stock, par value $0.00001 per share New York Stock Exchange Securities registered pursuant to Section 12(g) of the Act: None Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. -

Dynamic and Application-Aware Provisioning of Chained Virtual Security Network Functions
This is the author’s version of an article that has been published in IEEE Transactions on Network and Service Management. Changes were made to this version by the publisher prior to publication. The final version of record is available at https://doi.org/10.1109/TNSM.2019.2941128. The source code associated with this project is available at https://github.com/doriguzzi/pess-security. Dynamic and Application-Aware Provisioning of Chained Virtual Security Network Functions Roberto Doriguzzi-Corinα, Sandra Scott-Haywardβ, Domenico Siracusaα, Marco Saviα, Elio Salvadoriα αCREATE-NET, Fondazione Bruno Kessler - Italy β CSIT, Queen’s University Belfast - Northern Ireland Abstract—A promising area of application for Network Func- connected to the network through an automated and logically tion Virtualization is in network security, where chains of Virtual centralized management system. Security Network Functions (VSNFs), i.e., security-specific virtual functions such as firewalls or Intrusion Prevention Systems, The centralized management system, called NFV Manage- can be dynamically created and configured to inspect, filter ment and Orchestration (NFV MANO), controls the whole or monitor the network traffic. However, the traffic handled life-cycle of each VNF. In addition, the NFV MANO can by VSNFs could be sensitive to specific network requirements, dynamically provision complex network services in the form such as minimum bandwidth or maximum end-to-end latency. of sequences (often called chains) of VNFs. Indeed, Network Therefore, the decision on which VSNFs should apply for a given application, where to place them and how to connect them, Service Chaining (NSC) is a technique for selecting subsets should take such requirements into consideration. -
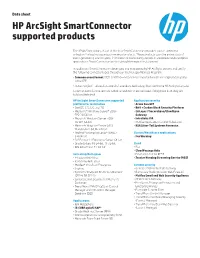
HP Arcsight Smartconnector Supported Products Data Sheet
Data sheet HP ArcSight SmartConnector supported products The HP ArcSight library of out-of-the-box SmartConnectors provides source-optimized collection for leading security commercial products. These products span the entire stack of event-generating source types, from network and security devices to databases and enterprise applications. SmartConnectors are the default listing in this document. In addition to SmartConnectors developed and maintained by HP ArcSight, we test and certify the following connector types through our Technology Alliances Program: • Common event format (CEF) Certified—helps ensure event information is captured properly in the CEF • Action Certified—allows for control of a vendor’s technology from within the HP ArcSight Console Common event format are in bold below and Action are Italicized. If they have both they are bold and Italicized. HP ArcSight SmartConnector supported Application security platform for installation • Arxan GuardIT • CentOS-6.5, 6.6, and 7.0 • Bit9 + Carbon Black Security Platform • Microsoft® Windows Server® 2008 • CA Layer 7 SecureSpan/CloudSpan SP2 32/64-bit Gateway • Microsoft Windows Server 2008 • Intralinks VIA R2 SP1 64-bit • McAfee Application Control (Solidcore) • Microsoft Windows Server 2012 • RSA Silver Tail Systems Forensics Standard 64-bit, R2 64-bit • Red Hat® Enterprise Linux® (RHEL) Clinical/Healthcare applications 6.4 64-bit • FairWarning • SUSE Linux 11 Enterprise Server 64-bit • Oracle Solaris 10 64-bit, 11 32-bit Cloud • IBM AIX version 7.1 64-bit • Box • CloudPassage