Mac OS X Server Command-Line Administration for Version 10.4 Or Later Second Edition
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The LAS File Format Contains a Header Block, Variable Length
LAS Specification Version 1.2 Approved by ASPRS Board 09/02/2008 LAS 1.2 1 LAS FORMAT VERSION 1.2: This document reflects the second revision of the LAS format specification since its initial version 1.0 release. Version 1.2 retains the same structure as version 1.1 including identical field alignment. LAS 1.1 file Input/Output (I/O) libraries will require slight modifications in order to be compliant with this revision. A LAS 1.1 Reader will read LAS 1.2 (without the new enhancements) with no modifications. A detailed change document that provides both an overview of the changes in the specification as well as the motivation behind each change is available from the ASPRS website in the LIDAR committee section. The additions of LAS 1.2 include: • GPS Absolute Time (as well as GPS Week Time) – LAS 1.0 and LAS 1.1 specified GPS “Week Time” only. This meant that GPS time stamps “rolled over” at midnight on Saturday. This makes processing of LIDAR flight lines that span the time reset difficult. LAS 1.2 allows both GPS Week Time and Absolute GPS Time (POSIX) stamps to be used. • Support for ancillary image data on a per point basis. You can now specify Red, Green, Blue image data on a point by point basis. This is encapsulated in two new point record types (type 2 and type 3). LAS FORMAT DEFINITION: The LAS file is intended to contain LIDAR point data records. The data will generally be put into this format from software (e.g. -
Key Aspects in 3D File Format Conversions
Key Aspects in 3D File Format Conversions Kenton McHenry and Peter Bajcsy Image Spatial Data Analysis Group, NCSA Presented by: Peter Bajcsy National Center for Supercomputing Applications University of Illinois at Urbana-Champaign Outline • Introduction • What do we know about 3D file formats? • Basic Archival Questions • Is there an optimal format to convert to? • Can we quantify 3D noise introduced during conversions? • NCSA Polyglot to Support Archival Processes • Automation of File Format Conversions • Quality of File Format Conversions • Scalability with Volume • Conclusions • Live demonstration Introduction Introduction to 3D File Format Reality *.k3d *.pdf (*.prc, *.u3d) *.ma, *.mb, *.mp *.w3d *.lwo *.c4d *.dwg *.blend *.iam *.max, *.3ds Introduction: Our Survey about 3D Content • Q: How Many 3D File Formats Exist? • A: We have found more than 140 3D file formats. Many are proprietary file formats. Many are extremely complex (1,200 and more pages of specifications). • Q: How Many Software Packages Support 3D File Format Import, Export and Display? • A: We have documented about 16 software packages. There are many more. Most of them are proprietary/closed source code. Many contain incomplete support of file specifications. Examples of Formats and Stored Content Format Geometry Appearance Scene Animation Faceted Parametric CSG B-Rep Color Material Texture Bump Lights Views Trans. Groups 3ds √ √ √ √ √ √ √ √ √ igs √ √ √ √ √ √ √ lwo √ √ √ √ √ √ obj √ √ √ √ √ √ √ ply √ √ √ √ √ stp √ √ √ √ √ √ wrl √ √ √ √ √ √ √ √ √ √ √ u3d √ √ √ √ √ -
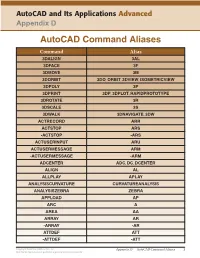
Autocad Command Aliases
AutoCAD and Its Applications Advanced Appendix D AutoCAD Command Aliases Command Alias 3DALIGN 3AL 3DFACE 3F 3DMOVE 3M 3DORBIT 3DO, ORBIT, 3DVIEW, ISOMETRICVIEW 3DPOLY 3P 3DPRINT 3DP, 3DPLOT, RAPIDPROTOTYPE 3DROTATE 3R 3DSCALE 3S 3DWALK 3DNAVIGATE, 3DW ACTRECORD ARR ACTSTOP ARS -ACTSTOP -ARS ACTUSERINPUT ARU ACTUSERMESSAGE ARM -ACTUSERMESSAGE -ARM ADCENTER ADC, DC, DCENTER ALIGN AL ALLPLAY APLAY ANALYSISCURVATURE CURVATUREANALYSIS ANALYSISZEBRA ZEBRA APPLOAD AP ARC A AREA AA ARRAY AR -ARRAY -AR ATTDEF ATT -ATTDEF -ATT Copyright Goodheart-Willcox Co., Inc. Appendix D — AutoCAD Command Aliases 1 May not be reproduced or posted to a publicly accessible website. Command Alias ATTEDIT ATE -ATTEDIT -ATE, ATTE ATTIPEDIT ATI BACTION AC BCLOSE BC BCPARAMETER CPARAM BEDIT BE BLOCK B -BLOCK -B BOUNDARY BO -BOUNDARY -BO BPARAMETER PARAM BREAK BR BSAVE BS BVSTATE BVS CAMERA CAM CHAMFER CHA CHANGE -CH CHECKSTANDARDS CHK CIRCLE C COLOR COL, COLOUR COMMANDLINE CLI CONSTRAINTBAR CBAR CONSTRAINTSETTINGS CSETTINGS COPY CO, CP CTABLESTYLE CT CVADD INSERTCONTROLPOINT CVHIDE POINTOFF CVREBUILD REBUILD CVREMOVE REMOVECONTROLPOINT CVSHOW POINTON Copyright Goodheart-Willcox Co., Inc. Appendix D — AutoCAD Command Aliases 2 May not be reproduced or posted to a publicly accessible website. Command Alias CYLINDER CYL DATAEXTRACTION DX DATALINK DL DATALINKUPDATE DLU DBCONNECT DBC, DATABASE, DATASOURCE DDGRIPS GR DELCONSTRAINT DELCON DIMALIGNED DAL, DIMALI DIMANGULAR DAN, DIMANG DIMARC DAR DIMBASELINE DBA, DIMBASE DIMCENTER DCE DIMCONSTRAINT DCON DIMCONTINUE DCO, DIMCONT DIMDIAMETER DDI, DIMDIA DIMDISASSOCIATE DDA DIMEDIT DED, DIMED DIMJOGGED DJO, JOG DIMJOGLINE DJL DIMLINEAR DIMLIN, DLI DIMORDINATE DOR, DIMORD DIMOVERRIDE DOV, DIMOVER DIMRADIUS DIMRAD, DRA DIMREASSOCIATE DRE DIMSTYLE D, DIMSTY, DST DIMTEDIT DIMTED DIST DI, LENGTH DIVIDE DIV DONUT DO DRAWINGRECOVERY DRM DRAWORDER DR Copyright Goodheart-Willcox Co., Inc. -

Mac Keyboard Shortcuts Cut, Copy, Paste, and Other Common Shortcuts
Mac keyboard shortcuts By pressing a combination of keys, you can do things that normally need a mouse, trackpad, or other input device. To use a keyboard shortcut, hold down one or more modifier keys while pressing the last key of the shortcut. For example, to use the shortcut Command-C (copy), hold down Command, press C, then release both keys. Mac menus and keyboards often use symbols for certain keys, including the modifier keys: Command ⌘ Option ⌥ Caps Lock ⇪ Shift ⇧ Control ⌃ Fn If you're using a keyboard made for Windows PCs, use the Alt key instead of Option, and the Windows logo key instead of Command. Some Mac keyboards and shortcuts use special keys in the top row, which include icons for volume, display brightness, and other functions. Press the icon key to perform that function, or combine it with the Fn key to use it as an F1, F2, F3, or other standard function key. To learn more shortcuts, check the menus of the app you're using. Every app can have its own shortcuts, and shortcuts that work in one app may not work in another. Cut, copy, paste, and other common shortcuts Shortcut Description Command-X Cut: Remove the selected item and copy it to the Clipboard. Command-C Copy the selected item to the Clipboard. This also works for files in the Finder. Command-V Paste the contents of the Clipboard into the current document or app. This also works for files in the Finder. Command-Z Undo the previous command. You can then press Command-Shift-Z to Redo, reversing the undo command. -

Mac OS X Server Administrator's Guide
034-9285.S4AdminPDF 6/27/02 2:07 PM Page 1 Mac OS X Server Administrator’s Guide K Apple Computer, Inc. © 2002 Apple Computer, Inc. All rights reserved. Under the copyright laws, this publication may not be copied, in whole or in part, without the written consent of Apple. The Apple logo is a trademark of Apple Computer, Inc., registered in the U.S. and other countries. Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, AppleScript, AppleShare, AppleTalk, ColorSync, FireWire, Keychain, Mac, Macintosh, Power Macintosh, QuickTime, Sherlock, and WebObjects are trademarks of Apple Computer, Inc., registered in the U.S. and other countries. AirPort, Extensions Manager, Finder, iMac, and Power Mac are trademarks of Apple Computer, Inc. Adobe and PostScript are trademarks of Adobe Systems Incorporated. Java and all Java-based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Netscape Navigator is a trademark of Netscape Communications Corporation. RealAudio is a trademark of Progressive Networks, Inc. © 1995–2001 The Apache Group. All rights reserved. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. 062-9285/7-26-02 LL9285.Book Page 3 Tuesday, June 25, 2002 3:59 PM Contents Preface How to Use This Guide 39 What’s Included -

Alias Manager 4
CHAPTER 4 Alias Manager 4 This chapter describes how your application can use the Alias Manager to establish and resolve alias records, which are data structures that describe file system objects (that is, files, directories, and volumes). You create an alias record to take a “fingerprint” of a file system object, usually a file, that you might need to locate again later. You can store the alias record, instead of a file system specification, and then let the Alias Manager find the file again when it’s needed. The Alias Manager contains algorithms for locating files that have been moved, renamed, copied, or restored from backup. Note The Alias Manager lets you manage alias records. It does not directly manipulate Finder aliases, which the user creates and manages through the Finder. The chapter “Finder Interface” in Inside Macintosh: Macintosh Toolbox Essentials describes Finder aliases and ways to accommodate them in your application. ◆ The Alias Manager is available only in system software version 7.0 or later. Use the Gestalt function, described in the chapter “Gestalt Manager” of Inside Macintosh: Operating System Utilities, to determine whether the Alias Manager is present. Read this chapter if you want your application to create and resolve alias records. You might store an alias record, for example, to identify a customized dictionary from within a word-processing document. When the user runs a spelling checker on the document, your application can ask the Alias Manager to resolve the record to find the correct dictionary. 4 To use this chapter, you should be familiar with the File Manager’s conventions for Alias Manager identifying files, directories, and volumes, as described in the chapter “Introduction to File Management” in this book. -

Dropdmg 3.6.2 Manual
DropDMG 3.6.2 Manual C-Command Software c-command.com February 16, 2021 Contents 1 Introduction 4 1.1 Feature List..............................................4 2 Installing and Updating 6 2.1 Requirements.............................................6 2.2 Installing DropDMG.........................................7 2.3 Updating From a Previous Version.................................7 2.4 Reinstalling a Fresh Copy......................................8 2.5 Uninstalling DropDMG.......................................9 2.6 Security & Privacy Access......................................9 3 Using DropDMG 13 3.1 Basics................................................. 13 3.2 Making a Bootable Device Image of a Hard Drive......................... 14 3.3 Backing Up Your Files to CD/DVD................................ 16 3.4 Burning Backups of CDs/DVDs................................... 17 3.5 Restoring Files and Disks...................................... 18 3.6 Making Images With Background Pictures............................. 19 3.7 Protecting Your Files With Encryption............................... 20 3.8 Transferring Files Securely...................................... 21 3.9 Sharing Licenses and Layouts.................................... 21 3.10 Splitting a File or Folder Into Pieces................................ 22 3.11 Creating a DropDMG Quick Action................................ 22 4 Menus 23 4.1 The DropDMG Menu........................................ 23 4.1.1 About DropDMG...................................... 23 4.1.2 Software -

Well Known TCP and UDP Ports Used by Apple Software Products
Well known TCP and UDP ports used by Apple Languages English software products Symptoms Learn more about TCP and UDP ports used by Apple products, such as OS X, OS X Server, Apple Remote Desktop, and iCloud. Many of these are referred to as "well known" industry standard ports. Resolution About this table The Service or Protocol Name column lists services registered with the Internet Assigned Numbers Authority (http://www.iana.org/), except where noted as "unregistered use." The names of Apple products that use these services or protocols appear in the Used By/Additional Information column. The RFC column lists the number of the Request For Comment document that defines the particular service or protocol, which may be used for reference. RFC documents are maintained by RFC Editor (http://www.rfc- editor.org/). If multiple RFCs define a protocol, there may only be one listed here. This article is updated periodically and contains information that is available at time of publication. This document is intended as a quick reference and should not be regarded as comprehensive. Apple products listed in the table are the most commonly used examples, not a comprehensive list. For more information, review the Notes below the table. Tip: Some services may use two or more ports. It is recommend that once you've found an instance of a product in this list, search on the name (Command-F) and then repeat (Command-G) to locate all occurrences of the product. For example, VPN service may use up to four diferent ports: 500, 1701, 1723, and 4500. -

A Review of HTTP Live Streaming
A Review of HTTP Live Streaming Andrew Fecheyr-Lippens ([email protected]) Abstract TODO: write abstract January 2010 A Review of HTTP Live Streaming Andrew Fecheyr-Lippens Table of Contents 1. Introduction to streaming media 3 On-demand vs live streaming 3 2. Popular solutions 5 RTP/RTSP 5 Adobe Flash Media Streaming Server 5 3. Apple’s HTTP Live Streaming 7 HTTP Streaming Architecture 7 Server Components 9 Media Segment Files 10 Distribution Components 11 Client Component 11 Using HTTP Live Streaming 12 Session Types 12 Content Protection 13 Caching and Delivery Protocols 14 Stream Alternatives 14 Failover Protection 15 4. Critical Comparison 16 Ease of Setup 16 HTTP Live Streaming - Apple tools 17 HTTP Live Streaming - Open Source tools 17 RTP/RTSP - Darwin Streaming Server 18 Compatibility 19 Features 20 Ease of Distribution 21 Cost 22 5. Conclusion 23 6. Appendices 25 Appendix 1 - Index file generated by Apple tool 25 Appendix 2 - Configuration file for the O.S. toolchain 26 Appendix 3 - Index files generated by O.S. toolchain 27 Appendix 4 - Web server access log 28 Appendix 5 - Akamai HD for iPhone architecture 29 7. References 30 2 A Review of HTTP Live Streaming Andrew Fecheyr-Lippens 1.Introduction to streaming media In the early 1990s consumer-grade personal computers became powerful enough to display video and playback audio. These early forms of computer media were usually delivered over non-streaming channels, by playing it back from CD-ROMs or by downloading a digital file from a remote web server and saving it to a local hard drive on the end user's computer. -

OS X Support Essentials 10.9 Apple Pro Training Series
Apple Pro Training Series: OS X Support Essentials 10.9 Apple Pro Training Series Training Apple Pro Network Configuration Locations: One selected by user Automatic Work Home Test Ethernet Wi-Fi Ethernet 2 FireWire VPN Services: Multiple services activate and prioritized based on service order Understand OS X Mavericks underlying technologies, Configurestand-alone and networked Mac Troubleshoot software and hardware issues software components, and industry-standard protocols. computers with step-by-step instructions. using Apple-recommended procedures and tools. OS X Mavericks Supporting and Troubleshooting OS X Support Essentials 10.9 The Apple-Certified Way to Learn This is the official curriculum of the Apple Mavericks 101: OS X The Apple Pro Training Series is both a self-paced Support Essentials 10.9 course and preparation for Apple learning tool and the official curriculum of the Apple Training and Certified Support Professional (ACSP) 10.9 certification— Certification program. Upon completing the course material in this as well as a top-notch primer for anyone who needs to support, book, you can become an Apple Certified Support Professional by troubleshoot, or optimize OS X Mavericks. This guide provides passing the OS X Support Essentials 10.9 Exam. Work through this comprehensive coverage of Mavericks and is part of the Apple book as self-study material or attend a class at an Apple Authorized Pro Training series—the only Apple-certified books on the Training Center. To learn more, please visit training.apple.com. market. Designed for support technicians, help desk specialists, and ardent Mac users, this guide takes you deep inside the Also in the Apple Pro Training Series: Mavericks operating system. -

Converting ASCII Files
Converting Data from ASCII to SPSS System Files Some data files, especially older ones, will not be available as SPSS system files, but instead will be provided with a fixed-format ASCII (American Standard Code for Information Interchange) file and an SPSS syntax file. Once you have downloaded your files and, if necessary, unzipped them: • Start SPSS and open the syntax file (the one with the “.sps” extension). • Find the “FILE HANDLE” command and replace “data-filename” with the path to your data file (the one ending in “.txt”). For example, if you download ICPSR Study 4131 (ABC News Pennsylvania Poll, Sept. 2004) in a directory on your “C” drive called “Temp,” the path created will be "C:\Temp\5268001\ICPSR_04131\DS0001_ABC_News_Pennsylvania_Poll,_Sept ember_2004__\04131-0001-Data.txt." (This is admittedly pretty unwieldy, and it might be a good idea to move and rename the file before proceeding). The FILE HANDLE: FILE HANDLE DATA / NAME="data-filename" LRECL=225. would become: FILE HANDLE DATA / NAME="C:\Temp\5268001\ICPSR_04131\DS0001_ABC_News_Pennsylvania_P oll,_September_2004__\04131-0001-Data.txt " LRECL=225. • Find the “SAVE OUTFILE” command (probably the last one in the file), and replace “spss-filename.sav” with the name and path of the SPSS system file you wish to create. If the command is preceded by an asterisk, remove the asterisk. For example, SAVE OUTFILE="spss-filename.sav". would become: SAVE OUTFILE="C:\Temp\5268001\ICPSR_04131\DS0001_ABC_News_Pennsylvania _Poll,_September_2004__\04131-0001-Data.sav". From the menu bar, click on “Run” and “All.” If no "SAVE OUTFILE" command exits, create one from scratch. -

Pooch Manual In
What’s New As of August 21, 2011, Pooch is updated to version 1.8.3 for use with OS X 10.7 “Lion”: Pooch users can renew their subscriptions today! Please see http://daugerresearch.com/pooch for more! On November 17, 2009, Pooch was updated to version 1.8: • Linux: Pooch can now cluster nodes running 64-bit Linux, combined with Mac • 64-bit: Major internal revisions for 64-bit, particularly updated data types and structures, for Mac OS X 10.6 "Snow Leopard" and 64-bit Linux • Sockets: Major revisions to internal networking to adapt to BSD Sockets, as recommended by Apple moving forward and required for Linux • POSIX Paths: Major revisions to internal file specification format in favor of POSIX paths, recommended by Apple moving forward and required for Linux • mDNS: Adapted usage of Bonjour service discovery to use Apple's Open Source mDNS library • Pooch Binary directory: Added Pooch binary directory support, making possible launching jobs using a remotely-compiled executable • Minor updates and fixes needed for Mac OS X 10.6 "Snow Leopard" Current Pooch users can renew their subscriptions today! Please see http://daugerresearch.com/pooch for more! On April 16, 2008, Pooch was updated to version 1.7.6: • Mac OS X 10.5 “Leopard” spurs updates in a variety of Pooch technologies: • Network Scan window • Preferences window • Keychain access • Launching via, detection of, and commands to the Terminal • Behind the Login window behavior • Other user interface and infrastructure adjustments • Open MPI support: • Complete MPI support using libraries