Stealing Keys from Pcs Using a Radio: Cheap Electromagnetic Attacks on Windowed Exponentiation (Extended Version)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Course 5 Lesson 2
This material is based on work supported by the National Science Foundation under Grant No. 0802551 Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author (s) and do not necessarily reflect the views of the National Science Foundation C5L3S1 With the advent of the Internet, social networking, and open communication, a vast amount of information is readily available on the Internet for anyone to access. Despite this trend, computer users need to ensure private or personal communications remain confidential and are viewed only by the intended party. Private information such as a social security numbers, school transcripts, medical histories, tax records, banking, and legal documents should be secure when transmitted online or stored locally. One way to keep data confidential is to encrypt it. Militaries,U the governments, industries, and any organization having a desire to maintain privacy have used encryption techniques to secure information. Encryption helps to boost confidence in the security of online commerce and is necessary for secure transactions. In this lesson, you will review encryption and examine several tools used to encrypt data. You will also learn to encrypt and decrypt data. Anyone who desires to administer computer networks and work with private data must have some familiarity with basic encryption protocols and techniques. C5L3S2 You should know what will be expected of you when you complete this lesson. These expectations are presented as objectives. Objectives are short statements of expectations that tell you what you must be able to do, perform, learn, or adjust after reviewing the lesson. -
MASTERCLASS GNUPG MASTERCLASS You Wouldn’T Want Other People Opening Your Letters and BEN EVERARD Your Data Is No Different
MASTERCLASS GNUPG MASTERCLASS You wouldn’t want other people opening your letters and BEN EVERARD your data is no different. Encrypt it today! SECURE EMAIL WITH GNUPG AND ENIGMAIL Send encrypted emails from your favourite email client. our typical email is about as secure as a The first thing that you need to do is create a key to JOHN LANE postcard, which is good news if you’re a represent your identity in the OpenPGP world. You’d Ygovernment agency. But you wouldn’t use a typically create one key per identity that you have. postcard for most things sent in the post; you’d use a Most people would have one identity, being sealed envelope. Email is no different; you just need themselves as a person. However, some may find an envelope – and it’s called “Encryption”. having separate personal and professional identities Since the early 1990s, the main way to encrypt useful. It’s a personal choice, but starting with a single email has been PGP, which stands for “Pretty Good key will help while you’re learning. Privacy”. It’s a protocol for the secure encryption of Launch Seahorse and click on the large plus-sign email that has since evolved into an open standard icon that’s just below the menu. Select ‘PGP Key’ and called OpenPGP. work your way through the screens that follow to supply your name and email address and then My lovely horse generate the key. The GNU Privacy Guard (GnuPG), is a free, GPL-licensed You can, optionally, use the Advanced Key Options implementation of the OpenPGP standard (there are to add a comment that can help others identify your other implementations, both free and commercial – key and to select the cipher, its strength and set when the PGP name now refers to a commercial product the key should expire. -
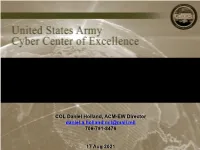
Future EW Capabilities
CRITICAL UNCLASSIFIED INFORMATION Future EW Capabilities COL Daniel Holland, ACM-EW Director [email protected] 706-791-8476 CRITICAL17 UNCLASSIFIEDAug 2021 INFORMATION Future Army EW Capabilities AISR Target identification, geo-location, and advanced non-kinetic effects delivery for the MDO fight. HELIOS (MDSS) Altitude 60k’ EW Planning and Management Tool LOS 500 kms (nadir 18 kms) HADES (MDSS) Altitude 40k+’ UAV LOS 400 kms Spectrum Analyzer MFEW Air Large MFEW Air Small Altitude 15k-25k’ Altitude 2500-8000’ LOS 250-300 kms LOS 100-150 kms C2 Counter Fire XX Radar SAM SRBM MEMSS C2 TT Radar Tech Effects CP TA Radar C2 AISR – Aerial ISR DEA – Defensive Electromagnetic Attack GSR- Ground Surveillance Radar TA Radar ERCA – Extended Range Cannon Artillery FLOT – Forward Line of Troops IFPC – Indirect Fire Protection Capability GMLS-ER – Guided Multiple Launch Rocket System Extended Rng UGS HADES – High Accuracy Detection & Exploitation System HELIOS – High altitude Extended range Long endurance Intel Observation System LOS – Line of Sight MDSS – Multi-Domain Sensor System MEMSS - Modular Electromagnetic Spectrum System TLS EAB MFEW – Multifunction Electromagnetic Warfare Ground to Air TLS BCT M-SHORAD – Mobile Short Range Air Defense Close fight TLS – Terrestrial Layer System 30km 70km 150km TT – Target Tracking 500km FLOT THREAT TA – Target Acquisition PrSM Ver 14.6 – 30 Jul 21 155mm ERCA GMLS-ER UGS – Unmanned Ground System AREA UNCLASSIFIED Electronic Warfare Planning and Management Tool (EWPMT) Electromagnetic Warfare/Spectrum -

ULTIMA X Series 3 EC Declaration of Conformity MSA
Operating Manual ULTIMAX-Series Gas Monitors Order No. 10046690/09 MSA AUER GmbH Thiemannstrasse 1 D-12059 Berlin Germany © MSA AUER GmbH. All rights reserved MSA EC Declaration of Conformity EC Declaration of Conformity Manufactured by: Mine Safety Appliances Company 1000 Cranberry Woods Drive Cranberry Township, PA 16066 USA The manufacturer or the European Authorized Representative: MSA AUER GmbH, Thiemannstrasse 1, D-12059 Berlin declares that the ULTIMA XE Main product ULTIMA XE Main with HART Module based on the EC-Type Examination Certificate: DMT 02 ATEX E 202 X complies with the ATEX directive 94/9/EC, Annex III. Quality Assurance Notification complying with Annex IV of the ATEX Directive 94/9/EC has been issued by Ineris of France, Notified Body number: 0080. The product is in conformance with the EMC directive 2004 / 108/ EC, EN 50270 :2006 Type 2 *, EN 61000 - 6 - 4 : 2007 * EN 61000-4-6 : Ultima XE MAIN HART MODULE : occasional transmission error can appear at the 2-wire version. A fault check has to be used at the receiver unit. The product complies with the directive 96/98 / EC (MarED), based on the EC-Type Examination Certificate : SEE BG 213.038 The quality survaillance is under the control of SEE BG, Notified Body number: 0736 We further declare that the product complies with the provisions of LVD Directive 2006 / 95/ EC, with the following harmonised standard: EN 61010-1 :2002 MSA AUER GmbH Berlin, October 2008 Dr. Axel Schubert R&D Instruments ® GB ULTIMA X Series 3 EC Declaration of Conformity MSA EC Declaration of Conformity Manufactured by: Mine Safety Appliances Company 1000 Cranberry Woods Drive Cranberry Township, PA 16066 USA The manufacturer or the European Authorized Representative: MSA AUER GmbH, Thiemannstrasse 1, D-12059 Berlin declares that the product ULTIMA SENSOR XE based on the EC-Type Examination Certificate: DMT 02 ATEX E 202 X complies with the ATEX directive 94/9/EC, Annex III. -

Wiretapping End-To-End Encrypted Voip Calls Real-World Attacks on ZRTP
Institute of Operating Systems and Computer Networks Wiretapping End-to-End Encrypted VoIP Calls Real-World Attacks on ZRTP Dominik Schürmann, Fabian Kabus, Gregor Hildermeier, Lars Wolf, 2017-07-18 wiretapping difficulty End-to-End Encryption SIP + DTLS-SRTP (SIP + Datagram Transport Layer Security-SRTP) End-to-End Encryption & Authentication SIP + SRTP + ZRTP Introduction Man-in-the-Middle ZRTP Attacks Conclusion End-to-End Security for Voice Calls Institute of Operating Systems and Computer Networks No End-to-End Security PSTN (Public Switched Telephone Network) SIP + (S)RTP (Session Initiation Protocol + Secure Real-Time Transport Protocol) 2017-07-18 Dominik Schürmann Wiretapping End-to-End Encrypted VoIP Calls Page 2 of 13 wiretapping difficulty End-to-End Encryption & Authentication SIP + SRTP + ZRTP Introduction Man-in-the-Middle ZRTP Attacks Conclusion End-to-End Security for Voice Calls Institute of Operating Systems and Computer Networks No End-to-End Security PSTN (Public Switched Telephone Network) SIP + (S)RTP (Session Initiation Protocol + Secure Real-Time Transport Protocol) End-to-End Encryption SIP + DTLS-SRTP (SIP + Datagram Transport Layer Security-SRTP) 2017-07-18 Dominik Schürmann Wiretapping End-to-End Encrypted VoIP Calls Page 2 of 13 wiretapping difficulty Introduction Man-in-the-Middle ZRTP Attacks Conclusion End-to-End Security for Voice Calls Institute of Operating Systems and Computer Networks No End-to-End Security PSTN (Public Switched Telephone Network) SIP + (S)RTP (Session Initiation Protocol + Secure Real-Time -

CS 255: Intro to Cryptography 1 Introduction 2 End-To-End
Programming Assignment 2 Winter 2021 CS 255: Intro to Cryptography Prof. Dan Boneh Due Monday, March 1st, 11:59pm 1 Introduction In this assignment, you are tasked with implementing a secure and efficient end-to-end encrypted chat client using the Double Ratchet Algorithm, a popular session setup protocol that powers real- world chat systems such as Signal and WhatsApp. As an additional challenge, assume you live in a country with government surveillance. Thereby, all messages sent are required to include the session key encrypted with a fixed public key issued by the government. In your implementation, you will make use of various cryptographic primitives we have discussed in class—notably, key exchange, public key encryption, digital signatures, and authenticated encryption. Because it is ill-advised to implement your own primitives in cryptography, you should use an established library: in this case, the Stanford Javascript Crypto Library (SJCL). We will provide starter code that contains a basic template, which you will be able to fill in to satisfy the functionality and security properties described below. 2 End-to-end Encrypted Chat Client 2.1 Implementation Details Your chat client will use the Double Ratchet Algorithm to provide end-to-end encrypted commu- nications with other clients. To evaluate your messaging client, we will check that two or more instances of your implementation it can communicate with each other properly. We feel that it is best to understand the Double Ratchet Algorithm straight from the source, so we ask that you read Sections 1, 2, and 3 of Signal’s published specification here: https://signal. -

FALL 2020 E-NEWSLETTER at Digital Mountain We Assist Our Clients with Their Computer Forensics, E-Discovery, Cybersecurity and Data Analytics Needs
FALL 2020 E-NEWSLETTER At Digital Mountain we assist our clients with their computer forensics, e-discovery, cybersecurity and data analytics needs. For this E-Newsletter, we focus on ephemeral communications and the affect of disappearing messages on discovery cases. Ephemeral Applications: Digital Trick or Treat The trick in trick or treating is one that has evolved from the neighbor who dons a monster mask when opening the door to the disappearance of peanut butter cups when Dad does the safety check of the night’s candy haul. Our digital communications have gone through an analogous transformation as we first marveled at how much data our devices could hold. Just as we upgraded from a small plastic pumpkin to a pillowcase for larger candy collections - we saved a growing plethora of emails, text messages, digital images, voice messages, and all manner of documents on mobile devices. Now, with the rise of discovery, we want our vulnerable data to disappear as if it were our least favorite candy. Ephemeral applications may be just the trick for that unwanted data. Call It What You Will There is no consensus about what constitutes an ephemeral application beyond the understanding that there is an element of impermanence. In 2016, three Georgia Tech College of Computing researchers proposed the creation of “ephemeral apps” that would allow users to engage with apps on a trial basis that would “pop-up instantaneously” on devices and then disappear after a certain period (https://www.cc.gatech.edu/~kbhardwa/papers/eapps.pdf). At the opposite end of the spectrum, in 2017 fan favorite Snapchat modified its app to allow recipients to determine when photographs and video would disappear rather than the burn after reading settings that propelled Snapchat’s rapid rise (https://www.vox.com/2017/5/9/15595040/snapchat-product-update-limitless-q1-earnings). -

Electromagnetic Side Channels of an FPGA Implementation of AES
Electromagnetic Side Channels of an FPGA Implementation of AES Vincent Carlier, Herv´e Chabanne, Emmanuelle Dottax and Herv´e Pelletier SAGEM SA Abstract. We show how to attack an FPGA implementation of AES where all bytes are processed in parallel using differential electromag- netic analysis. We first focus on exploiting local side channels to isolate the behaviour of our targeted byte. Then, generalizing the Square at- tack, we describe a new way of retrieving information, mixing algebraic properties and physical observations. Keywords: side channel attacks, DEMA, FPGA, AES hardware im- plementation, Square attack. 1 Introduction Side channel attacks first appear in [Koc96] where timing attacks are de- scribed. This kind of attack tends to retrieve information from the secret items stored inside a device by observing its behaviour during a crypto- graphical computation. In a timing attack, the adversary measures the time taken to perform the computations and deduces additionnal information about the cryptosystems. Similarly, power analysis attacks are introduced in [KJJ99] where the attacker wants to discover the secrets by analysing the power consumption. Smart cards are targets of choice as their power is sup- plied externally. Usually we distinguish Simple Power Analysis (SPA), that tries to gain information directly from the power consumption, and Differ- ential Power Analysis (DPA) where a large number of traces are acquired and statistically processed. Another side channel is the one that exploits the Electromagnetic (EM) emanations. Indeed, these emanations are correlated with the current flowing through the device. EM leakage in a PC environ- ment where eavesdroppers reconstruct video screens has been known for a 1 long time [vE85], see also [McN] for more references. -

Pgpfone Pretty Good Privacy Phone Owner’S Manual Version 1.0 Beta 7 -- 8 July 1996
Phil’s Pretty Good Software Presents... PGPfone Pretty Good Privacy Phone Owner’s Manual Version 1.0 beta 7 -- 8 July 1996 Philip R. Zimmermann PGPfone Owner’s Manual PGPfone Owner’s Manual is written by Philip R. Zimmermann, and is (c) Copyright 1995-1996 Pretty Good Privacy Inc. All rights reserved. Pretty Good Privacy™, PGP®, Pretty Good Privacy Phone™, and PGPfone™ are all trademarks of Pretty Good Privacy Inc. Export of this software may be restricted by the U.S. government. PGPfone software is (c) Copyright 1995-1996 Pretty Good Privacy Inc. All rights reserved. Phil’s Pretty Good engineering team: PGPfone for the Apple Macintosh and Windows written mainly by Will Price. Phil Zimmermann: Overall application design, cryptographic and key management protocols, call setup negotiation, and, of course, the manual. Will Price: Overall application design. He persuaded the rest of the team to abandon the original DOS command-line approach and designed a multithreaded event-driven GUI architecture. Also greatly improved call setup protocols. Chris Hall: Did early work on call setup protocols and cryptographic and key management protocols, and did the first port to Windows. Colin Plumb: Cryptographic and key management protocols, call setup negotiation, and the fast multiprecision integer math package. Jeff Sorensen: Speech compression. Will Kinney: Optimization of GSM speech compression code. Kelly MacInnis: Early debugging of the Win95 version. Patrick Juola: Computational linguistic research for biometric word list. -2- PGPfone Owner’s -

Toxic Potency Measurement for Fire Hazard Analysis
United States Department of Commerce National Institute of Standards and Technology NIST Special Publication 827 Toxic Potency Measurement for Fire Hazard Analysis Vytenis Babrauskas, Barbara C. Levin, Richard G. Gann, Maya Paabo, Richard H. Harris, Jr., Richard D. Peacock, and Shyuitsu Yusa NATIONAL INSTITUTE OF STANDARDS & TECHNOLOGY Research Information Center Gaithersburg, MD 20899 DATE DUE Demco, Inc. 38-293 MP NIST Special Publication 827 m Toxic Potency Measurement for Fire Hazard Analysis Vytenis Babrauskas, Barbara C. Levin, Richard G. Gann, Maya Paabo, Richard H. Harris, Jr., Richard D. Peacock, and Shyuitsu Yusa Building and Fire Research Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899 December 1991 U.S. Department of Commerce Robert A. Mosbacher, Secretary National Institute of Standards and Technology John W. Lyons, Director National Institute of Standards U.S. Government Printing Office For sale by the Superintendent and Technology Washington: 1991 of Documents Special Publication 827 U.S. Government Printing Office Natl. Inst. Stand. Technol. Washington, DC 20402 Spec. Publ. 827 119 pages (Dec. 1991) CODEN: NSPUE2 Table of Contents Page List of Figures v List of Tables vi Executive Summary vii Abstract 1 1 Introduction 1 2 Computations of fire hazard 4 2.1 Quantifying hazard in fires 4 2.1.1 Hand calculations 4 2.1.2 Computer models 5 2.2 Definitions of terms 6 2.3 Fire scenarios and toxic potency data 6 3 Types of fires 9 4 Toxic potency measurements 13 5 Criteria for bench-scale toxic -

Internet Telephony with Linphone WELLWELL CONNECTEDCONNECTED
Linphone COVER STORY Internet telephony with Linphone WELLWELL CONNECTEDCONNECTED When you want to call your friends in distant countries, don’t pick up municate with the VoIP provider, so you will need to install the library first. To do the phone; just put on your headset and fire up Linphone. so, open a terminal window, then be- come root by typing su and supplying BY SIMONE SCHÄFER the root password. Unpack the archive by typing tar xzf libosip2-2.2.0.tar.gz, ne of the most popular methods wants to take incoming calls via Purtel. and then change to the new directory (cd for accessing Voice over IP tech- The procedures are similar for other pro- libosip2-2.2.0). The following commands Onology is through a so-called viders. will build and install the library: softphone. A softphone is simply a com- puter program running on your desktop Installation ./configure --prefix=/usr that handles call establishment and com- The source code for the 1.1.0 release, make munication. Linphone [1] is one of the and the libraries, are available on the most popular softphone applications for DVD with this issue below LinuxUser/ Phone Numbers and SIP Ids Linux. Linphone is optimized for the linphone/. In the simplest of all cases, the phone Gnome desktop, although that doesn’t Mandriva Linux 2006 has the current number will be a simple telephone num- mean you can’t run it on KDE. This arti- 1.1.0 version. Gentoo Linux users can ber followed by the SIP domain, such as cles describes how to install, configure, install Linphone 1.1.0 simply by running [email protected]. -

Communication and Security Survey Results from US, UK and German Business Leaders
The most secure collaboration platform. Communication and Security Survey results from US, UK and German business leaders Communication and Security Survey | wire.com | February 2019 1 An introduction Every year we ask executives about key topics - this year we chose to focus on communication, security, privacy, and regulation as these have been hot topics in 2018. We asked more than 300 executives from US and Europe about their views on these topics. In addition, please find at the end of this presentation my personal predictions for 2019. We trust you will enjoy the report. Morten Brøgger · CEO Best regards, Morten Brøgger Chief Executive Officer at Wire Communication and Security Survey | wire.com | February 2019 2 Are we still secure? Many organizations have been a …. want their organization to be more proactive victim of a cyberattack and not a 81% in the ways it protects its sensitive information, single respondent disagreed that communication, and/or data. cybersecurity is a major challenge for businesses. Yet while the challenges posed by cybersecurity are understood …. believe security and compliance are key by businesses, some organizations 79% parameters when selecting cloud business aren’t doing enough to prepare. In crisis solutions. situations, in particular, businesses have gaps in their ability to communicate internally and externally in a safe and secure way. …. of organizations don’t have or are unsure if they 38% have, a plan in case of a security breach. …. of respondents said it would be useful to be 83% able to extend a company's secure communication infrastructure to business partners and customers Communication and Security Survey | wire.com | February 2019 3 Emails are popular, Email remains a popular communication to changes in instant messaging but are they tool yet business leaders spend too technology, an overwhelming number much of their time using it.