An Overview of Iot Operating System: Contiki Os and Its Communication Models
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Transactional Concurrency Control for Intermittent, Energy-Harvesting Computing Systems
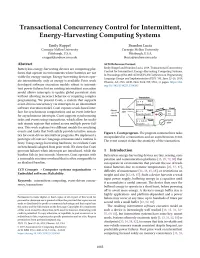
PLDI ’19, June 22ś26, 2019, Phoenix, AZ, USA Emily Ruppel and Brandon Lucia 52, 55, 82] and preserving progress [6, 7, 53]. Recent work sequences of multiple tasks to execute atomically with re- addressed input/output (I/O), ensuring that computations spect to events. Coati’s support for events and transactions were timely in their consumption of data collected from sen- is the main contribution of this work. Coati provides the sors [15, 31, 86]. However, no prior work on intermittent critical ability to ensure correct synchronization across re- computing provides clear semantics for programs that use gions of code that are too large to complete in a single power event-driven concurrency, handling asynchronous I/O events cycle. Figure 1 shows a Coati program with three tasks con- in interrupts that share state with transactional computa- tained in a transaction manipulating related variables x, y, tions that execute in a main control loop. The idiomatic use of and z, while an asynchronous event updates x and y. Coati interrupts to collect, process, and store sensor results is very ensures atomicity of all tasks in the figure, even if any task common in embedded systems. The absence of this event- individually is forced to restart by a power failure. driven I/O support in intermittent systems is an impediment This work explores the design space of transaction, task, to developing batteryless, energy-harvesting applications. and event implementations by examining two models that Combining interrupts and transactional computations in make different trade-offs between complexity and latency. an intermittent system creates a number of unique problems Coati employs a split-phase model that handles time-critical that we address in this work using new system support. -

Beyond Interoperability – Pushing the Performance of Sensor Network IP Stacks
Industry: Beyond Interoperability – Pushing the Performance of Sensor Network IP Stacks JeongGil Ko Joakim Eriksson Nicolas Tsiftes Department of Computer Science Swedish Institute of Computer Swedish Institute of Computer Johns Hopkins University Science (SICS) Science (SICS) Baltimore, MD 21218, USA Box 1263, SE-16429 Kista, Box 1263, SE-16429 Kista, [email protected] Sweden Sweden [email protected] [email protected] Stephen Dawson-Haggerty Jean-Philippe Vasseur Mathilde Durvy Computer Science Division Cisco Systems Cisco Systems University of California, Berkeley 11, Rue Camille Desmoulins, Issy 11, Rue Camille Desmoulins, Issy Berkeley, CA 94720, USA Les Moulineaux, 92782, France Les Moulineaux, 92782, France [email protected] [email protected] [email protected] Abstract General Terms Interoperability is essential for the commercial adoption Experimentation, Performance, Standardization of wireless sensor networks. However, existing sensor net- Keywords work architectures have been developed in isolation and thus IPv6, 6LoWPAN, RPL, IETF, Interoperability, Sensor interoperability has not been a concern. Recently, IP has Network, TinyOS, Contiki been proposed as a solution to the interoperability problem of low-power and lossy networks (LLNs), considering its open 1 Introduction and standards-based architecture at the network, transport, For wireless sensor networks to be widely adopted by and application layers. We present two complete and in- the industry, hardware and software implementations from teroperable implementations of the IPv6 protocol stack for different vendors need to interoperate and perform well to- LLNs, one for Contiki and one for TinyOS, and show that gether. While IEEE 802.15.4 has emerged as a common the cost of interoperability is low: their performance and physical layer that is used both in commercial sensor net- overhead is on par with state-of-the-art protocol stacks cus- works and in academic research, interoperability at the phys- tom built for the two platforms. -
AMNESIA 33: How TCP/IP Stacks Breed Critical Vulnerabilities in Iot
AMNESIA:33 | RESEARCH REPORT How TCP/IP Stacks Breed Critical Vulnerabilities in IoT, OT and IT Devices Published by Forescout Research Labs Written by Daniel dos Santos, Stanislav Dashevskyi, Jos Wetzels and Amine Amri RESEARCH REPORT | AMNESIA:33 Contents 1. Executive summary 4 2. About Project Memoria 5 3. AMNESIA:33 – a security analysis of open source TCP/IP stacks 7 3.1. Why focus on open source TCP/IP stacks? 7 3.2. Which open source stacks, exactly? 7 3.3. 33 new findings 9 4. A comparison with similar studies 14 4.1. Which components are typically flawed? 16 4.2. What are the most common vulnerability types? 17 4.3. Common anti-patterns 22 4.4. What about exploitability? 29 4.5. What is the actual danger? 32 5. Estimating the reach of AMNESIA:33 34 5.1. Where you can see AMNESIA:33 – the modern supply chain 34 5.2. The challenge – identifying and patching affected devices 36 5.3. Facing the challenge – estimating numbers 37 5.3.1. How many vendors 39 5.3.2. What device types 39 5.3.3. How many device units 40 6. An attack scenario 41 6.1. Other possible attack scenarios 44 7. Effective IoT risk mitigation 45 8. Conclusion 46 FORESCOUT RESEARCH LABS RESEARCH REPORT | AMNESIA:33 A note on vulnerability disclosure We would like to thank the CERT Coordination Center, the ICS-CERT, the German Federal Office for Information Security (BSI) and the JPCERT Coordination Center for their help in coordinating the disclosure of the AMNESIA:33 vulnerabilities. -

Key Infection: Smart Trust for Smart Dust
Key Infection: Smart Trust for Smart Dust Ross Anderson Haowen Chan Adrian Perrig University of Cambridge Carnegie Mellon University Carnegie Mellon University [email protected] [email protected] [email protected] Abstract and building safety. As sensor networks become cheaper and more commoditised, they will become attractive to Future distributed systems may include large self- home users and small businesses, and for other new appli- organizing networks of locally communicating sen- cations. sor nodes, any small number of which may be sub- A typical sensor network consists of a large number of verted by an adversary. Providing security for these small, low-cost nodes that use wireless peer-to-peer com- sensor networks is important, but the problem is compli- munication to form a self-organized network. They use cated by the fact that managing cryptographic key ma- multi-hop routing algorithms based on dynamic network terial is hard: low-cost nodes are neither tamper-proof and resource discovery protocols. To keep costs down and nor capable of performing public key cryptography effi- to deal with limited battery energy, nodes have fairly min- ciently. imal computation, communication, and storage resources. In this paper, we show how the key distribution problem They do not have tamper-proof hardware. We can thus ex- can be dealt with in environments with a partially present, pect that some small fraction of nodes in a network may be passive adversary: a node wishing to communicate securely compromised by an adversary over time. with other nodes simply generates a symmetric key and An interesting example of a sensor network technology sends it in the clear to its neighbours. -

Coap Based Acute Parking Lot Monitoring System Using Sensor Networks
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by Directory of Open Access Journals ISSN: 2229-6948(ONLINE) ICTACT JOURNAL ON COMMUNICATION TECHNOLOGY: SPECIAL ISSUE ON ADVANCES IN WIRELESS SENSOR NETWORKS, JUNE 2014, VOLUME: 05, ISSUE: 02 COAP BASED ACUTE PARKING LOT MONITORING SYSTEM USING SENSOR NETWORKS R. Aarthi1 and A. Pravin Renold2 TIFAC-CORE in Pervasive Computing Technologies, Velammal Engineering College, India E-mail: [email protected], [email protected] Abstract it to aid in overall management and planning. Sensor networks Vehicle parking is the act of temporarily maneuvering a vehicle in to are a natural candidate for car-park management systems [6], a certain location. To deal with parking monitoring system issue such because they allow status to be monitored very accurately - for as traffic, this paper proposes a vision of improvements in monitoring each parking space, if desired. the vehicles in parking lots based on sensor networks. Most of the existing paper deals with that of the automated parking which is of cluster based and each has its own overheads like high power, less energy efficiency, incompatible size of lots, space. The novel idea in this work is usage of CoAP (Constrained Application Protocol) which is recently created by IETF (draft-ietf-core-coap-18, June 28, 2013), CoRE group to develop RESTful application layer protocol for communications within embedded wireless networks. This paper deals with the enhanced CoAP protocol using multi hop flat topology, which makes the acuters feel soothe towards parking vehicles. We aim to minimize the time consumed for finding free parking lot as well as increase the energy efficiency. -

Tecnologías De Fuentes Abiertas Para Ciudades Inteligentes
Open Smart Cities Tecnologías de fuentes abiertas para ciudades inteligentes www.cenatic.es Abril 2013 Open Smart Cities Tecnologías de fuentes abiertas para ciudades inteligentes Título: Open Smart Cities: Tecnologías de fuentes abiertas para ciudades inteligentes Autora: Ana Trejo Pulido Abril 2012 Edita: CENATIC. Avda. Clara Campoamor s/n. 06200 Almendralejo (Badajoz). Primera Edición. ISBN-13: 978-84-15927-13-6 Los contenidos de esta obra está bajo una licencia Reconocimiento 3.0 España de Creative Commons. Para ver una copia de la licencia visite http://creativecommons.org/licenses/by/3.0/es/ www.cenatic.es Pág. 2 de 59 Open Smart Cities Tecnologías de fuentes abiertas para ciudades inteligentes Índice 1 Introducción...............................................................................................................6 2 La Internet de las Cosas: hacia la ciudad conectada.................................................7 3 Tecnologías de código abierto para la Internet de las Cosas.....................................9 3.1 Waspmote.................................................................................................................10 3.2 Arduino......................................................................................................................10 3.3 Dash7........................................................................................................................11 3.4 Rasberry Pi................................................................................................................11 -

A Fog Storage Software Architecture for the Internet of Things Bastien Confais, Adrien Lebre, Benoît Parrein
A Fog storage software architecture for the Internet of Things Bastien Confais, Adrien Lebre, Benoît Parrein To cite this version: Bastien Confais, Adrien Lebre, Benoît Parrein. A Fog storage software architecture for the Internet of Things. Advances in Edge Computing: Massive Parallel Processing and Applications, IOS Press, pp.61-105, 2020, Advances in Parallel Computing, 978-1-64368-062-0. 10.3233/APC200004. hal- 02496105 HAL Id: hal-02496105 https://hal.archives-ouvertes.fr/hal-02496105 Submitted on 2 Mar 2020 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. November 2019 A Fog storage software architecture for the Internet of Things Bastien CONFAIS a Adrien LEBRE b and Benoˆıt PARREIN c;1 a CNRS, LS2N, Polytech Nantes, rue Christian Pauc, Nantes, France b Institut Mines Telecom Atlantique, LS2N/Inria, 4 Rue Alfred Kastler, Nantes, France c Universite´ de Nantes, LS2N, Polytech Nantes, Nantes, France Abstract. The last prevision of the european Think Tank IDATE Digiworld esti- mates to 35 billion of connected devices in 2030 over the world just for the con- sumer market. This deep wave will be accompanied by a deluge of data, applica- tions and services. -

Shared Sensor Networks Fundamentals, Challenges, Opportunities, Virtualization Techniques, Comparative Analysis, Novel Architecture and Taxonomy
Journal of Sensor and Actuator Networks Review Shared Sensor Networks Fundamentals, Challenges, Opportunities, Virtualization Techniques, Comparative Analysis, Novel Architecture and Taxonomy Nahla S. Abdel Azeem 1, Ibrahim Tarrad 2, Anar Abdel Hady 3,4, M. I. Youssef 2 and Sherine M. Abd El-kader 3,* 1 Information Technology Center, Electronics Research Institute (ERI), El Tahrir st, El Dokki, Giza 12622, Egypt; [email protected] 2 Electrical Engineering Department, Al-Azhar University, Naser City, Cairo 11651, Egypt; [email protected] (I.T.); [email protected] (M.I.Y.) 3 Computers & Systems Department, Electronics Research Institute (ERI), El Tahrir st, El Dokki, Giza 12622, Egypt; [email protected] 4 Department of Computer Science & Engineering, School of Engineering and Applied Science, Washington University in St. Louis, St. Louis, MO 63130, 1045, USA; [email protected] * Correspondence: [email protected] Received: 19 March 2019; Accepted: 7 May 2019; Published: 15 May 2019 Abstract: The rabid growth of today’s technological world has led us to connecting every electronic device worldwide together, which guides us towards the Internet of Things (IoT). Gathering the produced information based on a very tiny sensing devices under the umbrella of Wireless Sensor Networks (WSNs). The nature of these networks suffers from missing sharing among them in both hardware and software, which causes redundancy and more budget to be used. Thus, the appearance of Shared Sensor Networks (SSNs) provides a real modern revolution in it. Where it targets making a real change in its nature from domain specific networks to concurrent running domain networks. That happens by merging it with the technology of virtualization that enables the sharing feature over different levels of its hardware and software to provide the optimal utilization of the deployed infrastructure with a reduced cost. -

NSF Nets Small RUI: Wireless Sensor Network Project
NSF NeTs Small RUI: Wireless Sensor Network Project Federal Agency and Organization Element to Which Report is Submitted: 4900 Federal Grant or Other Identifying Number Assigned by Agency: 1816197 Project Title: NeTS: Small: RUI: Bulldog Mote- Low Power Sensor Node and design Methodologies for Wireless Sensor Networks PD/PI Name: Nan Wang, Principal Investigator Woonki Na, Co-Principal Investigator Recipient Organization: California State University-Fresno Foundation Project/Grant Period: 10/01/2018 - 09/30/2021 Reporting Period: 10/01/2018 - 09/30/2019 Student Assistant: Russel Schellenberg Calvin Jarrod Smith Department of Electrical and Computer Engineering Lyles College of Engineering Contents 1 Purpose 3 2 Current Projects 3 2.1 Bulldog Mote . .3 2.2 Wireless Gateway Implementation . .3 2.2.1 Tmote Sky Mote . .3 2.2.2 Gateway Website . .7 2.3 MANET Routing Protocols and Software . .8 2.3.1 Contiki OS . .8 3 HM-10 BLE Communication Module 10 3.1 Overview . 10 3.2 HM-10 Module Configuration . 16 3.3 Connecting Two HM-10 Devices . 17 3.3.1 Setting up Slave Device . 18 3.3.2 Setting up Master Device . 18 3.3.3 Discovery Connection . 19 3.4 Connecting to HM-10 from Android Phone . 23 4 Wireless Gateway Implementation 30 4.1 Gateway Operating System and Environment . 30 4.2 Required hardware: . 30 4.3 Installation . 30 4.4 Contiki Program . 31 4.5 Gateway Program . 32 4.6 Web Server . 32 5 One-Hop, Ad-Hoc Sensor Network with Cooja 36 5.1 Overview . 36 5.2 Peripheral Node Gateway Detection . -

Performance Study of Real-Time Operating Systems for Internet Of
IET Software Research Article ISSN 1751-8806 Performance study of real-time operating Received on 11th April 2017 Revised 13th December 2017 systems for internet of things devices Accepted on 13th January 2018 E-First on 16th February 2018 doi: 10.1049/iet-sen.2017.0048 www.ietdl.org Rafael Raymundo Belleza1 , Edison Pignaton de Freitas1 1Institute of Informatics, Federal University of Rio Grande do Sul, Av. Bento Gonçalves, 9500, CP 15064, Porto Alegre CEP: 91501-970, Brazil E-mail: [email protected] Abstract: The development of constrained devices for the internet of things (IoT) presents lots of challenges to software developers who build applications on top of these devices. Many applications in this domain have severe non-functional requirements related to timing properties, which are important concerns that have to be handled. By using real-time operating systems (RTOSs), developers have greater productivity, as they provide native support for real-time properties handling. Some of the key points in the software development for IoT in these constrained devices, like task synchronisation and network communications, are already solved by this provided real-time support. However, different RTOSs offer different degrees of support to the different demanded real-time properties. Observing this aspect, this study presents a set of benchmark tests on the selected open source and proprietary RTOSs focused on the IoT. The benchmark results show that there is no clear winner, as each RTOS performs well at least on some criteria, but general conclusions can be drawn on the suitability of each of them according to their performance evaluation in the obtained results. -

C01 Plus 2010 301 185 0 Fr
P5-16...R40-17 Modèle : C01 PLUS fr Notice de montage et d’utilisation Moteur de volet roulant avec émetteur-récepteur radio intégré Informations importantes pour: • l'installateur / • l'électricien / • l'utilisateur À transmettre à la personne concernée! L'original de cette notice doit être conservée par l'utilisateur. 2010 301 185 0a 19/03/2021 Becker-Antriebe GmbH Friedrich-Ebert-Straße 2-4 35764 Sinn/Allemagne www.becker-antriebe.com Sommaire Généralités.......................................................................................................................................................................... 4 Garantie .............................................................................................................................................................................. 5 Consignes de sécurité.......................................................................................................................................................... 5 Remarques pour l’utilisateur ............................................................................................................................................ 5 Remarques pour le montage et la mise en service ............................................................................................................. 5 Utilisation conforme ............................................................................................................................................................. 7 Montage et démontage du câble de connexion enfichable -

Concepts General Concepts Wireless Sensor Networks (WSN)
Wireless Sensor Networks – Concepts General Concepts Wireless Sensor Networks (WSN) are built based on a combination of multiple sensors placed in diverse locations, wireless communication network infrastructure and software data processing to monitor and record multiple parameters. Commonly monitored parameters are temperature, atmospheric pressure, humidity, vibration, illuminance, sound level, power consumption, chemical concentration, body health signals and many others, dependant on the selected available sensors. The WSN are used in multiple fields, ranging from remote environment monitoring, medical health, to home surveillance and industrial machines monitoring. In some cases, WSN can also be additionally used for control functions, apart from monitoring functions. Typically a WSN is made of sensor nodes that are wirelessly connected to a gateway that is then connected to a main computer (Fig. 1). In some WSN the sensor nodes can also be connected to each other, so that is possible to implement multi-hop wireless mesh networks. The gateway connects to the main computer through a cabled or wireless connection. Figure 1 – Wireless sensor network The wireless communications used in WSN depend on the application requirements, taking into consideration the needs in terms of transmission distance, sensor data bandwidth, energy source and power consumption. Common communications include standard protocols such as 2.4 GHz radio based on either IEEE802.15.4 (ZigBee, ISA 100, WirelessHart, MiWi) or IEEE802.11 (WiFi) standards. Each sensor node typically includes an embedded microcontroller system with adequate electronic interface with a sensor (or set of sensors), a radio transceiver with antenna (internal or external) and an energy source, usually a battery, or in some cases an energy harvesting circuit.