Lista Para La Protección De Datos O Manual De Resistencia
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Universidad Pol Facultad D Trabajo
UNIVERSIDAD POLITÉCNICA DE MADRID FACULTAD DE INFORMÁTICA TRABAJO FINAL DE CARRERA ESTUDIO DEL PROTOCOLO XMPP DE MESAJERÍA ISTATÁEA, DE SUS ATECEDETES, Y DE SUS APLICACIOES CIVILES Y MILITARES Autor: José Carlos Díaz García Tutor: Rafael Martínez Olalla Madrid, Septiembre de 2008 2 A mis padres, Francisco y Pilar, que me empujaron siempre a terminar esta licenciatura y que tanto me han enseñado sobre la vida A mis abuelos (q.e.p.d.) A mi hijo icolás, que me ha dejado terminar este trabajo a pesar de robarle su tiempo de juego conmigo Y muy en especial, a Susana, mi fiel y leal compañera, y la luz que ilumina mi camino Agradecimientos En primer lugar, me gustaría agradecer a toda mi familia la comprensión y confianza que me han dado, una vez más, para poder concluir definitivamente esta etapa de mi vida. Sin su apoyo, no lo hubiera hecho. En segundo lugar, quiero agradecer a mis amigos Rafa y Carmen, su interés e insistencia para que llegara este momento. Por sus consejos y por su amistad, les debo mi gratitud. Por otra parte, quiero agradecer a mis compañeros asesores militares de Nextel Engineering sus explicaciones y sabios consejos, que sin duda han sido muy oportunos para escribir el capítulo cuarto de este trabajo. Del mismo modo, agradecer a Pepe Hevia, arquitecto de software de Alhambra Eidos, los buenos ratos compartidos alrrededor de nuestros viejos proyectos sobre XMPP y que encendieron prodigiosamente la mecha de este proyecto. A Jaime y a Bernardo, del Ministerio de Defensa, por haberme hecho descubrir las bondades de XMPP. -
Statement of Defence Counterclaim Same Parties Form 18A
Court File No. CV-20-00638823-0000 ONTARIO SUPERIOR COURT OF JUSTICE B E T W E E N: COPPERHEAD LIMITED Plaintiff (Defendant to the Counterclaim) and DANIEL MICAY Defendant (Plaintiff by Counterclaim) STATEMENT OF DEFENCE AND COUNTERCLAIM 1. Unless explicitly admitted herein, the defendant, Daniel Micay (“Micay”), denies the allegations contained in each paragraph of the Statement of Claim and puts the plaintiff to the strict proof thereof. Overview 2. “Open source” software development is the process through which source code is released publicly, and the public is encouraged to study, test, improve upon, and modify that code. Open source projects rely on communities of interested contributors, each of whom provides their code under the permissive, open source copyright license used by the project in question. The resulting software is often better and more secure as a result of this transparency and collaborative effort. Open source development is a critical feature of much modern software, especially in the realm of computer security. -2- 3. The plaintiff seeks to misappropriate the copyrights associated with an open source software project started by Micay. The code authored by Micay and the other contributors was created long before the plaintiff was incorporated. On the plaintiff’s own pleadings, no written assignment of any copyrights has ever taken place. 4. The plaintiff’s suit evinces a fundamental misunderstanding of copyright law, the principles of open source software development, and the factual record. Micay respectfully requests that the plaintiff’s suit be dismissed, with costs. Parties and Players 5. Micay is a 28-year-old computer programmer. -

An Investigation Into the Security and Privacy of Ios VPN Applications
An Investigation Into the Security and Privacy of iOS VPN Applications Jack Wilson Division of Cybersecurity School of Design and Informatics Abertay University, Dundee A thesis submitted for the degree of Bachelor of Science with Honours in Ethical Hacking 1st May 2018 Word Count: 11,448 Abstract Due to the increasing number of recommendations for people to use VPN’s for privacy reasons, more app developers are creating VPN apps and publishing them on the Apple App Store and Google Play Store. In this ‘gold rush’, apps are being developed quickly and, in turn, not being developed with security fully in mind. This paper investigated a selection of free VPN applications available on the Apple App Store (for iOS devices) and test the apps for security and privacy. This includes testing for any traffic being transmitted over plain HTTP, DNS leakage and transmission of personally-identifiable information (such as phone number, IMEI 1, email address, MAC address) and evaluating the security of the tunnelling protocol used by the VPN. The testing methodology involved installing free VPN apps on a test device (an iPhone 6 running iOS 11), simulating network traffic for a pre-defined period of time and capturing the traffic (either through ARP spoofing, or through a proxy program such as Burpsuite). This allows for all traffic to be analysed to check for anything being sent without encryption. Other issues that often cause de-anonymisation with VPN applications such as DNS leakage can be tested using websites such as dnsleaktest.com. The research found several common security issues with the VPN applications that were tested, with a large majority of the applications tested failing to implement HTTPS. -

Download Android Os for Phone Open Source Mobile OS Alternatives to Android
download android os for phone Open Source Mobile OS Alternatives To Android. It’s no exaggeration to say that open source operating systems rule the world of mobile devices. Android is still an open-source project, after all. But, due to the bundle of proprietary software that comes along with Android on consumer devices, many people don’t consider it an open source operating system. So, what are the alternatives to Android? iOS? Maybe, but I am primarily interested in open-source alternatives to Android. I am going to list not one, not two, but several alternatives, Linux-based mobile OSes . Top Open Source alternatives to Android (and iOS) Let’s see what open source mobile operating systems are available. Just to mention, the list is not in any hierarchical or chronological order . 1. Plasma Mobile. A few years back, KDE announced its open source mobile OS, Plasma Mobile. Plasma Mobile is the mobile version of the desktop Plasma user interface, and aims to provide convergence for KDE users. It is being actively developed, and you can even find PinePhone running on Manjaro ARM while using KDE Plasma Mobile UI if you want to get your hands on a smartphone. 2. postmarketOS. PostmarketOS (pmOS for short) is a touch-optimized, pre-configured Alpine Linux with its own packages, which can be installed on smartphones. The idea is to enable a 10-year life cycle for smartphones. You probably already know that, after a few years, Android and iOS stop providing updates for older smartphones. At the same time, you can run Linux on older computers easily. -

An Empirical Study Into the Absence of Consent to Third-Party Tracking in Android Apps
A Fait Accompli? An Empirical Study into the Absence of Consent to Third-Party Tracking in Android Apps Konrad Kollnig, Reuben Binns, Pierre Dewitte*, Max Van Kleek, Ge Wang, Daniel Omeiza, Helena Webb, Nigel Shadbolt Department of Computer Science, University of Oxford, UK *Centre for IT and IP Law, KU Leuven, Belgium firstname.lastname@(cs.ox.ac.uk | kuleuven.be) Abstract trackers benefits app developers in several ways, notably by Third-party tracking allows companies to collect users’ be- providing analytics to improve user retention, and by enabling havioural data and track their activity across digital devices. the placement of personalised advertising within apps, which This can put deep insights into users’ private lives into the often translates into a vital source of revenue for them [32,62]. hands of strangers, and often happens without users’ aware- However, it also makes app developers dependent on privacy- ness or explicit consent. EU and UK data protection law, invasive data practices that involve the processing of large however, requires consent, both 1) to access and store infor- amounts of personal data [40, 48, 62], with little awareness mation on users’ devices and 2) to legitimate the processing from users and app developers [28,71,74,85]. Data protection of personal data as part of third-party tracking, as we analyse and privacy legislation such as the General Data Protection in this paper. Regulation (GDPR) [38] in the EU and the UK, and the Chil- This paper further investigates whether and to what extent dren’s Online Privacy Protection Act (COPPA) [79] in the US, consent is implemented in mobile apps. -
Wireguard in Eduvpn Report
WireGuard in eduVPN Report Nick Aquina SURF, Utrecht Fontys University of Applied Sciences, Eindhoven INTERNSHIP REPORT FONTYS UNIVERSITY OF APPLIED SCIENCES HBO-ICT Data student: Family name, initials: Aquina, N Student number: project period: (from – till) 31 August 2020 – 22 January 2021 Data company: Name company/institution: SURF Department: Team Security Address: Kantoren Hoog Overborch, 3511 EP Utrecht, Moreelsepark 48 Company tutor: Family name, initials: Spoor, R Position: (Tech) Product Manager University tutor: Family name, initials: Vos, A Final report: Title: WireGuard in eduVPN Date: 12 January 2021 Approved and signed by the company tutor: Date: 12 January 2021 Signature: Preface This report is written for my internship for Fontys. The internship was done at SURF for the eduVPN project. My task was to build a proof of concept in which WireGuard is integrated into eduVPN. This internship took place from September 2020 until January 2021. I would like to thank Arno Vos for his guidance and feedback throughout this internship. I would also like to thank Rogier Spoor for guiding me throughout this internship and inviting me to meetings which gave me a valuable insight into cyber security and technological issues facing members of SURF. And last, but not least, I would like to thank François Kooman for all technical support, advice and code reviews which helped improve the project. All blue text can be clicked to open a hyperlink. 1 Contents Preface . .1 Summary 4 Introduction 5 Free software . .5 The company (SURF) 6 Project 7 Context / Initial situation . .7 Project goal . .7 Assignment . .7 Constraints . .8 Development strategy . -

Petchain: a Blockchain-Based Privacy Enhancing Technology
Received February 5, 2021, accepted February 22, 2021, date of publication March 9, 2021, date of current version March 18, 2021. Digital Object Identifier 10.1109/ACCESS.2021.3064896 PETchain: A Blockchain-Based Privacy Enhancing Technology IBRAHIM TARIQ JAVED 1, FARES ALHARBI 2, TIZIANA MARGARIA 1, NOEL CRESPI 3, AND KASHIF NASEER QURESHI 4 1Lero—Science Foundation Ireland Research Centre for Software, University of Limerick, V94 T9PX Limerick, Ireland 2Computer Science Department, Shaqra University, Riyadh 11961, Saudi Arabia 3Institut Polytechnique de Paris, Telecom SudParis, 91011 Evry, France 4Department of Computer Science, Bahria University, Islamabad 44000, Pakistan Corresponding author: Ibrahim Tariq Javed ([email protected]) This work is partly supported with the financial support of the Science Foundation Ireland grant 13/RC/2094_P2 and partly funded from the European Union's Horizon 2020 research and innovation programme under the Marie Skªodowska-Curie grant agreement No 754489. ABSTRACT With the increasing use of smart devices and sensors, enormous amounts of data are being generated continuously. The data is commonly stored in centralized cloud platforms and consumed by different services. The data is indeed a valuable resource for many service providers who provide advanced features and utilities to their subscribers. However, user data include personal and sensitive information which can be misused in many ways. There is no way for a subscriber to confirm that their service provider is compliant with data privacy regulations. The existing privacy enhancing techniques such as anonymization and differential privacy substantially reduce data usability while ensuring privacy. Therefore, it remains essential to provide a feasible solution that allows service providers to take advantage of user data while guaranteeing their privacy. -

An Asterisk Monitoring Infrastructure Based on Nagios Radu State, Cristi Stefan
An Asterisk monitoring infrastructure based on Nagios Radu State, Cristi Stefan To cite this version: Radu State, Cristi Stefan. An Asterisk monitoring infrastructure based on Nagios. 2007. inria- 00172050 HAL Id: inria-00172050 https://hal.inria.fr/inria-00172050 Preprint submitted on 12 Nov 2007 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Deliverable Management of the Internet and Complex Services European Sixth Framework Network of Excellence FP6-2004-IST-026854-NoE Deliverable An Asterisk monitoring infrastructure based on Nagios Radu State, [email protected], Cristian Stefan, [email protected] The EMANICS Consortium Caisse des Dépôts et Consignations, CDC, France Institut National de Recherche en Informatique et Automatique, INRIA, France University of Twente, UT, The Netherlands Imperial College, IC, UK International University Bremen, IUB, Germany KTH Royal Institute of Technology, KTH, Sweden Oslo University College, HIO, Norway Universitat Politecnica de Catalunya, UPC, Spain University of Federal Armed Forces Munich, CETIM, Germany Poznan Supercomputing and Networking Center, PSNC, Poland University of Zürich, UniZH, Switzerland Ludwig-Maximilian University Munich, LMU, Germany University of Surrey, UniS, UK University of Pitesti, UniP, Romania © Copyright 2006 the Members of the EMANICS Consortium For more information on this document or the EMANICS Project, please contact: Dr. -

Pipenightdreams Osgcal-Doc Mumudvb Mpg123-Alsa Tbb
pipenightdreams osgcal-doc mumudvb mpg123-alsa tbb-examples libgammu4-dbg gcc-4.1-doc snort-rules-default davical cutmp3 libevolution5.0-cil aspell-am python-gobject-doc openoffice.org-l10n-mn libc6-xen xserver-xorg trophy-data t38modem pioneers-console libnb-platform10-java libgtkglext1-ruby libboost-wave1.39-dev drgenius bfbtester libchromexvmcpro1 isdnutils-xtools ubuntuone-client openoffice.org2-math openoffice.org-l10n-lt lsb-cxx-ia32 kdeartwork-emoticons-kde4 wmpuzzle trafshow python-plplot lx-gdb link-monitor-applet libscm-dev liblog-agent-logger-perl libccrtp-doc libclass-throwable-perl kde-i18n-csb jack-jconv hamradio-menus coinor-libvol-doc msx-emulator bitbake nabi language-pack-gnome-zh libpaperg popularity-contest xracer-tools xfont-nexus opendrim-lmp-baseserver libvorbisfile-ruby liblinebreak-doc libgfcui-2.0-0c2a-dbg libblacs-mpi-dev dict-freedict-spa-eng blender-ogrexml aspell-da x11-apps openoffice.org-l10n-lv openoffice.org-l10n-nl pnmtopng libodbcinstq1 libhsqldb-java-doc libmono-addins-gui0.2-cil sg3-utils linux-backports-modules-alsa-2.6.31-19-generic yorick-yeti-gsl python-pymssql plasma-widget-cpuload mcpp gpsim-lcd cl-csv libhtml-clean-perl asterisk-dbg apt-dater-dbg libgnome-mag1-dev language-pack-gnome-yo python-crypto svn-autoreleasedeb sugar-terminal-activity mii-diag maria-doc libplexus-component-api-java-doc libhugs-hgl-bundled libchipcard-libgwenhywfar47-plugins libghc6-random-dev freefem3d ezmlm cakephp-scripts aspell-ar ara-byte not+sparc openoffice.org-l10n-nn linux-backports-modules-karmic-generic-pae -

Jabber & IRC & SIP ICQ-, Chat- Und Skype-Ersatz Für Echte Männer
Jabber & IRC & SIP ICQ-, Chat- und Skype-Ersatz für echte Männer (und Frauen) Schwabacher Linux Tage 09 Überblick „Unschönes“ an proprietärer Kommunikation Rechtliche Grauzone EULAs IRC & Jabber: ICQ erschlagen SIP-Telefonie: Skype erschlagen Zusammenfassung Diskussion & Fragen Schwabacher Linux Tage 09 Worüber reden wir eigentlich? ICQ, MSN, Yahoo! & Co. „Kostenlose“ Chat- und Kurznachrichten-Dienste Unterstützen „Offline-Nachrichten“ Infrastrukturen in Amerika Es gelten amerikanische Bedingungen! Bieten proprietäre Client-Software für Windoos und Mac an Alternative Client-Software ist nicht erlaubt Schwabacher Linux Tage 09 Worüber reden wir eigentlich? (2) Skype „Kostenloser“ Dienst für Internet-Telefonie Ebay bietet proprietäre Client-Software für Windoos, Mac Schwabacher Linux Tage 09 Der Haken Dienste sind „kostenlos“: Der wahre Preis steht in der EULA! EULA Lang (Soll nicht gelesen werden?) Unverständliche juristische Formulierungen Für den Standardnutzer heute nur noch „Auf 'Akzeptieren' klicken. Ist ein bindender Vertrag! Schwabacher Linux Tage 09 Der Haken (2) [...] You agree that [...] you surrender your copyright and any other proprietary right in the posted material or information. You further agree that ICQ LLC. is entitled to use at its own discretion any of the posted material or information in any manner it deems fit, including, but not limited to, publishing the material or distributing it. [...] Schwabacher Linux Tage 09 Unbewusste Probleme Massenhaftes Sammeln personenbezogener Daten Datenschleudern/Datenhandel Abgrasen -
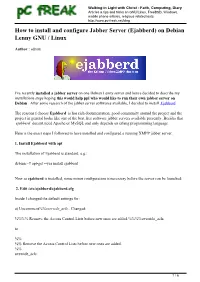
How to Install and Configure Jabber Server (Ejabberd) on Debian Lenny GNU / Linux
Walking in Light with Christ - Faith, Computing, Diary Articles & tips and tricks on GNU/Linux, FreeBSD, Windows, mobile phone articles, religious related texts http://www.pc-freak.net/blog How to install and configure Jabber Server (Ejabberd) on Debian Lenny GNU / Linux Author : admin I've recently installed a jabber server on one Debian Lenny server and hence decided to describe my installations steps hoping this would help ppl who would like to run their own jabber server on Debian . After some research of the jabber server softwares available, I decided to install Ejabberd The reasons I choose Ejabberd is has rich documentation, good community around the project and the project in general looks like one of the best free software jabber servers available presently. Besides that ejabberd doesn't need Apache or MySQL and only depends on erlang programming language. Here is the exact steps I followed to have installed and configured a running XMPP jabber server. 1. Install Ejabberd with apt The installation of Ejabberd is standard, e.g.: debian:~# apt-get --yes install ejabberd Now as ejabberd is installed, some minor configuration is necessery before the server can be launched: 2. Edit /etc/ejabberd/ejabberd.cfg Inside I changed the default settings for: a) Uncomment%%override_acls.. Changed: %%%% Remove the Access Control Lists before new ones are added.%%%%override_acls. to %% %% Remove the Access Control Lists before new ones are added. %% override_acls. 1 / 6 Walking in Light with Christ - Faith, Computing, Diary Articles & tips and tricks on GNU/Linux, FreeBSD, Windows, mobile phone articles, religious related texts http://www.pc-freak.net/blog b) Admin User from: %% Admin user {acl, admin, {user, "", "example.com"}}. -

Automatic Detection of Android Device Security Properties
Freie Universität Berlin Bachelorarbeit am Institut für Informatik der Freien Universität Berlin AG ID-Management Automatic Detection of Android Device Security Properties Janik Besendorf Matrikelnummer: xxx fvornameg.fnachnamegfatg f u − berlin.de Eingereicht bei: Prof. Dr. Marian Margraf Zweitgutachter: Prof. Dr. Jörn Eichler Berlin, May, 3, 2021 This work is licensed under CC BY-NC-SA cbea1 Abstract Smartphones are becoming more and more popular. As a result smartphone security is an increasingly important subject, especially with state actors discussing eIDs on smartphones. However, information about a smartphone’s specific security features is not readily available. There has been research to automatically gather smartphone security features, but the properties collected are not sufficient for evaluation of a smartphone’s compliance to eID regulations such as eIDAS. In our thesis we explore sources of such information and aggregate information from these sources using web scraping, and by gathering information with an Android app. We found that most of the information required for evaluation according to eIDAS is available to the public and suitable for automatic aggregation. However, since information on websites is sparse, usually an app on a smartphone is required to gather all information. Also, information about security certifications is not readily available. We conclude that the stakeholders in the smartphone market should make an effort to improve this situation by providing more information on public websites and by increasing machine-readability of this information. 1https://creativecommons.org/licenses/by-nc-sa/4.0 1 Eidesstattliche Erklärung Ich versichere hiermit an Eides Statt, dass diese Arbeit von niemand anderem als meiner Person verfasst worden ist.