Remote Access Forensics for VNC and RDP on Windows Platform
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
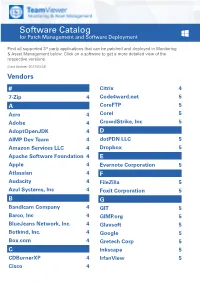
Software Catalog for Patch Management and Software Deployment
Software Catalog for Patch Management and Software Deployment Find all supported 3rd party applications that can be patched and deployed in Monitoring & Asset Management below. Click on a software to get a more detailed view of the respective versions. (Last Update: 2021/03/23) Vendors # Citrix 4 7-Zip 4 Code4ward.net 5 A CoreFTP 5 Acro 4 Corel 5 Adobe 4 CrowdStrike, Inc 5 AdoptOpenJDK 4 D AIMP Dev Team 4 dotPDN LLC 5 Amazon Services LLC 4 Dropbox 5 Apache Software Foundation 4 E Apple 4 Evernote Corporation 5 Atlassian 4 F Audacity 4 FileZilla 5 Azul Systems, Inc 4 Foxit Corporation 5 B G Bandicam Company 4 GIT 5 Barco, Inc 4 GIMP.org 5 BlueJeans Network, Inc. 4 Glavsoft 5 Botkind, Inc. 4 Google 5 Box.com 4 Gretech Corp 5 C Inkscape 5 CDBurnerXP 4 IrfanView 5 Cisco 4 Software Catalog for Patch Management and Software Deployment J P Jabra 5 PeaZip 10 JAM Software 5 Pidgin 10 Juraj Simlovic 5 Piriform 11 K Plantronics, Inc. 11 KeePass 5 Plex, Inc 11 L Prezi Inc 11 LibreOffice 5 Programmer‘s Notepad 11 Lightning UK 5 PSPad 11 LogMeIn, Inc. 5 Q M QSR International 11 Malwarebytes Corporation 5 Quest Software, Inc 11 Microsoft 6 R MIT 10 R Foundation 11 Morphisec 10 RarLab 11 Mozilla Foundation 10 Real 11 N RealVNC 11 Neevia Technology 10 RingCentral, Inc. 11 NextCloud GmbH 10 S Nitro Software, Inc. 10 Scooter Software, Inc 11 Nmap Project 10 Siber Systems 11 Node.js Foundation 10 Simon Tatham 11 Notepad++ 10 Skype Technologies S.A. -

Windows Phone App Security for Builders and Breakers
Windows Phone App Security for builders and breakers Luca De Fulgentis ~ [email protected] May 22nd, 2015 | Amsterdam About /me . Luca De Fulgentis ~ @_daath . Chief Technology Officer at Secure Network . OWASP Mobile Project Contributor . Nibble Security co-founder - blog.nibblesec.org . Consuming brain-power with InfoSec since 2001 2 Agenda . Introduction – Research overview and motivations . Mobile Top Ten for Windows Phone – Examples of real-world vulnerable code – Discussion on potential insecure APIs usage – Secure coding tips for builders . Final considerations Windows Phone App Security 3 Introduction . In 2014 we collected examples of insecure code for Windows Phone apps – Set of 60+ samples, of which 30% of mobile banking apps – Mostly developed with the Silverlight 8.x technology . Statistics on the initial study has been shared with the OWASP Mobile Project for the MTT 2015 definition . Later, we extended our research developing an automated script that allowed downloading 160+ AppX from US and IT regions of the WP Store – We needed to cover WP 8.1 Windows Runtime (WinRT) security as well Windows Phone App Security 4 Introduction – motivations . Too few (public) resources on WP apps security – MWR’s «Navigation a Sea of Pwn?» (SyScan, 2014) - pretty amazing paper on the topic – XDA Forum represents an invaluable source of information . We want both builders and breakers to be happy! – Provide a wide range of common APIs (MSDN) categorized on the basis of MTT 2014 and also define methods and strategies to mitigate these risks . We defined a public catalog of potentially insecure APIs – Focus on C#/XAML apps, still the most relevant development technologies . -

Realvnc @ LC August 2018 LC User Meeting
RealVNC @ LC August 2018 LC User Meeting Cameron Harr Title (optional) Aug. 21, 2018 LLNL-PRES-XXXXXX This work was performed under the auspices of the U.S. Department of Energy by Lawrence Livermore National Laboratory under contract DE-AC52-07NA27344. Lawrence Livermore National Security, LLC RealVNC @ LC § What is RealVNC? § What did we have? § What do we have now? § What’s coming in the future? § How do you use it? 2 LLNL-PRES-xxxxxx Cloud versus direct with VNC Connect VNC Connect is unique among remote access software in its ability to offer both cloud and direct connectivity methods within a single product. At first glance, knowing whether to connect directly or via our cloud service can seem confusing. However, there are clear benefits to each connection method. The trick is knowing how to maximize these benefits. This brief product guide provides an overview of the differences between cloud and direct connectivity, and offers some advice on how each method can be used to your greatest advantage. Key terminology Throughout this guide, we refer to certain RealVNC-specific terminology. VNC Connect is comprised of two separate apps: VNC Server and VNC Viewer. You must install and license VNC Server on the computer you want to control. This is known as your VNC Server computer. You must then install VNC Viewer on the computer or device you want to take control from, which is known as your VNC Viewer device. You do not need to license this device, meaning you can freely connect to your VNC Server computer from as many devices as you wish. -

Pass Microsoft 70-697 Exam with 100% Guarantee
https://www.certbus.com/70-697.html 2021 Latest certbus 70-697 PDF and VCE dumps Download 70-697Q&As Configuring Windows Devices Pass Microsoft 70-697 Exam with 100% Guarantee Free Download Real Questions & Answers PDF and VCE file from: https://www.certbus.com/70-697.html 100% Passing Guarantee 100% Money Back Assurance Following Questions and Answers are all new published by Microsoft Official Exam Center 70-697 Practice Test | 70-697 Study Guide | 70-697 Braindumps 1 / 13 https://www.certbus.com/70-697.html 2021 Latest certbus 70-697 PDF and VCE dumps Download QUESTION 1 You provide IT support for a small startup company. The company wants users to have Read and Write permissions to the company\\'s shared folder. The network consists of a workgroup that uses Windows 10 Enterprise computers. You add each user to a group named NetworkUsers. You need to grant permissions to the share. You have the following requirements: All users must have Read and Write access to existing files. Any new files must allow the creator to modify the new file\\'s permissions. Which two actions should you take? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point. A. Grant Modify permissions to the NetworkUsers group on the shared folder. B. Grant Full Control permissions to the Domain Admins group on the shared folder. C. Grant List and Execute permissions to the NetworkUsers group on the shared folder. D. Grant Full Control permissions to the Creator Owner group on the shared folder. -

VNC Connect Security Whitepaper
VNC Connect security whitepaper VNC Connect security whitepaper Version 1.3 Contents Contents .................................................................................................................................................................... 2 Introduction ............................................................................................................................................................... 3 Security architecture ................................................................................................................................................. 4 Cloud infrastructure ................................................................................................................................................... 7 Client security ........................................................................................................................................................... 9 Development procedures ........................................................................................................................................ 12 Summary ................................................................................................................................................................. 13 VNC Connect security whitepaper Introduction Customer security is of paramount importance to RealVNC. As such, our security strategy is ingrained in all aspects of our VNC Connect software. We have invested extensively in our security, and take great pride in our successful -

Repair up to 32 Major Windows Errors Using a Single Tool R 400/1
R 400.qxp_March 2018 30/01/2018 14:07 Page 15 Repair Your Windows System R 400/1 Repair Up to 32 Major Windows Errors Using a Single Tool Using the information given in this article you will be able to: Create a restore point to protect your system against damage, Repair up to 32 different errors with just one mouse click, Select and correct a specific Windows problem. No Windows system is error-free! Most people are content to simply tolerate minor Windows bugs, because they don’t have the time to hunt for the cause of the error. But small bugs can quickly spiral out of control, so it is important you deal with them fast. There are many tools on the market that claim to help you fix errors, but lots of them are expensive and don’t actually work. In my PC workshop, I use the Windows Repair tool. You can use this tool to look for errors, correct problematic settings and configure Windows to be more stable. And the best thing is that this tool is completely free. In this article, I’ll show you which errors Windows Repair can solve and how to successfully use this tool in practice. • Perform a Professional Error Check on Your Windows System .............................................................. R 400/2 • Important: Create a System Restore Point Before Applying Any Fixes ........................................................... R 400/3 • Use Windows Repair to Quickly Fix Your System ......... R 400/4 • Additi onal Repair Options in Windows Repair .............. R 400/5 • Back up Your Registry and Create a Restore Point ...... -
IBM Endpoint Manager for Remote Control Installation Guide Chapter 1
IBMEndpointManagerforRemoteControl Installation Guide Version 9.0.0 IBMEndpointManagerforRemoteControl Installation Guide Version 9.0.0 Note Before using this information and the product it supports, read the information in “Notices” on page 115. This edition applies to version 9, release 0, modification level 0 of IBM Endpoint Manager and to all subsequent releases and modifications until otherwise indicated in new editions. Contents Chapter 1. IBM Endpoint Manager for Installing Windows broker support .....63 Remote Control Installation Guide . 1 Installing Linux broker support.......64 Audience ...............1 Versions ................1 Chapter 5. Utility for extracting the Terms used in this guide ..........1 component installation files .....65 Using the additional setup utility .......65 Chapter 2. Overview of the IBM Endpoint Manager for Remote Control system . 3 Chapter 6. Managing the component Using this guide .............5 services ..............67 IBM Endpoint Manager for Remote Control operating Starting, stopping, or restarting the Windows requirements ..............5 components ..............67 A Basic installation ...........6 Starting, stopping, or restarting the Linux Installation with support for firewall and NAT components ..............67 traversal ...............7 Installation with support for remote control Chapter 7. Performing required sessions over the internet .........8 configuration ............69 Server requirements ...........9 Enabling email .............69 Server environment guidelines .......10 Configuring -

Accessing Remote Desktop Using VNC on Dell Poweredge Servers
Accessing Remote Desktop using VNC on Dell PowerEdge Servers and MX7000 Modular Infrastructure This technical white paper provides information about establishing secure remote desktop connections to server host operating systems (OS) by using the standard VNC clients. Abstract Dell EMC PowerEdge servers support efficient and secure remote management tools. Virtual Network Computing (VNC) technology is incorporated in the iDRAC Enterprise firmware to support open and easy-to-use remote desktop functionality. This functionality is in addition to the browser-based remote console support accessible on the iDRAC GUI. September 2018 Dell EMC Technical White Paper Revisions Revisions Date Description Sep 2018 Initial release Acknowledgements This paper was produced by the following members of the Dell EMC Server and Infrastructure Systems team: Authors Saurabh Kishore — Software Principal Engineer Alex Rote — Software Senior Engineer The information in this publication is provided “as is.” Dell Inc. makes no representations or warranties of any kind with respect to the information in this publication, and specifically disclaims implied warranties of merchantability or fitness for a particular purpose. Use, copying, and distribution of any software described in this publication requires an applicable software license. © <Sep/12/2018> Dell Inc. or its subsidiaries. All Rights Reserved. Dell, EMC, Dell EMC and other trademarks are trademarks of Dell Inc. or its subsidiaries. Other trademarks may be trademarks of their respective owners. Dell believes the information in this document is accurate as of its publication date. The information is subject to change without notice. 2 Accessing Remote Desktop using VNC on Dell PowerEdge Servers and MX7000 Modular Infrastructure Acknowledgements Contents Revisions............................................................................................................................................................................ -

Free Open Source Vnc
Free open source vnc click here to download TightVNC - VNC-Compatible Remote Control / Remote Desktop Software. free for both personal and commercial usage, with full source code available. TightVNC - VNC-Compatible Remote Control / Remote Desktop Software. It's completely free but it does not allow integration with closed-source products. UltraVNC: Remote desktop support software - Remote PC access - remote desktop connection software - VNC Compatibility - FileTransfer - Encryption plugins - Text chat - MS authentication. This leading-edge, cloud-based program offers Remote Monitoring & Management, Remote Access &. Popular open source Alternatives to VNC Connect for Linux, Windows, Mac, Self- Hosted, BSD and Free Open Source Mac Windows Linux Android iPhone. Download the original open source version of VNC® remote access technology. Undeniably, TeamViewer is the best VNC in the market. Without further ado, here are 8 free and some are open source VNC client/server. VNC remote access software, support server and viewer software for on demand remote computer support. Remote desktop support software for remote PC control. Free. All VNCs Start from the one piece of source (See History of VNC), and. TigerVNC is a high- performance, platform-neutral implementation of VNC (Virtual Network Computing), Besides the source code we also provide self-contained binaries for bit and bit Linux, installers for Current list of open bounties. VNC (Virtual Network Computing) software makes it possible to view and fully- interact with one computer from any other computer or mobile. Find other free open source alternatives for VNC. Open source is free to download and remember that open source is also a shareware and freeware alternative. -
VNC User Guide 7 About This Guide
VNC® User Guide Version 5.3 December 2015 Trademarks RealVNC, VNC and RFB are trademarks of RealVNC Limited and are protected by trademark registrations and/or pending trademark applications in the European Union, United States of America and other jursidictions. Other trademarks are the property of their respective owners. Protected by UK patent 2481870; US patent 8760366 Copyright Copyright © RealVNC Limited, 2002-2015. All rights reserved. No part of this documentation may be reproduced in any form or by any means or be used to make any derivative work (including translation, transformation or adaptation) without explicit written consent of RealVNC. Confidentiality All information contained in this document is provided in commercial confidence for the sole purpose of use by an authorized user in conjunction with RealVNC products. The pages of this document shall not be copied, published, or disclosed wholly or in part to any party without RealVNC’s prior permission in writing, and shall be held in safe custody. These obligations shall not apply to information which is published or becomes known legitimately from some source other than RealVNC. Contact RealVNC Limited Betjeman House 104 Hills Road Cambridge CB2 1LQ United Kingdom www.realvnc.com Contents About This Guide 7 Chapter 1: Introduction 9 Principles of VNC remote control 10 Getting two computers ready to use 11 Connectivity and feature matrix 13 What to read next 17 Chapter 2: Getting Connected 19 Step 1: Ensure VNC Server is running on the host computer 20 Step 2: Start VNC -
Test Result Report for Anydesk
Performance Test Results Report Prepared for AnyDesk For period 08/31/2020 – 09/09/2020 Reporter: Aliaksandr Hryshutsin Page: 1 of 13 Creation Date: 9/21/2020 Contents 1 Testing Approach ........................................................................................................................................... 3 1.1 Types of Tests ......................................................................................................................................... 3 1.2 Test set-up ............................................................................................................................................... 3 2 Summary on Test Results .............................................................................................................................. 4 2.1 Summary ................................................................................................................................................. 4 3 Test results ..................................................................................................................................................... 4 3.1 Framerate ................................................................................................................................................ 4 3.2 Latency .................................................................................................................................................... 5 3.3 Bandwidth ............................................................................................................................................... -

Unpermitted Resources
Process Check and Unpermitted Resources Common and Important Virtual Machines Parallels VMware VirtualBox CVMCompiler Windows Virtual PC Other Python Citrix Screen/File Sharing/Saving .exe File Name VNC, VPN, RFS, P2P and SSH Virtual Drives ● Dropbox.exe ● Dropbox ● OneDrive.exe ● OneDrive ● <name>.exe ● Google Drive ● etc. ● iCloud ● etc. Evernote / One Note ● Evernote_---.exe ● onenote.exe Go To Meeting ● gotomeeting launcher.exe / gotomeeting.exe TeamViewer ● TeamViewer.exe Chrome Remote ● remoting_host.exe www.ProctorU.com ● [email protected] ● 8883553043 Messaging / Video (IM, IRC) / .exe File Name Audio Bonjour Google Hangouts (chrome.exe - shown as a tab) (Screen Sharing) Skype SkypeC2CPNRSvc.exe Music Streaming ● Spotify.exe (Spotify, Pandora, etc.) ● PandoraService.exe Steam Steam.exe ALL Processes Screen / File Sharing / Messaging / Video (IM, Virtual Machines (VM) Other Saving IRC) / Audio Virtual Box Splashtop Bonjour ● iChat ● iTunes ● iPhoto ● TiVo ● SubEthaEdit ● Contactizer, ● Things ● OmniFocuse phpVirtualBox TeamViewer MobileMe Parallels Sticky Notes Team Speak VMware One Note Ventrilo Windows Virtual PC Dropbox Sandboxd QEM (Linux only) Chrome Remote iStumbler HYPERBOX SkyDrive MSN Chat Boot Camp (dual boot) OneDrive Blackboard Chat CVMCompiler Google Drive Yahoo Messenger Office (Word, Excel, Skype etc.) www.ProctorU.com ● [email protected] ● 8883553043 2X Software Notepad Steam AerooAdmin Paint Origin AetherPal Go To Meeting Spotify Ammyy Admin Jing Facebook Messenger AnyDesk