Jordan Hubbard's Talk
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Secure Browser Installation Guide –
Commercial Online Banking: Corporate First Mid Bank & Trust Commercial Online Banking Secure Browser Installation Guide for Mac Commercial Online Banking: Corporate Commercial Online Banking Secure Browser Commercial Online Banking Secure Browser is a secure solution that helps to provide a hardened stance against fraud. From new client implementation to ongoing support, Secure Browser offers a smooth customer experience. • Secure Site Access with consistent user & device authentication • Not susceptiBle to malware attacks • Prevents misdirection of users to false sites • Reduce risk By avoiding sites with malware • Eliminate hard tokens or 3rd party security products • Data integrity Getting Started - Installation In order to access Commercial Online Banking, users must install the Secure Browser on your PC. First Mid’s Secure Browser is a java-based application that runs on a user’s computer and which provides a captive, safe environment for accessing Commercial Online Banking and other weB sites that are permitted to the company by First Mid Bank & Trust. Secure Browser is a fully self-contained browser that does not use any other internet browser previously installed on a user’s computer, thereby insulating it from any malware that might Be attached to those other browsers. Users are allowed access to only web sites and applications defined and configured by the bank. Secure Browser does not produce an address line, so it is impossible for users to navigate away from entitled sites. All users are required by First Mid Bank & Trust to use the Secure Browser to access Commercial Online Banking. Getting Started • Secure Browser Installation | 2 Commercial Online Banking: Corporate Before You Begin Ensure You Have: • Strong internet connection • Administrative User privileges for the computer Secure Browser is to Be installed. -
Kinect in Mac: QC and Processing
Kinect in Mac: Quartz Composer and Processing A brief tutorial by NIRTeam @ TEI Crete Contents ● Using Quartz Composer with Kinect ● Using Processing programming language with kinect ● 3D scanning using Kinect Quartz Composer (QC) ● Node-based visual programming language used mainly for processing and rendering graphics. ● Included in the Xcode developer tools package by Apple ● Quartz Composer uses OpenGL (including GLSL), OpenCL, Core Image, Core Video, JavaScript, and other technologies to build an API and a developer tool Data types inside QC Boolean - a boolean value, 0 or 1 Index - a positive integer between 0 and 2147483647 Number - a double precision floating point number String - a unicode string Color - an RGBA or CMYK quartet, or a Grayscale value Image - a 2D image of arbitrary (possibly infinite) dimensions Structure - a named or ordered collection of objects, including nested structures Virtual - any of the above Mesh - a collection of vertices, and per-vertex normals, texture coordinates, and colors in 3-space. Interaction - a valueless type used to associate user input with user-interactive elements of the composition. QC Programming QC Programming = connecting different nodes (Patches). QC Patches The patches are divided into three categories: 1. “Providers” 2. “Processors” 3. “Consumers” QC resources - http://kineme.net/ - http://quartzcomposer.com/compositions - http://www.quartzcompositions.com/ - http://guides.macrumors.com/Quartz_Composer Kinect & QC Kineme KinectTools plugin http://kineme.net/KinectTools Synapse plugin http://synapsekinect.tumblr.com/ v002 open Kinect example http://kineme.net/forum/Discussion/Programming/v002OpenKinectBeta Quartz-Composer-Open-Kinect-Plugin https://github.com/stoulouse/Quartz-Composer-Open-Kinect-Plugin UIO Kinect with TUIO client QC Plugin https://code.google.com/p/tuiokinect/ http://prdownloads.sourceforge.net/reactivision/TUIO_Quartz-1.4.zip?download Tryplex Toolkit http://code.google.com/p/tryplex/ Kinect & QC: Kineme KinectTools plugin ● Retrieves color and depth image data from the Kinect. -
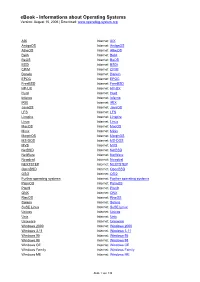
Ebook - Informations About Operating Systems Version: August 15, 2006 | Download
eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org AIX Internet: AIX AmigaOS Internet: AmigaOS AtheOS Internet: AtheOS BeIA Internet: BeIA BeOS Internet: BeOS BSDi Internet: BSDi CP/M Internet: CP/M Darwin Internet: Darwin EPOC Internet: EPOC FreeBSD Internet: FreeBSD HP-UX Internet: HP-UX Hurd Internet: Hurd Inferno Internet: Inferno IRIX Internet: IRIX JavaOS Internet: JavaOS LFS Internet: LFS Linspire Internet: Linspire Linux Internet: Linux MacOS Internet: MacOS Minix Internet: Minix MorphOS Internet: MorphOS MS-DOS Internet: MS-DOS MVS Internet: MVS NetBSD Internet: NetBSD NetWare Internet: NetWare Newdeal Internet: Newdeal NEXTSTEP Internet: NEXTSTEP OpenBSD Internet: OpenBSD OS/2 Internet: OS/2 Further operating systems Internet: Further operating systems PalmOS Internet: PalmOS Plan9 Internet: Plan9 QNX Internet: QNX RiscOS Internet: RiscOS Solaris Internet: Solaris SuSE Linux Internet: SuSE Linux Unicos Internet: Unicos Unix Internet: Unix Unixware Internet: Unixware Windows 2000 Internet: Windows 2000 Windows 3.11 Internet: Windows 3.11 Windows 95 Internet: Windows 95 Windows 98 Internet: Windows 98 Windows CE Internet: Windows CE Windows Family Internet: Windows Family Windows ME Internet: Windows ME Seite 1 von 138 eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org Windows NT 3.1 Internet: Windows NT 3.1 Windows NT 4.0 Internet: Windows NT 4.0 Windows Server 2003 Internet: Windows Server 2003 Windows Vista Internet: Windows Vista Windows XP Internet: Windows XP Apple - Company Internet: Apple - Company AT&T - Company Internet: AT&T - Company Be Inc. - Company Internet: Be Inc. - Company BSD Family Internet: BSD Family Cray Inc. -

Mac OS X Server Administrator's Guide
034-9285.S4AdminPDF 6/27/02 2:07 PM Page 1 Mac OS X Server Administrator’s Guide K Apple Computer, Inc. © 2002 Apple Computer, Inc. All rights reserved. Under the copyright laws, this publication may not be copied, in whole or in part, without the written consent of Apple. The Apple logo is a trademark of Apple Computer, Inc., registered in the U.S. and other countries. Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, AppleScript, AppleShare, AppleTalk, ColorSync, FireWire, Keychain, Mac, Macintosh, Power Macintosh, QuickTime, Sherlock, and WebObjects are trademarks of Apple Computer, Inc., registered in the U.S. and other countries. AirPort, Extensions Manager, Finder, iMac, and Power Mac are trademarks of Apple Computer, Inc. Adobe and PostScript are trademarks of Adobe Systems Incorporated. Java and all Java-based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Netscape Navigator is a trademark of Netscape Communications Corporation. RealAudio is a trademark of Progressive Networks, Inc. © 1995–2001 The Apache Group. All rights reserved. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. 062-9285/7-26-02 LL9285.Book Page 3 Tuesday, June 25, 2002 3:59 PM Contents Preface How to Use This Guide 39 What’s Included -

Learn Yosemite OS X from PCM's Apple Experts
Learn Yosemite OS X from PCM’s Apple Experts Yosemite 101: OS X Support Essentials Give PCM the opportunity to train your team to support users of Apple’s Mac OS X Yosemite. Our Apple certified trainers are ready to come to your location and provide PCM’s Apple certified trainers will teach your team Yosemite OS X fundamentals and how to be efficient with you with invaluable Yosemite tools and resources. hands-on instruction. OS X Yosemite Support Essentials is a three-day, Who Should Attend hands-on course that provides an in-depth explo- • Help desk specialists, technical coordinators, ration of troubleshooting on Mac OS X v10.10 Yo- service technicians, and others who support semite. This course is designed to give you a tour Mac users. of the breadth of functionality of Mac OS X v10.10 • Technical support personnel in businesses that Yosemite and the best methods for effectively use Macs. supporting users of Mac OS X v10.10 Yosemite • Technical coordinators or power users who systems. The course is a combination of lectures manage networks of computers running and hands-on case study exercises that provide Mac OS X — such as teachers and technology practical real-world experience. specialists who manage networks or computer labs. At your location For a class at your location, PCM will provide an What You Will Learn Apple Certified Trainer, all the student materials, • The troubleshooting process and how to and an exam voucher for each attendee (up to become more efficient with available tools 6 students included in price). -

Introduction Use Runit with Traditional Init (Sysvinit)
2021/07/26 19:10 (UTC) 1/12 Runit Runit Introduction runit is a UNIX init scheme with service supervision. It is a cross-platform Unix init scheme with service supervision, a replacement for sysvinit, and other init schemes and supervision that are used with the traditional init. runit is compatible with djb's daemontools. In Unix-based computer operating systems, init (short for initialization) is the first process started during booting of the computer system. Init is a daemon process that continues running until the system is shut down. Slackware comes with its own legacy init (/sbin/init) from the sysvinit package, that used to be included in almost all other major Linux distributions. The init daemon (or its replacement) is characterised by Process ID 1 (PID 1). To read on the benefits of runit, see here: http://smarden.org/runit/benefits.html * Unless otherwise stated, all commands in this article are to be run by root. Use runit with traditional init (sysvinit) runit is not provided by Slackware, but a SlackBuild is maintained on https://slackbuilds.org/. It does not have any dependencies. As we do not want yet to replace init with runit, run the slackbuild with CONFIG=no: CONFIG=no ./runit.SlackBuild Then install the resulting package and proceed as follows: mkdir /etc/runit/ /service/ cp -a /usr/doc/runit-*/etc/2 /etc/runit/ /sbin/runsvdir-start & Starting via rc.local For a typical Slackware-stlyle service, you can edit /etc/rc.d/rc.local file if [ -x /sbin/runsvdir-start ]; then /sbin/runsvdir-start & fi and then edit write /etc/rc.d/rc.local_shutdown #!/bin/sh SlackDocs - https://docs.slackware.com/ Last update: 2020/05/06 08:08 (UTC) howtos:slackware_admin:runit https://docs.slackware.com/howtos:slackware_admin:runit RUNIT=x$( /sbin/pidof runsvdir ) if [ "$RUNIT" != x ]; then kill $RUNIT fi Then give rc.local_shutdown executive permission: chmod +x /etc/rc.d/rc.local_shutdown and reboot Starting via inittab (supervised) Remove the entries in /etc/rc.d/rc.local and /etc/rc.d/rc.local_shutdown described above. -
Next-Generation Cryptographic Services I’M Going to Tell You, and I Won’T Kill You
Next-Generation Cryptographic Services I’m going to tell you, and I won’t kill you Session 212 Jon Callas Security Privateer These are confidential sessions—please refrain from streaming, blogging, or taking pictures 1 Introduction • Learn about exciting changes to Apple’s cryptographic architecture • First major reworking of crypto in a decade 2 What You Will Learn • Changes to existing APIs • New Transform API • How to use Apple’s Transform library • How to create your own custom Transforms 3 CDSA Common Data Security Architecture 4 CDSA Is Deprecated • It is a creature of its time • That time is the late 1990s • It is a thinly used, Open Group standard ■ All of the costs, few of the benefits • Only a Mac OS API, not iOS 5 Deprecated Does Not Mean Canceled • CDSA is still available • Start migrating away now • Some parts of Security Framework have layering issues with CDSA ■ Those parts are deprecated, too 6 Requirements for a Replacement Design for the decades ahead • Less code • Faster code • Concurrent code • Flexible programming ■ Crypto includes ciphers, compression, XML, networking, REST, LDAP, databases… 7 New Crypto Architecture • Low-level (pointer, length) Security Framework Core Foundation • Basic core algorithms • FoundationOnly for on FIPS 140 Transforms Core Foundation validation Mac OS • Traditional crypto toolkit CommonCrypto C-language programming • Documentation in man pages ■ man CC_crypto 8 New CommonCrypto Architecture • Starts from Snow Leopard’s CommonCrypto • Recoded internals ■ Both Mac OS, iOS ■ NIST algorithm -

Mac OS X: an Introduction for Support Providers
Mac OS X: An Introduction for Support Providers Course Information Purpose of Course Mac OS X is the next-generation Macintosh operating system, utilizing a highly robust UNIX core with a brand new simplified user experience. It is the first successful attempt to provide a fully-functional graphical user experience in such an implementation without requiring the user to know or understand UNIX. This course is designed to provide a theoretical foundation for support providers seeking to provide user support for Mac OS X. It assumes the student has performed this role for Mac OS 9, and seeks to ground the student in Mac OS X using Mac OS 9 terms and concepts. Author: Robert Dorsett, manager, AppleCare Product Training & Readiness. Module Length: 2 hours Audience: Phone support, Apple Solutions Experts, Service Providers. Prerequisites: Experience supporting Mac OS 9 Course map: Operating Systems 101 Mac OS 9 and Cooperative Multitasking Mac OS X: Pre-emptive Multitasking and Protected Memory. Mac OS X: Symmetric Multiprocessing Components of Mac OS X The Layered Approach Darwin Core Services Graphics Services Application Environments Aqua Useful Mac OS X Jargon Bundles Frameworks Umbrella Frameworks Mac OS X Installation Initialization Options Installation Options Version 1.0 Copyright © 2001 by Apple Computer, Inc. All Rights Reserved. 1 Startup Keys Mac OS X Setup Assistant Mac OS 9 and Classic Standard Directory Names Quick Answers: Where do my __________ go? More Directory Names A Word on Paths Security UNIX and security Multiple user implementation Root Old Stuff in New Terms INITs in Mac OS X Fonts FKEYs Printing from Mac OS X Disk First Aid and Drive Setup Startup Items Mac OS 9 Control Panels and Functionality mapped to Mac OS X New Stuff to Check Out Review Questions Review Answers Further Reading Change history: 3/19/01: Removed comment about UFS volumes not being selectable by Startup Disk. -

Absolute BSD—The Ultimate Guide to Freebsd Table of Contents Absolute BSD—The Ultimate Guide to Freebsd
Absolute BSD—The Ultimate Guide to FreeBSD Table of Contents Absolute BSD—The Ultimate Guide to FreeBSD............................................................................1 Dedication..........................................................................................................................................3 Foreword............................................................................................................................................4 Introduction........................................................................................................................................5 What Is FreeBSD?...................................................................................................................5 How Did FreeBSD Get Here?..................................................................................................5 The BSD License: BSD Goes Public.......................................................................................6 The Birth of Modern FreeBSD.................................................................................................6 FreeBSD Development............................................................................................................7 Committers.........................................................................................................................7 Contributors........................................................................................................................8 Users..................................................................................................................................8 -
SUSE® Linux Enterprise Desktop 12 and the Workstation Extension: What's New ?
SUSE® Linux Enterprise Desktop 12 and the Workstation Extension: What's New ? Frédéric Crozat <[email protected]> Enterprise Desktop Release Manager Scott Reeves <[email protected]> Enterprise Desktop Development Manager Agenda • Design Criteria • Desktop Environment in SUSE Linux Enterprise 12 • GNOME Shell • Desktop Features and Applications 2 Design Criteria SUSE Linux Enterprise Desktop Interoperability Ease of Use Security Ease of Management Lower Costs 4 SUSE Linux Enterprise Desktop 12 • Focus on technical workstation ‒ Developers and System administrators • One tool for the job • Main desktop applications will be shipped: ‒ Mail client, Office Suite, Graphical Editors, ... • SUSE Linux Enterprise Workstation Extension ‒ Extend SUSE Linux Enterprise Server with packages only available on SUSE Linux Enterprise Desktop. (x86-64 only) 5 Desktop in SUSE Linux Enterprise 12 As Part of the Common Code Base SUSE Linux Enterprise 12 Desktop Environment • SUSE Linux Enterprise 12 contains one primary desktop environment • Additional light-weight environment for special use-cases: ‒ Integrated Systems • Desktop environment is shared between the server and desktop products 7 SUSE Linux Enterprise 12 Desktop Environment • GNOME 3 is the main desktop environment ‒ SLE Classic mode by default ‒ GNOME 3 Classic Mode and GNOME 3 Shell Mode also available • SUSE Linux Enterprise 12 ships also lightweight IceWM ‒ Targeted at Integrated Systems • QT fully supported: ‒ QT5 supported for entire SLE12 lifecycle ‒ QT4 supported, will be removed in future -

Carbon Copy Cloner Documentation: English
Carbon Copy Cloner Documentation: English Getting started with CCC System Requirements, Installing, Updating, and Uninstalling CCC CCC License, Registration, and Trial FAQs Trouble Applying Your Registration Information? Establishing an initial backup Preparing your backup disk for a backup of Mac OS X Restoring data from your backup What's new in CCC Features of CCC specific to Lion and greater Release History Carbon Copy Cloner's Transition to a Commercial Product: Frequently Asked Questions Credits Example backup scenarios I want to clone my entire hard drive to a new hard drive or a new machine I want to backup my important data to another Macintosh on my network I want to backup multiple machines or hard drives to the same hard drive I want my backup task to run automatically on a scheduled basis Backing up to/from network volumes and other non-HFS volumes I want to back up my whole Mac to a Time Capsule or other network volume I want to defragment my hard drive Backup and archiving settings Excluding files and folders from a backup task Protecting data that is already on your destination volume Managing previous versions of your files Automated maintenance of CCC archives Advanced Settings Some files and folders are automatically excluded from a backup task The Block-Level Copy Scheduling Backup Tasks Scheduling a task and basic settings Performing actions Before and After the backup task Deferring and skipping scheduled tasks Frequently asked questions about scheduled tasks Email and Growl notifications Backing Up to Disk Images -

Security Analysis and Decryption of Lion Full Disk Encryption
Infiltrate the Vault: Security Analysis and Decryption of Lion Full Disk Encryption Omar Choudary Felix Grobert¨ ∗ Joachim Metz ∗ University of Cambridge [email protected] [email protected] [email protected] Abstract 1 Introduction Since the launch of Mac OS X 10.7, also known as Lion, With the launch of Mac OS X 10.7 (Lion), Apple has Apple includes a volume encryption software named introduced a volume encryption mechanism known as FileVault 2 [8] in their operating system. While the pre- FileVault 2. Apple only disclosed marketing aspects of vious version of FileVault (introduced with Mac OS X the closed-source software, e.g. its use of the AES-XTS 10.3) only encrypted the home folder, FileVault 2 can en- tweakable encryption, but a publicly available security crypt the entire volume containing the operating system evaluation and detailed description was unavailable until (this is commonly referred to as full disk encryption). now. This has two major implications: first, there is now a new functional layer between the encrypted volume and We have performed an extensive analysis of the original file system (typically a version of HFS Plus). FileVault 2 and we have been able to find all the This new functional layer is actually a full volume man- algorithms and parameters needed to successfully read ager which Apple called CoreStorage [10] Although this an encrypted volume. This allows us to perform forensic full volume manager could be used for more than volume investigations on encrypted volumes using our own encryption (e.g. mirroring, snapshots or online storage tools.