Application Layer Protocol Confusion in TLS Authentication
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Raccoon Attack: Finding and Exploiting Most-Significant-Bit
Raccoon Attack: Finding and Exploiting Most-Significant-Bit-Oracles in TLS-DH(E) Robert Merget,1 Marcus Brinkmann,1 Nimrod Aviram,2 Juraj Somorovsky,3 Johannes Mittmann,4 Jörg Schwenk1 Real World Crypto 2021 1 Ruhr University Bochum 2 Department of Electrical Engineering, Tel Aviv University 3 Paderborn University 4 Bundesamt für Sicherheit in der Informationstechnik (BSI), Germany Transport Layer Security ClientHello ServerHello, Certificate, ServerKeyExchange, ServerHelloDone ClientKeyExchange, ChangeCipherSpec, Finished ChangeCipherSpec, Finished TLS-DH(E) nC nS b ∊ ℤ g, p, g mod p, signature b p ∊ ℤ a a p g mod p gab mod p ab PRF(g , nc, nS, “master secret”) = master_secret TLS-DH(E) nC nS b ∊ ℤ g, p, g mod p, signature b p RFC 5246: The Transport Layer Security (TLS) Protocol Version 1.2 ∊ ℤ a a p g mod p 8.1. Computing the Master Secret master_secret = PRF(pre_master_secret, "master secret", ab ClientHello.random + ServerHello.random)g mod p [0..47]; Some servers reuse 8.1.2. Diffie-Hellman ephemeral keys A conventional Diffie-Hellman computationPRF(g isab ,performed. n , n , “master The secret”) = master_secret negotiated key (Z) is used as the pre_master_secret,c S and is converted into the master_secret, as specified above. Leading bytes of Z that contain all zero bits are stripped before it is used as the pre_master_secret. Key derivation and Constant Time Execution TLS key derivation is based on hash functions Hash functions operate in O(n) not O(1) This creates various side-channels: - Compression function invocation - Hash -

Graduate Programs MA | M.Sc
Graduate Programs M.A. | M.Sc. | LL.M. University of Duisburg-Essen, Essen Campus University of Duisburg-Essen, High Voltage Lab University of Duisburg-Essen, Library University Alliance Ruhr: Three universities. One community. Endless opportunities. Ruhr University Bochum, Ruhr University Bochum University of Duisburg-Essen TU Dortmund University, and the · 43,000 students (14% international) · 42,900 students (19% international) University of Duisburg-Essen formed · 3,400 academic staff · 4,200 academic staff the University Alliance Ruhr (incl. professors) (incl. professors) TU Dortmund University, Department of Arts and Material Culture Ruhr University Bochum, Main Campus (UA Ruhr) in 2007. By coming · 2,400 Master’s degrees per year · 2,200 Master’s degrees per year together to pool their expertise · 550 Doctoral degrees per year · 460 Doctoral degrees per year and enhance their collective · 900 international doctoral students · 470 international doctoral students potential, they have opened endless and guest researchers and guest researchers new opportunities. The UA Ruhr · Operating budget: €559.9m · Operating budget: €588.7m universities are located at the heart incl. €111.3m third-party funding incl. €117.7m third-party funding of Europe, in the metropolitan Ruhr for research projects for research projects area that offers a unique range of cultural and other leisure activities. TU Dortmund University The UA Ruhr universities cooperate · 34,000 students (11% international) with hundreds of universities and · 2,300 academic staff institutions around the world. To (incl. professors) support and deepen our international · 2,000 Master’s degrees per year exchange and collaboration, UA Ruhr · 270 Doctoral degrees per year created academic liaison offices in · 300 international doctoral students North America, Latin America and and guest researchers Russia. -

Curriculum Vitae Summary Education
Curriculum Vitae Jan-Frederik Kremer, PhD Candidate Born: 26th April 1986 Nationality: German Married, no children Office: Center for Global Studies / University of Bonn Walter Flex Straße 3 53113 Bonn / Germany + 49-228 73-60281 (office) [email protected] Main research areas: International Political Economy, Theories of International Relations, International Trade, U.S. foreign policy, External relations of the EU PHD- project: “International Trade and Global Power Shift” Summary Jan-Frederik Kremer heads the research group “Economy and Finance” and co-heads the research group “Structural Power” at the Center for Global Studies, University of Bonn, where he works as research fellow and lecturer. He studied Political Science, History, Economics and Philosophy at the Ruhr University Bochum and is PhD Candidate in the PhD program “International Development Studies” at the Institute of Development Research and Development Policy (IEE) and member of the DFG funded “Research School”. He was one of the very first Germans students offered a fast-track PhD opportunity. Furthermore, he was awarded several scholarships, like the Bronnbacher Scholarship and numerous DAAD and DFG travel and conference grants. In August and September 2012 Jan-Frederik stayed at the University of Miami as visiting scholar at the Miami-Florida European Union Center and in 2008 as short-term consultant at the University of the Western Cape, South-Africa. His PHD- project “International Trade and Global Power Shift” deals with the ontology of power in the realm of the global economy, focussing on the US, EU and China. He is member of the International Studies Association (ISA) and the British International Studies Association (BISA). -

MEMBERSHIP DIRECTORY Australia University of Guelph International Psychoanalytic U
MEMBERSHIP DIRECTORY Australia University of Guelph International Psychoanalytic U. Berlin University College Cork Curtin University University of LethbridGe Justus Liebig University Giessen University College Dublin La Trobe University University of Ottawa Karlsruhe Institute of TechnoloGy University of Ulster Monash University University of Toronto Katholische Universität Eichstätt- Italy National Tertiary Education Union* University of Victoria Ingolstadt SAR Italy Section University of Canberra Vancouver Island University Leibniz Universität Hannover European University Institute University of Melbourne Western University Mannheim University of Applied International School for Advanced University of New South Wales York University Sciences Studies (SISSA) University of the Sunshine Coast Chile Max Planck Society* International Telematic University Austria University of Chile Paderborn University (UNINETTUNO) Ruhr University Bochum Magna Charta Observatory Alpen-Adria-Universität Klagenfurt Czech Republic RWTH Aachen University Sapienza University of Rome MCI Management Center Innsbruck- Charles University in Prague Technische Universität Berlin Scuola IMT Alti Studi Lucca The Entrepreneurial School Palacký University Olomouc University of Graz Technische Universität Darmstadt Scuola Normale Superiore Vienna University of Economics and Denmark Technische Universität Dresden Scuola Superiore di Sant’Anna Business SAR Denmark Section Technische Universität München Scuola Superiore di Catania University of Vienna Aalborg University TH -

Examination Regulations for the Master's Programme in Biodiversity at the Ruhr-University Bochum and the University of Duisburg-Essen Dated from 17/01/2014
Examination Regulations for the Master's programme in Biodiversity at the Ruhr-University Bochum and the University of Duisburg-Essen dated from 17/01/2014 Because of §§ 2, paragraph 4 and 64 of the Higher Education Act of North Rhine-Westphalia (Higher Education Act - HG) dated from 31 October 2006 (GV NRW S. 474..), as last amended by the act of 28/05/2013 (GV .. NRW, p. 272) the Ruhr-University Bochum and the University of Duisburg-Essen have introduced the following exam regulations: Table of Contents I. General Provisions § 1 Scope and admission eligibility § 2 Programme objectives and purpose of the examination § 3 Master degree § 4 Standard period of study, study design and study extent § 5 Recognition of study and examination achievements, assessment into higher semesters § 6 Board of examiners § 7 Examiners and assessors II. Course-related examinations § 8 extent and type of examination § 9 Form of the examinations § 10 Oral Examinations § 11 Written exams § 12 Further types of examination § 13 Repetitions of examinations § 14 Absence, withdrawal, deception, regulation violation § 15 students in special situations § 16 Generation of examination grades § 17 Generation of module grades III. Master project § 18 Admission to the Master Project § 19 Master's Thesis § 20 Master's Colloquium § 21 Passing and Failing the Master's programme § 22 Calculation of the overall grade § 23 Additional Subjects § 24 Degree documents III. Final Provisions § 25 Invalidity of the Master examination, revoking of the Master's degree § 26 Access to examination records § 27 Scope § 28 Coming into force and publication I. General Provisions § 1 Scope and admission eligibility (1) These exam regulations govern the completion of studies in the joint master's program Biodiversität / Biodiversity of the Ruhr-University Bochum and the University of Duisburg-Essen. -

2019 European Learning & Teaching Forum Towards Successful Learning
2019 European Learning & Teaching Forum Towards successful learning: Controversies and common ground Organised by EUA and hosted by the University of Warsaw 14-15 February 2019 Author(s) Name: Susanne Lippold M.A. Position: Senior consultant for learning and teaching and assisstant to Vice Rector for Academic and International Affairs Organisation: Ruhr University Bochum Country: Germany E-mail address: [email protected] Short bio: Susanne Lippold, M.A. is the Assistant to the Vice Rector for Academic and International Affairs and Faculty at Ruhr-University Bochum and the senior consultant for learning and teaching. She is responsible for the curriculum development and related aspects, e.g. study regulations, accreditation, advices to educational goals. In 2017 and 2018, she represented the RUB in two Thematic Peer Groups of the Learning & Teaching Initiative. Name: Andreas Fritsch, Dr. Position: Head of Quality Assurance in Higher Education Dept. Organisation: University of Greifswald Country: Germany E-mail address: [email protected] Short bio: Dr. Andreas Fritsch is the Head of the Department of Quality Assurance at the University of Greifswald, Germany. After completing a doctorate degree in psychology at Dresden University of Technology in 2003 Dr. Andreas Fritsch gained some expertise in programme evaluation of educational measures. Since 2008 he is responsible for the evaluation, accreditation and quality assurance of study programmes at the University of Greifswald. His special interests in higher education area are survey studies, organizational development and university didactics. Proposal Title: About the benefits of cooperative action in curriculum development Abstract: 1. Problems and objectives The development of curricula sets the foundation for the quality of study and the success of a degree programme. -

Funding Programme: Nrwege Leuchttürme (Nrwege Lighthouses
Funding Programme: NRWege Leuchttürme (NRWege Lighthouses) - Projects to sustainably internationalise higher education institutions in North Rhine-Westphalia Overview of universities University Project Details Contact E-Mail Qualification for teachers with a refugee status (Lehrkräfte Plus/Teachers Plus) University of Bielefeld Lehrkräfte Plus - University of Bielefeld Dr. Renate Schüssler [email protected] Ruhr-University Bochum Lehrkräfte Plus - Ruhr-University Bochum Teacher qualification in NRW for teachers with Christina Siebert-Husmann [email protected] a refugee status, comprising linguistic, University of Duisburg-Essen Lehrkräfte Plus - University of Duisburg-Essen technical, pedagogical-intercultural, and didactic Dr. Anja Pitton [email protected] components, as well as an extended practical University of Cologne Lehrkräfte Plus - University of Cologne training phase at school accompanied by Dr. Susanne Preuschoff [email protected] mentors. University of Siegen Lehrkräfte Plus - University of Siegen Hendrik Coelen [email protected] Academic post-qualification Ostwestfalen-Lippe University of RefugING – Qualifikationsprogramm für Qualification of engineers with a refugee status Benjamin Hans [email protected] Applied Sciences and Arts/Bielefeld Ingenieure mit Fluchthintergrund in the fields of civil engineering (Ostwestfalen- University of Applied Sciences Lippe University of Applied Sciences and Arts), and engineering sciences and mathematics (Bielefeld University of Applied Sciences), including harmonisation of foreign degrees. Supporting academic success / transition into the labour market University of Bonn Start your career in Germany / I Start Preparing international students for the German Christine Müller [email protected] labour market by imparting job-relevant skills and knowledge of the German and regional labour market, and skills in building a professional network. -

Roux-En-Y Gastric Bypass Surgery Progressively Alters Radiologic Measures of Hypothalamic Inflammation in Obese Patients
Roux-en-Y gastric bypass surgery progressively alters radiologic measures of hypothalamic inflammation in obese patients Mohammed K. Hankir, … , Karsten Mul̈ ler, Burkhard Pleger JCI Insight. 2019. https://doi.org/10.1172/jci.insight.131329. Research In-Press Preview Metabolism Neuroscience Graphical abstract Find the latest version: https://jci.me/131329/pdf Roux-en-Y gastric bypass surgery progressively alters radiologic measures of hypothalamic inflammation in obese patients Abbreviated title: Gastric bypass effects on hypothalamic inflammation Mohammed K. Hankir1*§, Michael Rullmann2-5*§, Florian Seyfried6, Sven Preusser4, Sindy Poppitz2,4, Stefanie Heba7, Konstantinos Gousias8, Jana Hoyer9, Tatjana Schütz2, Arne Dietrich2,10, Karsten Müller4, Burkhard Pleger2,4,5,7 1Department of Experimental Surgery, University Hospital Wuerzburg, Wuerzburg 97080, Germany 2IFB AdiposityDiseases, University Hospital Leipzig, Leipzig 04103, Germany 3Department of Nuclear Medicine, University Hospital Leipzig 04103, Germany 4Department of Neurology, Max Planck Institute for Human Cognitive and Brain Sciences, Leipzig 04103, Germany 5Collaborative Research Centre 1052 in Obesity Mechanisms, University of Leipzig, Leipzig 04103, Germany 6Department of General, Visceral, Vascular and Pediatric Surgery, University Hospital Wuerzburg, Wuerzburg, 97080, Germany 7Department of Neurology, BG University Hospital Bergmannsheil, Ruhr-University Bochum, Bochum 44789, Germany 8Department of Neurosurgery, BG University Hospital Bergmannsheil, Ruhr-University Bochum, -
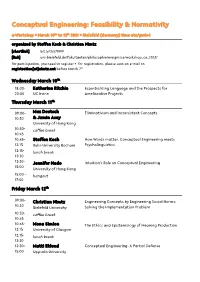
Conceptual Engineering: Feasibility & Normativity
Conceptual Engineering: Feasibility & Normativity e-Workshop . March 10th to 12th 2021 . Bielefeld (Germany) time utc/gmt+1 organized by Steffen Koch & Christian Nimtz [shortlink] bit.ly/3s57XW9 [link] uni-bielefeld.de/fakultaeten/philosophie/ereignisse/workshop_ce_2103/ for participation, you need to register . for registration, please sent an e-mail to registration[at]nimtz.net before March 7th Wednesday March 10th 18:00- Katherine Ritchie Essentializing Language and the Prospects for 20:00 UC Irvine Ameliorative Projects Thursday March 11th 09:00- Max Deutsch Eliminativism and Inconsistent Concepts 10:30 & Jamin Asay University of Hong Kong 10:30- coffee break 10:45 10:45- Steffen Koch How Words matter. Conceptual Engineering meets 12:15 Ruhr-University Bochum Psycholinguistics 12:15- lunch break 13:30 13:30- Jennifer Nado Intuition's Role on Conceptual Engineering 15:00 University of Hong Kong 15:00 – hangout 17:00 Friday March 12th 09:00- Christian Nimtz Engineering Concepts by Engineering Social Norms: 10:30 Bielefeld University Solving the Implementation Problem 10:30- coffee break 10:45 10:45- Mona Simion The Ethics and Epistemology of Meaning Production 12:15 University of Glasgow 12:15- lunch break 13:30 13:30- Matti Eklund Conceptual Engineering: A Partial Defense 15:00 Uppsala University Abstracts for the Talks Katherine Ritchie Essentializing Language and the Prospects for Ameliorative Projects UC Irvine Some language encourages essentialist thinking. I argue that psychological propensity to essentialize when nouns are used reveals a limitation for anti-essentialist ameliorative projects. Even ameliorated nouns can continue to underpin essentialist thinking. I conclude by arguing that representational essentialism does not doom anti-essentialist ameliorative projects. -

Curriculum Vitae
Curriculum Vitae Name: Detlef Gerhard Academic Degrees: Dipl.-Ing., Dr.-Ing. Nationality: German Contact Details: Universitätsstr. 150 44801, Bochum, Germany +49 234 32 27009 [email protected] Post-secondary Education: 1995 Dipl.-Ing. Mechanical Engineering (equivalent to MSc. Eng.) from University of Paderborn, Germany. Examination major: Computer Integrated Production 2000 Dr.-Ing. (equivalent to PhD) from Faculty of Mechanical Engineering (Information Technology in Mechanical Engineering Division) at Ruhr-University of Bochum, Germany Academic Positions: Since 04/2019 Ruhr-University Bochum - Faculty of Mechanical Engineering Full Professor Digital Engineering (Chair) 02/2006 – 03/2019 TU Wien – Full Professor for Mechanical Engineering Informatics and Virtual Product Development (MIVP Research Group Head) 2007 - 2011 Head of Faculty Commission for Curricula Development 2008 - 2011 Head of the Institute of Engineering Design and Logistics Engineering 2013 - 2018 Dean of the Faculty for Mechanical and Industrial Engineering Main Research Interests: Methods and IT tools for information management in multi- disciplinary product development and production with special focus on knowledge engineering, data analytics and semantics. Affiliations: Honorary Professor of Technical University Cluj-Napoca (RO) WiGeP - Wissenschaftliche Gesellschaft für Produktentwicklung (Elected Member of German Scientific Society for Product Development) Ö-WGP – Österreichisch Wissenschaftliche Gesellschaft für Produktion (Founding Member of Austrian Scientific Society of Production) VDI - Verein Deutscher Ingenieure (Association of German Engineers) Design Society GI - Gesellschaft für Informatik (German Computer Society) June 2019 – Page 1/3 Professional Record: 06/2001 – 01/2006 Loedige Industries Group, Warburg (Germany) Manufacturing company producing air cargo and material handling systems for automotive industry. Position: Manager IT and Business Automation (CIO) Department head (profit center) reporting directly to the CEO. -

Rheological Study on Squalane and Its Mixtures with CO2
Rheological Study on Squalane and Its Mixtures with CO2 Vincent Bürk C, S Chair of Particle Technology, Ruhr-University Bochum, Bochum, NRW, Germany [email protected] Sergio E. Quiñones-Cisneros Institute of Physical Chemistry, University of Cologne, Koeln, NRW, Germany Stefan Pollak Chair of Particle Technology, Ruhr-University Bochum, Bochum, NRW, Germany Eckhard Weidner Chair of Process Technology, Ruhr-University Bochum, Bochum, NRW, Germany The effect of temperature and pressure on the viscosity of squalane and its mixtures with carbon dioxide has been the subject of recent renovated interest. This research is motivated by the idea of establishing squalane as a reference fluid for the calibration of high-pressure viscosity devices. The purpose of this work is to expand the available viscosity data, to study its rheological behavior, and to provide an accurate viscosity model for the reproduction of the data in the range of conditions of application and interest. To carry out the measurements, a high-pressure capillary rheometer has been designed and constructed for operation from ambient conditions up to 353 K and 30 MPa, and variable shear rates. The shear rate can be adjusted by varying the capillary diameter and the volumetric flow rate. The rheometer is equipped with a mixing device to ensure gas saturation in order to facilitate the unperturbed transfer of the saturated fluid into the measurement chambers and capillaries. Due to its working principle, the capillary rheometer requires a pressure drop to realize the flow. Therefore, measurements near the phase boundary may lead to bubble formation. In order to avoid undesired vapor phase formation, the measurements are carried out above the estimated saturation pressure. -

Global Partners —
EXCHANGE PROGRAM Global DESTINATION GROUPS Group A: USA/ASIA/CANADA Group B: EUROPE/UK/LATIN AMERICA partners Group U: UTRECHT NETWORK CONTACT US — Office of Global Student Mobility STUDENTS MUST CHOOSE THREE PREFERENCES FROM ONE GROUP ONLY. Student Central (Builing 17) W: uow.info/study-overseas GROUP B AND GROUP U HAVE THE SAME APPLICATION DEADLINE. E: [email protected] P: +61 2 4221 5400 INSTITUTION GROUP INSTITUTION GROUP INSTITUTION GROUP AUSTRIA CZECH REPUBLIC HONG KONG University of Graz Masaryk University City University of Hong Kong Hong Kong Baptist University DENMARK BELGIUM The Education University of Aarhus University Hong Kong University of Antwerp University of Copenhagen The Hong Kong Polytechnic KU Leuven University of Southern University BRAZIL Denmark UOW College Hong Kong Federal University of Santa ESTONIA HUNGARY Catarina University of Tartu Eötvös Loránd University (ELTE) Pontifical Catholic University of Campinas FINLAND ICELAND Pontifical Catholic University of Rio de Janeiro University of Eastern Finland University of Iceland University of São Paulo FRANCE INDIA CANADA Audencia Business School Birla Institute of Management Technology (BIMTECH) Concordia University ESSCA School of Management IFIM Business School HEC Montreal Institut Polytechnique LaSalle Manipal Academy of Higher McMaster University Beauvais Education University of Alberta Lille Catholic University (IÉSEG School of Management) O.P. Jindal Global University University of British Columbia National Institute of Applied University of Calgary