Oracle Secure Enterprise Search Administrator's Guide, 11G Release 2 (11.2.2.2) E35070-15
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Oracle Data Sheet- Secure Enterprise Search
ORACLE SECURE ENTERPRISE SEARCH 11g DATA SHEET ORACLE SECURE ENTERPRISE SEARCH VERSION 11G R2 KEY FEATURES Oracle Secure Enterprise Search 11g (SES), a standalone product RELEASE 11.2.2.2 HIGHLIGHTS from Oracle, enables a high quality, secure search across all Facet Navigation enterprise information assets. Key SES features include: Push-based Content Indexing Multi-tier Install Search Result Tagging The ability to search and locate public, private and shared Unified Microsoft Sharepoint content across intranet web content, databases, files on local Connector, certified for MOSS 2010 version disk or file-servers, IMAP email, document repositories, New search result „hard sort‟ applications, and portals option Auto Suggestions “As You Type” Excellent search quality, with the most relevant items for a query Sitemap.org Support spanning diverse sources being shown first FACET NAVIGATION Full GUI support for facet Sub-second query performance creation, manipulation, and browsing. No programming required. Facet API support is Highly secure crawling, indexing, and searching also provided Facet navigation is secure. Integration with Desktop Search tools Facet values and counts are computed using only those documents that the search Ease of administration and maintenance – a „no-DBA‟ approach user is authorized to see Hierarchical- and range facets to Search. Date, number and string types Update facets without re- Information Uplift for the Intranet crawling As a result of search engines on the Internet, the power of effective search PUSH-BASED CONTENT technologies has become clear to everyone. Using the World Wide Web, consumers INDEXING have become their own information retrieval experts. But search within enterprises Allows customers to push differs radically from public Internet search. -
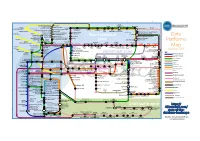
Data Platforms Map from 451 Research
1 2 3 4 5 6 Azure AgilData Cloudera Distribu2on HDInsight Metascale of Apache Kaa MapR Streams MapR Hortonworks Towards Teradata Listener Doopex Apache Spark Strao enterprise search Apache Solr Google Cloud Confluent/Apache Kaa Al2scale Qubole AWS IBM Azure DataTorrent/Apache Apex PipelineDB Dataproc BigInsights Apache Lucene Apache Samza EMR Data Lake IBM Analy2cs for Apache Spark Oracle Stream Explorer Teradata Cloud Databricks A Towards SRCH2 So\ware AG for Hadoop Oracle Big Data Cloud A E-discovery TIBCO StreamBase Cloudera Elas2csearch SQLStream Data Elas2c Found Apache S4 Apache Storm Rackspace Non-relaonal Oracle Big Data Appliance ObjectRocket for IBM InfoSphere Streams xPlenty Apache Hadoop HP IDOL Elas2csearch Google Azure Stream Analy2cs Data Ar2sans Apache Flink Azure Cloud EsgnDB/ zone Platforms Oracle Dataflow Endeca Server Search AWS Apache Apache IBM Ac2an Treasure Avio Kinesis LeanXcale Trafodion Splice Machine MammothDB Drill Presto Big SQL Vortex Data SciDB HPCC AsterixDB IBM InfoSphere Towards LucidWorks Starcounter SQLite Apache Teradata Map Data Explorer Firebird Apache Apache JethroData Pivotal HD/ Apache Cazena CitusDB SIEM Big Data Tajo Hive Impala Apache HAWQ Kudu Aster Loggly Ac2an Ingres Sumo Cloudera SAP Sybase ASE IBM PureData January 2016 Logic Search for Analy2cs/dashDB Logentries SAP Sybase SQL Anywhere Key: B TIBCO Splunk Maana Rela%onal zone B LogLogic EnterpriseDB SQream General purpose Postgres-XL Microso\ Ry\ X15 So\ware Oracle IBM SAP SQL Server Oracle Teradata Specialist analy2c PostgreSQL Exadata -

Magnify Search Security and Administration Release 8.2 Version 04
Magnify Search Security and Administration Release 8.2 Version 04 April 08, 2019 Active Technologies, EDA, EDA/SQL, FIDEL, FOCUS, Information Builders, the Information Builders logo, iWay, iWay Software, Parlay, PC/FOCUS, RStat, Table Talk, Web390, WebFOCUS, WebFOCUS Active Technologies, and WebFOCUS Magnify are registered trademarks, and DataMigrator and Hyperstage are trademarks of Information Builders, Inc. Adobe, the Adobe logo, Acrobat, Adobe Reader, Flash, Adobe Flash Builder, Flex, and PostScript are either registered trademarks or trademarks of Adobe Systems Incorporated in the United States and/or other countries. Due to the nature of this material, this document refers to numerous hardware and software products by their trademarks. In most, if not all cases, these designations are claimed as trademarks or registered trademarks by their respective companies. It is not this publisher's intent to use any of these names generically. The reader is therefore cautioned to investigate all claimed trademark rights before using any of these names other than to refer to the product described. Copyright © 2019, by Information Builders, Inc. and iWay Software. All rights reserved. Patent Pending. This manual, or parts thereof, may not be reproduced in any form without the written permission of Information Builders, Inc. Contents Preface ......................................................................... 7 Conventions ......................................................................... 7 Related Publications ................................................................. -

Enterprise Search Technology Using Solr and Cloud Padmavathy Ravikumar Governors State University
Governors State University OPUS Open Portal to University Scholarship All Capstone Projects Student Capstone Projects Spring 2015 Enterprise Search Technology Using Solr and Cloud Padmavathy Ravikumar Governors State University Follow this and additional works at: http://opus.govst.edu/capstones Part of the Databases and Information Systems Commons Recommended Citation Ravikumar, Padmavathy, "Enterprise Search Technology Using Solr and Cloud" (2015). All Capstone Projects. 91. http://opus.govst.edu/capstones/91 For more information about the academic degree, extended learning, and certificate programs of Governors State University, go to http://www.govst.edu/Academics/Degree_Programs_and_Certifications/ Visit the Governors State Computer Science Department This Project Summary is brought to you for free and open access by the Student Capstone Projects at OPUS Open Portal to University Scholarship. It has been accepted for inclusion in All Capstone Projects by an authorized administrator of OPUS Open Portal to University Scholarship. For more information, please contact [email protected]. ENTERPRISE SEARCH TECHNOLOGY USING SOLR AND CLOUD By Padmavathy Ravikumar Masters Project Submitted in partial fulfillment of the requirements For the Degree of Master of Science, With a Major in Computer Science Governors State University University Park, IL 60484 Fall 2014 ENTERPRISE SEARCH TECHNOLOGY USING SOLR AND CLOUD 2 Abstract Solr is the popular, blazing fast open source enterprise search platform from the Apache Lucene project. Its major features include powerful full-text search, hit highlighting, faceted search, near real-time indexing, dynamic clustering, database in9tegration, rich document (e.g., Word, PDF) handling, and geospatial search. Solr is highly reliable, scalable and fault tolerant, providing distributed indexing, replication and load-balanced querying, automated failover and recovery, centralized configuration and more. -

BI SEARCH and TEXT ANALYTICS New Additions to the BI Technology Stack
SECOND QUARTER 2007 TDWI BEST PRACTICES REPORT BI SEARCH AND TEXT ANALYTICS New Additions to the BI Technology Stack By Philip Russom TTDWI_RRQ207.inddDWI_RRQ207.indd cc11 33/26/07/26/07 111:12:391:12:39 AAMM Research Sponsors Business Objects Cognos Endeca FAST Hyperion Solutions Corporation Sybase, Inc. TTDWI_RRQ207.inddDWI_RRQ207.indd cc22 33/26/07/26/07 111:12:421:12:42 AAMM SECOND QUARTER 2007 TDWI BEST PRACTICES REPORT BI SEARCH AND TEXT ANALYTICS New Additions to the BI Technology Stack By Philip Russom Table of Contents Research Methodology and Demographics . 3 Introduction to BI Search and Text Analytics . 4 Defining BI Search . 5 Defining Text Analytics . 5 The State of BI Search and Text Analytics . 6 Quantifying the Data Continuum . 7 New Data Warehouse Sources from the Data Continuum . 9 Ramifications of Increasing Unstructured Data Sources . .11 Best Practices in BI Search . 12 Potential Benefits of BI Search . 12 Concerns over BI Search . 13 The Scope of BI Search . 14 Use Cases for BI Search . 15 Searching for Reports in a Single BI Platform Searching for Reports in Multiple BI Platforms Searching Report Metadata versus Other Report Content Searching for Report Sections Searching non-BI Content along with Reports BI Search as a Subset of Enterprise Search Searching for Structured Data BI Search and the Future of BI . 18 Best Practices in Text Analytics . 19 Potential Benefits of Text Analytics . 19 Entity Extraction . 20 Use Cases for Text Analytics . 22 Entity Extraction as the Foundation of Text Analytics Entity Clustering and Taxonomy Generation as Advanced Text Analytics Text Analytics Coupled with Predictive Analytics Text Analytics Applied to Semi-structured Data Processing Unstructured Data in a DBMS Text Analytics and the Future of BI . -

Text Analysis: the Next Step in Search
eDiscovery & Information Management Text Analysis: The Next Step In Search ZyLAB White Paper Johannes C. Scholtes, Ph.D. Chief Strategy Officer, ZyLAB Contents Summary 3 Finding Without Knowing Exactly What to Look For 4 Beyond the Google Standard 4 Challenges Facing Text Analysis 6 Control of Unstructured Information 6 Different Levels of Semantic Information Extraction 7 Co-reference and Anaphora Resolution 11 Faceted Search and Information Visualization 12 Text Analysis on Non-English Documents 15 Content Analytics on Multimedia Files: Audio Search 16 A Prosperous Future for Text Analysis 17 About ZyLAB 19 Summary Text and content analysis differs from traditional search in that, whereas search requires a user to know what he or she is looking for, text analysis attempts to discover information in a pattern that is not known before- hand. One of the most compelling differences with regular (web) search is that typical search engines are optimized to find only the most relevant documents; they are not optimized to find all relevant documents. The majority of commonly-used search tools are built to retrieve only the most popular hits—which simply doesn’t meet the demands of exploratory legal search. This whitepaper will lead the reader beyond the Google standard, explore the limitations and possibilities of text analysis technology and show how text analysis becomes an essential tool to help process and analyze to- day’s enormous amounts of enterprise information in a timely fashion. 3 Finding Without Knowing Exactly What to Look For In general, text analysis refers to the process of extracting interesting and non-trivial information and knowledge from unstructured text. -

Searching the Enterprise
R Foundations and Trends• in Information Retrieval Vol. 11, No. 1 (2017) 1–142 c 2017 U. Kruschwitz and C. Hull • DOI: 10.1561/1500000053 Searching the Enterprise Udo Kruschwitz Charlie Hull University of Essex, UK Flax, UK [email protected] charlie@flax.co.uk Contents 1 Introduction 2 1.1 Overview........................... 3 1.2 Examples........................... 5 1.3 PerceptionandReality . 9 1.4 RecentDevelopments . 10 1.5 Outline............................ 11 2 Plotting the Landscape 13 2.1 The Changing Face of Search . 13 2.2 DefiningEnterpriseSearch . 14 2.3 Related Search Areas and Applications . 17 2.4 SearchTechniques. 34 2.5 Contextualisation ...................... 37 2.6 ConcludingRemarks. 49 3 Enterprise Search Basics 52 3.1 StructureofData ...................... 53 3.2 CollectionGathering. 59 3.3 SearchArchitectures. 63 3.4 Information Needs and Applications . 68 3.5 SearchContext ....................... 76 ii iii 3.6 UserModelling........................ 78 3.7 Tools, Frameworks and Resources . 81 4 Evaluation 82 4.1 RelevanceandMetrics. 83 4.2 Evaluation Paradigms and Campaigns . 85 4.3 TestCollections ....................... 89 4.4 LessonsLearned ....................... 94 5 Making Enterprise Search Work 95 5.1 PuttingtheUserinControl . 96 5.2 Relevance Tuning and Support . 103 6 The Future 110 6.1 GeneralTrends........................ 110 6.2 TechnicalDevelopments. 111 6.3 Moving towards Cooperative Search . 113 6.4 SomeResearchChallenges . 114 6.5 FinalWords ......................... 117 7 Conclusion 118 Acknowledgements 120 References 121 Abstract Search has become ubiquitous but that does not mean that search has been solved. Enterprise search, which is broadly speaking the use of information retrieval technology to find information within organisa- tions, is a good example to illustrate this. -
Opentext Magellan Text Mining Helps Users Gain Insight from Unstructured Content How to Uncover Insights and Information That Optimize Organizations' Content
WHITE PAPER OpenText Magellan Text Mining helps users gain insight from unstructured content How to uncover insights and information that optimize organizations' content. Contents Introduction: Mining text for meaning 3 Definitions 4 Creating and using semantic metadata 6 Automated metadata assignment 6 Semi-automated metadata assignment 6 Methodology 7 Statistical patterns 7 Grammatical patterns 7 Machine learning 8 Decision trees 8 Post-processing algorithms 8 Knowledge engineering 9 Magellan Text Mining modules and architecture 9 Concept Extractor 10 Named Entity Extractor 10 Categorizer 10 Summarizer 11 Sentiment Analyzer 11 Language Detector 12 Additional Magellan Text Mining components 12 Conclusion 13 OpenText Magellan Text Mining helps users gain insight from unstructured content 2/13 OpenText Magellan Text Mining helps users gain insight from unstructured content. OpenText Magellan Text Mining enables enterprises to take control of their knowledge assets to manage and grow their business efficiently. Using thoughtfully selected text analytics techniques, such as metadata federation or crawlers to access data from multiple repositories, this tool can extract from content the meaningful pieces of information and help users connect with the content most relevant to them. This white paper focuses on how Magellan Text Mining streamlines and speeds up a key task of content analytics, the semantic annotation of content, to make documents more “findable” and usable for uses ranging from indexing and content curation to claim form processing and creating new, value-added content products. It takes on the task of tagging content with semantic metadata, traditionally done manually, and frees up workers from many hours of repetitive labor to exert more judgment in content management. -

Method of Semantic Refinement for Enterprise Search
Method of Semantic Refinement for Enterprise Search Alexey Pismak a, Serge Klimenkov b, Eugeny Tsopa c, Alexandr Yarkeev d, Vladimir Nikolaev e and Anton Gavrilov f ITMO University, Kronverksky pr 49, Saint-Petersburg, Russia Keywords: Semantic Networks, Translingual Data, Apache Lucene, Semantic Queries, Semantic Search, Pertinence of Search Results, Ontologies. Abstract: In this paper, we propose an approach of using the semantic refinement of the input search query for the enterprise search systems. The problem of enterprise search is actual because of the amount of processed data. Even with a good organization of documents, the process of searching for specific documents or specific data in these documents is very laborious. But even more significant problem is that the required content may have the matching meaning, but expressed with different words in the different languages, which prevents it from appearing in the search result. The proposed approach uses semantic refinement of the search query. First, the concepts are extracted from the semantic network based on translingual lexemes of the user query string, allowing to perform the search based on the senses rather than word forms. In addition, several rules are applied to the query in order to include or exclude senses which can affect the relevance and the pertinence of the search result. 1 INTRODUCTION set are closely related to each other and they usually belong to a common domain. Search systems are the mandatory component of any 2. Large number of documents. Typical digital environment of a modern enterprise. enterprise system stores a large set (from thousands Generally, the search in document databases is to millions) of different documents in various carried out by methods of grammatical full-text formats. -

Develop an Enterprise Search Strategy April 2014 Abstract
Develop an Enterprise Search Strategy April 2014 Abstract A decision to implement enterprise search cannot be taken lightly. Many companies end up frustrated with high priced products that failed to live up to their expectations. However, these companies typically put little effort into creating a compelling search experience especially given the potential productivity gains effective search can bring. To avoid the failed search experience, information and knowledge management professionals should follow these steps to maximize the impact of their search investments, while minimizing the risk of over-investing in the technology. Content Growth Demands Better Information Access Tools The past 10 years have seen both the volume and diversity of digital content within enterprises grow at unprecedented rates. Increased use of departmental file shares, collaboration tools, content management systems, messaging systems with file attachments, corporate blogs and wikis, and databases has turned corporate networks into a virtual mix of content where useless work-in-process, duplicate, and untraceable documents are mixed with valuable information needed to get work done. Despite IT efforts to control content through the use of content management systems, only a small percentage of content that gets created makes it into a managed repository like an enterprise portal or content management system. This results in: Hard to use, “system of record” document management repositories. Many of these systems have proven so complex to use that they have been relegated to storing specific authoritative information like business records, parts manuals, and formal methods and procedures that changes infrequently or must be retained for extended time period of time for legal reasons. -

G001 Speakers
New Frontiers in Enterprise Search Monday, August 20, 2018 11:00am-12:00pm #G001 SPEAKERS TODD FRIEDLICH RICK KRZYMINSKI SIMON PECOVNIK Senior Manager KM Technology & Chief Knowledge VP of Product Management Innovation Management Officer iManage LLC Ropes & Gray LLP Baker Donelson @tfriedlich CONVERSATIONAL SEARCH • Conversational Search • Voice Search PERSONAL ASSISTANTS CHATBOTS @ HOME • “Alexa, Turn off the lights.” • “OK Google, Set alarm for 6:30am” • “Siri, Where is ‘Eight Grade’ playing” I thought this was a session on search! Leslie Knope in the Alexa, Pawnee office is an Who is an expert on expert in Blockchain Blockchain? “I ALWAYS FEEL LIKE SOMEBODY'S WATCHING ME.” “Siri is listening to you, but she’s not spying” (Naked Security by Sophos) “Google tracks your movements, like it or not” (AP) “Here's how the Alexa spying scandal could become Amazon's worst nightmare” (Business Insider) NATURAL LANGUAGE PROCESSING (NLP) Intent Entity Who is an expert in Bitcoin? ContentSource:”Expertise” AND Skill:”Bitcoin” SIMPLE ANSWERS? Leslie Knope has experience with bitcoin. CANONICAL TERMS AND SYNONYMS Intent Entity Who is an expert in Bitcoin?Bitcoin? CANONICAL TERMS AND SYNONYMS Smart Contracts Who is an expert in Bitcoin? Ethereum Blockchain CLARIFYING QUESTIONS Leslie Knope has experience with bitcoin. Bitcoin is often a synonym for Blockchain, Ethereum, and Smart Contracts. Would you like me to expand my search to include those terms? MORE CLARIFICATION Contextual Conversational • What do we know about the user? • Expand search to include -

Webmethods Product Suite 9.6
webMethods Product Suite 9.6 Release Notes Release 9.6 of the webMethods product suite is another significant step in combining cloud, mobile, and social technologies with automated business processes and the agility needed to fully power your digital enterprise. Release Highlights Application Integration The webMethods suite provides many application integration enhancements in cloud integration, template-based provisioning, B2B and file transfer capabilities, mobile support for enterprise applications, and advanced API management. Some highlights are as follows: Multiple instances of webMethods Integration Server can now be configured within the same installation, eliminating the need to install Integration Server multiple times. webMethods Command Central configuration and large-scale installation tasks are made easier through the use of templates that can be created from existing installations and applied to other installations. The Command Central Cloud Factory provides a unified way of launching and managing a mixture of public cloud and private cloud instances. The processing of transactions in webMethods Trading Networks has become faster through the use of asset caching. Most of an organization’s JNDI assets and JMS assets, such as JMS queues and topics, can now seamlessly be moved from webMethods Broker to webMethods Universal Messaging using a new command line migration utility. A new feature of webMethods Enterprise Gateway, called webMethods Mobile Support, provides a mobile data synchronization framework for developers to create offline mobile applications that can access distributed data managed by backend ERP applications. Mobile Support provides built-in support for synchronization logic, thereby allowing developers to focus on developing the business logic. webMethods OneData includes several enhancements to improve the quality of data, including new engines that can be used in Cleanser and Matcher projects.