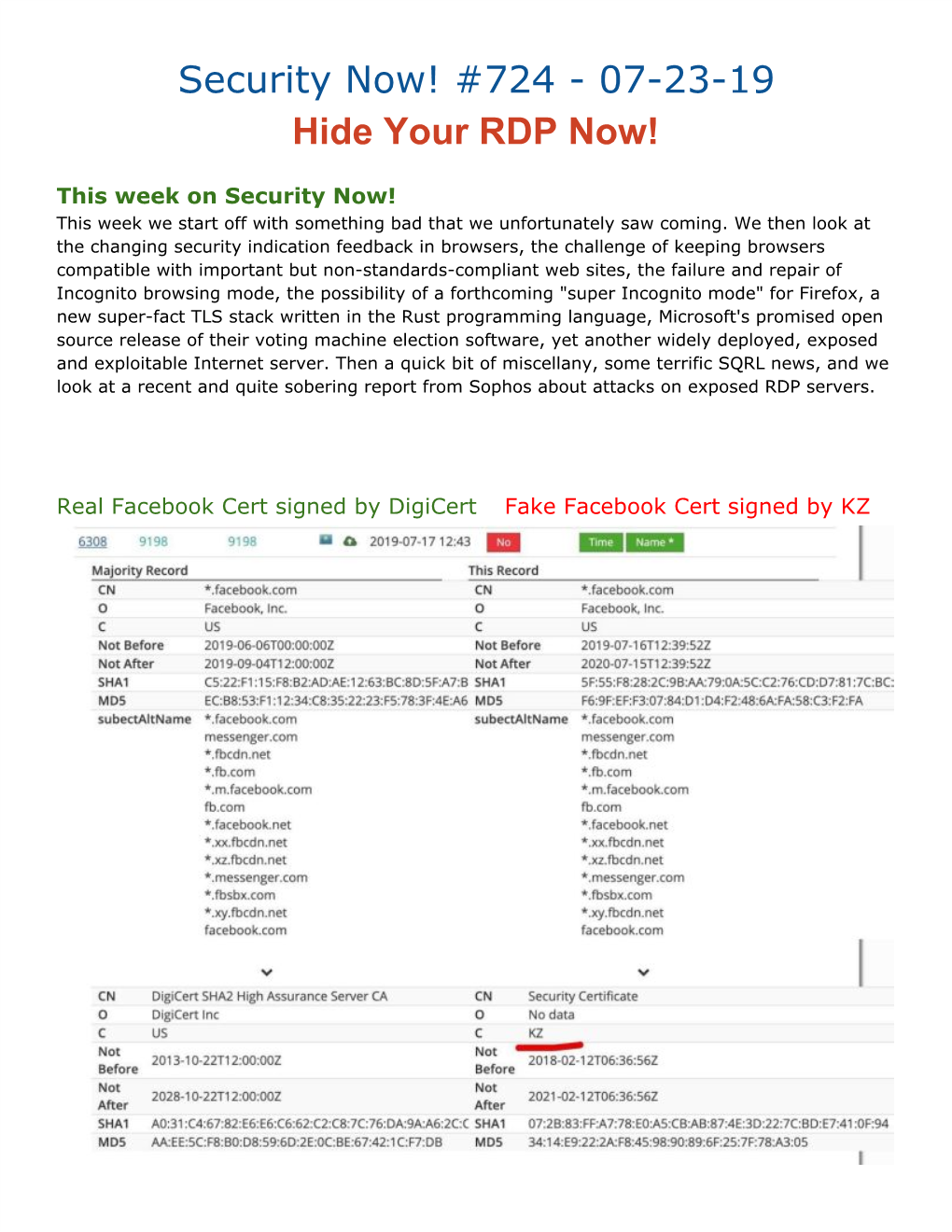
Security Now! #724 - 07-23-19 Hide Your RDP Now!
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
CPAS04 Authenticator Options Version 1.0 11 November 2015
GSM Association Non-confidential Official Document PDATA.03 - CPAS04 Authenticator Options CPAS04 Authenticator Options Version 1.0 11 November 2015 This is a Non-binding Permanent Reference Document of the GSMA Security Classification: Non-confidential Access to and distribution of this document is restricted to the persons permitted by the security classification. This document is confidential to the Association and is subject to copyright protection. This document is to be used only for the purposes for which it has been supplied and information contained in it must not be disclosed or in any other way made available, in whole or in part, to persons other than those permitted under the security classification without the prior written approval of the Association. Copyright Notice Copyright © 2016 GSM Association Disclaimer The GSM Association (“Association”) makes no representation, warranty or undertaking (express or implied) with respect to and does not accept any responsibility for, and hereby disclaims liability for the accuracy or completeness or timeliness of the information contained in this document. The information contained in this document may be subject to change without prior notice. Antitrust Notice The information contain herein is in full compliance with the GSM Association’s antitrust compliance policy. V1.0 Page 1 of 38 GSM Association Non-confidential Official Document PDATA.03 - CPAS04 Authenticator Options Table of Contents 1 Introduction 3 1.1 Overview 3 1.2 Scope 3 1.3 Abbreviations 3 1.4 References 5 2 Level -

Modern Password Security for System Designers What to Consider When Building a Password-Based Authentication System
Modern password security for system designers What to consider when building a password-based authentication system By Ian Maddox and Kyle Moschetto, Google Cloud Solutions Architects This whitepaper describes and models modern password guidance and recommendations for the designers and engineers who create secure online applications. A related whitepaper, Password security for users, offers guidance for end users. This whitepaper covers the wide range of options to consider when building a password-based authentication system. It also establishes a set of user-focused recommendations for password policies and storage, including the balance of password strength and usability. The technology world has been trying to improve on the password since the early days of computing. Shared-knowledge authentication is problematic because information can fall into the wrong hands or be forgotten. The problem is magnified by systems that don't support real-world secure use cases and by the frequent decision of users to take shortcuts. According to a 2019 Yubico/Ponemon study, 69 percent of respondents admit to sharing passwords with their colleagues to access accounts. More than half of respondents (51 percent) reuse an average of five passwords across their business and personal accounts. Furthermore, two-factor authentication is not widely used, even though it adds protection beyond a username and password. Of the respondents, 67 percent don’t use any form of two-factor authentication in their personal life, and 55 percent don’t use it at work. Password systems often allow, or even encourage, users to use insecure passwords. Systems that allow only single-factor credentials and that implement ineffective security policies add to the problem. -
Trusted Execution Environments
Trusted Execution Environments Assaf Rosenbaum Technion - Computer Science Department - M.Sc. Thesis MSC-2019-03 - 2019 Technion - Computer Science Department - M.Sc. Thesis MSC-2019-03 - 2019 Trusted Execution Environments Research Thesis Submitted in partial fulfillment of the requirements for the degree of Master of Science in Computer Science Assaf Rosenbaum Submitted to the Senate of the Technion | Israel Institute of Technology Kislev 5779 Haifa November 2018 Technion - Computer Science Department - M.Sc. Thesis MSC-2019-03 - 2019 Technion - Computer Science Department - M.Sc. Thesis MSC-2019-03 - 2019 This research was carried out under the supervision of Prof. Eli Biham and Dr. Sara Bitan, in the Faculty of Computer Science. Acknowledgements First and foremost, I wish to thank my advisors, Prof. Eli Biham and Dr. Sara Bitan, for their incredible support during the work on thesis. Thank you for providing me the freedom to find my own path while constantly guiding and directing me. I learned a lot from both of you. I would also like to thank my parents, siblings and my parents-in-law for their help and support during this stressful time. Thank you for being there whenever I needed. A special thanks is due to my three lovely children, you sparkle my life with moment of pure joy. Most importantly, I would like to thank my beautiful wife, Lior. Thank you for your endless support, the long hours in which you worked hard to give me the time I needed to work and for always pushing me forward. You ar the light of my life and I love you very much. -

A Closer Look at SQRL Research Findings
A closer look at SQRL Agenda • SQRL introduction • Related work • SQRL design details • Research questions • Research method • Research findings • Conclusion UvA-SNE-RP1 presentation 1 A closer look at SQRL SQRL introduction: trigger Secure Quick Reliable Login UvA-SNE-RP1 presentation 2 A closer look at SQRL SQRL introduction: how it works QR-scanning QR-tapping QR-clicking UvA-SNE-RP1 presentation 3 A closer look at SQRL SQRL introduction: design goals SSO 2FA out-of-band (OOB) authentication no secret(s) exchange anonymity no (additional) TTP low friction deployment UvA-SNE-RP1 presentation 4 A closer look at SQRL Related work: SSO • Open standards • OpenID • TiQR UvA-SNE-RP1 presentation 5 A closer look at SQRL SQRL design details: crypto ID site (fixed) specific secret 1-F secret 2-F Brute Elliptic Force Curve UvA-SNE-RP1 presentation 6 A closer look at SQRL SQRL design details: more crypto Compromised ID ? • ID revocation support • proves ID ownership • uses additional keys • Lock (disable) • Unlock (enable/change) UvA-SNE-RP1 presentation 7 A closer look at SQRL SQRL design details: messages UvA-SNE-RP1 presentation 8 A closer look at SQRL Research questions • How does SQRL improve authentication security compared to related solutions? • What does SQRL offer to both parties? • What constraints must be met to guaranty this behaviour? • What additional features are relevant to extend deployability? • What attacks remain feasible and what countermeasures are to be considered? UvA-SNE-RP1 presentation 9 A closer look at SQRL -

Zero-Knowledge User Authentication: an Old Idea Whose Time Has Come
Zero-Knowledge User Authentication: An Old Idea Whose Time Has Come Laurent Chuat, Sarah Plocher, and Adrian Perrig ETH Zurich Abstract User authentication can rely on various factors (e.g., a pass- word, a cryptographic key, and/or biometric data) but should not re- veal any secret information held by the user. This seemingly paradoxical feat can be achieved through zero-knowledge proofs. Unfortunately, naive password-based approaches still prevail on the web. Multi-factor authen- tication schemes address some of the weaknesses of the traditional login process, but generally have deployability issues or degrade usability even further as they assume users do not possess adequate hardware. This as- sumption no longer holds: smartphones with biometric sensors, cameras, short-range communication capabilities, and unlimited data plans have become ubiquitous. In this paper, we show that, assuming the user has such a device, both security and usability can be drastically improved using an augmented password-authenticated key agreement (PAKE) pro- tocol and message authentication codes. 1 Introduction User authentication still typically involves transmitting a plaintext password to the web server, which is problematic for many reasons. First, an attacker could obtain the user’s password using malware, a keystroke logger, phishing, or a man-in-the-middle attack. Second, the user might be using the same password on different websites, allowing a malicious server operator to impersonate the user. Third, if the website’s database is breached, although passwords may be protected by a hash function, a brute-force attack could reveal low-entropy pass- words. Fourth, as password-reuse and low-entropy passwords are problematic, users are constantly advised to pick new, long, complicated passwords. -

SQRL: Anti-Phishing & Revocation
Security Now! Transcript of Episode #426 Page 1 of 30 Transcript of Episode #426 SQRL: Anti-Phishing & Revocation Description: After following-up on a week chockful of interesting security news, Steve and Leo continue with their discussion of SQRL, the Secure QR code Login system, to discuss two recent innovations in the system that bring additional valuable features. High quality (64 kbps) mp3 audio file URL: http://media.GRC.com/sn/SN-426.mp3 Quarter size (16 kbps) mp3 audio file URL: http://media.GRC.com/sn/sn-426-lq.mp3 SHOW TEASE: It's time for Security Now!. Steve Gibson has the latest - yes, another Java patch - and more information about Lavabit. More information about the NSA, too. What is a Ferret's Cannon? It's coming up next on Security Now!. Leo Laporte: This is Security Now! with Steve Gibson, Episode 426, recorded October 16th, 2013: SQRL, Anti-Phishing, and Revocation. It's time for Security Now!, the show that covers your privacy and security online. Somebody in the chatroom before we began the show today, Steve Gibson, Explainer in Chief, said we should call it "Insecurity Now!" since it really talks mostly about insecure. But not today. Today we're going to talk about better security. Steve Gibson: Well, yeah. Actually, this is one of those episodes where so much happened in the last week in security news that, I mean, we just - there's a whole bunch of really interesting stuff to talk about. And in the past when we've done that we've just said, okay, we're not going to have any major topic because too much happened. -

Management Digitaler Identitäten : Aktueller Status Und Zukünftige Trends
Management Digitaler Identitäten: Aktueller Status und zukünftige Trends Christian Tietz, Chris Pelchen, Christoph Meinel, Maxim Schnjakin Technische Berichte Nr. 114 des Hasso-Plattner-Instituts für Softwaresystemtechnik an der Universität Potsdam ISBN 978-3-86956-395-4 ISSN 1613-5652 Technische Berichte des Hasso-Plattner-Instituts für Softwaresystemtechnik an der Universität Potsdam Technische Berichte des Hasso-Plattner-Instituts für Softwaresystemtechnik an der Universität Potsdam | 114 Christian Tietz | Chris Pelchen | Christoph Meinel | Maxim Schnjakin Management Digitaler Identitäten Aktueller Status und zukünftige Trends Universitätsverlag Potsdam Bibliografische Information der Deutschen Nationalbibliothek Die Deutsche Nationalbibliothek verzeichnet diese Publikation in der Deutschen Nationalbibliografie; detaillierte bibliografische Daten sind im Internet über http://dnb.dnb.de/ abrufbar. Universitätsverlag Potsdam 2017 http://verlag.ub.uni-potsdam.de/ Am Neuen Palais 10, 14469 Potsdam Tel.: +49 (0)331 977 2533 / Fax: 2292 E-Mail: [email protected] Die Schriftenreihe Technische Berichte des Hasso-Plattner-Instituts für Softwaresystemtechnik an der Universität Potsdam wird herausgegeben von den Professoren des Hasso-Plattner-Instituts für Softwaresystemtechnik an der Universität Potsdam. ISSN (print) 1613-5652 ISSN (online) 2191-1665 Das Manuskript ist urheberrechtlich geschützt. Online veröffentlicht auf dem Publikationsserver der Universität Potsdam URN urn:nbn:de:kobv:517-opus4-103164 http://nbn-resolving.de/urn:nbn:de:kobv:517-opus4-103164 -

World Speed Skating Championships 2021
On behalf of the KNSB, the Organizing Committee has the honor and pleasure to invite you to participate in the WORLD SPEED SKATING CHAMPIONSHIPS 2021 which will be held in Heerenveen, Netherlands on February 11-14, 2021 PROGRAM Wednesday, February 10, 2021 17:30 Online Team Leaders Meeting via MS Teams in combination with the online draw Invitation will be sent in due time Thursday, February 11, 2021 14:50 3000m Ladies 5000m Men Friday, February 12, 2021 15:10 Team Pursuit Ladies Team Pursuit Men 500m Men 500m Ladies Saturday, February 13, 2021 13:45 Semi-Finals Mass Start Ladies Semi-Finals Mass Start Men 1000m Ladies 1000m Men Final Mass Start Ladies Final Mass Start Men Sunday, February 14, 2021 12:35 1500m Ladies 1500m Men 5000m Ladies 10 000m Men REGULATIONS The ISU World Speed Skating Championships 2021 (Single Distances & Team Pursuit) will be held in accordance with the 2018 Regulations of the International Skating Union (ISU), relevant ISU Communications, in particular ISU Communication No. 2361, Guidelines for ISU Events During the COVID-19 Pandemic and all Health Regulations guidelines edited and released by House of Sports. Participation in the Championships is open to Skaters who belong to an ISU Member (Rule 130, paragraph 1) that has been allocated quota place(s) for the Championships, and who have met the qualification criteria according to Rule 208 and ISU Communication No. 2361. TRACK Thialf is an indoor artificially frozen ice rink with a standard track of 400 meters and inner and outer curves with radii of 26 and 30 meters respectively. -

Justin Love FVCP 2018-03-14 Outline
Next Get Authentication SQRL and other trends in authentication systems Justin Love FVCP 2018-03-14 Outline • Theft of Server DB • Weak Passwords • Loss of User Information • Theft of User Information Next Get Authentication SQRL and other trends in authentication systems Justin Love FVCP 2018-03-14 Secure Quick Reliable Login Justin Love [email protected] http://wondible.com @wondible THREAT Theft of Server Database https://duckduckgo.com/?q=database+compromise “Three may keep a secret if two are dead. –Benjamin Franklin Some Secrets Should not be shared Nothing to Lose Public/Private Key Cryptography One Way Functions SSH Elliptic Curve https://en.wikipedia.org/wiki/File:EllipticCurveCatalog.svg Elliptic Curve https://en.wikipedia.org/wiki/File:EllipticCurveCatalog.svg ED25519 http://arstechnica.com/security/2013/10/a-relatively-easy- to-understand-primer-on-elliptic-curve-cryptography/ Bitcoin AES Bittorrent Sync FIDO UAF “256 bits is the new black.” –Steve Gibson https://github.com/jedisct1/libsodium THREAT Weak Passwords Weak https://xato.net/passwords/more-top-worst-passwords/ Password Schemes http://xkcd.com/936/ Forgotten http://xkcd.com/936/ Reused http://xkcd.com/792/ Password Manager Something you Know Something you Have Something you Are Agents Apps Mobile Push Authentication Public/Private Key Cryptography SSH Crypto Currency Wallet SQRL Secure the Private Key Encryption Levels of Protection Multi-level Encryption THREAT Loss of User Information User Responsibility Out-of-band may be possible Offline Storage MetaMask Words -
SQRL Revisited
Security Now! Transcript of Episode #516 Page 1 of 27 Transcript of Episode #516 SQRL Revisited Description: Security and privacy-related news keeps coming! So this week Father Robert and I will cover the past week's many interesting events. Then we revisit the much evolved and nearly finalized SQRL protocol to see how it has grown and matured during the 92 weeks since I first disclosed its concept during Podcast 424 with Tom. High quality (64 kbps) mp3 audio file URL: http://media.GRC.com/sn/SN-516.mp3 Quarter size (16 kbps) mp3 audio file URL: http://media.GRC.com/sn/sn-516-lq.mp3 SHOW TEASE: Today with Steve Gibson: Hacking Team follies, UEFI nightmare. Can exceptional access exist beside strong encryption? And everything you ever wanted to know about SQRL but were afraid to ask. Security Now! is next. FATHER ROBERT BALLECER: This is Security Now! with Steve Gibson, Episode 516, recorded July 14th, 2015: Hacking Team vs. SQRL. It's time for Security Now!, the show that covers your privacy and security online with the one, the only, the incomparable Steve Gibson from GRC.com. That's right, the creator of ShieldsUP!, SpinRite, and soon SQRL. Steve, so good to see you again, my friend. Steve Gibson: Well, Father, this is our third and final podcast together. And, boy, based on the feedback from the last couple, you're definitely a hit as my co-host. So anytime Leo feels that he needs to take a break from this, I know that you'll be welcome back. -

Lousy Phish— Relay Attacks on Visual Code Authentication Schemes
I bought a new security token and all I got was this lousy phish| Relay attacks on visual code authentication schemes Graeme Jenkinson, Max Spencer, Chris Warrington, Frank Stajano fgraeme.jenkinson, max.spencer, chris.warrington, [email protected] University of Cambridge Computer Laboratory, Cambridge, UK Abstract. One recent thread of academic and commercial research into web authentication has focused on schemes where users scan a visual code with their smartphone, which is a convenient alternative to password- based login. We find that many schemes in the literature (including, previously, our own) are, unfortunately, vulnerable to relay attacks. We explain the inherent reasons for this vulnerability and offer an architec- tural fix, evaluating its trade-offs and discussing why it has never been proposed by other authors. 1 Introduction We consider a relatively new class of web authentication schemes, currently at- tracting significant academic and commercial interest, which we refer to as visual code authentication schemes. A user may log into a website which supports such an authentication scheme by scanning a visual code, such as a Quick Response (QR) code [1], using their hand-held authenticator device, henceforth scanner. The scanner is generally a smartphone, but might be a dedicated hardware gad- get. The user carries their scanner at all times, or at least whenever they might want to authenticate to a website; the scanner may have a mechanism to prevent its misuse if lost or stolen. Our own Pico system [2] is of course in this class too. Such schemes are interesting because they have some important usability benefits which passwords do not; specifically, there is nothing for users to remem- ber or type1. -
Sqrl and U2f As 2Fa for Cern Sso
EVALUATION AND IMPLEMENTATION OF SQRL AND U2F AS 2FA FOR CERN SSO SUPERVISORS BY VINCENT BRILLAULT (IT-DI-CSO) AZQA NADEEM (IT-DI-CSO) STEFAN LUEDERS (IT-DI-CSO) PROJECT GOALS 2 AZQA NADEEM (IT-DI-CSO) PROJECT GOALS Evaluation of SQRL and U2F 2 AZQA NADEEM (IT-DI-CSO) PROJECT GOALS Evaluation of SQRL and U2F Implementation of feasible 2FA algorithm 2 AZQA NADEEM (IT-DI-CSO) PROJECT GOALS Evaluation of SQRL and U2F Implementation of feasible 2FA algorithm Integration with CERN Single Sign-on (SSO) 2 AZQA NADEEM (IT-DI-CSO) 2ND FACTOR AUTHENTICATION 3 AZQA NADEEM (IT-DI-CSO) 2ND FACTOR AUTHENTICATION 3 AZQA NADEEM (IT-DI-CSO) 2ND FACTOR AUTHENTICATION 4 AZQA NADEEM (IT-DI-CSO) 2ND FACTOR AUTHENTICATION • Username • Password 5 AZQA NADEEM (IT-DI-CSO) 2ND FACTOR AUTHENTICATION • Cell phone • Physical token • Biometrics 6 AZQA NADEEM (IT-DI-CSO) CERN SINGLE SIGN-ON 7 AZQA NADEEM (IT-DI-CSO) CERN SINGLE SIGN-ON SMS 7 AZQA NADEEM (IT-DI-CSO) CERN SINGLE SIGN-ON SMS Google Authenticator 7 AZQA NADEEM (IT-DI-CSO) CERN SINGLE SIGN-ON SMS Google Authenticator Yubikey 7 AZQA NADEEM (IT-DI-CSO) CERN SINGLE SIGN-ON SMS Google Authenticator Yubikey Smartcard 7 AZQA NADEEM (IT-DI-CSO) CERN SINGLE SIGN-ON Can we do better? 8 AZQA NADEEM (IT-DI-CSO) SQRL VS. U2F Secure Quick Reliable Login (SQRL) Universal 2nd Factor (U2F) 9 AZQA NADEEM (IT-DI-CSO) SECURE QUICK RELIABLE LOGIN (SQRL) 10 AZQA NADEEM (IT-DI-CSO) SECURE QUICK RELIABLE LOGIN (SQRL) • Software based authentication mechanism 10 AZQA NADEEM (IT-DI-CSO) SECURE QUICK RELIABLE LOGIN (SQRL)