Digging in the Dark
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

UC Santa Barbara UC Santa Barbara Electronic Theses and Dissertations
UC Santa Barbara UC Santa Barbara Electronic Theses and Dissertations Title A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz Permalink https://escholarship.org/uc/item/6w76f8x7 Author Swift, Kathy Publication Date 2017 Peer reviewed|Thesis/dissertation eScholarship.org Powered by the California Digital Library University of California UNIVERSITY OF CALIFORNIA Santa Barbara A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz A dissertation submitted in partial satisfaction of the requirements for the degree Doctor of Philosophy in Education by Kathleen Anne Swift Committee in charge: Professor Richard Duran, Chair Professor Diana Arya Professor William Robinson September 2017 The dissertation of Kathleen Anne Swift is approved. ................................................................................................................................ Diana Arya ................................................................................................................................ William Robinson ................................................................................................................................ Richard Duran, Committee Chair June 2017 A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz Copyright © 2017 by Kathleen Anne Swift iii ACKNOWLEDGEMENTS I would like to thank the members of my committee for their advice and patience as I worked on gathering and analyzing the copious amounts of research necessary to -
BUGS in the SYSTEM a Primer on the Software Vulnerability Ecosystem and Its Policy Implications
ANDI WILSON, ROSS SCHULMAN, KEVIN BANKSTON, AND TREY HERR BUGS IN THE SYSTEM A Primer on the Software Vulnerability Ecosystem and its Policy Implications JULY 2016 About the Authors About New America New America is committed to renewing American politics, Andi Wilson is a policy analyst at New America’s Open prosperity, and purpose in the Digital Age. We generate big Technology Institute, where she researches and writes ideas, bridge the gap between technology and policy, and about the relationship between technology and policy. curate broad public conversation. We combine the best of With a specific focus on cybersecurity, Andi is currently a policy research institute, technology laboratory, public working on issues including encryption, vulnerabilities forum, media platform, and a venture capital fund for equities, surveillance, and internet freedom. ideas. We are a distinctive community of thinkers, writers, researchers, technologists, and community activists who Ross Schulman is a co-director of the Cybersecurity believe deeply in the possibility of American renewal. Initiative and senior policy counsel at New America’s Open Find out more at newamerica.org/our-story. Technology Institute, where he focuses on cybersecurity, encryption, surveillance, and Internet governance. Prior to joining OTI, Ross worked for Google in Mountain About the Cybersecurity Initiative View, California. Ross has also worked at the Computer The Internet has connected us. Yet the policies and and Communications Industry Association, the Center debates that surround the security of our networks are for Democracy and Technology, and on Capitol Hill for too often disconnected, disjointed, and stuck in an Senators Wyden and Feingold. unsuccessful status quo. -

The Internet and Drug Markets
INSIGHTS EN ISSN THE INTERNET AND DRUG MARKETS 2314-9264 The internet and drug markets 21 The internet and drug markets EMCDDA project group Jane Mounteney, Alessandra Bo and Alberto Oteo 21 Legal notice This publication of the European Monitoring Centre for Drugs and Drug Addiction (EMCDDA) is protected by copyright. The EMCDDA accepts no responsibility or liability for any consequences arising from the use of the data contained in this document. The contents of this publication do not necessarily reflect the official opinions of the EMCDDA’s partners, any EU Member State or any agency or institution of the European Union. Europe Direct is a service to help you find answers to your questions about the European Union Freephone number (*): 00 800 6 7 8 9 10 11 (*) The information given is free, as are most calls (though some operators, phone boxes or hotels may charge you). More information on the European Union is available on the internet (http://europa.eu). Luxembourg: Publications Office of the European Union, 2016 ISBN: 978-92-9168-841-8 doi:10.2810/324608 © European Monitoring Centre for Drugs and Drug Addiction, 2016 Reproduction is authorised provided the source is acknowledged. This publication should be referenced as: European Monitoring Centre for Drugs and Drug Addiction (2016), The internet and drug markets, EMCDDA Insights 21, Publications Office of the European Union, Luxembourg. References to chapters in this publication should include, where relevant, references to the authors of each chapter, together with a reference to the wider publication. For example: Mounteney, J., Oteo, A. and Griffiths, P. -

Download (589Kb)
This is an Open Access document downloaded from ORCA, Cardiff University's institutional repository: http://orca.cf.ac.uk/95227/ This is the author’s version of a work that was submitted to / accepted for publication. Citation for final published version: Décary-Hétu, David and Giommoni, Luca 2017. Do police crackdowns disrupt drug cryptomarkets? a longitudinal analysis of the effects of Operation Onymous. Crime, Law and Social Change 67 (1) , pp. 55-75. 10.1007/s10611-016-9644-4 file Publishers page: http://dx.doi.org/10.1007/s10611-016-9644-4 <http://dx.doi.org/10.1007/s10611- 016-9644-4> Please note: Changes made as a result of publishing processes such as copy-editing, formatting and page numbers may not be reflected in this version. For the definitive version of this publication, please refer to the published source. You are advised to consult the publisher’s version if you wish to cite this paper. This version is being made available in accordance with publisher policies. See http://orca.cf.ac.uk/policies.html for usage policies. Copyright and moral rights for publications made available in ORCA are retained by the copyright holders. 1 Do Police Crackdowns Disrupt Drug Cryptomarkets? A Longitudinal Analysis Of The Effects Of Operation Onymous In recent years, there has been a proliferation of online illicit markets where participants can purchase and sell a wide range of goods and services such as drugs, hacking services, and stolen financial information. Second- generation markets, known as cryptomarkets, provide a pseudo-anonymous platform from which to operate and have attracted the attention of researchers, regulators, and law enforcement. -

Threat Modeling and Circumvention of Internet Censorship
Threat modeling and circumvention of Internet censorship David Fifield September 27, 2017 Abstract Research on Internet censorship is hampered by a lack of adequate models of censor behavior, encompassing both censors' current practice and their likely future evolution. Censor models guide the development of circumvention systems, so it is important to get them right. A censor model should be understood not only as a set of capabilities| such as the ability to monitor network traffic—but also as a set of priorities constrained by resource limitations. A circumvention system designed under inadequate assumptions runs the risk of being either easily blocked, or impractical to deploy. My thesis research will be concerned with developing empirically informed censor models and practical, effective circumvention systems to counter them. My goal is to move the field away from seeing the censorship problem as a cat-and-mouse game that affords only incre- mental and temporary advancements. We should instead state the hypotheses and assumptions under which our circumvention designs will work|with the designs being more or less practical depending on how well the hypotheses and assumptions match the behavior of real-world censors. 1 Thesis My research is about Internet censorship and how to make it ineffective. To this end, I am interested in building useful models of real-world censors as they exist today and may exist in the future, for the purpose of building circumvention systems that are not only sound in theory but also effective in practice. 1 2 Scope Internet censorship is an enormous topic. My thesis research is concerned with one important case of it: the border firewall. -

Van De Laarschot and Rolf Van Wegberg, Delft University of Technology
Risky Business? Investigating the Security Practices of Vendors on an Online Anonymous Market using Ground-Truth Data Jochem van de Laarschot and Rolf van Wegberg, Delft University of Technology https://www.usenix.org/conference/usenixsecurity21/presentation/van-de-laarschot This paper is included in the Proceedings of the 30th USENIX Security Symposium. August 11–13, 2021 978-1-939133-24-3 Open access to the Proceedings of the 30th USENIX Security Symposium is sponsored by USENIX. Risky Business? Investigating the Security Practices of Vendors on an Online Anonymous Market using Ground-Truth Data Jochem van de Laarschot Rolf van Wegberg Delft University of Technology Delft University of Technology Abstract However, there are numerous indications in earlier work that cybercriminals do not always achieve maximum security. Cybercriminal entrepreneurs on online anonymous markets Due to competing business incentives, criminals may turn rely on security mechanisms to thwart investigators in at- to insecure practices that ease transacting illegal products or tributing their illicit activities. Earlier work indicates that – services. Here, we witness an inevitable trade-off between despite the high-risk criminal context – cybercriminals may enhanced security and improved efficiency of operations [42]. turn to poor security practices due to competing business ‘Perfect security’ therefore, is not economically viable. Like incentives. This claim has not yet been supported through in the legitimate economy [54], security in the underground empirical, quantitative analysis on ground-truth data. In this economy comes at a cost [53]. This leads us to wonder how paper, we investigate the security practices on Hansa Mar- prevalent poor security practices (or: “insecure practices”) ket (2015-2017) and measure the prevalence of poor security among online anonymous market vendors actually are. -
BUGS in the SYSTEM a Primer on the Software Vulnerability Ecosystem and Its Policy Implications
ANDI WILSON, ROSS SCHULMAN, KEVIN BANKSTON, AND TREY HERR BUGS IN THE SYSTEM A Primer on the Software Vulnerability Ecosystem and its Policy Implications JULY 2016 About the Authors About New America New America is committed to renewing American politics, Andi Wilson is a policy analyst at New America’s Open prosperity, and purpose in the Digital Age. We generate big Technology Institute, where she researches and writes ideas, bridge the gap between technology and policy, and about the relationship between technology and policy. curate broad public conversation. We combine the best of With a specific focus on cybersecurity, Andi is currently a policy research institute, technology laboratory, public working on issues including encryption, vulnerabilities forum, media platform, and a venture capital fund for equities, surveillance, and internet freedom. ideas. We are a distinctive community of thinkers, writers, researchers, technologists, and community activists who Ross Schulman is a co-director of the Cybersecurity believe deeply in the possibility of American renewal. Initiative and senior policy counsel at New America’s Open Find out more at newamerica.org/our-story. Technology Institute, where he focuses on cybersecurity, encryption, surveillance, and Internet governance. Prior to joining OTI, Ross worked for Google in Mountain About the Cybersecurity Initiative View, California. Ross has also worked at the Computer The Internet has connected us. Yet the policies and and Communications Industry Association, the Center debates that surround the security of our networks are for Democracy and Technology, and on Capitol Hill for too often disconnected, disjointed, and stuck in an Senators Wyden and Feingold. unsuccessful status quo. -

IPFS and Friends: a Qualitative Comparison of Next Generation Peer-To-Peer Data Networks Erik Daniel and Florian Tschorsch
1 IPFS and Friends: A Qualitative Comparison of Next Generation Peer-to-Peer Data Networks Erik Daniel and Florian Tschorsch Abstract—Decentralized, distributed storage offers a way to types of files [1]. Napster and Gnutella marked the beginning reduce the impact of data silos as often fostered by centralized and were followed by many other P2P networks focusing on cloud storage. While the intentions of this trend are not new, the specialized application areas or novel network structures. For topic gained traction due to technological advancements, most notably blockchain networks. As a consequence, we observe that example, Freenet [2] realizes anonymous storage and retrieval. a new generation of peer-to-peer data networks emerges. In this Chord [3], CAN [4], and Pastry [5] provide protocols to survey paper, we therefore provide a technical overview of the maintain a structured overlay network topology. In particular, next generation data networks. We use select data networks to BitTorrent [6] received a lot of attention from both users and introduce general concepts and to emphasize new developments. the research community. BitTorrent introduced an incentive Specifically, we provide a deeper outline of the Interplanetary File System and a general overview of Swarm, the Hypercore Pro- mechanism to achieve Pareto efficiency, trying to improve tocol, SAFE, Storj, and Arweave. We identify common building network utilization achieving a higher level of robustness. We blocks and provide a qualitative comparison. From the overview, consider networks such as Napster, Gnutella, Freenet, BitTor- we derive future challenges and research goals concerning data rent, and many more as first generation P2P data networks, networks. -
Privacy Enhancing Technologies 2003 an Analysis of Gnunet And
Privacy Enhancing Technologies 2003 An Analysis of GNUnet and the Implications for Anonymous, Censorship-Resistant Networks Dennis Kügler Federal Office for Information Security, Germany [email protected] 1 Anonymous, Censorship-Resistant Networks • Anonymous Peer-to-Peer Networks – Gnutella • Searching is relatively anonymous • Downloading is not anonymous • Censorship-Resistant Networks – Eternity Service • Distributed storage medium • Attack resistant • Anonymous, Censorship-Resistant Networks – Freenet – GNUnet 2 GNUnet: Obfuscated, Distributed Filesystem Content Hash Key: [H(B),H(E (B))] • H(B) – Content encryption: H(B) – Unambiguous filename: H(E (B)) H(B) • Content replication – Caching while delivering – Based on unambiguous filename • Searchability – Keywords 3 GNUnet: Peer-to-Peer MIX Network • Initiating node – Downloads content • Supplying nodes – Store content unencrypted • Intermediary nodes – Forward and cache encrypted content – Plausible deniability due to encryption • Economic model – Based on credit Query A Priority=20 B – Charge for queries c =c -20 B B - – Pay for responses 4 GNUnet Encoding • DBlocks DBlock DBlock ... DBlock – 1KB of the content – Content hash encrypted • IBlocks IBlock ... IBlock – CHKs of 25 DBlocks – Organized as tree – Content hash encrypted IBlock • RBlock – Description of the content – CHK of the root IBlock RBlock – Keyword encrypted 5 The Attacker Model • Attacker – Controls malicious nodes that behave correctly – Prepares dictionary of interesting keywords – Observes queries and -

An Evolving Threat the Deep Web
8 An Evolving Threat The Deep Web Learning Objectives distribute 1. Explain the differences between the deep web and darknets.or 2. Understand how the darknets are accessed. 3. Discuss the hidden wiki and how it is useful to criminals. 4. Understand the anonymity offered by the deep web. 5. Discuss the legal issues associated withpost, use of the deep web and the darknets. The action aimed to stop the sale, distribution and promotion of illegal and harmful items, including weapons and drugs, which were being sold on online ‘dark’ marketplaces. Operation Onymous, coordinated by Europol’s Europeancopy, Cybercrime Centre (EC3), the FBI, the U.S. Immigration and Customs Enforcement (ICE), Homeland Security Investigations (HSI) and Eurojust, resulted in 17 arrests of vendors andnot administrators running these online marketplaces and more than 410 hidden services being taken down. In addition, bitcoins worth approximately USD 1 million, EUR 180,000 Do in cash, drugs, gold and silver were seized. —Europol, 20141 143 Copyright ©2018 by SAGE Publications, Inc. This work may not be reproduced or distributed in any form or by any means without express written permission of the publisher. 144 Cyberspace, Cybersecurity, and Cybercrime THINK ABOUT IT 8.1 Surface Web and Deep Web Google, Facebook, and any website you can What Would You Do? find via traditional search engines (Internet Explorer, Chrome, Firefox, etc.) are all located 1. The deep web offers users an anonym- on the surface web. It is likely that when you ity that the surface web cannot provide. use the Internet for research and/or social What would you do if you knew that purposes you are using the surface web. -

Into the Reverie: Exploration of the Dream Market
Into the Reverie: Exploration of the Dream Market Theo Carr1, Jun Zhuang2, Dwight Sablan3, Emma LaRue4, Yubao Wu5, Mohammad Al Hasan2, and George Mohler2 1Department of Mathematics, Northeastern University, Boston, MA 2Department of Computer & Information Science, Indiana University - Purdue University, Indianapolis, IN 3Department of Mathematics and Computer Science, University of Guam, Guam 4Department of Mathematics and Statistics, University of Arkansas at Little Rock, AK 5Department of Computer Science, Georgia State University, Atlanta, GA [email protected], [email protected], [email protected], [email protected], [email protected], [email protected], [email protected], [email protected] Abstract—Since the emergence of the Silk Road market in Onymous" in 2014, a worldwide action taken by law enforce- the early 2010s, dark web ‘cryptomarkets’ have proliferated and ment and judicial agencies aimed to put a kibosh on these offered people an online platform to buy and sell illicit drugs, illicit behaviors [5]. Law enforcement interventions such as relying on cryptocurrencies such as Bitcoin for anonymous trans- actions. However, recent studies have highlighted the potential for Onymous, along with exit scams and hacks, have successfully de-anonymization of bitcoin transactions, bringing into question shut down numerous cryptomarkets, including AlphaBay, Silk the level of anonymity afforded by cryptomarkets. We examine a Road, Dream, and more recently, Wall Street [6]. Despite these set of over 100,000 product reviews from several cryptomarkets interruptions, new markets have continued to proliferate. The collected in 2018 and 2019 and conduct a comprehensive analysis authors of [7] note that there appears to be a consistent daily of the markets, including an examination of the distribution of drug sales and revenue among vendors, and a comparison demand of about $500,000 for illicit products on the dark web, of incidences of opioid sales to overdose deaths in a US city. -
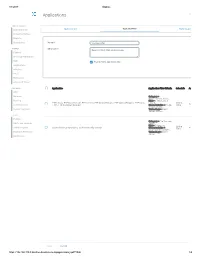
Applications Log Viewer
4/1/2017 Sophos Applications Log Viewer MONITOR & ANALYZE Control Center Application List Application Filter Traffic Shaping Default Current Activities Reports Diagnostics Name * Mike App Filter PROTECT Description Based on Block filter avoidance apps Firewall Intrusion Prevention Web Enable Micro App Discovery Applications Wireless Email Web Server Advanced Threat CONFIGURE Application Application Filter Criteria Schedule Action VPN Network Category = Infrastructure, Netw... Routing Risk = 1-Very Low, 2- FTPS-Data, FTP-DataTransfer, FTP-Control, FTP Delete Request, FTP Upload Request, FTP Base, Low, 4... All the Allow Authentication FTPS, FTP Download Request Characteristics = Prone Time to misuse, Tra... System Services Technology = Client Server, Netwo... SYSTEM Profiles Category = File Transfer, Hosts and Services Confe... Risk = 3-Medium Administration All the TeamViewer Conferencing, TeamViewer FileTransfer Characteristics = Time Allow Excessive Bandwidth,... Backup & Firmware Technology = Client Server Certificates Save Cancel https://192.168.110.3:4444/webconsole/webpages/index.jsp#71826 1/4 4/1/2017 Sophos Application Application Filter Criteria Schedule Action Applications Log Viewer Facebook Applications, Docstoc Website, Facebook Plugin, MySpace Website, MySpace.cn Website, Twitter Website, Facebook Website, Bebo Website, Classmates Website, LinkedIN Compose Webmail, Digg Web Login, Flickr Website, Flickr Web Upload, Friendfeed Web Login, MONITOR & ANALYZE Hootsuite Web Login, Friendster Web Login, Hi5 Website, Facebook Video